DocumentoHacking - CEH Cheat Sheet Exercisescaricato da
DocumentoHacking - CEH Cheat Sheet Exercisescaricato da rgolfnut1
rgolfnut1 DocumentoRapsodo Mobile Launch Monitor Review The Breakfast Ballcaricato da
DocumentoRapsodo Mobile Launch Monitor Review The Breakfast Ballcaricato da rgolfnut1
rgolfnut1 DocumentoSheriff's Sale No. 2018-13893caricato da
DocumentoSheriff's Sale No. 2018-13893caricato da rgolfnut1
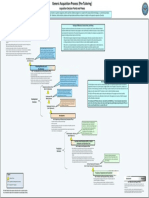
rgolfnut1 DocumentoDefense Acquisition Process Waterfall Methodcaricato da
DocumentoDefense Acquisition Process Waterfall Methodcaricato da rgolfnut1
rgolfnut1 DocumentoFundamentals of System Acquisition Mgmt Part2caricato da
DocumentoFundamentals of System Acquisition Mgmt Part2caricato da rgolfnut1
rgolfnut1 DocumentoATTACKS by OSI model Layers DDoS Quick Guide.pdfcaricato da
DocumentoATTACKS by OSI model Layers DDoS Quick Guide.pdfcaricato da rgolfnut1
rgolfnut1 DocumentoSteganographic Embedding Undetectable by JPEG Compatibility Steganalysis Newman etal2002.pdfcaricato da
DocumentoSteganographic Embedding Undetectable by JPEG Compatibility Steganalysis Newman etal2002.pdfcaricato da rgolfnut1
rgolfnut1 DocumentoSteganographic Embedding Undetectable by JPEG Compatibility Steganalysis Newman Etal2002caricato da
DocumentoSteganographic Embedding Undetectable by JPEG Compatibility Steganalysis Newman Etal2002caricato da rgolfnut1
rgolfnut1 DocumentoShavlik Patch User Guidecaricato da
DocumentoShavlik Patch User Guidecaricato da rgolfnut1
rgolfnut1 DocumentoRegistryDecoder Offline Analysis Instructions v1.1 (1)caricato da
DocumentoRegistryDecoder Offline Analysis Instructions v1.1 (1)caricato da rgolfnut1
rgolfnut1 DocumentoFundamental Computer Investigation Guide for Windowscaricato da
DocumentoFundamental Computer Investigation Guide for Windowscaricato da rgolfnut1
rgolfnut1 DocumentoGolf Swing Speed Training Logcaricato da
DocumentoGolf Swing Speed Training Logcaricato da rgolfnut1
rgolfnut1 DocumentoRotator Cuff and AB Exercisescaricato da
DocumentoRotator Cuff and AB Exercisescaricato da rgolfnut1
rgolfnut1 DocumentoLinear Codes - cryptographycaricato da
DocumentoLinear Codes - cryptographycaricato da rgolfnut1
rgolfnut1 DocumentoCryptography - Lecture1caricato da
DocumentoCryptography - Lecture1caricato da rgolfnut1
rgolfnut1 DocumentoOrthogonal Matricescaricato da
DocumentoOrthogonal Matricescaricato da rgolfnut1
rgolfnut1 DocumentoLouisian Private Investigator Lawscaricato da
DocumentoLouisian Private Investigator Lawscaricato da rgolfnut1
rgolfnut1 DocumentoInstallShield AdminStudio ConfiguringRepackage PHrcaricato da
DocumentoInstallShield AdminStudio ConfiguringRepackage PHrcaricato da rgolfnut1
rgolfnut1 DocumentoInstallShield AdminStudio ConfiguringRepackage PHrcaricato da
DocumentoInstallShield AdminStudio ConfiguringRepackage PHrcaricato da rgolfnut1
rgolfnut1 DocumentoInstallShield AdminStudio ConfiguringRepackage PHrcaricato da
DocumentoInstallShield AdminStudio ConfiguringRepackage PHrcaricato da rgolfnut1
rgolfnut1 DocumentoTypes of Forgeriescaricato da
DocumentoTypes of Forgeriescaricato da rgolfnut1
rgolfnut1 DocumentoStat Formulascaricato da
DocumentoStat Formulascaricato da rgolfnut1
rgolfnut1 DocumentoEcryptfs Enterprise Linuxcaricato da
DocumentoEcryptfs Enterprise Linuxcaricato da rgolfnut1
rgolfnut1 DocumentoFatness to Fitness Digital Versioncaricato da
DocumentoFatness to Fitness Digital Versioncaricato da rgolfnut1
rgolfnut1 DocumentoFEMA ICS200_Student Manualcaricato da
DocumentoFEMA ICS200_Student Manualcaricato da rgolfnut1
rgolfnut1 DocumentoMold_remediation Instructions Univ South Carolinacaricato da
DocumentoMold_remediation Instructions Univ South Carolinacaricato da rgolfnut1
rgolfnut1 Documento09.02.10.HashingPasswords Class.csci4621caricato da
Documento09.02.10.HashingPasswords Class.csci4621caricato da rgolfnut1
rgolfnut1 Documento09.02.10.BirthdayParadox.CSC4621caricato da
Documento09.02.10.BirthdayParadox.CSC4621caricato da rgolfnut1
rgolfnut1 Documento9.23.10.Polyinstantiation PDFcaricato da
Documento9.23.10.Polyinstantiation PDFcaricato da rgolfnut1
rgolfnut1 DocumentoSocket Programmingcaricato da
DocumentoSocket Programmingcaricato da rgolfnut1
rgolfnut1 Documento47349048 Malware Detection Using OWA Measurecaricato da
Documento47349048 Malware Detection Using OWA Measurecaricato da rgolfnut1
rgolfnut1 DocumentoGeologic Conditions Beneath New Orleanscaricato da
DocumentoGeologic Conditions Beneath New Orleanscaricato da rgolfnut1
rgolfnut1 DocumentoAbsolute Value Inequalitiescaricato da
DocumentoAbsolute Value Inequalitiescaricato da rgolfnut1
rgolfnut1 DocumentoPenetration Testing Sample Reportcaricato da
DocumentoPenetration Testing Sample Reportcaricato da rgolfnut1
rgolfnut1 DocumentoLinux Security Quick Reference Guidecaricato da
DocumentoLinux Security Quick Reference Guidecaricato da rgolfnut1
rgolfnut1 DocumentoLimits of Steganographycaricato da
DocumentoLimits of Steganographycaricato da rgolfnut1
rgolfnut1 Documentogdb-refcardcaricato da
Documentogdb-refcardcaricato da rgolfnut1
rgolfnut1 DocumentoEmacs Referencecaricato da
DocumentoEmacs Referencecaricato da rgolfnut1
rgolfnut1 DocumentoArray List ADT'scaricato da
DocumentoArray List ADT'scaricato da rgolfnut1
rgolfnut1 DocumentoComplex Networkscaricato da
DocumentoComplex Networkscaricato da rgolfnut1
rgolfnut1 DocumentoSet Theory Functionscaricato da
DocumentoSet Theory Functionscaricato da rgolfnut1
rgolfnut1
Documenti di Didattica
Documenti di Professioni
Documenti di Cultura