Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
VPN
Caricato da
vanka7409Descrizione originale:
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
VPN
Caricato da
vanka7409Copyright:
Formati disponibili
MOBILE IP VPN CONNECTIVEY AND SECURITY
Mobile IP VPN Connectivity
1. Objective
This document describes a short overview of VPN technology and specifies the standards and
processes used. VPN is one part (but only part) of securing a mobile and distributed network.
2. Introduction
A virtual private network (VPN) is a group of computers connected to a private network (a network
built and maintained by an enterprise solely for its own use with limited public-network access), that
communicates "securely" over a public network.
Data VPNs typically have been implemented at the data link layer using Frame Relay and ATM
networking technologies for roughly ten years. Now, VPN services based on IP and the use of the
Internet are quickly gaining public interest and market acceptance. Like traditional VPNs, IP VPNs
utilize shared facilities to emulate private networks and deliver reliable, secure services to end users.
Mobile IP VPNs, which provide these services over wireless media, also use IP tunneling
technologies.
The business benefits of deploying Mobile VPNs (MVPNs) are numerous.
• Mobile IP VPNs can help companies reap benefits such as dramatically lowered WAN costs,
improved global connectivity, and better reliability, while enabling capabilities such as secure
extranet communications.
• MVPNs can provide remote workers with constant connectivity to corporate sites or to the ISPs
and ASPs of their choice.
• MVPNs also enable businesses and ISPs to outsource mobile access
• By enabling always on connectivity, Real time information can be shared.
3. Implementing Mobile VPNs
Various types of VPN connectivity implementations are possible depending on the business needs of
the contracting enterprise. These connections can be lumped as: gateway-to-gateway, gateway-to-
host, host-to-gateway, and host-to-host.
Various protocols can be used to implement MVPN: IP Security (IPSec) protocols, Multi-Protocol
Label Switching (MPLS) and L2 Tunneling Protocol (L2TP). IPSec based Firewall’s are common and
appropriate for most business needs.
IPSec is made up of three main protocols:
• Authentication Header (AH) Protocol provides integrity and authentication to IP packets.
• Encapsulating Security Payload (ESP) protocol is used to provide encryption for IP data.
• Internet Key Exchange (IKE) Protocol is used for all IPSec negotiations.
IPSec is typically used in one of the two modes: gateway-to-gateway or host-to-gateway. Refer to
Figure1, figure 2 for those MVPN implementations. Gateway-to-gateway connection is the preferred
MVPN implementation because host-to-gateway end-to-end connection contain important
weaknesses:
• Mobile must support IPSec client
• IPSec will use up to 30% of airlink bandwidth
• NAT (Network Address Translation) is not available
m-trilogix VPN security 2
FW/Gateway
GPRS Internet Corporate
Network ATM, FR Intranet
VPN Client
FW/Gateway
Public Wireless
VPN Mobile user Public Network Enterprise Network
Network
IP Encrypted IP Tunnel IP
IPSec Tunnel
Fig.1 VPN -- Host-to-Gateway connection
FW/Gateway
GPRS Internet Corporate
Network ATM, FR Intranet
no VPN
software
FW/Gateway
Public Wireless
VPN Mobile user Public Network Enterprise Network
Network
IP/PPP GTP Tunnel IP/PPP Encrypted IP Tunnel IP/PPP
IPSec Tunnel
Fig.2 VPN -- Gateway-to-Gateway Connection
MVPN access is provided through one of two access modes in GPRS – Transparent or Non-
Transparent. GPRS transparent access mode is intended to provide only IP-based communication
and creation of IP-type Packet Data Protocol (PDP) context at GGSN.
With Transparent GPRS access mode:
• GPRS operators offer connectivity to IP network without any user authentication
• Mobile devices do not send any authentication request at PDP context activation
• GPRS operators issue public addresses to GPRS users
The host-to-gateway VPN connection is the only solution in GPRS transparent access mode. The
transparent access mode needs more airlink bandwidth, more public IP addresses and IPSec
supported mobile devices.
A wireless GPRS network is already deployed with non-transparent GPRS access:
m-trilogix VPN security 3
• The MS is dynamically allocated a private IP address.
• GGSNs request user RADIUS authentication based on user authentication requests made at
PDP context activation.
• Tunneling IPSec protocols are used between GGSN and ISPs to transmit user traffic to a final
destination point, such as: corporate private network.
In non-transparent access service operation, the GPRS network needs to assign APN network
identifiers to corporations. The APNs are used by the SGSN to select the GGSN to be addressed
for a specific group of corporate mobile users and are also used for billing. The GGSN determines
the IP addresses of the GGSNs to which mobile users will be attached.
Unique APNs for large corporations allow an additional level of authentication to the corporate
customer as it allows a unique access profile for the customer to be implemented in RADIUS.
The MVPN system architecture is shown in Figure 3.
Private Network Private Network
S G
B Corporate
G G
S Internet Intranet
S S
S
Laptop computer N N
FW/ VPN FW/VPN
Radio Gateway Gateway
Application
IP/PPP IP/PPP
Relay Relay
L2TP
SNDCP GTP GTP L2TP
SNDCP
LLC UDP/ UDP UDP UDP
LLC TCP
Relay
BSSGP
RLC RLC BSSGP IP IP IPSec IP/IPSec
Network Network L2
L2
MAC MAC Service Service L2
GSM RF GSM RF L1 bis L1 bis L1 L1 L1
MS Um BSS Gb Gn
SGSN
GGSN Gi
Fig3. GPRS Non-Transparent Access, IPSec-Based VPN
4. Mobile VPN Gateway and Capacity
There are many choices to build a VPN to link corporate networks. In theory, all of the IPSec-based
VNP gateways are compatible with standard VPN-1 gateways. Nevertheless, extensive testing is
required to determine the extent of this compatible.
VPN concentrators are implemented at Toronto, Montreal and Vancouver to ensure that sufficient
capacity is available and operational requirements are met.
m-trilogix VPN security 4
A typical standard VPN implementation from major carriers would include:
• IPSec-Based supported
• Authentication Header: MD5 (Message-Digest Algorithm)
• Encapsulating Security Payload: 3DES(triple Data Encryption Standard)
• Internet Key Exchange: Diffie-Hellman
• No Integrated Certificate Authority (CA)
• Interface: 10- or 100-Mbit/s Ethernet through Internet
• Concurrent connections: 50+
5. Conclusion
VPN technology is an important part of an overall secure solution for protecting data within a
mobile, wireless or distributed network. However VPN technology is not by itself sufficient to
ensure a secure operation. Each layer of the OSI stack must be protected and secure. VPN
technology is sufficient in many cases to protect the data link layer and transfer of data but it should
be augmented with other technologies. The following grid provides a simple overview of
technologies in securing a mobile architecture:
Layer 7 Application x.400, Programs that use the Network SSID (hardware to access points)
Layer 6 Presentation SNMP, FTP, Functions apps need Extensible Authentication Protocol,
Access Lists, SSL, SHTTP
Layer 5 Session Protocol software which handles Wireless Equivalency Protocol
functionality
Layer 4 Transport TCP, UDP, end to end, sce and dest Proprietary Token Card, Certificates
hosts
Layer 3 Network IP. Host/Network Communication Mobile IP, ICMP, IPSEC, VPN
Layer 2 Data Link HDLC, Frames between host and packet PPP, 802.1x, VPN
switches
Layer 1 Physical Interconnection host and network 802.11b, VPN
While VPN’s provide speed, and secure access in joining nodes on disparate networks, they are only
one piece of the greater security puzzle. Most major Telco carriers provide M-VPN access and
services and care should be taken by clients to understand how M-VPNs fit into an overarching
security architecture.
If you have any questions please call 416-259-3343 or email us at info@m-trilogix.com
m-trilogix Ltd. 47 Jutland Rd., Etobicoke, M8Z 2G6
m-trilogix VPN security 5
Potrebbero piacerti anche
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (894)
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (587)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (265)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (119)
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- KS8000Documento16 pagineKS8000chrisNessuna valutazione finora
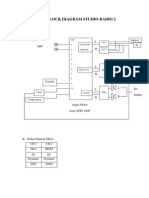
- Block Diagram Studio Radio 2Documento1 paginaBlock Diagram Studio Radio 2fharhyeNessuna valutazione finora
- Video Editor ResumeDocumento5 pagineVideo Editor ResumeprashantmachharNessuna valutazione finora
- UniFi Security Gateway DSDocumento4 pagineUniFi Security Gateway DSGerson MayerNessuna valutazione finora
- BEHRINGER - UCA202 P0484 - Product Information Document PDFDocumento6 pagineBEHRINGER - UCA202 P0484 - Product Information Document PDFbeeej.bNessuna valutazione finora
- Panasonic BT LH900 ManualDocumento28 paginePanasonic BT LH900 ManualElectra/Off TraxNessuna valutazione finora
- Sansui Rz-3700av 5700av 7700avDocumento53 pagineSansui Rz-3700av 5700av 7700avjose sebastian rojas galdamesNessuna valutazione finora
- Ol IctDocumento5 pagineOl IctDasun Nilanjana100% (2)
- HP LaserJet P4014 Error ListDocumento8 pagineHP LaserJet P4014 Error ListKendrew BladesNessuna valutazione finora
- VoLTE OverviewDocumento36 pagineVoLTE OverviewNguyễn Thanh Thủy50% (2)
- GSM WhitepaperDocumento3 pagineGSM WhitepaperMichael LionNessuna valutazione finora
- Bureå Church Organ SoundfontDocumento4 pagineBureå Church Organ SoundfontluisNessuna valutazione finora
- Datasheet Wdeh220 20120702-14235212729Documento4 pagineDatasheet Wdeh220 20120702-14235212729Marjan StojanovskiNessuna valutazione finora
- Owner's Manual: Integrated High Definition LCD TelevisionDocumento64 pagineOwner's Manual: Integrated High Definition LCD TelevisionyamaharahNessuna valutazione finora
- Final Exam CEN534Documento2 pagineFinal Exam CEN534Omari Juma KilalileNessuna valutazione finora
- Lenovo B320c320r4 - CIH61S Daoquamb6doDocumento55 pagineLenovo B320c320r4 - CIH61S Daoquamb6doConsorcio Delta XIX50% (4)
- Control Center Operator GuideDocumento132 pagineControl Center Operator GuideCarlos Rumay100% (1)
- System Administrator BiodataDocumento3 pagineSystem Administrator BiodataPankaj NinganiaNessuna valutazione finora
- Mircom TX3-TOUCH-F22 Data SheetDocumento3 pagineMircom TX3-TOUCH-F22 Data SheetJMAC SupplyNessuna valutazione finora
- BSNL Summer Training ReportDocumento39 pagineBSNL Summer Training Reportbhumika9verma100% (1)
- The Need for Free Public Wi-FiDocumento2 pagineThe Need for Free Public Wi-FiAmsyar HaikalNessuna valutazione finora
- Raspberry Pi Wireless Notice BoardDocumento29 pagineRaspberry Pi Wireless Notice BoardManjunath RajashekaraNessuna valutazione finora
- FCP Translation Results 2019-01!25!11-39Documento2 pagineFCP Translation Results 2019-01!25!11-39Toma Vasile MarianNessuna valutazione finora
- White Paper A Comparison of Video Wall TechnologiesDocumento28 pagineWhite Paper A Comparison of Video Wall TechnologiesKaren SimsNessuna valutazione finora
- WL-1120AP Manual PDFDocumento39 pagineWL-1120AP Manual PDFjarkovrbkoNessuna valutazione finora
- CD. DVD Spiral Length and SpeedDocumento17 pagineCD. DVD Spiral Length and SpeedLollipopsuckerNessuna valutazione finora
- Persuasive Speech OutlineDocumento3 paginePersuasive Speech Outlineapi-533742755Nessuna valutazione finora
- UNITE 200 User ManualDocumento34 pagineUNITE 200 User ManualGiovanni León Trujillo GuarderasNessuna valutazione finora
- WRT54Gv7 7.00.8 FwReleaseNotesDocumento2 pagineWRT54Gv7 7.00.8 FwReleaseNoteshn2379Nessuna valutazione finora
- Ricoh Pro 5100s BrochureDocumento12 pagineRicoh Pro 5100s BrochurePolygonNessuna valutazione finora