Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Chap-11 UDP
Caricato da
dineshchachanCopyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Chap-11 UDP
Caricato da
dineshchachanCopyright:
Formati disponibili
Chapter 11
User Datagram
Protocol
Objectives
Upon completion you will be able to:
Be able to explain process-to-process communication
Know the format of a UDP user datagram
Be able to calculate a UDP checksum
Understand the operation of UDP
Know when it is appropriate to use UDP
Understand the modules in a UDP package
TCP/IP Protocol Suite 1
Figure 11.1 Position of UDP in the TCP/IP protocol suite
TCP/IP Protocol Suite 2
11.1 PROCESS-TO-PROCESS
COMMUNICATION
Before we examine UDP, we must first understand host-to-host
communication and process-to-process communication and the
difference between them.
The topics discussed in this section include:
Port Numbers
Socket Addresses
TCP/IP Protocol Suite 3
Figure 11.2 UDP versus IP
TCP/IP Protocol Suite 4
Figure 11.3 Port numbers
TCP/IP Protocol Suite 5
Figure 11.4 IP addresses versus port numbers
TCP/IP Protocol Suite 6
Figure 11.5 ICANN ranges
TCP/IP Protocol Suite 7
Note:
The well-known port numbers are less
than 1024.
TCP/IP Protocol Suite 8
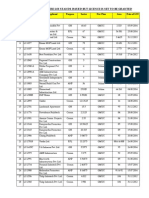
Table 11.1 Well-known ports used with UDP
TCP/IP Protocol Suite 9
Example 1
In UNIX, the well-known ports are stored in a file called
/etc/services. Each line in this file gives the name of the server
and the well-known port number. We can use the grep utility to
extract the line corresponding to the desired application. The
following shows the port for TFTP. Note TFTP can use port 69
on either UDP or TCP.
$ grep tftp /etc/services
tftp 69/tcp
tftp 69/udp
See Next Slide
TCP/IP Protocol Suite 10
Example 1 (Continued)
SNMP uses two port numbers (161 and 162), each for a
different purpose, as we will see in Chapter 21.
$ grep snmp /etc/services
snmp 161/tcp #Simple Net Mgmt Proto
snmp 161/udp #Simple Net Mgmt Proto
snmptrap 162/udp #Traps for SNMP
TCP/IP Protocol Suite 11
Figure 11.6 Socket address
TCP/IP Protocol Suite 12
11.2 USER DATAGRAM
UDP packets are called user datagrams and have a fixed-size header of 8
bytes.
TCP/IP Protocol Suite 13
Figure 11.7 User datagram format
TCP/IP Protocol Suite 14
Note:
UDP length =
IP length IP headers length
TCP/IP Protocol Suite 15
11.3 CHECKSUM
UDP checksum calculation is different from the one for IP and ICMP.
Here the checksum includes three sections: a pseudoheader, the UDP
header, and the data coming from the application layer.
The topics discussed in this section include:
Checksum Calculation at Sender
Checksum Calculation at Receiver
Optional Use of the Checksum
TCP/IP Protocol Suite 16
Figure 11.8 Pseudoheader for checksum calculation
TCP/IP Protocol Suite 17
Figure 11.9 Checksum calculation of a simple UDP user datagram
TCP/IP Protocol Suite 18
11.4 UDP OPERATION
UDP uses concepts common to the transport layer. These concepts will be
discussed here briefly, and then expanded in the next chapter on the TCP
protocol.
The topics discussed in this section include:
Connectionless Services
Flow and Error Control
Encapsulation and Decapsulation
Queuing
Multiplexing and Demultiplexing
TCP/IP Protocol Suite 19
Figure 11.10 Encapsulation and decapsulation
TCP/IP Protocol Suite 20
Figure 11.11 Queues in UDP
TCP/IP Protocol Suite 21
Figure 11.12 Multiplexing and demultiplexing
TCP/IP Protocol Suite 22
11.5 USE OF UDP
We discuss some uses of the UDP protocol in this section.
TCP/IP Protocol Suite 23
11.6 UDP PACKAGE
To show how UDP handles the sending and receiving of UDP packets,
we present a simple version of the UDP package. The UDP package
involves five components: a control-block table, input queues, a control-
block module, an input module, and an output module.
The topics discussed in this section include:
Control-Block Table
Input Queues
Control-Block Module
Input Module
Output Module
TCP/IP Protocol Suite 24
Figure 11.13 UDP design
TCP/IP Protocol Suite 25
Table 11.2 The control-block table at the beginning of examples
TCP/IP Protocol Suite 26
Example 2
The first activity is the arrival of a user datagram with
destination port number 52,012. The input module searches for
this port number and finds it. Queue number 38 has been
assigned to this port, which means that the port has been
previously used. The input module sends the data to queue 38.
The control-block table does not change.
TCP/IP Protocol Suite 27
Example 3
After a few seconds, a process starts. It asks the operating
system for a port number and is granted port number 52,014.
Now the process sends its ID (4,978) and the port number to
the control-block module to create an entry in the table. The
module takes the first FREE entry and inserts the information
received. The module does not allocate a queue at this moment
because no user datagrams have arrived for this destination
(see Table 11.3).
See Next Slide
TCP/IP Protocol Suite 28
Table 11.3 Control-block table after Example 3
TCP/IP Protocol Suite 29
Example 4
A user datagram now arrives for port 52,011. The input module
checks the table and finds that no queue has been allocated for
this destination since this is the first time a user datagram has
arrived for this destination. The module creates a queue and
gives it a number (43). See Table 11.4.
See Next Slide
TCP/IP Protocol Suite 30
Table 11.4 Control-block after Example 4
TCP/IP Protocol Suite 31
Example 5
After a few seconds, a user datagram arrives for port 52,222.
The input module checks the table and cannot find an entry for
this destination. The user datagram is dropped and a request is
made to ICMP to send an unreachable port message to the
source.
TCP/IP Protocol Suite 32
Potrebbero piacerti anche
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (119)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (399)
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (587)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2219)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (890)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- 6th Central Pay Commission Salary CalculatorDocumento15 pagine6th Central Pay Commission Salary Calculatorrakhonde100% (436)
- Pentest Command Tools Gpen Based Cheat SheetDocumento10 paginePentest Command Tools Gpen Based Cheat Sheetlbb1987Nessuna valutazione finora
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (73)
- SureSigns VS4 Monitor Network Configuration Guide Release A.06Documento78 pagineSureSigns VS4 Monitor Network Configuration Guide Release A.06pericopepe100% (2)
- Ports Used On OnGuard SystemDocumento1 paginaPorts Used On OnGuard Systemositomx100% (1)
- Lab8 Sequential Lab Router ConfigDocumento6 pagineLab8 Sequential Lab Router ConfigmedjacNessuna valutazione finora
- Natural Therapies EndometriosisDocumento13 pagineNatural Therapies EndometriosispjsbooksNessuna valutazione finora
- Natural Therapies EndometriosisDocumento13 pagineNatural Therapies EndometriosispjsbooksNessuna valutazione finora
- PCNSA Exam QuestionsDocumento35 paginePCNSA Exam QuestionsDiego Fernando Bedoya CamachoNessuna valutazione finora
- Apply for Philippine VisaDocumento3 pagineApply for Philippine VisadineshchachanNessuna valutazione finora
- Socket Programing GuideDocumento101 pagineSocket Programing GuideAnurag AggarwalNessuna valutazione finora
- Free Lancing WebsiteDocumento1 paginaFree Lancing WebsitedineshchachanNessuna valutazione finora
- (Ebook) Understanding General Packet Radio Service (GPRS)Documento32 pagine(Ebook) Understanding General Packet Radio Service (GPRS)chrispeweNessuna valutazione finora
- LLC 44 064v13Documento66 pagineLLC 44 064v13dineshchachanNessuna valutazione finora
- WBspeechCodec - 26 - 201v080200pDocumento25 pagineWBspeechCodec - 26 - 201v080200pdineshchachanNessuna valutazione finora
- Not FreedDocumento1 paginaNot FreeddineshchachanNessuna valutazione finora
- Cuisine RegaleDocumento29 pagineCuisine RegaledineshchachanNessuna valutazione finora
- Automatic Neighbour Relation ManagementDocumento15 pagineAutomatic Neighbour Relation ManagementdineshchachanNessuna valutazione finora
- Licence LOI Issued CasesDocumento3 pagineLicence LOI Issued CasesdineshchachanNessuna valutazione finora
- SON Features PDFDocumento23 pagineSON Features PDFSanjeev KumarNessuna valutazione finora
- 36 300v11Documento222 pagine36 300v11dineshchachanNessuna valutazione finora
- 36 300v080000Documento84 pagine36 300v080000dineshchachanNessuna valutazione finora
- List FDA Rejected Ramdev ProductsDocumento1 paginaList FDA Rejected Ramdev ProductsdineshchachanNessuna valutazione finora
- Lte Attach PDFDocumento6 pagineLte Attach PDFNitin KatariaNessuna valutazione finora
- Payment Plan 26 8 10Documento1 paginaPayment Plan 26 8 10dineshchachanNessuna valutazione finora
- Lte Son Self-Configuration Plug&PlayDocumento4 pagineLte Son Self-Configuration Plug&PlaydineshchachanNessuna valutazione finora
- SON Features PDFDocumento23 pagineSON Features PDFSanjeev KumarNessuna valutazione finora
- LAB 03 - Configuring Inter VLAN TrunkingDocumento29 pagineLAB 03 - Configuring Inter VLAN TrunkingJhorel Axel Ticlavilca VillazanteNessuna valutazione finora
- ExchangeDocumento4 pagineExchangeMarcos SachiNessuna valutazione finora
- Snort Config and RulesDocumento15 pagineSnort Config and RulesNehal RizviNessuna valutazione finora
- 06-Chapter6 BGP ConfigurationDocumento79 pagine06-Chapter6 BGP ConfigurationRandy DookheranNessuna valutazione finora
- Read Extreme Policies and SecurityDocumento803 pagineRead Extreme Policies and Securitydibyam baralNessuna valutazione finora
- CSC 3116 Computer Networks: Rifat Tasnim AnannyaDocumento14 pagineCSC 3116 Computer Networks: Rifat Tasnim AnannyaMike HeisenbergNessuna valutazione finora
- Protocol Internet Packetized Routed Networked: IP May Refer To Any of The FollowingDocumento3 pagineProtocol Internet Packetized Routed Networked: IP May Refer To Any of The FollowingJuliusUbasNessuna valutazione finora
- Study of DVMRP, MOSPF, CBT, PIM, MBONE, EIGRP, CIDRDocumento6 pagineStudy of DVMRP, MOSPF, CBT, PIM, MBONE, EIGRP, CIDRnishiNessuna valutazione finora
- Native VLAN and Default VLANDocumento6 pagineNative VLAN and Default VLANAaliyah WinkyNessuna valutazione finora
- RedDocumento2 pagineRedGalo MariduenaNessuna valutazione finora
- DNS Overview and WorkingDocumento27 pagineDNS Overview and WorkingraysieusNessuna valutazione finora
- DGTL-BRKCLD-3440-Multicloud Networking - Design and DeploymentDocumento225 pagineDGTL-BRKCLD-3440-Multicloud Networking - Design and Deploymentpaulo_an7381Nessuna valutazione finora
- National Institute of Technology: Jalandhar, PunjabDocumento45 pagineNational Institute of Technology: Jalandhar, PunjabGaurav SachdevaNessuna valutazione finora
- Optipoint 410 EntryDocumento247 pagineOptipoint 410 EntryFonesul TelecomNessuna valutazione finora
- Cisco Confidential Chapter ReviewDocumento8 pagineCisco Confidential Chapter Reviewxcvbvcb cvbcvbvcNessuna valutazione finora
- Signalling Issues in ImsDocumento18 pagineSignalling Issues in Imssali2801Nessuna valutazione finora
- Troubleshoot Security Intelligence Feed Update Failures On The FireSIGHT Management CenterDocumento5 pagineTroubleshoot Security Intelligence Feed Update Failures On The FireSIGHT Management CenterWafikNessuna valutazione finora
- Datasheet: Ethernet/Ip™ To Modbus Serial Communication GatewayDocumento3 pagineDatasheet: Ethernet/Ip™ To Modbus Serial Communication GatewayCarlos Francisco Diaz PozzuoliNessuna valutazione finora
- DLink Product Guide PDFDocumento44 pagineDLink Product Guide PDFHelmy HtssNessuna valutazione finora
- 128037-CUBE ASR HA Application Note Pamistry v2Documento29 pagine128037-CUBE ASR HA Application Note Pamistry v2Karma_2006Nessuna valutazione finora
- Cisco IOS Security Command Reference-Commands S To ZDocumento1.426 pagineCisco IOS Security Command Reference-Commands S To ZscorcdNessuna valutazione finora
- BSCI Module 4-Lesson 3-EditedDocumento33 pagineBSCI Module 4-Lesson 3-EditedAlan LisiNessuna valutazione finora
- Basic Packet Switching TrainingDocumento28 pagineBasic Packet Switching TrainingMaxamed YusufNessuna valutazione finora
- Integrating Lync Server and CUCMDocumento37 pagineIntegrating Lync Server and CUCMrakgautam1980Nessuna valutazione finora
- Paxson Spring 2017 CS 161 Computer Security Final Exam: (Last) (First)Documento35 paginePaxson Spring 2017 CS 161 Computer Security Final Exam: (Last) (First)Hassanein Al-hadadNessuna valutazione finora