Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
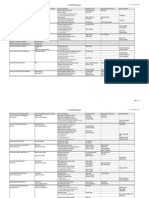
Federal Computer Attack Laws
Caricato da
Michael Perez0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
38 visualizzazioni25 pagineTitolo originale
ethcpp03 part 2
Copyright
© © All Rights Reserved
Formati disponibili
PPT, PDF, TXT o leggi online da Scribd
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
© All Rights Reserved
Formati disponibili
Scarica in formato PPT, PDF, TXT o leggi online su Scribd
0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
38 visualizzazioni25 pagineFederal Computer Attack Laws
Caricato da
Michael PerezCopyright:
© All Rights Reserved
Formati disponibili
Scarica in formato PPT, PDF, TXT o leggi online su Scribd
Sei sulla pagina 1di 25
Federal Laws for Prosecuting
Computer Attacks
Ethics in Information Technology, Fourth Edition
Implementing Trustworthy Computing
• Trustworthy computing
– Delivers secure, private, and reliable computing
– Based on sound business practices
Ethics in Information Technology, Fourth Edition
Implementing Trustworthy Computing
(cont’d.)
• Security of any system or network
– Combination of technology, policy, and people
– Requires a wide range of activities to be effective
• Systems must be monitored to detect possible
intrusion
• Clear reaction plan addresses:
– Notification, evidence protection, activity log
maintenance, containment, eradication, and
recovery
Ethics in Information Technology, Fourth Edition
Risk Assessment
• Process of assessing security-related risks:
– To an organization’s computers and networks
– From both internal and external threats
• Identifies investments that best protect from most
likely and serious threats
• Focuses security efforts on areas of highest payoff
Ethics in Information Technology, Fourth Edition
Risk Assessment (cont’d.)
• Eight-step risk assessment process
– #1 Identify assets of most concern
– #2 Identify loss events that could occur
– #3 Assess likelihood of each potential threat
– #4 Determine the impact of each threat
– #5 Determine how each threat could be mitigated
– #6 Assess feasibility of mitigation options
– #7 Perform cost-benefit analysis
– #8 Decide which countermeasures to implement
Ethics in Information Technology, Fourth Edition
Risk Assessment (cont’d.)
Ethics in Information Technology, Fourth Edition
Risk Assessment (cont’d.)
Ethics in Information Technology, Fourth Edition
Establishing a Security Policy
• A security policy defines:
– Organization’s security requirements
– Controls and sanctions needed to meet the
requirements
• Delineates responsibilities and expected behavior
• Outlines what needs to be done
– Not how to do it
• Automated system policies should mirror written
policies
Ethics in Information Technology, Fourth Edition
Establishing a Security Policy (cont’d.)
• Trade-off between:
– Ease of use
– Increased security
• Areas of concern
– Email attachments
– Wireless devices
• VPN uses the Internet to relay communications but
maintains privacy through security features
• Additional security includes encrypting originating
and receiving network addresses
Ethics in Information Technology, Fourth Edition
Educating Employees, Contractors,
and Part-Time Workers
• Educate and motivate users to understand and
follow policy
• Discuss recent security incidents
• Help protect information systems by:
– Guarding passwords
– Not allowing sharing of passwords
– Applying strict access controls to protect data
– Reporting all unusual activity
– Protecting portable computing and data storage
devices
Ethics in Information Technology, Fourth Edition
Prevention
• Implement a layered security solution
– Make computer break-ins harder
• Installing a corporate firewall
– Limits network access
• Intrusion prevention systems
– Block viruses, malformed packets, and other threats
• Installing antivirus software
– Scans for sequence of bytes or virus signature
– United States Computer Emergency Readiness
Team (US-CERT) serves as clearinghouse
Ethics in Information Technology, Fourth Edition
Prevention (cont’d.)
Ethics in Information Technology, Fourth Edition
Prevention (cont’d.)
Ethics in Information Technology, Fourth Edition
Prevention (cont’d.)
• Safeguards against attacks by malicious insiders
• Departing employees and contractors
– Promptly delete computer accounts, login IDs, and
passwords
• Carefully define employee roles and separate key
responsibilities
• Create roles and user accounts to limit authority
Ethics in Information Technology, Fourth Edition
Prevention (cont’d.)
• Defending against cyberterrorism
– Department of Homeland Security and its National
Cyber Security Division (NCSD) is a resource
• Builds and maintains a national security
cyberspace response system
• Implements a cyber-risk management program
for protection of critical infrastructure, including
banking and finance, water, government
operations, and emergency services
Ethics in Information Technology, Fourth Edition
Prevention (cont’d.)
• Conduct periodic IT security audits
– Evaluate policies and whether they are followed
– Review access and levels of authority
– Test system safeguards
– Information Protection Assessment kit is available
from the Computer Security Institute
Ethics in Information Technology, Fourth Edition
Detection
• Detection systems
– Catch intruders in the act
• Intrusion detection system
– Monitors system/network resources and activities
– Notifies the proper authority when it identifies:
• Possible intrusions from outside the organization
• Misuse from within the organization
– Knowledge-based approach
– Behavior-based approach
Ethics in Information Technology, Fourth Edition
Response
• Response plan
– Develop well in advance of any incident
– Approved by:
• Legal department
• Senior management
• Primary goals
– Regain control and limit damage
– Not to monitor or catch an intruder
• Only 56% have response plan
Ethics in Information Technology, Fourth Edition
Response (cont’d.)
• Incident notification defines:
– Who to notify
– Who not to notify
• Security experts recommend against releasing
specific information about a security compromise in
public forums
• Document all details of a security incident
– All system events
– Specific actions taken
– All external conversations
Ethics in Information Technology, Fourth Edition
Response (cont’d.)
• Act quickly to contain an attack
• Eradication effort
– Collect and log all possible criminal evidence
– Verify necessary backups are current and complete
– Create new backups
• Follow-up
– Determine how security was compromised
• Prevent it from happening again
Ethics in Information Technology, Fourth Edition
Response (cont’d.)
• Review
– Determine exactly what happened
– Evaluate how the organization responded
• Weigh carefully the amount of effort required to
capture the perpetrator
• Consider the potential for negative publicity
• Legal precedent
– Hold organizations accountable for their own IT
security weaknesses
Ethics in Information Technology, Fourth Edition
Computer Forensics
• Combines elements of law and computer science
to identify, collect, examine, and preserve data and
preserve its integrity so it is admissible as evidence
• Computer forensics investigation requires
extensive training and certification and knowledge
of laws that apply to gathering of criminal evidence
Ethics in Information Technology, Fourth Edition
Summary
• Ethical decisions in determining which information
systems and data most need protection
• Most common computer exploits
– Viruses
– Worms
– Trojan horses
– Distributed denial-of-service attacks
– Rootkits
– Spam
– Phishing, spear-fishing, smishing, vishing
Ethics in Information Technology, Fourth Edition
Summary (cont’d.)
• Perpetrators include:
– Hackers
– Crackers
– Malicious insider
– Industrial spies
– Cybercriminals
– Hacktivist
– Cyberterrorists
Ethics in Information Technology, Fourth Edition
Summary (cont’d.)
• Must implement multilayer process for managing
security vulnerabilities, including:
– Assessment of threats
– Identifying actions to address vulnerabilities
– User education
• IT must lead the effort to implement:
– Security policies and procedures
– Hardware and software to prevent security breaches
• Computer forensics is key to fighting computer
crime in a court of law
Ethics in Information Technology, Fourth Edition
Potrebbero piacerti anche
- Ethics in Information Technology, Fourth Edition: Computer and Internet CrimeDocumento22 pagineEthics in Information Technology, Fourth Edition: Computer and Internet CrimeWajiha RehmanNessuna valutazione finora
- CIA Security Model ExplainedDocumento26 pagineCIA Security Model ExplainedWajiha Rehman100% (1)
- Computer Security and Penetration Testing: Incident HandlingDocumento60 pagineComputer Security and Penetration Testing: Incident HandlingOsei SylvesterNessuna valutazione finora
- IS Lecture 3Documento58 pagineIS Lecture 3Abdul MoizNessuna valutazione finora
- 2incident ManagementDocumento54 pagine2incident ManagementJaico DictaanNessuna valutazione finora
- Information SecurityDocumento29 pagineInformation SecuritykhaledawarsiNessuna valutazione finora
- Computer and Internet Crime: Ethics in Information Technology, Fourth EditionDocumento51 pagineComputer and Internet Crime: Ethics in Information Technology, Fourth EditionsamraNessuna valutazione finora
- Chapter 3 Komputer Masyarakat Dan Etika Profesi English PDFDocumento47 pagineChapter 3 Komputer Masyarakat Dan Etika Profesi English PDFElly JongNessuna valutazione finora
- Ethics in Information Technology, Fourth Edition: Computer and Internet CrimeDocumento51 pagineEthics in Information Technology, Fourth Edition: Computer and Internet CrimeSaleh ShakibNessuna valutazione finora
- Dr. Phil Nyoni: Digital Forensics Lecture 1: Introduction To ForensicsDocumento40 pagineDr. Phil Nyoni: Digital Forensics Lecture 1: Introduction To ForensicsQomindawoNessuna valutazione finora
- Ethics in IT Security IncidentsDocumento43 pagineEthics in IT Security IncidentsdharsiniNessuna valutazione finora
- Security, Privacy, and EthicsDocumento37 pagineSecurity, Privacy, and EthicsvsmurthytNessuna valutazione finora
- Ethics in Information Technology, Fourth Edition: Computer and Internet CrimeDocumento67 pagineEthics in Information Technology, Fourth Edition: Computer and Internet CrimeAlbert PaytarenNessuna valutazione finora
- Manage cyber incidents effectively with NIST frameworkDocumento54 pagineManage cyber incidents effectively with NIST frameworkLGU GALIMUYODNessuna valutazione finora
- PPT Ch02-Amr PDFDocumento57 paginePPT Ch02-Amr PDFCharlito MikolliNessuna valutazione finora
- 98-367 2E Lesson 1 SlidesDocumento35 pagine98-367 2E Lesson 1 SlidesKefy AhmeedNessuna valutazione finora
- Risk - Assessment & Forensic AnalysisDocumento15 pagineRisk - Assessment & Forensic Analysisrjkj123Nessuna valutazione finora
- Cyber Security: Mrs. V. NikithaDocumento78 pagineCyber Security: Mrs. V. Nikithanikitha veeramallaNessuna valutazione finora
- 03 - Etika ProfesiDocumento51 pagine03 - Etika ProfesiBaramukti DewayanaNessuna valutazione finora
- Feleke Network Security Part 1 2023Documento17 pagineFeleke Network Security Part 1 2023Abni booNessuna valutazione finora
- Ethics in Information TechnologyDocumento49 pagineEthics in Information Technologythetechboss100% (1)
- Hands-On Ethical Hacking and Network Defense, 3rd EditionDocumento30 pagineHands-On Ethical Hacking and Network Defense, 3rd EditionSiddhartha Bikram KarkiNessuna valutazione finora
- Operating Systems and Computer Security: Week - 1Documento26 pagineOperating Systems and Computer Security: Week - 1Mangala SemageNessuna valutazione finora
- Cert-In: IT Security PolicyDocumento13 pagineCert-In: IT Security PolicyAFSungoNessuna valutazione finora
- Information Security Chapter 2Documento20 pagineInformation Security Chapter 2bscitsemvNessuna valutazione finora
- 98-367 2E Lesson 1 SlidesDocumento41 pagine98-367 2E Lesson 1 SlidesEsraa Sayed Abdelhamed SayedNessuna valutazione finora
- The Certified Ethical Hacker Exam - version 8 (The concise study guide)Da EverandThe Certified Ethical Hacker Exam - version 8 (The concise study guide)Valutazione: 3 su 5 stelle3/5 (9)
- Lesson 1 Introduction To Information SecurityDocumento42 pagineLesson 1 Introduction To Information Securityrazel gicaleNessuna valutazione finora
- Ch 1 Intro to InfoSecDocumento65 pagineCh 1 Intro to InfoSecShakti SriNessuna valutazione finora
- IS-486 Unit 1 (ch01)Documento55 pagineIS-486 Unit 1 (ch01)ِ ᏞUᏦᎪ x22Nessuna valutazione finora
- Information Security Chapter 1Documento44 pagineInformation Security Chapter 1bscitsemvNessuna valutazione finora
- Ethics in Information Technology, Second Edition: Computer and Internet CrimeDocumento49 pagineEthics in Information Technology, Second Edition: Computer and Internet Crimecarl_abanganNessuna valutazione finora
- 98-367 Lesson 1 SlidesDocumento32 pagine98-367 Lesson 1 SlidesOligo CocoNessuna valutazione finora
- Module 4b Security PDFDocumento72 pagineModule 4b Security PDFAngella Chisomo MagomboNessuna valutazione finora
- PPT Ch01Documento49 paginePPT Ch01Ryxn xxNessuna valutazione finora
- Incident & Incident Response MethodologyDocumento38 pagineIncident & Incident Response MethodologyKashish VermaNessuna valutazione finora
- Ch11 DropboxDocumento19 pagineCh11 DropboxJanes VuNessuna valutazione finora
- Information Security: Code: ETCS-401Documento27 pagineInformation Security: Code: ETCS-401Uday VermaNessuna valutazione finora
- Principles of Information Security, Fourth Edition: The Need For SecurityDocumento55 paginePrinciples of Information Security, Fourth Edition: The Need For SecurityGawerNessuna valutazione finora
- Principles of Information Security, Fourth Edition: The Need For SecurityDocumento58 paginePrinciples of Information Security, Fourth Edition: The Need For SecurityFifa FIFA0% (1)
- Isaa M1Documento105 pagineIsaa M1AshwinSivasankar VenkatesanNessuna valutazione finora
- Principles of Information Security, Fourth Edition: Why Security Is NeededDocumento55 paginePrinciples of Information Security, Fourth Edition: Why Security Is NeededAntonyNessuna valutazione finora
- IS & F Lecture 2-3 Introduction To Information SecurityDocumento31 pagineIS & F Lecture 2-3 Introduction To Information SecuritySadiholicNessuna valutazione finora
- Computer and Internet CrimeDocumento51 pagineComputer and Internet CrimeClara PanggabeanNessuna valutazione finora
- BASICINFOSECWEEK4Documento7 pagineBASICINFOSECWEEK4rizaldeadonis2020Nessuna valutazione finora
- SCI4201 Lecture 1 - OverviewDocumento45 pagineSCI4201 Lecture 1 - Overviewonele mabhena100% (1)
- Ethics in Information Technology, Second Edition: Computer and Internet CrimeDocumento48 pagineEthics in Information Technology, Second Edition: Computer and Internet CrimeSULTAN SksaNessuna valutazione finora
- NS - 12 Incident ResponseDocumento24 pagineNS - 12 Incident ResponseYogaRizwanNessuna valutazione finora
- lecture 01 Information SecurityDocumento45 paginelecture 01 Information Securityfsamreen30970Nessuna valutazione finora
- Principles of Information: Systems, Ninth EditionDocumento59 paginePrinciples of Information: Systems, Ninth EditiononlyhawaNessuna valutazione finora
- Introduction to Cyber ForensicsDocumento22 pagineIntroduction to Cyber ForensicsRekha V RNessuna valutazione finora
- 03-Csirt Operation FirstDocumento77 pagine03-Csirt Operation FirstPredrag SkundricNessuna valutazione finora
- Risk Analysis and Minimizing Network ThreatsDocumento41 pagineRisk Analysis and Minimizing Network ThreatsJuanNessuna valutazione finora
- Introduction To Digital ForensicsDocumento28 pagineIntroduction To Digital ForensicsSurendra Dawadi50% (2)
- Sanchez-Adrian-B. Final Reviewer 06-01-23Documento6 pagineSanchez-Adrian-B. Final Reviewer 06-01-23Frankrine SolanoNessuna valutazione finora
- About The PresentationsDocumento55 pagineAbout The PresentationsperihelionessNessuna valutazione finora
- CEH Notes Cybrary PDFDocumento34 pagineCEH Notes Cybrary PDFJashan Singh100% (1)
- Session 4 (Computer Crimes Protection)Documento20 pagineSession 4 (Computer Crimes Protection)crisanto porniaNessuna valutazione finora
- Incident ResponseDocumento63 pagineIncident ResponseANIRUDH B K 19BIT0348Nessuna valutazione finora
- New Text DocumentDocumento1 paginaNew Text DocumentMichael PerezNessuna valutazione finora
- CB400 PartsDocumento2 pagineCB400 PartsMichael PerezNessuna valutazione finora
- 03 Software ApplicationDocumento29 pagine03 Software ApplicationMichael PerezNessuna valutazione finora
- Segmentation: CS 537 - Introduction To Operating SystemsDocumento13 pagineSegmentation: CS 537 - Introduction To Operating SystemsAnjali KumariNessuna valutazione finora
- CB400 PartsDocumento2 pagineCB400 PartsMichael PerezNessuna valutazione finora
- Abec VSDocumento4 pagineAbec VSMichael PerezNessuna valutazione finora
- List of Figures TitleDocumento1 paginaList of Figures TitleMichael PerezNessuna valutazione finora
- Effects of Computer Games To The Academic Studies of StudentsDocumento39 pagineEffects of Computer Games To The Academic Studies of StudentsMichael PerezNessuna valutazione finora
- Socrates Thesis Antithesis SynthesisDocumento8 pagineSocrates Thesis Antithesis Synthesisgjfcp5jb100% (2)
- 12 - Chapter 5Documento65 pagine12 - Chapter 5Kumar SujeetNessuna valutazione finora
- Page 75Documento3 paginePage 75Aya AlayonNessuna valutazione finora
- Governmentality and risk in the new NHSDocumento21 pagineGovernmentality and risk in the new NHSS A SouravNessuna valutazione finora
- City of Rochester Press Log: From 04/15/2021 12:00:00 AM Through 04/15/2021 23:59:59 PMDocumento7 pagineCity of Rochester Press Log: From 04/15/2021 12:00:00 AM Through 04/15/2021 23:59:59 PMinforumdocsNessuna valutazione finora
- Trummer and MeyerDocumento12 pagineTrummer and MeyerMD LzaNessuna valutazione finora
- Salient Features of The Companies ActDocumento3 pagineSalient Features of The Companies ActAniket MishraNessuna valutazione finora
- Preliminary InjunctionDocumento6 paginePreliminary InjunctionThe Salt Lake TribuneNessuna valutazione finora
- 194 Ferrer v. Sandiganbayan (Mozo)Documento4 pagine194 Ferrer v. Sandiganbayan (Mozo)JUAN MIGUEL MOZONessuna valutazione finora
- Result FileDocumento42 pagineResult Fileclaudio pizziniNessuna valutazione finora
- EthicsJustice-And-Fairness Finals ReportingDocumento38 pagineEthicsJustice-And-Fairness Finals ReportingannahsenemNessuna valutazione finora
- Family Law Weekly AssignmentDocumento7 pagineFamily Law Weekly AssignmentPrakriti RainsNessuna valutazione finora
- HWSG News 5th June, 2011 IssueDocumento4 pagineHWSG News 5th June, 2011 IssuehmarwelfaresocietyghyNessuna valutazione finora
- The Historical Development of TrademarksDocumento3 pagineThe Historical Development of Trademarksmarikit.marit100% (1)
- Sworn Statement Not BlacklistedDocumento2 pagineSworn Statement Not BlacklistedpatrickkayeNessuna valutazione finora
- Noble Roman's Defendants' Answer, Affirmative Defenses, and CounterclaimDocumento22 pagineNoble Roman's Defendants' Answer, Affirmative Defenses, and CounterclaimKenan FarrellNessuna valutazione finora
- Reaction Paper Educ 410Documento1 paginaReaction Paper Educ 410Anamie Dela Cruz ParoNessuna valutazione finora
- ECB ManagersDocumento3 pagineECB Managersnikitas666Nessuna valutazione finora
- Poverty Alleviation and Distribution: Villanueva E. - Escobio - Morente - Roa - Orantia - PincasDocumento45 paginePoverty Alleviation and Distribution: Villanueva E. - Escobio - Morente - Roa - Orantia - PincasTin RobisoNessuna valutazione finora
- Sango bh.0Documento11 pagineSango bh.0rayyanrashid.neNessuna valutazione finora
- CIAC Jurisdiction Over Construction DisputeDocumento3 pagineCIAC Jurisdiction Over Construction DisputeRoland Joseph MendozaNessuna valutazione finora
- R0404 BD040722 QuippDocumento5 pagineR0404 BD040722 QuippLovely Jane MorenoNessuna valutazione finora
- Rosebud SIoux Tribe Criminal Offense CodeDocumento5 pagineRosebud SIoux Tribe Criminal Offense CodeOjinjintka NewsNessuna valutazione finora
- Bob Marley's Message of PeaceDocumento3 pagineBob Marley's Message of PeaceMargaret The WinnerNessuna valutazione finora
- RFBT 03 SalesDocumento10 pagineRFBT 03 SalesShiela Marie Sta AnaNessuna valutazione finora
- Laws Regulating Transportation EstablishmentDocumento18 pagineLaws Regulating Transportation Establishmentletisha BellyNessuna valutazione finora
- The Rundown 11/25/13Documento3 pagineThe Rundown 11/25/13American Enterprise InstituteNessuna valutazione finora
- Letter of AgreementDocumento5 pagineLetter of AgreementIndra YurmanNessuna valutazione finora
- Laws Related To Family PlanningDocumento14 pagineLaws Related To Family PlanningMA. JYRELL BONITONessuna valutazione finora
- VHL University of Applied Sciences Regulation For Enrolment 2019-2020Documento14 pagineVHL University of Applied Sciences Regulation For Enrolment 2019-2020Abraham BairuNessuna valutazione finora