DocumentoAndysah Putera Utama Siahaan - Rabin-Karp Elaboration in Comparing Pattern Based on Hash Datacaricato da
DocumentoAndysah Putera Utama Siahaan - Rabin-Karp Elaboration in Comparing Pattern Based on Hash Datacaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoComposite Performance Index for Student Admissioncaricato da
DocumentoComposite Performance Index for Student Admissioncaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoSolly Aryza - Novelty Stability Of Electrical System Single Machine Based Runge Kutta Orde 4 Method.pdfcaricato da
DocumentoSolly Aryza - Novelty Stability Of Electrical System Single Machine Based Runge Kutta Orde 4 Method.pdfcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoMesran - Implementation of Complex Proportional Assessment Method in the Selection of Mango Seeds.pdfcaricato da
DocumentoMesran - Implementation of Complex Proportional Assessment Method in the Selection of Mango Seeds.pdfcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoMasdin Saragih - Violations of Cybercrime and the Strength of Jurisdiction in Indonesia.pdfcaricato da
DocumentoMasdin Saragih - Violations of Cybercrime and the Strength of Jurisdiction in Indonesia.pdfcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoExpert System of Catfish Disease Determinant Using Certainty Factor Methodcaricato da
DocumentoExpert System of Catfish Disease Determinant Using Certainty Factor Methodcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoFuzzification of College Adviser Proficiency Based on Specific Knowledgecaricato da
DocumentoFuzzification of College Adviser Proficiency Based on Specific Knowledgecaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoWLAN Penetration Examination of the University of Pembangunan Panca Budicaricato da
DocumentoWLAN Penetration Examination of the University of Pembangunan Panca Budicaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoVernam Conjugated Manipulation of Bit-Plane Complexity Segmentationcaricato da
DocumentoVernam Conjugated Manipulation of Bit-Plane Complexity Segmentationcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoThree-Pass Protocol Implementation on Caesar Cipher in Classic Cryptographycaricato da
DocumentoThree-Pass Protocol Implementation on Caesar Cipher in Classic Cryptographycaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoThree-Pass Protocol Concept in Hill Cipher Encryption Technique Ver 2caricato da
DocumentoThree-Pass Protocol Concept in Hill Cipher Encryption Technique Ver 2caricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoThe Analysis of Average Waiting Time in Managing Concurrent Processcaricato da
DocumentoThe Analysis of Average Waiting Time in Managing Concurrent Processcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoHuffman Text Compression Techniquecaricato da
DocumentoHuffman Text Compression Techniquecaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoRC4 Technique in Visual Cryptography RGB Image Encryptioncaricato da
DocumentoRC4 Technique in Visual Cryptography RGB Image Encryptioncaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoRail Fence Cryptography in Securing Informationcaricato da
DocumentoRail Fence Cryptography in Securing Informationcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoProfile Matching in Solving Rank Problemcaricato da
DocumentoProfile Matching in Solving Rank Problemcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoOptimasi Penjadwalan Mata Kuliah Dengan Algoritma Genetikacaricato da
DocumentoOptimasi Penjadwalan Mata Kuliah Dengan Algoritma Genetikacaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoNoise-Like Region Security Improvisation in BPCS Steganographycaricato da
DocumentoNoise-Like Region Security Improvisation in BPCS Steganographycaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoKlasifikasi Data Minuman Wine Menggunakan Algoritma K-Nearest Neighborcaricato da
DocumentoKlasifikasi Data Minuman Wine Menggunakan Algoritma K-Nearest Neighborcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoFactorization Hack of RSA Secret Numberscaricato da
DocumentoFactorization Hack of RSA Secret Numberscaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoDynamic Key Matrix of Hill Cipher Using Genetic Algorithm Ver 3caricato da
DocumentoDynamic Key Matrix of Hill Cipher Using Genetic Algorithm Ver 3caricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoDining Philosophers Theory and Concept in Operating System Schedulingcaricato da
DocumentoDining Philosophers Theory and Concept in Operating System Schedulingcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoDetermination of Thesis Preceptor and Examiner Based on Specification of Teaching Using Fuzzy Logiccaricato da
DocumentoDetermination of Thesis Preceptor and Examiner Based on Specification of Teaching Using Fuzzy Logiccaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoAdler-32 Integrity Validation in 24bit Color Imagecaricato da
DocumentoAdler-32 Integrity Validation in 24bit Color Imagecaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoComparison Between WEKA and Salford System in Data Mining Softwarecaricato da
DocumentoComparison Between WEKA and Salford System in Data Mining Softwarecaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoA Fingerprint Pattern Approach to Hill Cipher Implementationcaricato da
DocumentoA Fingerprint Pattern Approach to Hill Cipher Implementationcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoRC4 Technique in Visual Cryptography RGB Image Encryptioncaricato da
DocumentoRC4 Technique in Visual Cryptography RGB Image Encryptioncaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoDetermination of Thesis Preceptor and Examiner Based on Specification of Teaching Using Fuzzy Logiccaricato da
DocumentoDetermination of Thesis Preceptor and Examiner Based on Specification of Teaching Using Fuzzy Logiccaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoPlaying Guitar A Beginner’s Guidecaricato da
DocumentoPlaying Guitar A Beginner’s Guidecaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoBasic 4 Androidcaricato da
DocumentoBasic 4 Androidcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoData Visual Basiccaricato da
DocumentoData Visual Basiccaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoWhat is Name? And What is its Function?caricato da
DocumentoWhat is Name? And What is its Function?caricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoRBGcaricato da
DocumentoRBGcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoJazz Bass Book Notationcaricato da
DocumentoJazz Bass Book Notationcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoMatrikscaricato da
DocumentoMatrikscaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoPinaocaricato da
DocumentoPinaocaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoLatihancaricato da
DocumentoLatihancaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoPENDAHULUANcaricato da
DocumentoPENDAHULUANcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoDining Philosophers Problemcaricato da
DocumentoDining Philosophers Problemcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoDining Philosophers Problemcaricato da
DocumentoDining Philosophers Problemcaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoAuthentication Text Sourcecaricato da
DocumentoAuthentication Text Sourcecaricato da Andysah Putra Utama Siahaan
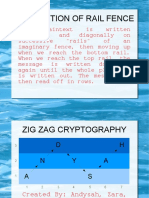
Andysah Putra Utama Siahaan DocumentoZig Zag Cryptographycaricato da
DocumentoZig Zag Cryptographycaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoThe Weakness of Wireless Networkscaricato da
DocumentoThe Weakness of Wireless Networkscaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoVarious Patterns of Data Mining Techniquescaricato da
DocumentoVarious Patterns of Data Mining Techniquescaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoShortest Way Huffman Text Compressioncaricato da
DocumentoShortest Way Huffman Text Compressioncaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoGreen Computing Pada Teknologi Virtualisasicaricato da
DocumentoGreen Computing Pada Teknologi Virtualisasicaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoKompresi Huffmancaricato da
DocumentoKompresi Huffmancaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoThe Weakness of Wireless Networkscaricato da
DocumentoThe Weakness of Wireless Networkscaricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentoMicrosoft Word 2010caricato da
DocumentoMicrosoft Word 2010caricato da Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan
Documenti di Didattica
Documenti di Professioni
Documenti di Cultura