Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Cisco Interview Questions
Caricato da
ssprudhviDescrizione originale:
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Cisco Interview Questions
Caricato da
ssprudhviCopyright:
Formati disponibili
1.
You need to retrieve a file from the file server for your word processing application, which layer of the OSI model is responsible for this function? 1. Presentation layer 2. Application layer 3. Session layer 4. Transport layer 5. Datalink layer 2. You are working in a word processing program, which is run from the file server. Your data comes back to you in an unintelligible manner. Which layer of the OSI model would you investigate? 1. Application layer 2. Presentation layer 3. Session layer 4. Network layer 5. Datalink layer 3. The IEEE subdivided the datalink layer to provide for environments that need connectionless or connection-oriented services. What are the two layers called? 1. Physical 2. MAC 3. LLC 4. Session 5. IP 4. You are working with graphic translations. Which layer of the OSI model is responsible for code formatting and conversion and graphic standards. 1. Network layer 2. Session layer 3. Transport layer 4. Presentation layer 5. Which is the best definition of encapsulation? 1. Each layer of the OSI model uses encryption to put the PDU from the upper layer into its data field. It adds header and trailer information that is available to its counterpart on the system that will receive it. 2. Data always needs to be tunneled to its destination so encapsulation must be used. 3. Each layer of the OSI model uses compression to put the PDU from the upper layer into its data field. It adds header and trailer information that is available to its counterpart on the system that will receive it. 4. Each layer of the OSI model uses encapsulation to put the PDU from the upper layer into its data field. It adds header and trailer information that is available to its counterpart on the system that will receive it. 6. Routers can be configured using several sources. Select which of the following sources can be used. 1. Console Port 2. Virtual Terminals 3. TFTP Server
4. Floppy disk 5. Removable media 7. Which memory component on a Cisco router contains the dynamic system configuration? 1. ROM 2. NVRAM 3. Flash 4. RAM/DRAM 8. Which combination of keys will allow you to view the previous commands that you typed at the router? 1. ESC-P 2. Ctrl-P 3. Shift-P 4. Alt-P 9. Which commands will display the active configuration parameters? 1. show running-config 2. write term 3. show version 4. display term 10. You are configuring a router, which prompt tells you that you are in the privileged EXEC mode? 1. @ 2. > 3. ! 4. : 5. # 11. What does the command IP name-server 255.255.255.255 accomplish? 1. It disables domain name lookup. 2. It sets the domain name lookup to be a local broadcast. 3. This is an illegal command. 4. The command is now defunct and has been replaced by IP server-name ip any 12. The following selections show the command prompt and the configuration of the IP network mask. Which two are correct? 1. Router(config-if)#netmask-format { bitcount | decimal | hexadecimal } 2. Router#term IP netmask-format { bitcount | decimal | hexadecimal } 3. Router(config-if)#IP netmask-format { bitcount | decimal | hexadecimal } 4. Router#ip netmask-format { bitcount | decimal | hexadecimal } 13. Which layer is responsible for flow control with sliding windows and reliability with sequence numbers and acknowledgments? 1. Transport 2. Application 3. Internet 4. Network Interface 14. Which processes does TCP, but not UDP, use? 1. Windowing
2. Acknowledgements 3. Source Port 4. Destination Port 15. Select which protocols use distance vector routing? 1. OSPF 2. RIP 3. IGRP 4. PPP 1. 2 2. 1 3. 3,4 4. 4 5. 2 6. 1,2,3 7. 4 8. 2 9. 1 10. 5 11. 4 12. 3 13. 1 14. 1 15. 2,3 A: The layers are physical, data link, network, transport, session, presentation, and application layers. Q: In the TCP client-servel model, how does the three-way handshake work in opening connection? A: The client first sends a packet with sequence "x" to the server. When the server receives this packet, the server will send back another packet with sequence "y", acknowledging the request of the client. When the client receives the acknowledgement from the server, the client will then send an acknowledge back to the server for acknowledging that sequence "y" has been received. Q: What is the purpose of exchanging beginning sequence numbers during the the connection in the TCP client-server model? A: To ensure that any data lost during data transfer can be retransmitted.
Q: How does Asynchronous Transfer Mode (ATM) work? A: ATM works by transmitting all traffic in small, fixed-sized cells. These small, fixed-size cells reduces queuing delay and can be switched quickly. ATM fits into layer 2 of the OSI model and provides functions for framing and error correction. At the port interface, ATM switches convert cells into frames, and vice versa. ATM provides Quality of Service and traffic shaping. Q: Given a Class B Network with subnet mask of 255.255.248.0 and a packet addressed to 130.40.32.16, what is the subnet address? A: Take the 2 addresses, write them in binary form, then AND them. The answer is 130.40.32.0 What is UTP? UTP Unshielded twisted pair 10BASE-T is the preferred Ethernet medium of the 90s. It is based on a star topology and provides a number of advantages over coaxial media: It uses inexpensive, readily available copper phone wire. UTP wire is much easier to install and debug than coax. UTP uses RG-45 connectors, which are cheap and reliable. What is a router? What is a gateway? Routers are machines that direct a packet through the maze of networks that stand between its source and destination. Normally a router is used for internal networks while a gateway acts a door for the packet to reach the outside of the internal network What is Semaphore? What is deadlock? Semaphore is a synchronization tool to solve critical-section problem, can be used to control access to the critical section for a process or thread. The main disadvantage (same of mutual-exclusion) is require busy waiting. It will create problems in a multiprogramming system, where a single CPU is shared among many processes. Busy waiting wastes CPU cycles. Deadlock is a situation when two or more processes are waiting indefinitely for an event that can be caused by only one of the waiting
processes. The implementation of a semaphore with a waiting queue may result in this situation. What is Virtual Memory? Virtual memory is a technique that allows the execution of processes that may not be completely in memory. A separation of user logical memory from physical memory allows an extremely large virtual memory to be provided for programmers when only a smaller physical memory is available. It is commonly implemented by demand paging. A demand paging system is similar to a paging system with swapping. Processes reside on secondary memory (which is usually a disk). When we want to execute a process, we swap it into memory. Explain the layered aspect of a UNIX system. What are the layers? What does it mean to say they are layers? A UNIX system has essentially three main layers: ? The hardware ? The operating system kernel ? The user-level programs The kernel hides the systems hardware underneath an abstract, highlevel programming interface. It is responsible for implementing many of the facilities that users and user-level programs take for granted. The kernel assembles all of the following UNIX concepts from lowerlevel hardware features: ? Processes (time-sharing, protected address space) ? Signals and semaphores ? Virtual Memory (swapping, paging, and mapping) ? The filesystem (files, directories, namespace) ? Pipes and network connections (inter-process communication) Question 1: How does the race condition occur? It occurs when two or more processes are reading or writing some shared data and the final result depends on who runs precisely when.
Question 2: What is multiprogramming? Multiprogramming is a rapid switching of the CPU back and forth between processes. Question 3: Name the seven layers of the OSI Model and describe them briefly. Physical Layer - covers the physical interface between devices and the rules by which bits are passed from one to another. Data Link Layer - attempts o make the physical link reliable and provides the means to activate, maintain, and deactivate the link. Network Layer - provides for the transfer of information between end systems across some sort communications network. Transport Layer - provides a mechanism for the exchange of data between end system. Session Layer - provides the mechanism for controlling the dialogue between applications in end systems. Presentation Layer - defines the format of the data to be exchanged between applications and offers application programs a set of data transformation services. Application Layer - provides a means for application programs to access the OSI environment. Question 4: What is the difference between TCP and UDP? TCP and UDP are both transport-level protocols. TCP is designed to provide reliable communication across a variety of reliable and unreliable networks and internets. UDP provides a connectionless service for application-level procedures. Thus, UDP is basically
an unreliable service; delivery and duplicate protection are not guareented. Question 5: What does a socket consists of? The combination of an IP address and a port number is called a socket.
Network engineer/architect interview questions
1. Explain how traceroute, ping, and tcpdump work and what they are used for? 2. Describe a case where you have used these tools to troubleshoot. 3. What is the last major networking problem you troubleshot and solved on your own in the last year? 4. What LAN analyzer tools are you familiar with and describe how you use them to troubleshoot and on what media and network types. 5. Explain the contents of a routing table (default route, next hop, etc.) 6. What routing protocols have you configured? 7. Describe the commands to set up a route. 8. What routing problems have you troubleshot? 9. How do you display a routing table on a Cisco? On a host? 10. How do you use a routing table and for what? 11. What is a route flap? 12. What is a metric? 13. When do you use BGP, IGRP, OSPF, Static Routes? 14. What do you see as current networking security issues (e.g. NFS mounting, spoofing, one time passwords, etc.)? 15. Describe a routing filter and what it does. 16. Describe an access list and what it does. 17. What is a network management system? 18. Describe how SNMP works. 19. Describe the working environment you are currently in, e.g. frequent interruptions, frequent priority shifting, team or individual. 20. What do you use to write documentation? Editor? Mail reader? 21. What platform (s) do you currently work on at your desk? 22. How do you manage multiple concurrent high level projects? 23. Describe a recent short term stressful situation and how you managed it. 24. How do you manage a long term demanding stressful work environment? 25. Have you worked in an assignment based environment, e.g. work request/trouble ticket system, and if so, describe that environment. 26. Describe what network statistics or measurement tools you are familiar with and how you have used them. 27. Describe what a VPN is and how it works. 28. Describe how VoIP works. 29. Describe methods of QoS. 30. How does ToS bit work?
Potrebbero piacerti anche
- Tutorial CentOS Sendmail Roundcube ConfigurationDocumento7 pagineTutorial CentOS Sendmail Roundcube ConfigurationhectoramolinaNessuna valutazione finora
- Avaya Ethernet Routing Switching ImplementationDocumento76 pagineAvaya Ethernet Routing Switching ImplementationSAPTARSHI GHOSHNessuna valutazione finora
- CCNA VOICE Study Summary 461Documento31 pagineCCNA VOICE Study Summary 461brianmurindagomoNessuna valutazione finora
- AIX For System AdministratorsDocumento4 pagineAIX For System AdministratorsimamnurhadiNessuna valutazione finora
- CUCM VirtualizationDocumento15 pagineCUCM Virtualizationjasjusr100% (1)
- VPN and SecureClient CommandsDocumento5 pagineVPN and SecureClient CommandsAtul ChauhanNessuna valutazione finora
- CCNP Exam Dumps CollectionDocumento2 pagineCCNP Exam Dumps CollectionKhaleelNessuna valutazione finora
- Guide To Hardening The Cisco IOS DevicesDocumento61 pagineGuide To Hardening The Cisco IOS DevicesBrian TurnerNessuna valutazione finora
- BGP Part2 - CheatSheet ATech (Waqas Karim)Documento1 paginaBGP Part2 - CheatSheet ATech (Waqas Karim)Waqas KarimNessuna valutazione finora
- 350 018 PDFDocumento530 pagine350 018 PDFamxyzNessuna valutazione finora
- TCP/IP Suite Error and Control MessagesDocumento28 pagineTCP/IP Suite Error and Control MessagesbaraynavabNessuna valutazione finora
- Mail Server Installation and ConfigurationDocumento34 pagineMail Server Installation and ConfigurationSalum YusuphNessuna valutazione finora
- Discovering the Value of IBM API Connect Firmware Version: 5.0.0.1Documento137 pagineDiscovering the Value of IBM API Connect Firmware Version: 5.0.0.1Manish GuptaNessuna valutazione finora
- Internetworking Troubleshooting Case StudyDocumento26 pagineInternetworking Troubleshooting Case StudyNigel Terry Sanou100% (1)
- EIGRP Interview QuestionsDocumento6 pagineEIGRP Interview QuestionshamedNessuna valutazione finora
- Top 10 VMware Engineer Interview QuestionsDocumento3 pagineTop 10 VMware Engineer Interview QuestionsnaraynapotugariNessuna valutazione finora
- Are You Preparing For SCCM InterviewDocumento39 pagineAre You Preparing For SCCM Interviewyuva razNessuna valutazione finora
- Embedded Software Primer - Ch8Documento30 pagineEmbedded Software Primer - Ch8komal purohit50% (2)
- System Receives A Software Forced Crash: How Do I Reset The 6504 To Default Settings If I Need To?Documento16 pagineSystem Receives A Software Forced Crash: How Do I Reset The 6504 To Default Settings If I Need To?Rep SteveNessuna valutazione finora
- Encryption and Authentication Interview QuestionsDocumento19 pagineEncryption and Authentication Interview QuestionsSam RogerNessuna valutazione finora
- FactSheet - Ports For CucmDocumento3 pagineFactSheet - Ports For Cucmtimbrown88Nessuna valutazione finora
- Networking and Protocols Interview QuestionsDocumento5 pagineNetworking and Protocols Interview Questionsapi-19912132Nessuna valutazione finora
- NNMi Introduction Slide InformativeDocumento71 pagineNNMi Introduction Slide InformativeMohammad Danish NasimNessuna valutazione finora
- BRKUCC-2676 Migrating From VCS To CUCMDocumento113 pagineBRKUCC-2676 Migrating From VCS To CUCMSidney LebreNessuna valutazione finora
- Cisco TAC Entry Training - 12 - Open Shortest Path First (OSPF) PDFDocumento54 pagineCisco TAC Entry Training - 12 - Open Shortest Path First (OSPF) PDFFerasHamdanNessuna valutazione finora
- Cisco TAC Entry Training - 6 - Inter-VLAN RoutingDocumento29 pagineCisco TAC Entry Training - 6 - Inter-VLAN RoutingFerasHamdanNessuna valutazione finora
- CUCM Smart Licensing Version 12.XDocumento5 pagineCUCM Smart Licensing Version 12.XGeo ThomasNessuna valutazione finora
- ACI EIGRP Routing For External Layer 3 Connectivity - DCLessonsDocumento6 pagineACI EIGRP Routing For External Layer 3 Connectivity - DCLessonsravi kantNessuna valutazione finora
- RectDocumento156 pagineRectFrank AlNessuna valutazione finora
- Cisco IOS XR Routing Configuration Guide For The Cisco CRS RouterDocumento644 pagineCisco IOS XR Routing Configuration Guide For The Cisco CRS RouterChristopher Pepito0% (1)
- Cisco IOS ListDocumento33 pagineCisco IOS ListAnonymous eTVLLaZ3yNessuna valutazione finora
- Configure Cyberoam SNMPDocumento5 pagineConfigure Cyberoam SNMPdhamecha_sweetu_6730Nessuna valutazione finora
- Types of FirewallDocumento10 pagineTypes of FirewallsanjeevNessuna valutazione finora
- Basic Notes On BGP (Border Gateway Protocol) : Ospf EigrpDocumento2 pagineBasic Notes On BGP (Border Gateway Protocol) : Ospf Eigrpshrikant_more41612Nessuna valutazione finora
- CCIE Security v5 Configure LAB1 QuestionsDocumento23 pagineCCIE Security v5 Configure LAB1 QuestionsmentalxNessuna valutazione finora
- How To Identify MQ Client Connections and Stop ThemDocumento26 pagineHow To Identify MQ Client Connections and Stop ThemPurushotham100% (1)
- Cisco Unified Wireless Network Solution OverviewDocumento20 pagineCisco Unified Wireless Network Solution OverviewPaul CherresNessuna valutazione finora
- SM MQ CICS IntegrationDocumento50 pagineSM MQ CICS IntegrationRahul JaiswalNessuna valutazione finora
- 300-115 by Aditya Gaur v-7Documento4 pagine300-115 by Aditya Gaur v-7madagonerajuNessuna valutazione finora
- Basic Cisco Troubleshooting PDFDocumento1 paginaBasic Cisco Troubleshooting PDFshareefgs55600% (1)
- 02 - Introduction To CMS and UCMDBDocumento39 pagine02 - Introduction To CMS and UCMDBluisnor1100% (1)
- Configuracion Switch Zyxel PDFDocumento384 pagineConfiguracion Switch Zyxel PDFJulio Perez Ferrufino100% (1)
- TCP Interview QuestionDocumento3 pagineTCP Interview QuestionOlaleye OlayinkaNessuna valutazione finora
- Ig 4 Command Line Interface Reference: Document Release 1.01Documento25 pagineIg 4 Command Line Interface Reference: Document Release 1.01aBui KANessuna valutazione finora
- Maples It: Ibm Websphere Message Queuing V7.1/7.5Documento4 pagineMaples It: Ibm Websphere Message Queuing V7.1/7.5gpsmlkNessuna valutazione finora
- Core Java document titleDocumento191 pagineCore Java document titleSubhabrata MishraNessuna valutazione finora
- Fortinet as an organization, its history and productsDocumento4 pagineFortinet as an organization, its history and productsWady L. BautistaNessuna valutazione finora
- 3com 7750 Config GuideDocumento940 pagine3com 7750 Config GuideFranklin Miranda RoblesNessuna valutazione finora
- Troubleshooting Cisco Catalyst 2960 3560 and 3750 Series SwitchesDocumento135 pagineTroubleshooting Cisco Catalyst 2960 3560 and 3750 Series SwitchesJose Adrian Saenz100% (1)
- Cisco Unity Connection SIP Integration With CUCM Step by Step GuideDocumento17 pagineCisco Unity Connection SIP Integration With CUCM Step by Step Guideeyob_2Nessuna valutazione finora
- UCMDB Integration Release 3Documento15 pagineUCMDB Integration Release 3vijay kumarNessuna valutazione finora
- Admin Role ProfilesDocumento31 pagineAdmin Role ProfilesChau NguyenNessuna valutazione finora
- r80 10 Ccsa OverviewDocumento1 paginar80 10 Ccsa Overviewreggie dNessuna valutazione finora
- 10 Troubleshooting PDFDocumento25 pagine10 Troubleshooting PDFCarito AvellanedaNessuna valutazione finora
- WSTE 04282010 WMQFunctionsCommandsNewUsers LampkinDocumento43 pagineWSTE 04282010 WMQFunctionsCommandsNewUsers LampkinManikanta_Redd_916Nessuna valutazione finora
- Troubleshooting Campus Networks: Practical Analysis of Cisco and LAN ProtocolsDa EverandTroubleshooting Campus Networks: Practical Analysis of Cisco and LAN ProtocolsValutazione: 4 su 5 stelle4/5 (1)
- Bridging and Switching Basics: What Are Bridges and Switches?Documento6 pagineBridging and Switching Basics: What Are Bridges and Switches?Pavan KumarNessuna valutazione finora
- Osi ExplanationDocumento9 pagineOsi ExplanationssprudhviNessuna valutazione finora
- Windows Power Shell CommandsDocumento7 pagineWindows Power Shell CommandsssprudhviNessuna valutazione finora
- MCITP SylabusDocumento3 pagineMCITP SylabusssprudhviNessuna valutazione finora
- CNA Syllabus: Here Is A Clickable List of How Our Content Maps To The Latest CCNA SyllabusDocumento5 pagineCNA Syllabus: Here Is A Clickable List of How Our Content Maps To The Latest CCNA SyllabusssprudhviNessuna valutazione finora
- MCSE ClassesDocumento58 pagineMCSE ClassesssprudhviNessuna valutazione finora
- Raid Levels Etc..Documento57 pagineRaid Levels Etc..ssprudhviNessuna valutazione finora
- Installing and Upgrading Windows VistaDocumento6 pagineInstalling and Upgrading Windows VistaVinod SharmaNessuna valutazione finora
- Active Directory FAQDocumento14 pagineActive Directory FAQnarendra_30thuNessuna valutazione finora
- Review of Wired NetworkDocumento6 pagineReview of Wired NetworkssprudhviNessuna valutazione finora
- CCNA Syllabus and Topics Must To FollowDocumento4 pagineCCNA Syllabus and Topics Must To Followchaladhi33% (3)
- CCNA Syllabus Content: Describe How A Network WorksDocumento4 pagineCCNA Syllabus Content: Describe How A Network WorksssprudhviNessuna valutazione finora
- Start-Run Commands For Windows XP, Vista and Windows 7:: CHKDSKDocumento4 pagineStart-Run Commands For Windows XP, Vista and Windows 7:: CHKDSKssprudhviNessuna valutazione finora
- Flash TutorialDocumento12 pagineFlash TutorialssprudhviNessuna valutazione finora
- Review of Wired NetworkDocumento6 pagineReview of Wired NetworkssprudhviNessuna valutazione finora
- 156 Comandos para Windows XPDocumento9 pagine156 Comandos para Windows XPleoword100% (10)
- HTML TutorialDocumento100 pagineHTML TutorialssprudhviNessuna valutazione finora
- DOTNET TutorialDocumento9 pagineDOTNET TutorialssprudhviNessuna valutazione finora
- An A-Z Index of The Command Line: Windows CMDDocumento6 pagineAn A-Z Index of The Command Line: Windows CMDssprudhviNessuna valutazione finora
- What Is A Computer Network?Documento20 pagineWhat Is A Computer Network?ssprudhviNessuna valutazione finora
- ASP TutorialDocumento102 pagineASP TutorialssprudhviNessuna valutazione finora
- Windows CMD Commands - CMD Network CommandsDocumento5 pagineWindows CMD Commands - CMD Network CommandsssprudhviNessuna valutazione finora
- MCITPDocumento23 pagineMCITPssprudhviNessuna valutazione finora
- CDDocumento42 pagineCDssprudhviNessuna valutazione finora
- Proteins classificationsDocumento16 pagineProteins classificationsssprudhviNessuna valutazione finora
- Desigo PX PXM20 / PXM20-E Operator Unit: User's GuideDocumento72 pagineDesigo PX PXM20 / PXM20-E Operator Unit: User's GuidedavidNessuna valutazione finora
- iPECS UCP DatasheetDocumento2 pagineiPECS UCP DatasheetArkadiusz MacińskiNessuna valutazione finora
- Kurama Arutha XDCCDocumento10 pagineKurama Arutha XDCCjosepharubioNessuna valutazione finora
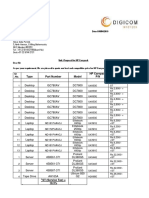
- Type Part Number Model HP Carepack P/N Price/Unit: Dated-08/04/2010 Kind AttnDocumento2 pagineType Part Number Model HP Carepack P/N Price/Unit: Dated-08/04/2010 Kind AttnEmerge SolutionsNessuna valutazione finora
- Brihat Tantra SaraDocumento6 pagineBrihat Tantra Saramallikai_10% (1)
- TK 80Documento4 pagineTK 80etishereNessuna valutazione finora
- Privacy Preservation For SDNSDocumento9 paginePrivacy Preservation For SDNSVivekananda GNNessuna valutazione finora
- LG Aria 24 130 26 300 ProgrammingDocumento233 pagineLG Aria 24 130 26 300 ProgrammingDayalan Vino80% (5)
- Cisco ACI Multi-Site ArchitectureDocumento134 pagineCisco ACI Multi-Site ArchitectureGabriela PopescuNessuna valutazione finora
- Quick IPv4 Addressing and Subnetting by OlivoyDocumento27 pagineQuick IPv4 Addressing and Subnetting by OlivoyviladroNessuna valutazione finora
- A Comparison of in Memory DatabasesDocumento6 pagineA Comparison of in Memory DatabasesPiyush MandalNessuna valutazione finora
- Chapter 5: SONET/SDHDocumento100 pagineChapter 5: SONET/SDHrahul_mhatre_26Nessuna valutazione finora
- Ups Cyber Power PDFDocumento64 pagineUps Cyber Power PDFgiangpd vtNessuna valutazione finora
- SIM Card Reg DocumentationDocumento54 pagineSIM Card Reg Documentationanon-607553100% (4)
- OpenOffice / Libre Office Report Designer GuideDocumento9 pagineOpenOffice / Libre Office Report Designer GuideEdcarlos ReisNessuna valutazione finora
- Micro Twinax ConnectorsDocumento4 pagineMicro Twinax ConnectorsSmiths ConnectorsNessuna valutazione finora
- How To Use DASSIDIRECT DAServer Together With Siemens S7-200 PLCDocumento14 pagineHow To Use DASSIDIRECT DAServer Together With Siemens S7-200 PLCTio_louis32Nessuna valutazione finora
- Zain Kuwait PPT - Executive Report - v3Documento21 pagineZain Kuwait PPT - Executive Report - v3Manuel CardenasNessuna valutazione finora
- Expanding telecom's future role with internet integrationDocumento8 pagineExpanding telecom's future role with internet integrationremo_nemoNessuna valutazione finora
- 7safe Prospectus Jan 2017Documento19 pagine7safe Prospectus Jan 2017MikeNessuna valutazione finora
- Freshman Comp Are We Technology November 15Documento16 pagineFreshman Comp Are We Technology November 15api-300826599Nessuna valutazione finora
- Inventor File Dialog Open SaveDocumento3 pagineInventor File Dialog Open SaveVitorHugoNessuna valutazione finora
- ZXDU68 G020 (V5.0) DC Power System Quick User GuideDocumento8 pagineZXDU68 G020 (V5.0) DC Power System Quick User GuideJose Luis Gonzalez100% (1)
- Using Identity-Based Encryption To Eliminate Certificates in SSL TransactionsDocumento46 pagineUsing Identity-Based Encryption To Eliminate Certificates in SSL TransactionsParth005Nessuna valutazione finora
- Fire Protection Engineering Summer 2001Documento33 pagineFire Protection Engineering Summer 2001Hany RifaatNessuna valutazione finora
- Week 1 Empowerment TechnologiesDocumento11 pagineWeek 1 Empowerment TechnologiesVillavicencio KylaNessuna valutazione finora
- Bank Management SystemDocumento54 pagineBank Management SystemJuNaid Sheikh100% (1)
- History of Internet: Accounting Information System of Technology Faculty of Economic Gunadarma University 2019/2020Documento16 pagineHistory of Internet: Accounting Information System of Technology Faculty of Economic Gunadarma University 2019/2020Adib GhulamNessuna valutazione finora
- Genera Intro Mu Phinsiii 002 CDocumento14 pagineGenera Intro Mu Phinsiii 002 CMoorthy PakisamyNessuna valutazione finora