Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Imt 94
Caricato da
Ashwani ParasharDescrizione originale:
Titolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Imt 94
Caricato da
Ashwani ParasharCopyright:
Formati disponibili
ASSIGNMENT QUESTIONS
IMT CENTRE FOR DISTANCE LEARNING GHAZIABAD Distance Learning Programme IMT-94 Network Security Threats, Attacks and Loopholes
Notes:
a. b. c. d. e. All set of assignments would be made in a single MS. Word file and would be sent together through e-mail to Subject of the e-mail of assignment submission should be UNIT-4. Students are required to clearly mention their name, roll no, and subject code in the first page of the word file. Write answers in your own words as far as possible and refrain from copying from the textbooks/handouts. Last date for assignment submission is 31st December 2011. imt.ankitfadia@gmail.com with a cc to nidhimathur@imtcdl.ac.in & shweta@imtcdl.ac.in
FIRST SET OF ASSIGNMENTS (Subjective)
Assignment (I) = 10 Marks
ASSIGNMENT-I
1. 2. 3. 4. 5. 6. 7. 8. 9. 10. What is social engineering? Describe different types of social engineering attacks. Give ideas of social engineering attacks that could possibly be implemented on people around you. What is the difference between intimidation and impersonation? Describe the various types of password cracking attacks. Give three examples of weak passwords. Give three examples of strong passwords. How can an attacker crack a UNIX password? How can an attacker crack a WINDOWS password? How can an attacker crack a Screen Saver password? What are default passwords? Why are they enabled in applications by software developers?
SECOND SET OF ASSIGNMENTS (Subjective) ASSIGNMENT-II
1. 2. 3. 4. 5. 6. 7. 8. 9. 10.
Assignment (II) = 5 Marks
Describe the functions, structure and uses of the various layers of TCP/IP. What is the use of checksum on the Internet? What is the use of sequencing on the Internet? How can an attacker carry out IP spoofing? What are the four biggest challenges associated with IP spoofing? What are the advantages of proxy bouncing compared with proxy servers? How can you carry out proxy bouncing? What are trust relationships? Are they more secure than username-password authentication? What are the three steps of connection establishment and connection termination respectively? Describe the functions of the following data packets: ACK, SYN, FIN, URG and PSH. What role do DOS attacks play in IP spoofing?
THIRD SET OF ASSIGNMENTS ASSIGNMENT-III
Practical Lab Sessions = 5 Marks
1. Download the file named ankitfadia.zip from the course mailing list and crack its password. (Kindly submit the cracked password as your answer). 2. Imagine that you are a social engineer and you wish to find out the bank account number of Mr A. You decide to call the call centre of the bank and carry out a social engineering attack. How would you do it? Kindly do not actually carry out such an attack, simply submit conversation records/logs of a social engineering attack.
Potrebbero piacerti anche
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- Registration Services IndiaDocumento150 pagineRegistration Services IndiaAshwani ParasharNessuna valutazione finora
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- New Microsoft Excel WorksheetDocumento1 paginaNew Microsoft Excel WorksheetAshwani ParasharNessuna valutazione finora
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
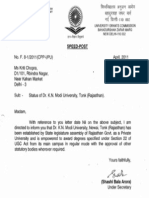
- Ugc Acknowledgement Letter To Award DegreesDocumento1 paginaUgc Acknowledgement Letter To Award DegreesAshwani ParasharNessuna valutazione finora
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (895)
- 466 - Directors On The Board of National Institute For Smart GovernmentDocumento3 pagine466 - Directors On The Board of National Institute For Smart GovernmentAshwani ParasharNessuna valutazione finora
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (400)
- To, The Deputy DirectorDocumento1 paginaTo, The Deputy DirectorAshwani ParasharNessuna valutazione finora
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- IGNOU Examination FormDocumento2 pagineIGNOU Examination FormShashank VashisthaNessuna valutazione finora
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- National Informatics Centre: Esults Ramework Ocument OFDocumento8 pagineNational Informatics Centre: Esults Ramework Ocument OFAshwani ParasharNessuna valutazione finora
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- NetVault Backup Installation Upgrade Guide v8 2 2 EnglishDocumento100 pagineNetVault Backup Installation Upgrade Guide v8 2 2 EnglishAshwani ParasharNessuna valutazione finora
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (588)
- CXC Past PapersDocumento5 pagineCXC Past Paperssarfaraz7% (14)
- Training Session On Servicenow PDFDocumento12 pagineTraining Session On Servicenow PDFZarmakoye Ango HassaneNessuna valutazione finora
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- Xyzmo OverviewDocumento4 pagineXyzmo Overviewxyzmo SIGNificantNessuna valutazione finora
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (74)
- Session 1 ICS Basics - Q and ADocumento5 pagineSession 1 ICS Basics - Q and ARocKetNessuna valutazione finora
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- SMTP Status Codes LibraryDocumento15 pagineSMTP Status Codes Libraryronycd2003Nessuna valutazione finora
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (266)
- Theme Development WordPress CodexDocumento10 pagineTheme Development WordPress CodexnezidNessuna valutazione finora
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (344)
- $daily UCE Protect IP Block ListDocumento295 pagine$daily UCE Protect IP Block ListTabish KhalidNessuna valutazione finora
- Amazon Prime Music: User CategoriesDocumento13 pagineAmazon Prime Music: User CategoriesAoun ShahNessuna valutazione finora
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2259)
- Infobip Whitepaper SMS FW Fraud DetectionDocumento6 pagineInfobip Whitepaper SMS FW Fraud DetectionRoman GrischukNessuna valutazione finora
- The Book of DojoDocumento394 pagineThe Book of DojoAnkit SanghaviNessuna valutazione finora
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- Electronic RecordsDigital Signatures & CertificatesDocumento18 pagineElectronic RecordsDigital Signatures & CertificatesSekhar PNessuna valutazione finora
- Instagram For BusinessDocumento102 pagineInstagram For BusinessMarivil V. MagdamitNessuna valutazione finora
- Allot Ac500-6000Documento4 pagineAllot Ac500-6000No SNessuna valutazione finora
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- ICTF15 PfSense IPS FirewallDocumento34 pagineICTF15 PfSense IPS FirewallkyriosNessuna valutazione finora
- Martech Landscape 2020 Martech5000 PDFDocumento1 paginaMartech Landscape 2020 Martech5000 PDFThiago BritoNessuna valutazione finora
- Integrations: A Quick Start GuideDocumento48 pagineIntegrations: A Quick Start Guidebasudeo35Nessuna valutazione finora
- Cyber CrimesDocumento5 pagineCyber CrimesShaik Abdul MuneerNessuna valutazione finora
- What Is Cpaas?: Communications Platform As A ServiceDocumento25 pagineWhat Is Cpaas?: Communications Platform As A ServiceShabir AhmedNessuna valutazione finora
- What Is Social Media MarketingDocumento5 pagineWhat Is Social Media MarketingKHILY SAXENANessuna valutazione finora
- Report 3 PDFDocumento55 pagineReport 3 PDFmanishNessuna valutazione finora
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (121)
- SEC504 C01 SANS Online Training Release Notes Rev20170403Documento1 paginaSEC504 C01 SANS Online Training Release Notes Rev20170403sdwNessuna valutazione finora
- Maintenance Mobile Offline Mode Implementation GuideDocumento27 pagineMaintenance Mobile Offline Mode Implementation GuideHajer HabibiNessuna valutazione finora
- FortiAnalyzer 7.2.1 CLI ReferenceDocumento291 pagineFortiAnalyzer 7.2.1 CLI ReferenceRenan SoaresNessuna valutazione finora
- Port NumberDocumento5 paginePort NumberarekbeeNessuna valutazione finora
- Brksec 2058Documento131 pagineBrksec 2058Rehan KhanNessuna valutazione finora
- Installation - Laravel - The PHP Framework For Web Artisans PDFDocumento7 pagineInstallation - Laravel - The PHP Framework For Web Artisans PDFMisbah QureshiNessuna valutazione finora
- Cisco Expressway Cluster Creation and Maintenance Deployment Guide X8 11 4Documento58 pagineCisco Expressway Cluster Creation and Maintenance Deployment Guide X8 11 4cciedestinyNessuna valutazione finora
- Title: Author: Date:: Anonymity Guide - How To Be Safe On The WebDocumento12 pagineTitle: Author: Date:: Anonymity Guide - How To Be Safe On The WebJáissom BarthNessuna valutazione finora
- Team Recipe CSC 413 Advanced Software Development I Spring 2015Documento24 pagineTeam Recipe CSC 413 Advanced Software Development I Spring 2015api-289537610Nessuna valutazione finora
- s3900 Series Switch Cli Reference GuideDocumento594 pagines3900 Series Switch Cli Reference GuidedavidNessuna valutazione finora
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)