Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Report
Caricato da
dream_catcher14Descrizione originale:
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Report
Caricato da
dream_catcher14Copyright:
Formati disponibili
Engineering College, Ajmer
ABSTRACT
I have done my Summer Training under HCL Career Development Centre, Jaipur Division. I have worked on ASP.NET and various pertinent technologies, used in the project provided to me to work upon, under professional guidance. The project, I worked on is based on collective information about Tours and Travels. The project aimed at providing online information to Tours and Travels anywhere in India and thus saving time and efficiency of the human resource and the system.
Engineering College, Ajmer
Chapter - 1 Introduction 1.1 Introduction of the Project:
Our project called PROTOCOL EXSEQUENDAM is responsible for showcasing the simulation of routing protocols, namely Go Back-N and Selective Repeat ARQ algorithm. It also aims to resolve shortest path problems and give a step by step visualization of Open Shortest path First Algorithm which is based on Dijkstras Algorithm. In computer networks, communication occurs between entities in different systems. An entity is anything capable of sending or receiving information. However two entities cannot simply send bit streams to each other and expect to be understood. For communication to occur, entities must agree on a protocol. A protocol is a set of rules that governs data communications. A protocol defines what is communicated, how it is communicated and when it is communicated.
1.2 Introduction of Technology Used:
1.2.1 Overview of the .Net Frame Work: The .NET framework is a new computing platform that simplifies application development in the highly distributed environment of the internet. The .NET framework is designed to full fill the following objectives: 1) To provide a consistent object oriented programming environment whether object code is stored and executed locally but internet- distributed or executed remotely.
2) To provide a code execution environment that minimizes software deployment and versioning conflicts. 3) To provide a code execution environment that guarantees safe execution of code, including code created by an unknown or semi trusted third party. 4) To provide a code execution environment that eliminates the performance problem of scripted or interpreted environments. 5)To make the developer experience consistent across widely types of application, such as windows based applications and web based applications. 6) To build all communication on industry standards to ensure that code based on the .NET framework can integrate with any other code. 1.2.2 C#.NET: C# (pronounced "C Sharp") is a multi-paradigm programming language encompassing imperative, functional, generic, object-oriented (class-based), and component-oriented programming disciplines. It
Engineering College, Ajmer
was developed by Microsoft within the .NET initiative and later approved as a standard by Ecma (ECMA-334) and ISO (ISO/IEC 23270). C# is one of the programming languages designed for the Common Language Infrastructure. C# is intended to be a simple, modern, general-purpose, object-oriented programming language. It has an object-oriented syntax based on C++. It was initially named Cool, which stood for "C-like Object Oriented Language". However, in July 2000, when Microsoft made the project public, the name of the programming language was given as C#.
Engineering College, Ajmer
Chapter - 2 Case Study 2.1 Data Link Layer:
The Data Link Layer is Layer 2 of the seven-layer OSI model of computer networking. It corresponds to, or is part of the link layer of the TCP/IP reference model. The Data Link Layer is the protocol layer which transfers data between adjacent network nodes in a wide area network or between nodes on the same local area network segment.[1] The Data Link Layer provides the functional and procedural means to transfer data between network entities and might provide the means to detect and possibly correct errors that may occur in the Physical Layer. Examples of data link protocols are Ethernet for local area networks (multi-node), the Point-to-Point Protocol (PPP), HDLC and ADCCP for point-topoint (dual-node) connections. The Data Link Layer is concerned with local delivery of frames between devices on the same LAN. Data Link frames, as these protocol data units are called, do not cross the boundaries of a local network. Inter-network routing and global addressing are higher layer functions, allowing Data Link protocols to focus on local delivery, addressing, and media arbitration. In this way, the Data Link layer is analogous to a neighbourhood traffic cop; it endeavours to arbitrate between parties contending for access to a medium. When devices attempt to use a medium simultaneously, frame collisions occur. Data Link protocols specify how devices detect and recover from such collisions, and may provide mechanisms to reduce or prevent them. Delivery of frames by layer 2 devices is affected through the use of unambiguous hardware addresses. A frame's header contains source and destination addresses that indicate which device originated the frame and which device is expected to receive and process it. In contrast to the hierarchical and routable addresses of the network layer, layer 2 addresses are flat, meaning that no part of the address can be used to identify the logical or physical group to which the address belongs. The data link thus provides data transfer across the physical link. That transfer can be reliable or unreliable; many data link protocols do not have acknowledgments of successful frame reception and acceptance, and some data link protocols might not even have any form of checksum to check for transmission errors. In those cases, higher-level protocols must provide flow control, error checking, and acknowledgments and retransmission.
2.2 Data Link Layer Design Issues:
Services Provided to the Network Layer: A) Framing B) Error Control C) Flow Control
2.3 Functions of the Data Link Layer:
A) Provide service interface to the network layer B) Dealing with transmission errors
Engineering College, Ajmer
C) Regulating data flow D) Slow receivers not swamped by fast senders
2.4 Types of services provided to the Network Layer:
Unacknowledged Connectionless service Acknowledged Connectionless service Acknowledged Connection-Oriented service
2.5 Flow Control:
Functions of flow control are: a) Ensuring the sending entity does not overwhelm the receiving entity b) Preventing buffer overflow c) Transmission time d) Time taken to emit all bits into medium e) Propagation time f) Time for a bit to traverse the link
2.6 Error Detection and Correction:
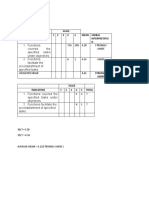
EDC= Error Detection and Correction bits (redundancy) D=Data protected by error checking, may include header fields Error detection is not 100% reliable! Protocol may miss some errors, but rarely larger EDC field yields better detection and correction.
Fig 2.1 Error Checking
2.7 Internet Checksum:
5
Engineering College, Ajmer
Sender Side:
Treat segment contents as sequence of 16-bit integers Checksum: addition (1s complement sum) of segment contents Sender puts checksum value into UDP checksum field
Receiver Side:
Compute checksum of received segment Check if computed checksum equals checksum field value: NO - error detected YES - no error detected.
Engineering College, Ajmer
Chapter - 3 System Specifications 3.1 Hardware Description
The selection of hardware is very important in the existence and proper working of any software. When selecting hardware, the size and requirements are also important. Minimum Requirements: Processor RAM Hard Disk Drive Video CD-ROM : : : : : Pentium IV class 512MB 80GB 800X600, 256 colours Required
The proposed System is developed on Processor RAM Hard Disk Drive Key Board Monitor Display Adapter Network Adapter Mouse : : : : : : : : INTEL Core2Duo 1GB 160GB Standard 101/102 or Digi Sync Family Display Panel (1024 X 764) Trident Super VGA SMC Ethernet Card Elite 16 Ultra Logitech Serial Mouse
3.2 Software Description
Operating System Front- End : : Windows 7 C#. NET.
Microsoft .NET is software that connects information, people, systems and devices. It spans clients, servers and developer tools and consists of: The .NET Framework programming model that enables developers to build Web-based applications which expose their functionality programmatically over a network using standard protocols such as SOAP and HTTP. Developer tools such as Microsoft Visual Studio .NET, which provide a rapid application integrated development environment for programming with the .NET Framework. A set of servers including Microsoft Windows 2000, Microsoft SQL, Server and Microsoft BizTalk Server that integrates, runs, operates and manages XML Web services and applications.
Engineering College, Ajmer
Client software such as Windows XP, Windows CE and Microsoft Office XP that helps developers deliver a deep and compelling user experience across a family of devices and existing products.
The .NET Framework is the programming model of the .NET environment for building, deploying and running Web- based applications, smart client applications and XML Web services. It manages much of the plumbing, enabling developers to focus on writing the business logic code for their applications. The .NET Framework includes the common language runtime and class libraries.
Engineering College, Ajmer
Chapter - 4 System Design
Topic consist the study of mainly three types of routing algorithms: 1. 2. Go Back-N Selective Repeat ARQ
3. Open Shortest Path First Algorithm (OSPF)
4.1 Go Back-N
4.1.1 State Transition Diagram:
Fig 4.1 State Transition Diagram
Engineering College, Ajmer
4.1.2 Sequence Diagram:
Fig 4.2 Sequence Diagram 4.1.3 Data Flow Diagram:
Fig 4.3 Data Flow Diagram
4.2 Selective Repeat ARQ
10
Engineering College, Ajmer
4.2.1 State Transition Diagram:
Fig 4.4 State Transition Diagram 4.2.2 Sequence Diagram:
Fig 4.5 Sequence Diagram
4.3 OSPF
11
Engineering College, Ajmer
4.3.1 State Transition Diagram:
Fig 4.6 State Transition Diagram
12
Engineering College, Ajmer
Chapter-5 Description of the Project 5.1 Features
5.1.1 Sliding Window Protocol: SWP (Sliding Window Protocol) is a connection-less protocol in one direction between a pair of users. It allows data to be sent in one direction subject to a maximum number of unacknowledged messages. The sliding-window algorithm is the basis of many standard network protocols, such as TCP and SPX. It ensures reliable, in-order delivery, and provides a mechanism for flow control and congestion control. The key feature of the sliding-window protocol is that it permits pipelined communication. In contrast, with a simple stop-and-wait protocol, the sender waits for an acknowledgment after transmitting every frame. As a result, there is at most a single outstanding frame on the channel at any given time, which may be far less than the channel's capacity.
Sender: The sender assigns a sequence number to each frame, ranging from 0 up to some maximum number. At any instant of time, the sender maintains a list of consecutive sequence numbers corresponding to frames it is permitted to send. This list, termed the sending window, represents frames sent but not yet acknowledged. When an acknowledgment arrives, the lower edge of the window is advanced to the corresponding sequence number, thereby allowing the sender to transmit new frames. Let SWS be the maximum sender window size. Let LAR be the sequence number of the last acknowledgment received. Let LFS be the sequence number of the last frame sent. The sender maintains the invariant: LFS - LAR + 1 <= SWS. Since frames currently within the sender's window may ultimately be lost or damaged in transit, the sender must keep all these frames in its memory for possible retransmission. Thus, the sender must have a buffer large enough to hold as many frames as there are in its window. The sender records the time at which every packet is sent. If the sender does not receive an acknowledgment for a packet before the timeout period elapses, it retransmits the original frame.
13
Engineering College, Ajmer
Receiver:
The receiver also maintains a receiving window, corresponding to the number of out-of-order frames it is permitted to accept. Any frames falling outside the window are discarded without comment.
Let RWS be the maximum receiver window size. Let HFA be the highest-numbered frame that will be accepted. Let NFE be the next frame expected.
The receiver maintains the invariant: HFA - NFE + 1 <= RWS.
When a frame with sequence number s arrives, the receiver takes the following action. If s < NFE or s > HFA, then the frame is outside the receiver's window and so it is discarded.
If NFE <= s <= HFA, then the frame is accepted.
An acknowledgment for s is sent if the following conditions are met: 1) s has not yet been acknowledged. 2) All frames in the range from NFE to s have been received.
In this way, the acknowledgments are cumulative. When the acknowledgment is sent, the receiver sets NFE = s + 1 and HFA = s + RWS.
5.1.2 Go Back-N Protocol: Go-Back-N ARQ is a specific instance of the automatic repeat request (ARQ) protocol, in which the sending process continues to send a number of frames specified by a window size even without receiving an acknowledgement (ACK) packet from the receiver. It is a special case of the general sliding window protocol with the transmit window size of N and receive window size of 1. The receiver process keeps track of the sequence number of the next frame it expects to receive, and sends that number with every ACK it sends. The receiver will ignore any frame that does not have the exact sequence number it expects whether that frame is a "past" duplicate of a frame it has already acknowledged [1] or whether that frame is a "future" frame past the last packet it is waiting for. Once the sender has sent all of the frames in its window, it will detect that all of the frames since the first lost frame are outstanding, and will go back to sequence number of the last ACK it received from the receiver process and fill its window starting with that frame and continue the process over again.
14
Engineering College, Ajmer
Sender Window:
Fig 5.1 Sender Window Receiver Window:
Fig 5.2 Receiver Window
Normal Operation:
15
Engineering College, Ajmer
Fig 5.3 Normal Operation Lost Frame:
Fig 5.4 Lost Frame Process
Features of Go Back-N: Based on sliding window
16
Engineering College, Ajmer
-If no error, ACK as usual with next frame expected -Use window to control number of outstanding frames -If error, reply with rejection -Discard that frame and all future frames until error frame received correctly -Transmitter must go back and retransmit that frame and all subsequent frames Damaged Frame:
-Receiver detects error in frame i -Receiver sends rejection-i -Transmitter gets rejection-i -Transmitter retransmits frame i and all subsequent
Lost Frame (1):
-Frame i lost -Transmitter sends i+1 -Receiver gets frame i+1 out of sequence -Receiver send reject i -Transmitter goes back to frame i and retransmits
Lost Frame (2):
-Frame i lost and no additional frame sent -Receiver gets nothing and returns neither acknowledgement nor rejection -Transmitter times out and sends acknowledgement frame with P bit set to 1 -Receiver interprets this as command which it acknowledges with the number of the next frame it expects (frame i ) -Transmitter then retransmits frame i Damaged Acknowledgement:
-Receiver gets frame i and send acknowledgement (i+1) which is lost -Acknowledgements are cumulative, so next acknowledgement (i+n) may arrive before transmitter times out on frame i -If transmitter times out, it sends acknowledgement with P bit set as before -This can be repeated a number of times before a reset procedure are initiated. 5.1.3 Selective Repeat ARQ:
17
Engineering College, Ajmer
Selective Repeat ARQ / Selective Reject ARQ is a specific instance of the Automatic Repeat-request (ARQ) Protocol. It may be used as a protocol for the delivery and acknowledgement of message units, or it may be used as a protocol for the delivery of subdivided message sub-units. When used as the protocol for the delivery of messages, the sending process continues to send a number of frames specified by a window size even after a frame loss. Unlike Go-Back-N ARQ, the receiving process will continue to accept and acknowledge frames sent after an initial error; this is the general case of the sliding window protocol with both transmit and receive window sizes greater than 1.It does the following:
Receiver individually acknowledges all correctly received packets
-buffers packets, as needed, for eventual in-order delivery to upper layer
Sender only resends packets for which ACK not received
-sender timer for each unacknowledged packets
Sender window
-N consecutive sequence #s -again limits sequence #s of sent, unacknowledged packets Sender Window:
Fig 5.5 Sender Window Receiver Window:
Fig 5.6 Reciver Window Flow Diagram:
18
Engineering College, Ajmer
Fig 5.7 Flow Diagram Window Size:
Fig 5.8 Window Size Selective Repeat in Action:
19
Engineering College, Ajmer
Fig 5.9 Selective Repeat in Action
5.2 Open Shortest Path First Algorithm:
OSPF (Open Shortest path First) uses the shortest path first (SPF) algorithm, also referred to as the Dijkstra algorithm, to determine the route to reach each destination. All routers in an area run this algorithm in parallel, storing the results in their individual topological databases. Routers with interfaces to multiple areas run multiple copies of the algorithm. Dijkstras Shortest Path Algorithm for a Graph: Input: Graph (N,E) with N the set of nodes and E N the set of edges dvw -link cost (dvw = infinity if (v,w) E, dvv = 0) s -source node. Output: Dn-cost of the least-cost path from node s to node n M = {s};
20
Engineering College, Ajmer
for (each n not equal to M ) Dn = dsn; while (M not equal to all nodes) do Find w not equal toM for which Dw = min{Dj ; j not equal toM}; Add w to M; for each n not equal to M Dn = minw [ Dn, Dw + dwn ]; Update route; End do Features of OSPF: Provides authentication of routing messages. Enables load balancing by allowing traffic to be split evenly across routes with equal cost Type-of-Service routing allows to setup different routes dependent on the TOS field. Supports subletting, multicasting and 2 level hierarchical model. SPF calculation is performed independently for each area. Typically faster convergence than DVRPs and has Relatively low, steady state bandwidth. Uses metricspath cost Typically faster convergence than DVRPs. Support for CIDR, VLSM, authentication, multipath, and IP unnumbered. Relatively low, steady state bandwidth Requirements.
Cost applied on all routers link paths -16-bit positive number 165,535. -The lower the more desirable. Relevant going out an interface only. Route decisions made on total cost of path
Network changes generates LSAs
All routers exchange LSAs to build and maintain a consistent database.
-The protocol remains relatively quiet during steady-state conditions. -Periodic refresh of LSAs every 30 minutes Otherwise, updates only sent when there are changes. They share a common protocol header - Routing protocol packets are sent with type of service (TOS) of 0.
-Five types of OSPF routing protocol packets: Hello
21
Engineering College, Ajmer
Database description Link-state request Link-state update Link-state acknowledgment
22
Engineering College, Ajmer
Chapter - 6 Snapshots of Project 6.1 Go Back-N Algorithm
6.1.1 Client Side Simulation:
Fig 6.1 GBN Client Side Simulation 6.1.2 Server Side Simulation:
Fig 6.2 GBN Server Side Simulation
23
Engineering College, Ajmer
6.1.3 Sending a File:
Fig 6.3 Sending a File Through GBN 6.1.4 Receiving a File:
Fig 6.4 Receiving a File Through GBN
24
Engineering College, Ajmer
6.2 Selective Repeat ARQ
6.2.1 Normal Interface:
Fig 6.5 Normal Interface of Selective Repeat ARQ 6.2.2 Sending a File:
Fig 6.6 Sending a File through Selective Repeat ARQ
6.3 Open Shortest Path First (OSPF)
25
Engineering College, Ajmer
6.3.1 Adding Location:
Fig 6.7 Adding Location in OSPF 6.3.2 Adding Weights:
Fig 6.8 Adding Weights in OSPF
6.3.3 Calculating Shortest/Minimum Cost Path:
26
Engineering College, Ajmer
Fig 6.9 Calculating Shortest Path in OSPF
27
Engineering College, Ajmer
Chapter 7 Limitations
Our project has followings constraints: Less Improved router memory and CPU utilization when compared to dynamic routing algorithms. Non-Intelligent bandwidth control Dynamic protocols take into consideration the available bandwidth when determining the rate at which it will transmit updates. Interfaces can also be configured to use a certain (maximum) percentage of the bandwidth, so that even during routing topology computations, a defined portion of the link capacity remains available for data traffic. Dynamic protocols do not require a hierarchical network design to operate efficiently. These will automatically summarize routes where applicable which is not the case with static protocols like ours. Unlike our static protocols, which only takes bandwidth into consideration when calculating the cost of a route, dynamic protocols can be configured to use bandwidth, delay, reliability, and load when calculating optimum routes. This has proven to be a valuable consideration in a wireless environment. Dynamic protocols have greater control on timing issues, such as hold times and hello intervals, than does OSPF. This allows greater flexibility with wireless connections, where these intervals must be fine-tuned to a particular device or bandwidth. Dynamic protocols are less complex and have less cost (manpower and time) involved in configuration and administration.
28
Engineering College, Ajmer
Chapter 8 Conclusions
The current global Internet based on IP protocol supports only the best effort service, i.e., network resources are contended and fairly shared by all traffic injected into the networks. Data packets of a session may follow different paths to the destination. However, with the success of Internet in recent years, IP networks are also expected to support various services, not only the traditional services (e.g., email, ftp), but also the upcoming high-speed and real-time services (e.g., audio-video real-time transmission, virtual private networks). The latter ones exhibit much different traffic characteristics from the former ones in terms of bit rate and burst, and they require fixed QoS assurances in the duration of transmission. Considering this problem, how to support the QoS requirements is becoming a hot topic in the Internet community. Our project has been able to successfully simulate the routing algorithms and provide the routers enough information in order for them to be able to handle complex network characteristics like congestion control, flow and error control, cost metrics calculation. However this project is still in its infancy and can be used to take useful real time information from routers and provide simulation to router. As time goes on it should be able to provide rich and user interactive information regarding simulation and overall flow of data and information across various nodes.
29
Engineering College, Ajmer
Chapter 9 Future Enhancements
A variety of future extensions are possible including
Feasibility and benefit/cost analysis of QoS routing: Link state updates algorithms Route calculation algorithms
Specially, we are interested in examining the determination of the timer value in periodic algorithm and the threshold value in the threshold based algorithm. An integrated software platform should be developed to examine our interests. This platform must contain a suit of components such as state maintenance and distribution, path calculation, resource reservation and so on. Moreover, the platform should provide an easy interface to measure the cost and facilitate our study in other aspects of QoS routing area in future study.
Generality - Multimedia applications tend to have diverse QoS requirements on bandwidth, delay, delay jitter, cost, and so on. From a network designer's point of view, it would be beneficial to develop a generic routing algorithm instead of implementing different routing algorithms for different types of QoS requirements independently. The generic algorithm captures the common messaging and computational structure.
Extensibility - As the network infrastructure evolves and capacity increases, new applications are made possible. It requires the routing algorithms to adapt in order to accommodate new service types. It is important to design extensible algorithms and make them adapt to new applications, because the networks become increasingly complex and the deployment of new routing algorithms is very costly.
Simplicity - The simplicity of a routing algorithm in terms of time/logical complexity often allows efficient implementation, debugging and evaluation. It also makes the algorithm easier to understand, maintain, and upgrade. Scalability QoS based routing should be scalable.
30
Engineering College, Ajmer
Chapter 10 Bibliography and References
1. Data communications and networking by Forouzan.
2.
Introduction to telecommunications networking by Tarmo Anttalainen.
3.
Data and computer communications by William Stallings.
4. www.cs.rice.edu/Conferences.
5. www.en.wikipedia.org/wiki/Category:Routing_algorithms
6. www.cs.northwestern.edu
7.
Quality of Service - Delivering QoS on the Internet and in Corporate Networks. P.Ferguson, G. Huston. John Wiley & Sons, 1998.
8.
C#.NET by WROX Publication.
31
Potrebbero piacerti anche
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (895)
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (588)
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (400)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (74)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (345)
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (121)
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- Thesis SidelineDocumento8 pagineThesis SidelineChristian Aries LansanganNessuna valutazione finora
- Final 05Documento8 pagineFinal 05Taha EtemNessuna valutazione finora
- Chapter 25 Homework Questions: Mr. Mahmoud Moussa A2 CS 9618Documento8 pagineChapter 25 Homework Questions: Mr. Mahmoud Moussa A2 CS 9618Eyad UsamaNessuna valutazione finora
- S7plcsim Advanced Readme en-US en-US PDFDocumento5 pagineS7plcsim Advanced Readme en-US en-US PDFDalethSepúlvedaNessuna valutazione finora
- Fundamentals of Electrical Circuits AnalysisDocumento8 pagineFundamentals of Electrical Circuits AnalysisArcturus VoidNessuna valutazione finora
- KPSC Assistant Professor in CS Question PaperDocumento22 pagineKPSC Assistant Professor in CS Question PaperBabaNessuna valutazione finora
- Flyer Controller DX200 E 03.2017Documento4 pagineFlyer Controller DX200 E 03.2017Elio Franklin O TavaresNessuna valutazione finora
- SQL Server OperationsDocumento5 pagineSQL Server OperationsshadiNessuna valutazione finora
- GuideDocumento225 pagineGuideantalicNessuna valutazione finora
- For Digital Alarm ClockDocumento21 pagineFor Digital Alarm Clockrajsridhar JayaseelanNessuna valutazione finora
- Telematics (9175)Documento5 pagineTelematics (9175)Gajanan BirajdarNessuna valutazione finora
- Raid PDFDocumento24 pagineRaid PDFamitNessuna valutazione finora
- Priority Inversion Problem PaperDocumento6 paginePriority Inversion Problem PaperjayanthimurthyNessuna valutazione finora
- Ci RT3606 Placa PCDocumento72 pagineCi RT3606 Placa PCjackson lopesNessuna valutazione finora
- F2X14 Series IP MODEM Technical Specification V2.0.0Documento4 pagineF2X14 Series IP MODEM Technical Specification V2.0.0Xiamen Four-Faith Industrial Router supplierNessuna valutazione finora
- Uploading New Software in Unisab III Using SD-Card - 1.0.9.0Documento3 pagineUploading New Software in Unisab III Using SD-Card - 1.0.9.0robgrollemanNessuna valutazione finora
- 6 +Athena,+QuickSight,+EMRDocumento63 pagine6 +Athena,+QuickSight,+EMRAhmad HammadNessuna valutazione finora
- Laptop - Simple English Wikipedia, The Free EncyclopediaDocumento2 pagineLaptop - Simple English Wikipedia, The Free EncyclopediaglennNessuna valutazione finora
- Ebook DFC 7.2 Development Guide PDFDocumento186 pagineEbook DFC 7.2 Development Guide PDFHilmy Dzul FaqarNessuna valutazione finora
- 20221010CSX-Job Announcement For IT Listing and Assistant To CEODocumento2 pagine20221010CSX-Job Announcement For IT Listing and Assistant To CEOGPS MPWTNessuna valutazione finora
- User Manual For New HR11 6-10kVA Rack Mounted UPS (PF 1) - V1.4Documento38 pagineUser Manual For New HR11 6-10kVA Rack Mounted UPS (PF 1) - V1.4Cristian ReyesNessuna valutazione finora
- Lenovo Yoga 9i 1415 - Intel - DatasheetDocumento4 pagineLenovo Yoga 9i 1415 - Intel - DatasheetBambang HarjantoNessuna valutazione finora
- Teradata Client ANSI TERADATA ModesDocumento2 pagineTeradata Client ANSI TERADATA ModesPradeep KothakotaNessuna valutazione finora
- Modul Minggu Ke-2 (DB6 Dan DB7)Documento14 pagineModul Minggu Ke-2 (DB6 Dan DB7)farrel prambudiNessuna valutazione finora
- Configuration Management and Orchestration With SaltStackDocumento39 pagineConfiguration Management and Orchestration With SaltStackAnoop MannathukandyNessuna valutazione finora
- Redlion MPiec Modbus Configuration W Crimson2 v007Documento14 pagineRedlion MPiec Modbus Configuration W Crimson2 v007minhtutran1983Nessuna valutazione finora
- Dr. Dobb (Ap) S Journal (Volume 30, Issue 2, No. 369, February 2005) SDocumento75 pagineDr. Dobb (Ap) S Journal (Volume 30, Issue 2, No. 369, February 2005) SKola AgoutiNessuna valutazione finora
- Aho Johnson PaperDocumento14 pagineAho Johnson PaperGanesh SutarNessuna valutazione finora
- PatelDocumento10 paginePatelArpan PatelNessuna valutazione finora
- Complete Final Sem Report PDFDocumento79 pagineComplete Final Sem Report PDFbhanu pratap mishraNessuna valutazione finora