Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Troubleshooting Guide IKE VPN Initialization Rev0
Caricato da
johnemeryisiDescrizione originale:
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Troubleshooting Guide IKE VPN Initialization Rev0
Caricato da
johnemeryisiCopyright:
Formati disponibili
Troubleshooting Guide: IKE VPN Initialization For SonicWALL-to-SonicWALL
Prepared by SonicWALL, Inc. 09/03/2003
Introduction
This guide will present the basic information required to troubleshoot problems in establishing a SonicWALL-to-SonicWALL IKE VPN Tunnel. The guide will first present the basic premise of IKE negotiation, protocol support, successful IKE negotiation examples and noteworthy configuration details. This guide will then provide a methodology to test and troubleshoot using the SonicWALL log messages.
IKE Negotiation
An IKE VPN tunnel is established by negotiations between two SonicWALL Security Appliances. The VPN Security Association (SA) configured on each SonicWALL defines the Security Policy settings proposed in the IKE negotiation. For negotiations to succeed, these Security Policies must be in agreement. When a SonicWALL receives a packet (e.g. a ping) destined for a subnet behind the remote peer SonicWALL and the tunnel is not established, it will initiate the IKE negotiations to establish the VPN tunnel. The SonicWALL security appliances negotiating an IKE VPN are referred to as an IKE Initiator and an IKE Responder. This distinction is evident in the logs. They are defined as follows: IKE Initiator: SonicWALL initiating the IKE VPN tunnel negotiation request. IKE Responder: SonicWALL receiving the request to establish an IKE VPN tunnel.
IKE VPN Protocols
The IKE protocol is used during the entire negotiation phase. The negotiation defines policy settings and keys used by the IPSec tunnel protocol. These protocols must not be blocked by any firewalls or the ISP networks between the SonicWALLs establishing the tunnel. The protocols used for the IKE negotiation and VPN tunnel are as follows: Standard IKE negotiations UDP Port 500 IPSec Tunnel IP 50 With NAT Traversal (NAT-T) active IKE negotiations UDP Port 500 UDP Encapsulated IPSec tunnel UDP 500
NAT Traversal (NAT-T)
NAT Traversal (NAT-T) is a Global VPN option on SonicWALL security appliances. It is enabled by default. With this option, a NAT discovery process runs after the IKE initiation request to determine if there are any NAT devices in the tunnel path. If a NAT device is detected in the tunnel path, SonicWALL security appliances will use UDP encapsulated IPSec packets for the VPN tunnel. NAT discovery messages are displayed in the logs, but only in the IKE Responder log with Aggressive Mode.
Page 1 of 14
2003 SonicWALL, Inc. SonicWALL is a registered trademark of SonicWALL, Inc. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies.
Troubleshooting Guide: IKE VPN Initialization
IKE Access Rules
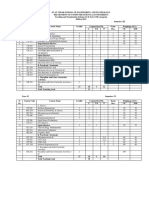
Inbound and outbound IKE Access Rules are required on the negotiating SonicWALLs to allow IKE sessions. The rules are automatically generated when you enable an IKE VPN SA, including the Group VPN SA. Figure 1 displays the IKE access rules. Be sure not to disable the IKE rules. There should not be any other rules before the IKE access rule that would deny access for this service.
Figure 1: SonicWALL IKE Access Rules
Main Mode vs. Aggressive Mode
There are two phases of the IKE negotiations, Phase 1 and Phase 2. Phase 1 can be configured to use either Main Mode or Aggressive Mode. Main Mode is more secure in providing identity protection for the negotiating nodes. Main Mode requires a static IP address on both units negotiating the VPN tunnel. Aggressive Mode is used when one SonicWALL has a dynamic WAN IP address (uses DHCP, PPPoE, L2TP or PPTP). Aggressive Mode has the following configuration requirements: The SA name on each SonicWALL must be the same as the Unique Firewall Identifier found on the VPN Summary page of the other SonicWALL. Use 0.0.0.0 for the IPSec Gateway address of the unit with DHCP.
Page 2 of 14
2003 SonicWALL, Inc. SonicWALL is a registered trademark of SonicWALL, Inc. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies.
Troubleshooting Guide: IKE VPN Initialization
Main Mode Negotiations Example
IKE Initiator and IKE Responder log entries for a successful IKE negotiation using Main Mode (Phase 1) negotiation are displayed in Figures 2 & 3. The negotiation can be followed readily as it progresses through initiation, Phase 1, Phase 2 and completion. The logs also show the NAT discovery process that is enabled by default, but is optional in SonicWALL Security Appliances. Information about the IPSec SA added (tunnel activated) provided in the notes section includes encryption/authentication type, subnet routes added and life time of the tunnel.
Figure 2: IKE Initiator Log after Successfully Establishing VPN (Main Mode)
Page 3 of 14
2003 SonicWALL, Inc. SonicWALL is a registered trademark of SonicWALL, Inc. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies.
Troubleshooting Guide: IKE VPN Initialization
Main Mode Negotiations Example (continued)
Figure 3: IKE Responder Log after Successfully Establishing VPN (Main Mode)
Page 4 of 14
2003 SonicWALL, Inc. SonicWALL is a registered trademark of SonicWALL, Inc. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies.
Troubleshooting Guide: IKE VPN Initialization
Aggressive Mode Negotiations Example
IKE Initiator and IKE Responder log entries for a successful IKE negotiation using Aggressive Mode (Phase 1) negotiation are displayed in Figures 4 & 5. The negotiation can be followed readily as it progresses through initiation, Phase 1, Phase 2 and completion. The logs also show the NAT discovery process only runs from the IKE Responder. If using Aggressive Mode, the SA name on each SonicWALL must be the same as the Unique Firewall Identifier found on the VPN Summary page of the other SonicWALL Information about the IPSec SA added (tunnel activated) provided in the notes section includes encryption/authentication type, subnet routes added and life time of the tunnel.
Figure 4: IKE Initiator Log after Successfully Establishing VPN (Aggressive Mode)
Page 5 of 14
2003 SonicWALL, Inc. SonicWALL is a registered trademark of SonicWALL, Inc. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies.
Troubleshooting Guide: IKE VPN Initialization
Aggressive Mode Negotiations Example (continued)
Figure 5: IKE Responder Log after Successfully Establishing VPN (Aggressive Mode)
Page 6 of 14
2003 SonicWALL, Inc. SonicWALL is a registered trademark of SonicWALL, Inc. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies.
Troubleshooting Guide: IKE VPN Initialization
Routing Multiple Subnets through VPN
The SA on each SonicWALL also defines the subnet(s) behind the remote peer SonicWALL to which the VNP tunnel will route. If there are multiple remote destination subnets defined in an SA, there will actually be a separate tunnel established for each subnet. Thus, a separate negotiation occurs for each subnet. Figure 6 displays status of the NY Office SA which has two remote subnets defined in the destination. The Green dot indicates a tunnel for the destination subnet 192.168.4.0/24 is active. A separate negotiation will occur to establish a tunnel for the destination subnet 192.168.3.0/24.
Figure 6: Routing Multiple Subnets through a VPN
Central Gateway Configurations
Selecting the Use this SA as default route for all internet traffic allows you to configure a remote office or home installation to route all traffic including internet traffic to a Central Gateway SonicWALL. This is to prevent Split Tunneling and is often used in Hub and Spoke VPN configurations. The configuration on the Central Gateway SonicWALL must define a Default LAN Gateway IP address in the advanced configuration settings of the VPN SA. Traffic destined for the internet will then route through the VPN and be forwarded to another firewall or router, defined as the Default LAN Gateway, which will route and control access to the internet from the central site.
Page 7 of 14
2003 SonicWALL, Inc. SonicWALL is a registered trademark of SonicWALL, Inc. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies.
Troubleshooting Guide: IKE VPN Initialization
DMZ in Standard Mode
When using DMZ in Standard Mode, an IP address range is typically specified for a group of hosts located on the DMZ. Specifying an address range in this manner does not generate a typical network address and subnet mask combination in the routing table. This design allows flexibility in assigning host addresses to the DMZ. However, entering an IP address range in this manner may cause a problem routing to some or all of the addresses through a VPN. To overcome this problem, each IP address on the DMZ must be entered individually in the DMZ Addresses page as demonstrated in Figure 7. This will force each host address to be listed with a 32 bit subnet mask in the routing table. Additionally, host addresses of the servers must be entered individually (with 32 bit subnet mask) in the SA destination network field on the other SonicWALL.
Figure 7: Entering Individual Host Addresses for DMZ in Standard Mode
Page 8 of 14
2003 SonicWALL, Inc. SonicWALL is a registered trademark of SonicWALL, Inc. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies.
Troubleshooting Guide: IKE VPN Initialization
Testing the IKE VPN Tunnel
Initiating traffic through the VPN will start the IKE negotiation. Check the SonicWALL VPN>Summary page to see the status of VPN Policies and Active Tunnels. If a tunnel does not show as active after traffic for it has been generated, review the log messages on both SonicWALL security appliances to determine the problem. The final sections of this document provide troubleshooting tips based on the error messages displayed. Running a PING test will initiate traffic through the VPN.
VPN TELE3 SP WAN IP: 10.50.22.127 LAN IP: 192.168.2.1/24 PRO 330 WAN IP: 10.50.22.128 LAN IP: 192.168.3.1/24
Perform a VPN tunnel PING test as follows: 1) 2) 3) 4) Log into the management GUI of both SonicWALL appliances. Clear the Logs. Select the PING command on the Tools>Diagnostics page of the local Sonicwall. Enter the LAN interface address of the remote SonicWALL and press GO If Terminate on DMZ advanced option is selected on the remote peer, PING a server on the DMZ. The DMZ interface will not respond to a PING. If Apply NAT and firewall rules advanced option is enabled, use the LAN interface NAT address (the WAN IP address) and ensure appropriate rules exist to allow the ping and other desired protocols to the LAN subnet or hosts. If using DHCP over VPN, switch to specify destination networks and list the remote SonicWALL LAN IP address as a destination network to verify the VPN functionality. The first ping should result in a Destination Unreachable error (only one ICMP packet is sent). The ping should initiate the IKE negotiation. Repeat step 4 (ping a second time) If the ping succeeds the second time, then there is no problem with the VPN tunnel. If the second ping fails, review the IKE Initiator log and IKE Responder log to determine if and/or why the IKE negotiations failed
5) 6) 7) 8)
Note: If a server is not responding to PING across a tunnel that appears to be active, verify that there is not a routing or connectivity problem between the server and the SonicWALL local to it. Also, verify the TCP/IP configurations of the server.
Page 9 of 14
2003 SonicWALL, Inc. SonicWALL is a registered trademark of SonicWALL, Inc. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies.
Troubleshooting Guide: IKE VPN Initialization
Troubleshooting IKE VPN Tunnel Establishment
There are 3 basic scenarios to investigate if the IKE VPN tunnel fails to establish: 1) No Response to IKE Initiation Request 2) IKE Negotiation Fails 3) IKE Negotiation Completes, but No Traffic is Passing The log messages generated during the IKE negotiations will show quickly which of the scenarios is occurring and where to focus the troubleshooting. The log entries in the Initiator log are different than those in the Responder log. In most cases, the responder will provide more precise information when there is an SA proposal mismatch during the negotiations. The logs of both the IKE Initiator and IKE Responder should be checked when troubleshooting establishment of a VPN.
Scenario 1: No Response to IKE Initiation Request
Use the following table of log entries to determine troubleshooting steps to resolve a problem initiating the IKE negotiations. IKE Initiator Log Messages No IKE Initiator Start Negotiation message in log Troubleshooting Notes Check the following: Disable this SA box is not checked in SA of IKE Initiator. Destination subnet defined in SA of IKE Initiator.
IKE Initiator: No response Remote Party Timeout IKE Initiator: No response Remote Party Timeout IKE Initiator: No response Remote Party Timeout IKE negotiation aborted due to timeout Note: If IKE Initiator Log only shows several timeout messages and negotiation aborted after a short delay, then there is a communication problem between the Initiator and Responder.
Check the following: Network connectivity between the units. (Hint: Try to access remote unit HTTPS management console from a host behind the local unit) Disable this SA box is not checked in SA of IKE Responder. IPSec Gateway address in Initiator SA specifies WAN address of IKE Responder IPSec Gateway Name (if used) resolves to WAN address of IKE Responder IKE Access Rules are enabled on both SonicWALLs. No other firewalls in path blocking IKE (UDP 500) or IPSec (IP 50) protocols. Contact ISP to see if they are blocking IKE (UDP 500) or IPSec (IP 50) protocols.
Page 10 of 14
2003 SonicWALL, Inc. SonicWALL is a registered trademark of SonicWALL, Inc. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies.
Troubleshooting Guide: IKE VPN Initialization
Scenario 2: IKE Negotiation Failures
Use the following tables to identify pertinent log entries in the IKE Initiator and IKE Responder and appropriate troubleshooting steps to resolve the problem.
Troubleshooting with IKE Initiator Log Messages
IKE Initiator Log Messages Received notify: INVALID_ID_INFO Troubleshooting Notes Aggressive Mode request error: Set SA security policy to use Aggressive Mode in both units. SA name in local unit must be the same as the remote peer Unique Firewall Identifier (and vice-versa).
Received notify: PAYLOAD_MALFORMED
Shared Secret mismatch error
IKE Initiator: Received notify. NO_PROPOSAL_CHOSEN Note: IKE Responder log will provide specifics of this error.
SA Security Policy settings dont match or the destination network field in either SA is incorrect. Check the IKE Responder log for specifics of the error. Check the following SA Security Policy settings match: Phase 1 DH Group Phase 1 Encryption/Authentication Phase 2 Encryption/Authentication PFS should be either enabled or disabled on both units unit (in Advanced Settings) Phase 2 DH Group, if PFS is enabled If Specify destination networks option is selected in VPN SA, verify the following: Destination network field in each SA is defined on remote peer LAN or has a static route on the remote peer. If terminating on DMZ, destination network must be defined in DMZ If Apply NAT and firewall rules enabled, destination addresses must be configured in NAT.
IKE Responder: Received Aggressive Mode request (Phase 1) Note: If this log message shows in the IKE Initiator log after initiating an Aggressive Mode request. Check the IKE Responder log for an INVALID_ID_INFO error.
Page 11 of 14
Aggressive Mode request error: SA name in remote peer must be the same as the local units Unique Firewall Identifier in the Global VPN Settings (and vice-versa).
2003 SonicWALL, Inc. SonicWALL is a registered trademark of SonicWALL, Inc. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies.
Troubleshooting Guide: IKE VPN Initialization
Scenario 2: IKE Negotiation Failures (continued) Troubleshooting with Responder Log Messages (Part 1)
IKE Responder Log Messages (Basic) Received notify: INVALID_ID_INFO Troubleshooting Notes Aggressive Mode request error. Check the following: SA name in remote peer must be the same as the local units Unique Firewall Identifier in the Global VPN Settings (and vice-versa).
Failed payload verification after decryption. Possible preshare key mismatch.
Shared Secret mismatch
IKE Responder: IKE proposal does not match (Phase 1)
Phase 1 Encryption/Authentication mismatch
IKE Responder: Algorithms and/or keys do not match (Phase 2)
Phase 2 Encryption/Authentication mismatch
IKE Responder: ESP Perfect Forward Secrecy mismatch
PFS should be either enabled or disabled on both units unit (in Advanced Settings) Phase 2 DH Group mismatch for PFS (in Advanced Settings)
IKE Responder: No match for proposed remote network address
Proposed source network from IKE Initiator is not defined in the destination network field on the IKE Responder SA. If Apply NAT and firewall rules is enabled on IKE Initiator SA, destination field on IKE Responder needs to use the IKE Initiator public NAT address(es).
IKE Responder: Tunnel terminates inside firewall but proposed local network is not inside firewall
Destination network in IKE Initiator SA is not defined on LAN or static route on the IKE Responder.
Page 12 of 14
2003 SonicWALL, Inc. SonicWALL is a registered trademark of SonicWALL, Inc. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies.
Troubleshooting Guide: IKE VPN Initialization
Scenario 2: IKE Negotiation Failures (continued) Troubleshooting with Responder Log Messages (Part 2)
IKE Responder Log Messages (Advanced) IKE Responder: Tunnel terminates on DMZ but proposed local network is on LAN Troubleshooting Notes IKE Responder SA is configured to terminate on DMZ, but the proposed destination network is on the LAN.
IKE Responder: Tunnel terminates on LAN but proposed local network is on DMZ
IKE Responder SA is configured to terminate on LAN, but the proposed destination network is on the DMZ.
IKE Responder: Tunnel terminates outside firewall but proposed local network is not NAT public address
Apply NAT and firewall rules advanced option is enabled on the IKE Responder, but proposed destination network is not a public IP address on the IKE Responder.
IKE Responder: Proposed local network is 0.0.0.0 but SA has no LAN Default Gateway
The IKE Initiator SA is configured as default route for all internet traffic but the IKE Responder has no Default LAN Gateway (advanced option) address defined.
IKE Responder: Proposed remote network is 0.0.0.0 but not DHCP relay nor default route
Default LAN Gateway advanced option in IKE Initiator defines a gateway address, but the IKE Responder SA is not configured as default route for all internet traffic (nor is DHCP relay configured).
IKE Responder: Default LAN gateway is set but peer is not proposing to use this SA as a default route
Default LAN Gateway advanced option in IKE Responder defines a gateway address, but the IKE Initiator SA is not configured as default route for all internet traffic.
Page 13 of 14
2003 SonicWALL, Inc. SonicWALL is a registered trademark of SonicWALL, Inc. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies.
Troubleshooting Guide: IKE VPN Initialization
Scenario 3: IKE Negotiation Completes, but No Traffic is Passing
If traffic will not pass through the VPN tunnel after the IKE negotiations successfully complete, then the VPN tunnel protocol is being blocked. The NAT discovery entries will determine which protocol, IPSec or encapsulated IPSec, is being used for the tunnel. If using Aggressive Mode, check the IKE Responder log to find the NAT Discovery messages. In Aggressive Mode, only the IKE Responder performs the NAT Discovery process. Be sure to verify the problem is with the VPN tunnel and not an external routing problem. The problem can be isolated by changing advanced configurations to terminate on LAN, including the remote LAN interface subnet as destination network, and running PING directly from the local SonicWALL to the remote SonicWALL LAN interface address. NAT Discovery Log Messages NAT Discovery: No NAT/NAPT device detected between IPSec Security gateways Troubleshooting Notes Verify IPSec protocol (IP 50) is not being blocked by your ISP or another firewall
NAT Discovery: Local IPSec Security Gateway behind a NAT/NAPT Device or NAT Discovery: Remote IPSec Security Gateway behind a NAT/NAPT Device
The NAT device may be blocking UDP encapsulated IPSec packets. Check with the NAT device manufacturer to see if they know of a problem with blocking UDP encapsulated IPSec. Try disabling the NAT Traversal option if there are no other NAT devices in the tunnel path and the suspect NAT device supports IPSec pass-thru.
NAT Discovery: Peer IPSec Security Gateway doesnt support VPN NAT Traversal
Verify there are no NAT devices in the tunnel path by enabling NAT Traversal on both units. Verify IPSec protocol (IP 50) is not being blocked by your ISP or another firewall.
No NAT discovery messages found in either firewall log
Verify there are no NAT devices in the tunnel path by enabling NAT Traversal on both units. Verify IPSec protocol (IP 50) is not being blocked by your ISP or another firewall.
Page 14 of 14
2003 SonicWALL, Inc. SonicWALL is a registered trademark of SonicWALL, Inc. Other product and company names mentioned herein may be trademarks and/or registered trademarks of their respective companies.
Potrebbero piacerti anche
- Cisco CCNA Command Guide: An Introductory Guide for CCNA & Computer Networking Beginners: Computer Networking, #3Da EverandCisco CCNA Command Guide: An Introductory Guide for CCNA & Computer Networking Beginners: Computer Networking, #3Nessuna valutazione finora
- Troubleshooting IKE VPNDocumento9 pagineTroubleshooting IKE VPNjefersonsbNessuna valutazione finora
- SonicWALL VPN With Red Hat LinuxDocumento4 pagineSonicWALL VPN With Red Hat Linuxjpereira100% (2)
- Configuring An Ipsec VPN Tunnel Between A Cisco Sa 500 and A Mac Ipsecuritas ClientDocumento11 pagineConfiguring An Ipsec VPN Tunnel Between A Cisco Sa 500 and A Mac Ipsecuritas Clientjhoan9924Nessuna valutazione finora
- Palo Alto Interview QuestionsDocumento28 paginePalo Alto Interview QuestionsdezaxxlNessuna valutazione finora
- Chapter 3 - Setting Up Site-to-Site VPNs and Large-Scale VPNs - Securing Remote Access in Palo Alto NetworksDocumento47 pagineChapter 3 - Setting Up Site-to-Site VPNs and Large-Scale VPNs - Securing Remote Access in Palo Alto NetworksHeera SinghNessuna valutazione finora
- Configuring Cisco VPNDocumento15 pagineConfiguring Cisco VPNmstepp100% (3)
- CTM-200 IPsec VPN QuestionnaireDocumento12 pagineCTM-200 IPsec VPN Questionnairemohammedakbar880% (1)
- Thegreenbow Ipsec VPN Client Configuration Guide: Ingate FirewallDocumento15 pagineThegreenbow Ipsec VPN Client Configuration Guide: Ingate FirewallMedosevic LejlaNessuna valutazione finora
- Configuring Route Based IPSec With Overlapping NetworksDocumento13 pagineConfiguring Route Based IPSec With Overlapping NetworksRyanb378Nessuna valutazione finora
- ITNE2005LAB6-SecuringLocalAreaDocumento27 pagineITNE2005LAB6-SecuringLocalArearitadhikarycseNessuna valutazione finora
- Configuring Vpns Between Sonicos Standard and Sonicos EnhancedDocumento8 pagineConfiguring Vpns Between Sonicos Standard and Sonicos Enhancedtest2012Nessuna valutazione finora
- Lksn2019 Itnetwork Modul A PreDocumento11 pagineLksn2019 Itnetwork Modul A PreAhmad HabibiNessuna valutazione finora
- Lksn2019 Itnetwork Modul A ActualDocumento11 pagineLksn2019 Itnetwork Modul A Actualarizal putraNessuna valutazione finora
- Edge Router Lite Essential Configuration GuideDocumento12 pagineEdge Router Lite Essential Configuration GuideNuriffa Izzati100% (1)
- LCTN0013 Proxicast IPSec VPN Client ExampleDocumento20 pagineLCTN0013 Proxicast IPSec VPN Client ExampleProxicastNessuna valutazione finora
- Cisco Spiad - Labv1.3.1Documento91 pagineCisco Spiad - Labv1.3.1fernando JmzNessuna valutazione finora
- Citrix Easycall Gateway Telephony System Integrator'S Guide: For Alcatel Omnipcx EnterpriseDocumento16 pagineCitrix Easycall Gateway Telephony System Integrator'S Guide: For Alcatel Omnipcx EnterpriseKenza LazrakNessuna valutazione finora
- Configuring A VPN Using Easy VPN and An Ipsec Tunnel: Figure 6-1Documento12 pagineConfiguring A VPN Using Easy VPN and An Ipsec Tunnel: Figure 6-1Toufik AchrafeNessuna valutazione finora
- Cisco ASA 5520Documento47 pagineCisco ASA 5520sayritabelenNessuna valutazione finora
- Neo Gate Product Description 1008Documento49 pagineNeo Gate Product Description 1008Goran GrbicNessuna valutazione finora
- How To Configure IPSec VPNDocumento6 pagineHow To Configure IPSec VPNankitNessuna valutazione finora
- ASA5500 - Configuration - Guide - 8.4 and 8.6 - VPN - Configuring LAN-to-LAN VPNsDocumento1 paginaASA5500 - Configuration - Guide - 8.4 and 8.6 - VPN - Configuring LAN-to-LAN VPNschassisdNessuna valutazione finora
- SonicOS Standard 2 (1) (1) .0 Configuring NAT PoliciesDocumento10 pagineSonicOS Standard 2 (1) (1) .0 Configuring NAT PoliciesAbhijit PjNessuna valutazione finora
- G250 G350 Security PDFDocumento40 pagineG250 G350 Security PDFJosé DalmiNessuna valutazione finora
- Configuring NOE VoIPDocumento32 pagineConfiguring NOE VoIPpbartlett1977Nessuna valutazione finora
- Avaya CISCO3750E-POE InteroperabilityDocumento15 pagineAvaya CISCO3750E-POE InteroperabilityHeliosOmegaNessuna valutazione finora
- Asdm 6.4: Site-To-Site VPN Tunnel With Ikev2 Configuration ExampleDocumento9 pagineAsdm 6.4: Site-To-Site VPN Tunnel With Ikev2 Configuration ExampleAsha kumariNessuna valutazione finora
- Configuring AudioCodes NCite With Avaya SIP Enablement Services and Avaya Communication Manager To Support SIP TrunkingDocumento49 pagineConfiguring AudioCodes NCite With Avaya SIP Enablement Services and Avaya Communication Manager To Support SIP TrunkingSilvio RomeroNessuna valutazione finora
- What Is VPNTDocumento3 pagineWhat Is VPNTVineeth BabuNessuna valutazione finora
- IP Office Anywhere and Power Demo Resource GuideDocumento12 pagineIP Office Anywhere and Power Demo Resource GuidealiceiswonderfulNessuna valutazione finora
- CUCM8 IPO80 IPtkDocumento27 pagineCUCM8 IPO80 IPtkAbdulla SnrNessuna valutazione finora
- Lab 3.4 Configuring Site-To-Site Ipsec Vpns With SDM: Learning ObjectivesDocumento40 pagineLab 3.4 Configuring Site-To-Site Ipsec Vpns With SDM: Learning Objectivesnguoitronggiangho2k1Nessuna valutazione finora
- Csco LLDP MedDocumento11 pagineCsco LLDP MedAlex TejerinaNessuna valutazione finora
- 6.3.1.1 Lab - Securing Layer 2 SwitchesDocumento23 pagine6.3.1.1 Lab - Securing Layer 2 Switchesandy last100% (1)
- Cisco Voip/Ccme: Introduction To Cisco Unified Communication Manager Express (Callmanager Express - Cme)Documento28 pagineCisco Voip/Ccme: Introduction To Cisco Unified Communication Manager Express (Callmanager Express - Cme)Ministere EdificeNessuna valutazione finora
- PolycomSS CS1KDocumento36 paginePolycomSS CS1KIsrael MoraNessuna valutazione finora
- Volte CallDocumento9 pagineVolte CallAKJOSHINessuna valutazione finora
- Internet Key Exchange (IKEv2) ProtocolDocumento10 pagineInternet Key Exchange (IKEv2) ProtocolPrashant TiwariNessuna valutazione finora
- Fibeair® Ip-10G and Ip-10E: 7.2 Release NotesDocumento55 pagineFibeair® Ip-10G and Ip-10E: 7.2 Release NotesKarla VertiNessuna valutazione finora
- Configure Anyconnect Virtual Private Network (VPN) Connectivity On The Rv34X Series RouterDocumento13 pagineConfigure Anyconnect Virtual Private Network (VPN) Connectivity On The Rv34X Series RouterThe Maison MaidsNessuna valutazione finora
- Browser-Based Interface Quick Access GuideDocumento40 pagineBrowser-Based Interface Quick Access GuideSatish KumarNessuna valutazione finora
- SonicOS 5.9 SonicPoint Layer 3 Management GuideDocumento37 pagineSonicOS 5.9 SonicPoint Layer 3 Management GuideaarnulfoNessuna valutazione finora
- 6.3.1.1 Lab - Securing Layer 2 SwitchesDocumento22 pagine6.3.1.1 Lab - Securing Layer 2 SwitchesJson CañedaNessuna valutazione finora
- 11.3.1.2 Lab - CCNA Security ASA 5505 Comprehensive - InstructorDocumento65 pagine11.3.1.2 Lab - CCNA Security ASA 5505 Comprehensive - Instructorcheicktest1Nessuna valutazione finora
- Implementing A Sonicwall VPN in Your OrganizationDocumento11 pagineImplementing A Sonicwall VPN in Your Organizationmero_samyNessuna valutazione finora
- CloudVPNGuide UsingCloudVPNwithPaloAltoNetworksPA 3020Documento28 pagineCloudVPNGuide UsingCloudVPNwithPaloAltoNetworksPA 3020wilpraNessuna valutazione finora
- Silver Series Secrets: Video Tutorial CatalogDocumento5 pagineSilver Series Secrets: Video Tutorial CatalogEdinho De PaulaNessuna valutazione finora
- ZYXEL Application-Note PMG1005-T20B 1.0Documento22 pagineZYXEL Application-Note PMG1005-T20B 1.0JasonNessuna valutazione finora
- Advanced Features of Linux Strongswan The Opensource VPN SolutionDocumento17 pagineAdvanced Features of Linux Strongswan The Opensource VPN SolutionThinh LeNessuna valutazione finora
- Ipsec AdvancedDocumento24 pagineIpsec AdvancedSelma SelmiNessuna valutazione finora
- OTEC-S Am OTSBC 8AL90562ENAA 1 enDocumento12 pagineOTEC-S Am OTSBC 8AL90562ENAA 1 enlocuras34Nessuna valutazione finora
- ASDM 6.4 Site To Site VPN Tunnel With IKEv2Documento8 pagineASDM 6.4 Site To Site VPN Tunnel With IKEv2satya28Nessuna valutazione finora
- 04 - Interfaces Protocols (PDF Word)Documento12 pagine04 - Interfaces Protocols (PDF Word)Ashish NokiaNessuna valutazione finora
- Prod Mvision Unified Cloud Edge IntegrationDocumento11 pagineProd Mvision Unified Cloud Edge IntegrationDemétrio De Azevedo SiqueiraNessuna valutazione finora
- Linksys Rv082 VPN Router Interoperability Profile: C o M C OmDocumento11 pagineLinksys Rv082 VPN Router Interoperability Profile: C o M C OmhackergenomaNessuna valutazione finora
- Network with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationDa EverandNetwork with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationNessuna valutazione finora
- Set Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNDa EverandSet Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNValutazione: 5 su 5 stelle5/5 (1)
- Securing Application Deployment with Obfuscation and Code Signing: How to Create 3 Layers of Protection for .NET Release BuildDa EverandSecuring Application Deployment with Obfuscation and Code Signing: How to Create 3 Layers of Protection for .NET Release BuildNessuna valutazione finora
- D5056401 Scholar MXP Assembly-User GuideDocumento32 pagineD5056401 Scholar MXP Assembly-User GuidejohnemeryisiNessuna valutazione finora
- TANDBERG MXP Administrator Guide (F9)Documento359 pagineTANDBERG MXP Administrator Guide (F9)johnemeryisiNessuna valutazione finora
- H.323 Beacon: An H.323 Application Related End-to-End Performance Troubleshooting ToolDocumento6 pagineH.323 Beacon: An H.323 Application Related End-to-End Performance Troubleshooting TooljohnemeryisiNessuna valutazione finora
- Cisco TMS Install Guide 13-0Documento69 pagineCisco TMS Install Guide 13-0johnemeryisiNessuna valutazione finora
- Designing AV Automation For The Mediasite Rich Media RecorderDocumento26 pagineDesigning AV Automation For The Mediasite Rich Media RecorderjohnemeryisiNessuna valutazione finora
- CP IPS BestPracticesDocumento21 pagineCP IPS BestPracticesGabino PampiniNessuna valutazione finora
- Internal CommunicationDocumento11 pagineInternal Communicationanks0909Nessuna valutazione finora
- Nortel Networks Alteon Switched FirewallDocumento6 pagineNortel Networks Alteon Switched FirewallPF4ScribdNessuna valutazione finora
- Irca 173 CPD LogDocumento19 pagineIrca 173 CPD LogSerdar Aldanmazlar100% (1)
- A Different World: An Educational Tool Kit For Building Global JusticeDocumento252 pagineA Different World: An Educational Tool Kit For Building Global JusticeElvira TrugliaNessuna valutazione finora
- Power Planning Signal Route Closure PDFDocumento41 paginePower Planning Signal Route Closure PDFBaluvu JagadishNessuna valutazione finora
- 5g Vision DocumentDocumento37 pagine5g Vision DocumentPramaNessuna valutazione finora
- We The Urban Magazine Issue 6, 2013Documento84 pagineWe The Urban Magazine Issue 6, 2013Holly GolightlyNessuna valutazione finora
- Open by Paul Dravis Source Software Perspectives For DevelopmentDocumento54 pagineOpen by Paul Dravis Source Software Perspectives For DevelopmentKishan PunNessuna valutazione finora
- JSP TutorialDocumento16 pagineJSP Tutorialvilasmenon100% (2)
- Virgin Mobile-WATConsult Indian Panga LeagueDocumento2 pagineVirgin Mobile-WATConsult Indian Panga LeagueRahul ShenoyNessuna valutazione finora
- Prologue, Winter 2010, Vol. 42, No. 4Documento76 paginePrologue, Winter 2010, Vol. 42, No. 4Prologue MagazineNessuna valutazione finora
- Coffee House Project ReportDocumento11 pagineCoffee House Project ReportmayankNessuna valutazione finora
- Effects (Physical, Behavioural and Psycho-Social) of Using Mobile Phones and Other Devices With Internet Accessibility by ChildrenDocumento42 pagineEffects (Physical, Behavioural and Psycho-Social) of Using Mobile Phones and Other Devices With Internet Accessibility by Childrenshivani shindeNessuna valutazione finora
- B. Tech. CSE PDFDocumento37 pagineB. Tech. CSE PDFpriti089Nessuna valutazione finora
- Pertemuan 1Documento37 paginePertemuan 1Mul YonoNessuna valutazione finora
- Gab Hernandez Freelance Resume PDFDocumento2 pagineGab Hernandez Freelance Resume PDFGabriel HernandezNessuna valutazione finora
- Unit 5 Activity 5Documento9 pagineUnit 5 Activity 5Marian SalidoNessuna valutazione finora
- January 2019 PDFDocumento5 pagineJanuary 2019 PDFBadrun sham bin Ahmad TanzeziNessuna valutazione finora
- Digit 1209Documento135 pagineDigit 1209pmm67Nessuna valutazione finora
- Lis6711 Research Paper by Crystal StephensonDocumento8 pagineLis6711 Research Paper by Crystal Stephensonapi-470886892Nessuna valutazione finora
- Google Keep Headers FREEBIE Product InfoDocumento6 pagineGoogle Keep Headers FREEBIE Product InfoEnrique AlejandroNessuna valutazione finora
- Regulations - 2008Documento82 pagineRegulations - 2008BubbyOshinNessuna valutazione finora
- Quick Mikrotik / Freeradius HowtoDocumento6 pagineQuick Mikrotik / Freeradius HowtoBarnabie Riddick OpiyoNessuna valutazione finora
- HTTP Chunked Encoding - HttpWatchDocumento3 pagineHTTP Chunked Encoding - HttpWatchHector David ZenitNessuna valutazione finora
- 200 Google Ranking Factors TiHanson 530 1683528061Documento52 pagine200 Google Ranking Factors TiHanson 530 1683528061Dhiraj GuptaNessuna valutazione finora
- AUP CatalogDocumento128 pagineAUP Catalogbabatoto21Nessuna valutazione finora
- CCNA Latest 2017 PDFDocumento85 pagineCCNA Latest 2017 PDFArun SharmaNessuna valutazione finora
- Clark D, Blended LearningDocumento44 pagineClark D, Blended LearningTanja Che100% (1)
- License Certificate: Premium License (Unlimited Use Without Attribution)Documento2 pagineLicense Certificate: Premium License (Unlimited Use Without Attribution)hafuta1992Nessuna valutazione finora