Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Securing Information Systems: Video Cases
Caricato da
Bazla BzDescrizione originale:
Titolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Securing Information Systems: Video Cases
Caricato da
Bazla BzCopyright:
Formati disponibili
Securing Information Systems
VIDEO CASES
Case 1: IBM Zone Trusted Information Channel (ZTIC)
Case 2: Open ID and Web Security
Instructional Video 1: The Quest for Identity 2.0
Instructional Video 2: Identity 2.0
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Chapter 8
Why are information systems vulnerable to destruction, error,
and abuse?
What is the business value of security and control?
What are the components of an organizational framework for
security and control?
What are the most important tools and technologies for
safeguarding information resources?
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Learning Objectives
Facebook worlds largest social network
Problem Identity theft and malicious software
Examples:
2009 18-month hacker scam for passwords, resulted in Trojan
horse download that stole financial data
Dec 2008 Koobface worm
May 2010 Spam campaigned aimed at stealing logins
Illustrates: Types of security attacks facing consumers
Demonstrates: Ubiquity of hacking, malicious software
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Youre on Facebook? Watch Out!
Security:
Policies, procedures and technical measures used to prevent
unauthorized access, alteration, theft, or physical damage to
information systems
Controls:
Methods, policies, and organizational procedures that ensure
safety of organizations assets; accuracy and reliability of its
accounting
records;
and
operational
adherence
to
management standards
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
System Vulnerability and Abuse
Why systems are vulnerable
Accessibility of networks
Hardware problems (breakdowns,
damage from improper use or crime)
configuration
errors,
Software problems (programming errors, installation errors,
unauthorized changes)
Disasters
Use of networks/computers outside of firms control
Loss and theft of portable devices
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
System Vulnerability and Abuse
System Vulnerability and Abuse
FIGURE 8-1
The architecture of a Web-based application typically includes a Web client, a
server, and corporate information systems linked to databases. Each of these
components presents security challenges and vulnerabilities. Floods, fires,
power failures, and other electrical problems can cause disruptions at any point
in the network.
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
CONTEMPORARY SECURITY CHALLENGES AND VULNERABILITIES
Internet vulnerabilities
Network open to anyone
Size of Internet means abuses can have wide impact
Use of fixed Internet addresses with cable or DSL modems
creates fixed targets hackers
Unencrypted VOIP
E-mail, P2P, IM
Interception
Attachments with malicious software
Transmitting trade secrets
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
System Vulnerability and Abuse
System Vulnerability and Abuse
Radio frequency bands easy to scan
SSIDs (service set identifiers)
Identify access points
Broadcast multiple times
War driving
Eavesdroppers drive by buildings and try to detect
SSID and gain access to network and resources
WEP (Wired Equivalent Privacy)
Security standard for 802.11; use is optional
Uses shared password for both users and access point
Users often fail to implement WEP or stronger systems
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Wireless security challenges
System Vulnerability and Abuse
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
WI-FI
SECURITY
CHALLENGES
Many Wi-Fi networks
can
be
penetrated
easily
by
intruders
using sniffer programs
to obtain an address to
access the resources of
a
network
without
authorization.
FIGURE 8-2
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Malware (malicious software)
Viruses
Rogue software program that attaches itself to other software
programs or data files in order to be executed
Worms
Independent computer programs that copy themselves from
one computer to other computers over a network.
Trojan horses
Software program that appears to be benign but then does
something other than expected.
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
System Vulnerability and Abuse
Malware (cont.)
SQL injection attacks
Hackers submit data to Web forms that exploits sites
unprotected software and sends rogue SQL query to database
Spyware
Small programs install themselves surreptitiously on
computers to monitor user Web surfing activity and serve up
advertising
Key loggers
Record every keystroke on computer to steal serial numbers,
passwords, launch Internet attacks
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
System Vulnerability and Abuse
Hackers and computer crime
Hackers vs. crackers
Activities include
System intrusion
System damage
Cybervandalism
Intentional disruption, defacement, destruction of Web
site or corporate information system
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
System Vulnerability and Abuse
Spoofing
Misrepresenting oneself by using fake e-mail addresses or
masquerading as someone else
Redirecting Web link to address different from intended one,
with site masquerading as intended destination
Sniffer
Eavesdropping program that monitors information traveling
over network
Enables hackers to steal proprietary information such as email, company files, etc.
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
System Vulnerability and Abuse
Denial-of-service attacks (DoS)
Flooding server with thousands of false requests to crash the
network.
Distributed denial-of-service attacks (DDoS)
Use of numerous computers to launch a DoS
Botnets
Networks of zombie PCs infiltrated by bot malware
Worldwide, 6 - 24 million computers serve as zombie PCs in
thousands of botnets
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
System Vulnerability and Abuse
Computer crime
Defined as any violations of criminal law that involve a
knowledge of computer technology for their perpetration,
investigation, or prosecution
Computer may be target of crime, e.g.:
Breaching confidentiality of protected computerized data
Accessing a computer system without authority
Computer may be instrument of crime, e.g.:
Theft of trade secrets
Using e-mail for threats or harassment
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
System Vulnerability and Abuse
Identity theft
Theft of personal Information (social security id, drivers
license or credit card numbers) to impersonate someone else
Phishing
Setting up fake Web sites or sending e-mail messages that
look like legitimate businesses to ask users for confidential
personal data.
Evil twins
Wireless networks that pretend to offer trustworthy Wi-Fi
connections to the Internet
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
System Vulnerability and Abuse
Pharming
Redirects users to a bogus Web page, even when individual
types correct Web page address into his or her browser
Click fraud
Occurs when individual or computer program fraudulently
clicks on online ad without any intention of learning more
about the advertiser or making a purchase
Cyberterrorism and Cyberwarfare
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
System Vulnerability and Abuse
Internal threats: employees
Security threats often originate inside an organization
Inside knowledge
Sloppy security procedures
User lack of knowledge
Social engineering:
Tricking employees into revealing their passwords by
pretending to be legitimate members of the company in need
of information
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
System Vulnerability and Abuse
Software vulnerability
Commercial software contains flaws that create security
vulnerabilities
Hidden bugs (program code defects)
Zero defects cannot be achieved because complete
testing is not possible with large programs
Flaws can open networks to intruders
Patches
Vendors release small pieces of software to repair flaws
However exploits often created faster than patches be
released and implemented
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
System Vulnerability and Abuse
System Vulnerability and Abuse
Read the Interactive Session and discuss the following questions
What management, organization, and technology factors were
responsible for McAfees software problem?
What was the business impact of this software problem, both for
McAfee and for its customers?
If you were a McAfee enterprise customer, would you consider
McAfees response to the problem be acceptable? Why or why
not?
What should McAfee do in the future to avoid similar problems?
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
WHEN ANTIVIRUS SOFTWARE CRIPPLES YOUR COMPUTERS
Failed computer systems can lead to significant or total loss of
business function
Firms now more vulnerable than ever
Confidential personal and financial data
Trade secrets, new products, strategies
A security breach may cut into firms market value almost
immediately
Inadequate security and controls also bring forth issues of
liability
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Business Value of Security and Control
Legal and regulatory requirements
management and privacy protection
for
electronic
records
HIPAA: Medical security and privacy rules and procedures
Gramm-Leach-Bliley Act: Requires financial institutions to
ensure the security and confidentiality of customer data
Sarbanes-Oxley Act: Imposes responsibility on companies and
their management to safeguard the accuracy and integrity of
financial information that is used internally and released
externally
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Business Value of Security and Control
Electronic evidence
Evidence for white collar crimes often in digital form
Data on computers, e-mail, instant messages, e-commerce
transactions
Proper control of data can save time and money when
responding to legal discovery request
Computer forensics:
Scientific
collection,
examination,
authentication,
preservation, and analysis of data from computer storage
media for use as evidence in court of law
Includes recovery of ambient and hidden data
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Business Value of Security and Control
Information systems controls
Manual and automated controls
General and application controls
General controls
Govern design, security, and use of computer programs and
security of data files in general throughout organizations
information technology infrastructure.
Apply to all computerized applications
Combination of hardware, software, and manual procedures to
create overall control environment
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Establishing a Framework for Security
and Control
Establishing a Framework for Security
and Control
Types of general controls
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Software controls
Hardware controls
Computer operations controls
Data security controls
Implementation controls
Administrative controls
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Prentice Hall 2011
Application controls
Specific controls unique to each computerized application,
such as payroll or order processing
Include both automated and manual procedures
Ensure that only authorized data are
accurately processed by that application
Include:
Input controls
Processing controls
Output controls
Management Information Systems: Managing the Digital Firm, 12e
completely
Authors: Kenneth C. Laudon and Jane P. Laudon
and
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Establishing a Framework for Security
and Control
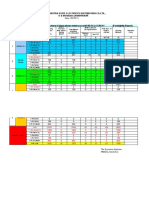
Risk assessment: Determines level of risk to firm if specific
activity or process is not properly controlled
Types of threat
Probability of occurrence during year
Potential losses, value of threat
Expected annual loss
EXPECTED
ANNUAL
LOSS
PROBABILI
TY
LOSS RANGE
(AVG)
Power
failure
30%
$5K - $200K
($102,500)
Embezzlem
ent
5%
$1K - $50K
($25,500)
User error
98%
Authors:
Kenneth C. Laudon and Jane P.$19,698
Laudon
$200
- $40K
EXPOSURE
Management Information Systems: Managing the Digital Firm, 12e
$30,750
$1,275
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Establishing a Framework for Security
and Control
Security policy
Ranks information risks, identifies
acceptable security goals, and identifies
mechanisms for achieving these goals
Drives other policies
Acceptable use policy (AUP)
Defines acceptable uses of firms information resources
and computing equipment
Authorization policies
Determine differing levels of user access to information
assets
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Establishing a Framework for Security
and Control
Identity management
Business processes and tools to identify valid users of system
and control access
Identifies and authorizes different categories of users
Specifies which portion of system users can access
Authenticating users and protects identities
Identity management systems
Captures access rules for different levels of users
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Establishing a Framework for Security
and Control
System Vulnerability and Abuse
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
SECURITY
PROFILES FOR
A PERSONNEL
SYSTEM
These two examples
represent two security
profiles or data security
patterns that might be
found in a personnel
system. Depending on
the security profile, a
user
would
have
certain restrictions on
access
to
various
systems, locations, or
data in an organization.
FIGURE 8-3
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Disaster recovery planning: Devises plans for restoration of
disrupted services
Business continuity planning: Focuses on restoring business
operations after disaster
Both types of plans needed
systems
to identify firms most critical
Business impact analysis to determine impact of an outage
Management must determine which systems restored first
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Establishing a Framework for Security
and Control
MIS audit
Examines firms overall security environment as well as
controls governing individual information systems
Reviews technologies, procedures, documentation, training,
and personnel.
May even simulate disaster to test response of technology, IS
staff, other employees.
Lists and ranks all control weaknesses and estimates
probability of their occurrence.
Assesses financial and organizational impact of each threat
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Establishing a Framework for Security
and Control
System Vulnerability and Abuse
SAMPLE AUDITORS
WEAKNESSES
LIST
OF
CONTROL
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
This chart is a sample
page from a list of
control
weaknesses
that an auditor might
find in a loan system in
a
local
commercial
bank. This form helps
auditors record and
evaluate
control
weaknesses and shows
the
results
of
discussing
those
weaknesses
with
management, as well
as
any
corrective
actions
taken
by
management.
FIGURE 8-4
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Identity management software
Automates keeping track of all users and privileges
Authenticates users, protecting identities, controlling access
Authentication
Password systems
Tokens
Smart cards
Biometric authentication
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Technologies and Tools for Protecting
Information Resources
Firewall:
Combination of hardware and software that prevents
unauthorized users from accessing private networks
Technologies include:
Static packet filtering
Network address translation (NAT)
Application proxy filtering
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Technologies and Tools for Protecting
Information Resources
Technologies and Tools for Protecting
Information Resources
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
A CORPORATE FIREWALL
The firewall is placed
between
the
firms
private network and
the public Internet or
another
distrusted
network
to
protect
against unauthorized
traffic.
FIGURE 8-5
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Intrusion detection systems:
Monitor hot spots on corporate networks to detect and deter
intruders
Examines events as they are happening to discover attacks in
progress
Antivirus and antispyware software:
Checks computers for presence of malware and can often
eliminate it as well
Require continual updating
Unified threat management (UTM) systems
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Technologies and Tools for Protecting
Information Resources
Securing wireless networks
WEP security can provide some security by
Assigning unique name to networks SSID and not
broadcasting SSID
Using it with VPN technology
Wi-Fi Alliance finalized WAP2 specification, replacing WEP with
stronger standards
Continually changing keys
Encrypted authentication system with central server
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Technologies and Tools for Protecting
Information Resources
Encryption:
Transforming text or data into cipher text that cannot be read
by unintended recipients
Two methods for encryption on networks
Secure Sockets Layer (SSL) and successor Transport Layer
Security (TLS)
Secure Hypertext Transfer Protocol (S-HTTP)
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Technologies and Tools for Protecting
Information Resources
Two methods of encryption
Symmetric key encryption
Sender and receiver use single, shared key
Public key encryption
Uses two, mathematically related keys: Public key and private
key
Sender encrypts message with recipients public key
Recipient decrypts with private key
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Technologies and Tools for Protecting
Information Resources
Technologies and Tools for Protecting
Information Resources
FIGURE 8-6
A public key encryption system can be viewed as a series of public and private
keys that lock data when they are transmitted and unlock the data when they
are received. The sender locates the recipients public key in a directory and
uses it to encrypt a message. The message is sent in encrypted form over the
Internet or a private network. When the encrypted message arrives, the
recipient uses his or her private key to decrypt the data and read the message.
Management Information Systems: Managing the Digital Firm, 12e
41
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
PUBLIC KEY ENCRYPTION
Digital certificate:
Data file used to establish the identity of users and electronic
assets for protection of online transactions
Uses a trusted third party, certification authority (CA), to
validate a users identity
CA verifies users identity, stores information in CA server,
which generates encrypted digital certificate containing owner
ID information and copy of owners public key
Public key infrastructure (PKI)
Use of public key cryptography working with certificate
authority
Widely used in e-commerce
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Technologies and Tools for Protecting
Information Resources
Technologies and Tools for Protecting
Information Resources
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
DIGITAL
CERTIFICATES
Digital certificates help
establish the identity of
people or electronic
assets. They protect
online transactions by
providing
secure,
encrypted,
online
communication.
FIGURE 8-7
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Ensuring system availability
Online transaction processing requires 100% availability, no
downtime
Fault-tolerant computer systems
For continuous availability, e.g. stock markets
Contain redundant hardware, software, and power supply
components that create an environment that
provides
continuous, uninterrupted service
High-availability computing
Helps recover quickly from crash
Minimizes, does not eliminate downtime
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Technologies and Tools for Protecting
Information Resources
Recovery-oriented computing
Designing systems that recover quickly with capabilities to
help operators pinpoint and correct of faults in multicomponent systems
Controlling network traffic
Deep packet inspection (DPI)
Video and music blocking
Security outsourcing
Managed security service providers (MSSPs)
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Technologies and Tools for Protecting
Information Resources
Technologies and Tools for Protecting
Information Resources
Security in the cloud
Responsibility for security resides with company owning the
data
Firms must ensure providers provides adequate protection
Service level agreements (SLAs)
Securing mobile platforms
Security policies should include and cover any special
requirements for mobile devices
E.g. updating smart phones with latest security
patches, etc.
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Technologies and Tools for Protecting
Information Resources
Read the Interactive Session and discuss the following questions
What security and control problems are described in this case?
What people, organization, and technology factors contribute to
these problems?
How secure is cloud computing? Explain your answer.
If you were in charge of your companys information systems
department, what issues would you want to clarify with
prospective vendors?
Would you entrust your corporate systems to a cloud computing
provider? Why or why not?
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
HOW SECURE IS THE CLOUD?
Ensuring software quality
Software metrics: Objective assessments of system in form of
quantified measurements
Number of transactions
Online response time
Payroll checks printed per hour
Known bugs per hundred lines of code
Early and regular testing
Walkthrough: Review of specification or design document by
small group of qualified people
Debugging: Process by which errors are eliminated
Management Information Systems: Managing the Digital Firm, 12e
Authors: Kenneth C. Laudon and Jane P. Laudon
Copyright 2013 Dorling Kindersley (India) Pvt. Ltd.
Technologies and Tools for Protecting
Information Resources
Potrebbero piacerti anche
- Where Is Dell VulnerableDocumento7 pagineWhere Is Dell Vulnerableapu043Nessuna valutazione finora
- BB309 - Sme - Asm - Assignment Case Study - Jan11Documento5 pagineBB309 - Sme - Asm - Assignment Case Study - Jan11Tony LinNessuna valutazione finora
- Study Material For Strategy ManagementDocumento12 pagineStudy Material For Strategy ManagementamitNessuna valutazione finora
- Assignment of Business EthicsDocumento10 pagineAssignment of Business Ethicsmehwishabid20Nessuna valutazione finora
- Databases and Information ManagementDocumento41 pagineDatabases and Information ManagementDawit GetchoNessuna valutazione finora
- Management Information Systems: Managing The Digital Firm, 12e Authors: Kenneth C. Laudon and Jane P. LaudonDocumento40 pagineManagement Information Systems: Managing The Digital Firm, 12e Authors: Kenneth C. Laudon and Jane P. Laudonhello everyoneNessuna valutazione finora
- Admsci 10 00060Documento19 pagineAdmsci 10 00060hexenejenineNessuna valutazione finora
- Chapter 1Documento35 pagineChapter 1hello everyoneNessuna valutazione finora
- Management Information Systems: Managing The Digital Firm, 12e Authors: Kenneth C. Laudon and Jane P. LaudonDocumento36 pagineManagement Information Systems: Managing The Digital Firm, 12e Authors: Kenneth C. Laudon and Jane P. Laudonhello everyoneNessuna valutazione finora
- Telecommunications, The Internet, and Wireless Technology: Video CasesDocumento40 pagineTelecommunications, The Internet, and Wireless Technology: Video CasesBazla BzNessuna valutazione finora
- Unethical Labor PracticesDocumento11 pagineUnethical Labor Practicesmuqtharmaharoof0% (1)
- Chapter 13Documento45 pagineChapter 13MEDISHETTY MANICHANDANANessuna valutazione finora
- Introduction To E-Business and E-CommerceDocumento22 pagineIntroduction To E-Business and E-CommerceSakibMDShafiuddinNessuna valutazione finora
- Course Outline For MIS 2013 - V1Documento5 pagineCourse Outline For MIS 2013 - V1Shiva Kumar DunaboinaNessuna valutazione finora
- Laudon Traver 3E Chapter2 Final 2Documento41 pagineLaudon Traver 3E Chapter2 Final 2নাজমুল হাসান দিনানNessuna valutazione finora
- Module Handbook Digital Landscape 2021 2022Documento12 pagineModule Handbook Digital Landscape 2021 2022Saba MalikNessuna valutazione finora
- Batch Processing and in Real-Time (Or Online) Processing. Pizza Hut in Doing Trasnsaksi AlreadyDocumento4 pagineBatch Processing and in Real-Time (Or Online) Processing. Pizza Hut in Doing Trasnsaksi AlreadySumbul ZehraNessuna valutazione finora
- What Technologies Are Used in UPSDocumento11 pagineWhat Technologies Are Used in UPSranvirsingh760% (1)
- Strategy Management Assignment TomTom Case Study 2013Documento15 pagineStrategy Management Assignment TomTom Case Study 2013Kenneth MoNessuna valutazione finora
- Business EthicsDocumento9 pagineBusiness EthicsHamshavathini YohoratnamNessuna valutazione finora
- Ethical Case Study: Nike: by Jaycie, Kayley, & ShannonDocumento13 pagineEthical Case Study: Nike: by Jaycie, Kayley, & ShannonsorryimanonimNessuna valutazione finora
- Ethics CaseDocumento10 pagineEthics CaseAayush AkhauriNessuna valutazione finora
- Lse-Laudon Mis12 Ppt04Documento12 pagineLse-Laudon Mis12 Ppt04gul_e_sabaNessuna valutazione finora
- Chapter 1 (Compatibility Mode)Documento29 pagineChapter 1 (Compatibility Mode)Moh BhaNessuna valutazione finora
- Unethical Business PracticesDocumento14 pagineUnethical Business PracticesTayyabaNessuna valutazione finora
- Levy6e - Chap15-Retail Communcation MixDocumento23 pagineLevy6e - Chap15-Retail Communcation MixNurzakiah DaulayNessuna valutazione finora
- Laudon-Traver Ec12 PPT CH04Documento53 pagineLaudon-Traver Ec12 PPT CH04Quỳnh Lê NhưNessuna valutazione finora
- Sample Case Study - LOW - COST - STRATEGYDocumento11 pagineSample Case Study - LOW - COST - STRATEGYbernie011Nessuna valutazione finora
- SVOD in India: Kilaru Megha Bandhav - Sec-E - 240Documento3 pagineSVOD in India: Kilaru Megha Bandhav - Sec-E - 240Megha Bandhav Kilaru100% (1)
- CRM On BergerDocumento25 pagineCRM On BergerSakhawat Hossain0% (1)
- CVP Creative Brief WebsiteDocumento6 pagineCVP Creative Brief WebsitetomwalkerNessuna valutazione finora
- CSR and BusinessesDocumento14 pagineCSR and BusinessesMahen RagNessuna valutazione finora
- Mcdonald Grant Value Propositions White Paper January 2016Documento16 pagineMcdonald Grant Value Propositions White Paper January 2016goutham sivasailamNessuna valutazione finora
- Information Systems in The Enterprise: © 2006 by Prentice HallDocumento18 pagineInformation Systems in The Enterprise: © 2006 by Prentice HallShivani GautamNessuna valutazione finora
- ENT300 Case Study Outline - LatestDocumento2 pagineENT300 Case Study Outline - LatestHasni Abdul RahimNessuna valutazione finora
- 1.ethics & BusinessDocumento6 pagine1.ethics & BusinessCamae LamigoNessuna valutazione finora
- HRM Reference NotesDocumento29 pagineHRM Reference NotesSaher KapdiNessuna valutazione finora
- BusinessEthics DilemaasDocumento7 pagineBusinessEthics Dilemaasmi_owextoNessuna valutazione finora
- Foundations of Business Intelligence: Databases and Information ManagementDocumento40 pagineFoundations of Business Intelligence: Databases and Information ManagementBazla BzNessuna valutazione finora
- Social Media Marketing: Emarketing Excellence by Dave Chaffey and PR SmithDocumento46 pagineSocial Media Marketing: Emarketing Excellence by Dave Chaffey and PR SmithHaris KhanNessuna valutazione finora
- SM Midterm Descriptive NN Campus FA-20Documento5 pagineSM Midterm Descriptive NN Campus FA-20Noshaba KashifNessuna valutazione finora
- Laudon-Traver Ec11 PPT Ch01 ReviewedDocumento10 pagineLaudon-Traver Ec11 PPT Ch01 ReviewedDinesh NathanNessuna valutazione finora
- Leveraging Secondary Brand Associations To Build Brand EquityDocumento18 pagineLeveraging Secondary Brand Associations To Build Brand EquityJoy Loraine ConananNessuna valutazione finora
- Managing Ethics in Business OrganizationsDocumento32 pagineManaging Ethics in Business OrganizationsAbienash ThangavelNessuna valutazione finora
- Chapter 8 - Securing Information SystemsDocumento28 pagineChapter 8 - Securing Information SystemsIrvan 69Nessuna valutazione finora
- Chapter 1 Introduction To Human Resource ManagementDocumento69 pagineChapter 1 Introduction To Human Resource ManagementMurthyNessuna valutazione finora
- HRMDocumento39 pagineHRMFatin AfifaNessuna valutazione finora
- Global E-Business and Collaboration: Video CasesDocumento38 pagineGlobal E-Business and Collaboration: Video CasesBazla BzNessuna valutazione finora
- E-Commerce: Digital Markets, Digital GoodsDocumento39 pagineE-Commerce: Digital Markets, Digital GoodsMahnoor KhalidNessuna valutazione finora
- Course Title: Principle of Management Course Id: Mgt-201 Section: 5 Semester: Autumn 2020 SUBMITTED TO: Dr. Nazmunnesa Mahtab Organization: SailorsDocumento11 pagineCourse Title: Principle of Management Course Id: Mgt-201 Section: 5 Semester: Autumn 2020 SUBMITTED TO: Dr. Nazmunnesa Mahtab Organization: SailorsAra AdibaNessuna valutazione finora
- Case Study 1 Rosier - EthicsDocumento7 pagineCase Study 1 Rosier - EthicsBenito BrowningNessuna valutazione finora
- HRD 2 Questions and AnswersDocumento24 pagineHRD 2 Questions and AnswersJoram WambuguNessuna valutazione finora
- BRM Research - NetflixDocumento13 pagineBRM Research - NetflixArpit JainNessuna valutazione finora
- Perceived Value MeasurementDocumento17 paginePerceived Value MeasurementJanuar Robin Stanley100% (1)
- Change Management 2011Documento14 pagineChange Management 2011শাওন ইসতিয়াকNessuna valutazione finora
- Volkswagen ScandalDocumento13 pagineVolkswagen Scandalapi-349167413Nessuna valutazione finora
- IS Security: Management Information Systems: Managing The Digital Firm, 12e Authors: Kenneth C. Laudon and Jane P. LaudonDocumento43 pagineIS Security: Management Information Systems: Managing The Digital Firm, 12e Authors: Kenneth C. Laudon and Jane P. LaudonMostaque Ahmed AnntoNessuna valutazione finora
- Management Information Systems: Managing The Digital Firm, 12e Authors: Kenneth C. Laudon and Jane P. LaudonDocumento15 pagineManagement Information Systems: Managing The Digital Firm, 12e Authors: Kenneth C. Laudon and Jane P. LaudonOmar Fahim Khan 1911758030Nessuna valutazione finora
- Securing Information Systems - Study Guide: System Vulnerability and AbuseDocumento12 pagineSecuring Information Systems - Study Guide: System Vulnerability and AbuseDalicia OlivierNessuna valutazione finora
- Audit and ControlDocumento42 pagineAudit and ControlFish de PaieNessuna valutazione finora
- Air Pollution - SVE - 12.6.2015 PDFDocumento34 pagineAir Pollution - SVE - 12.6.2015 PDFBazla BzNessuna valutazione finora
- Noise Pollution 2.8.2015 PDFDocumento22 pagineNoise Pollution 2.8.2015 PDFBazla BzNessuna valutazione finora
- Agro Forestry and Social Forestry..ajmal Bhai - Nov 2015 PDFDocumento28 pagineAgro Forestry and Social Forestry..ajmal Bhai - Nov 2015 PDFBazla BzNessuna valutazione finora
- Telecommunications, The Internet, and Wireless Technology: Video CasesDocumento40 pagineTelecommunications, The Internet, and Wireless Technology: Video CasesBazla BzNessuna valutazione finora
- Managing Projects: Video CasesDocumento36 pagineManaging Projects: Video CasesBazla BzNessuna valutazione finora
- Wildlife Management and ConservationDocumento64 pagineWildlife Management and ConservationBazla Bz100% (1)
- E-Commerce: Digital Markets, Digital Goods: Video CasesDocumento40 pagineE-Commerce: Digital Markets, Digital Goods: Video CasesBazla Bz100% (1)
- Foundations of Business Intelligence: Databases and Information ManagementDocumento40 pagineFoundations of Business Intelligence: Databases and Information ManagementBazla BzNessuna valutazione finora
- Leadership and Influence ProcessDocumento9 pagineLeadership and Influence ProcessBazla BzNessuna valutazione finora
- 4 - Managing Decision MakingDocumento13 pagine4 - Managing Decision MakingBazla BzNessuna valutazione finora
- Global E-Business and Collaboration: Video CasesDocumento38 pagineGlobal E-Business and Collaboration: Video CasesBazla BzNessuna valutazione finora
- 8 - Managing Human ResourceDocumento13 pagine8 - Managing Human ResourceBazla BzNessuna valutazione finora
- Planning & Strategic Management LectureDocumento30 paginePlanning & Strategic Management LectureBazla BzNessuna valutazione finora
- 5-Organisation Structure and DesignDocumento19 pagine5-Organisation Structure and DesignBazla BzNessuna valutazione finora
- Entrepreneurship Lecture on Starting New VenturesDocumento18 pagineEntrepreneurship Lecture on Starting New VenturesBazla BzNessuna valutazione finora
- 6-Organisation, Change and InnovationDocumento10 pagine6-Organisation, Change and InnovationBazla BzNessuna valutazione finora
- L3Documento22 pagineL3Bazla BzNessuna valutazione finora
- L2Documento25 pagineL2Bazla BzNessuna valutazione finora
- 4 - Managing Decision MakingDocumento13 pagine4 - Managing Decision MakingBazla BzNessuna valutazione finora
- 5-Organisation Structure and DesignDocumento19 pagine5-Organisation Structure and DesignBazla BzNessuna valutazione finora
- JOB ANALYSIS LECTUREDocumento20 pagineJOB ANALYSIS LECTUREBazla BzNessuna valutazione finora
- Ecruitment Ecture: Lecturer: Amnah Imtiaz Fall 2013 Kinnaird College For WomenDocumento19 pagineEcruitment Ecture: Lecturer: Amnah Imtiaz Fall 2013 Kinnaird College For WomenBazla BzNessuna valutazione finora
- Planning & Strategic Management LectureDocumento30 paginePlanning & Strategic Management LectureBazla BzNessuna valutazione finora
- Fix 3Documento12 pagineFix 3Eng TrNessuna valutazione finora
- Approved List of Manufacturers: Line Pipes (Carbon/Alloy Steel)Documento4 pagineApproved List of Manufacturers: Line Pipes (Carbon/Alloy Steel)Sourav Kumar GuptaNessuna valutazione finora
- AST Waveguide Switch 1 1 PDFDocumento5 pagineAST Waveguide Switch 1 1 PDFANTONIO MARMOLNessuna valutazione finora
- Iphone 6 Full schematic+IC BoardDocumento86 pagineIphone 6 Full schematic+IC BoardSIDNEY TABOADANessuna valutazione finora
- Preferred Electronic Data Interchange Standards (EDIS) For The Container IndustryDocumento51 paginePreferred Electronic Data Interchange Standards (EDIS) For The Container Industryjuan.vargas.calle6904Nessuna valutazione finora
- Form-HSE-TMR-006 Compressor, Genzet, Water Jet InspectionDocumento2 pagineForm-HSE-TMR-006 Compressor, Genzet, Water Jet Inspectionkenia infoNessuna valutazione finora
- Wind MachinesDocumento34 pagineWind Machinesjeswin johnsonNessuna valutazione finora
- Merkava Siman 3 Merkava MK 3 in IDF Service PaDocumento80 pagineMerkava Siman 3 Merkava MK 3 in IDF Service Pasacripal95% (20)
- The Future of HovercraftDocumento3 pagineThe Future of Hovercrafthovpod6214100% (4)
- Instructions Isb YlpDocumento3 pagineInstructions Isb YlpVikas BhoomaNessuna valutazione finora
- Linear Loaded Vert 80-40Documento14 pagineLinear Loaded Vert 80-40Claudio ChiconNessuna valutazione finora
- Electronically Controlled On-Demand 4WDDocumento32 pagineElectronically Controlled On-Demand 4WDjulio797Nessuna valutazione finora
- UGC MarketingDocumento16 pagineUGC MarketingJK MarketingNessuna valutazione finora
- Rigging View Modular Overland ConveyorDocumento84 pagineRigging View Modular Overland Conveyorrtyuibnm100% (2)
- Nano Particle Characterization MethodsDocumento32 pagineNano Particle Characterization MethodsVignesh Raja PNessuna valutazione finora
- Cie - Publist - 2008 Penerangan PDFDocumento11 pagineCie - Publist - 2008 Penerangan PDFAli RosidiNessuna valutazione finora
- ISN SM 50 ManualDocumento8 pagineISN SM 50 Manualsinggih bramantyoNessuna valutazione finora
- iPLON India SolutionsDocumento4 pagineiPLON India Solutionssudhirm16Nessuna valutazione finora
- Resume Mithun UpdatedDocumento7 pagineResume Mithun UpdatedmithunNessuna valutazione finora
- True/False: List of Attempted Questions and AnswersDocumento15 pagineTrue/False: List of Attempted Questions and AnswersDeepak Kumar VermaNessuna valutazione finora
- Maharashtra State Electricity Distribution Co - LTD., O & M Division, NANDURBARDocumento3 pagineMaharashtra State Electricity Distribution Co - LTD., O & M Division, NANDURBARPuru BornareNessuna valutazione finora
- Syabas Water ApplicationDocumento7 pagineSyabas Water ApplicationKen Chia0% (1)
- INDUCTORDocumento18 pagineINDUCTORBhavaniPrasadNessuna valutazione finora
- NV 24 Globe ActuatorDocumento12 pagineNV 24 Globe ActuatorRodrigo AlvesNessuna valutazione finora
- A Young Lasallian Is US Environmental ScholarDocumento1 paginaA Young Lasallian Is US Environmental ScholarDia DimayugaNessuna valutazione finora
- Evaluating SWOT's Value in Creating Actionable, Strategic IntelligenceDocumento94 pagineEvaluating SWOT's Value in Creating Actionable, Strategic IntelligenceMJFinnegan4100% (4)
- Enterprise, Innovation Creativity 2018-19 S3 CourseworkDocumento7 pagineEnterprise, Innovation Creativity 2018-19 S3 CourseworkSajidNessuna valutazione finora
- BIT3251 BIT3251 BIT3251 BIT3251 應用指南 應用指南 應用指南 應用指南: Beyond Innovation TechnologyDocumento10 pagineBIT3251 BIT3251 BIT3251 BIT3251 應用指南 應用指南 應用指南 應用指南: Beyond Innovation TechnologyHamza AbbasiNessuna valutazione finora
- West Bengal's Leather Industry OpportunitiesDocumento5 pagineWest Bengal's Leather Industry OpportunitiesDeepak AgarwalNessuna valutazione finora
- Bugcrowd Vulnerability Rating Taxonomy 1.7Documento13 pagineBugcrowd Vulnerability Rating Taxonomy 1.7junior108Nessuna valutazione finora