Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Hardware Design of Aes S-Box Using Pipelining Structure Over GF ( (2) )
Caricato da
Mustafamna Al SalamDescrizione originale:
Titolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Hardware Design of Aes S-Box Using Pipelining Structure Over GF ( (2) )
Caricato da
Mustafamna Al SalamCopyright:
Formati disponibili
HARDWARE DESIGN OF AES S-BOX USING PIPELINING
STRUCTURE OVER GF((24)2)
Ahmed H. Sawalmeh
Technical and Vocational Training Corporation, Saudi Arabia
sawalmeh@gotevot.edu.sa
ABSTRACT Consequently, early hardware implementations
of AES began with various loop unrolled architectures
High data throughput AES hardware architecture is [1]-[2], [8], where huge tables were generated with
proposed by partitioning the ten rounds into sub-blocks of limited number of architecture optimizations. Thus, a
repeated AES modules. The blocks are separated by pioneer attempts from V. Rijmen [7] proposed an AES s-
intermediate buffers providing a complete ten stages of box implementation based on composite field [2] which
AES pipeline structure. In addition, the AES is internally considered as the firs step in compaction the AES
evenly divided to ten pipeline stages; with the addition implementation [6],[10],[11].
feature that the shift rows block (ShiftRow) is structured
to operate before the byte substitute (ByteSubstitute) Therefore, Galois fields serves as a vehicle for
block. This proposed swapping operation has no effect several AES hardware implementation blocks. In general,
on the AES encryption algorithm; however, it streamlines most of the current hardware architectures were based on
the processing of four blocks of data in parallel rather memory, shift register, or pipeline approaches [8]-[10],
than 16 blocks which is considered the key advantage for where these choices are limited to its applications.
area saving. We evaluate the performance of our new Besides, many of these attempts provide performance
implementation and current implementations in terms of advantages tradeoff between area and speed; such as,
throughput rate and hardware area for ALTERA iterative looping provides small silicon area and low data
MAX3000A family FPGA EMP3128ATC100-5. The rate of throughput, while pipelining gives high data rate
simulation results show that the proposed AES has higher and large area overhead and might not be attractive for
throughput rate of about 4.25% than the general AES modes with feedback operations [6],[9],[10], [11].
pipeline structure with a saving hardware area of 56%.
In this brief, we proposed a new pipeline FPGA
Index Terms— AES pipeline, FPGA, GF((24)2), implementation of AES algorithm that provides high data
Rijndael, S-BOX throughput and small hardware area in comparing to
current existing pipeline designs. The proposed design
1. INTRODUCTION reorder the ByteSub and ShiftRow operations; such that,
4-byte instead of 16-byte are processed in parallel,
The National Institute of Standards and Technology yielding a small hardware area. Furthermore, the design
(NIST) have initiated a process to develop a Federal adhere deep pipelining of 10 stages for one AES block,
Information Processing Standard (FIPS) [3] for the resulting in 110 pipeline stages for complete 10 rounds
Advanced Encryption Standard (AES) [1]. In October of AES blocks, which is the key advantage for high
2000, NIST announced Rijndael as the winner of throughput design.
Advanced Encryption Standard (AES) contest in effort to
address threatened key size of Data Encryption Standard Analysis and performance evaluations were
(DES). Currently, most AES algorithms are implemented adequately performed by having the general pipeline AES
in software [9]; thereby, the secret key is vulnerable to algorithm on the same FPGA device and compared
attacks and relies on underlying programs. In addition, thoroughly with our proposed design in terms of area and
achievable speed by software implementation is not throughput. In addition, all simulations were conducted
acceptable for internet applications such as routers [9]. for one block and 16 blocks of input data, where each
This leads to hardware design of AES where parallel block consists of 16 bytes.
processing and pipelining is possible [4], [7]. Thus,
hardware systems offer superior performance with higher The paper is organized as follows; in section 2
throughput [10]. Moreover, hardware implementations we present the proposed designs structure and
are considered physically secured and preclude tempering mathematical comparative analysis, FPGA hardware
by an outside attacker. design is the subject of section 3. Then, section 4
presents experimental results and discussion. Finally, we
present the conclusion in section 5.
2. DESIGN STRUCTURE AND MATHEMATICAL
COMPARATIVE ANALYSIS
In this section, we evaluate two general designs for AES
algorithm against our proposed design. The first design
does not have the advantage of pipeline and strictly use
iterative looping approach, in contrast, to second design
which uses pipeline buffers between ten AES stages. On
the other hand, our design uses the pipeline architecture
of ten AES pipeline stages as well as it divides the AES
into ten stages yielding an over all of 110 pipeline stages.
The resulting speed in terms of throughput rate and Figure 1. General structure for the AES encryption
implementation area is evaluated and compared with algorithm.
existing design implementations in terms of the same gate
technology factor and pipeline architectural measure in 2.1. General AES structure without pipelining
[12] . We began the design of the AES by analyzing the
basic architecture as introduced in figure 1 [3], which
shows structure of the AES round for encryption. In
In this architecture we implement only one round with
Iterative looping structure; such that, the data-path
addition, let’s define the following notations:
consists of Key Addition, Mix Column, Byte-Substitution,
and Row Shift as clearly demonstrated in Figure 1 [7].
Ngate: Number of cascaded gates
Gate_delay: ALTERA MAX3000A 2-input
2.1.1. Time analysis
AND gate delay, 1.636 nano
second (nsec)
Number_of_rounds: Number of AES rounds The amount of time required to encrypt N blocks for 10
Number_of_blocks: Number of raw data coming rounds can be evaluated using the following:
blocks
N_logest_pipe: Longest cascaded number of T = Number_of_blocks × Number_of_rounds ×
gates between two pipelines, 9 Ngate× Gate_delay (1)
gates
N_BS: Cascaded number of gates for
ByteSubstitution, 33 gates For one block of input data which is equal to 16 byte of
N_SR: Cascaded number of gates for information:
ShiftRowTransformations, 5 gates
N_MC: Cascaded number of gates for T = 1 x 33 x 10 x 1.636 + (N_SR + N_MC +
MixColumns Transformations, 3 N_ARK) x 10 (2)
gates = (54 + K) x 10
N_ARK: Cascaded number of gates for = (540 + 10K) ns
AddRoundKey Transformations, = (540 + 10 x 11 x 1.636) = 719.9 ns
3 gates
K: (N_SR + N_MC + N_ARK) x For 1600 blocks of input data which is equal to 25600
Gate_delay byte of information:
M: Number of pipeline stages
N: Number of data blocks, where T = 1600 x 33 x 10 x 1.636 + (N_SR + N_MC +
each block is 16 bytes of data N_ARK) x 10
= 1600 x (54 + K) x 10 = (864000 + 16000K) (3)
ns = 1,1150,880 ns
2.2. General AES structure with 10 pipeline stages
In this structure, the implementation of a fully pipelined
AES using deep pipeline structure is used. The AES
Iterative Looping architecture must be converted into a
suitable form for deep pipelining as in figure 2; this is
achieved by removing all the loops to form a loop-
unrolled design, and by replicating the round function
hardware and registering the intermediate data between
rounds, where the data is moved through the round
execution resources. On each clock cycle, a new item of
data (1 block) is input and progress over 10 cycles
through the pipeline resulting in the output of data at each
cycle.
Figure 2. AES with 10 pipeline stages
2.2.1. Time analysis
The amount of time required to encrypt N blocks for 10
rounds can be evaluated using the following:
T = [(N-1) + M] x Ngate x Gate_delay (4)
For one block of input data which is equal to 16 bytes of
information:
T = [(1-1) +10] x (33 x 1.636 + K)
Figure 3. Proposed AES pipeline design
= [540 + 10K] ns. (5)
= 719.3 ns
For 1600 blocks of input data which is equal to 25600 2.3.1. Time analysis
byte of information:
The amount of time required to encrypt N blocks for 10
T = [(1600 – 1) + 10] x (33 x 1.636 + K) rounds can be evaluated using the following:
= [86886 + 1609K] ns (6)
= 115,735 ns T = [((N x 16/4) -1) + K] x [N_logest_pipe x (7)
Gate_delay] + (N x 16/4
2.3. Proposed AES pipeline structure
For one block of input data which is equal to 16-byte of
information:
In this section, the architecture evaluation of the proposed
design is achieved, where the AES is divided equally into
T = [(16/4 -1) + 11] x [9 x 1.636] + 4
ten pipeline stages with equal gates delay of about nine
= 14 x 15 = 214 ns (8)
gates per stage. In addition, 10 AES blocks are used
which are separated by pipeline stages resulting in total
For 1600 blocks
eleven stages per each round as depicted in Figure 3. In
order to reduce the area and alleviate the processing of all
T = [((1600 x 16/4) – 1) + 110] x [9 x 1.636] +
16-byte (one block) at a single AES, the ByteSub and
(1600 x 16/4) (9)
ShiftRow operation in Figure 1 are reordered as clearly
= 6509 x 15 = 104,035 ns
shown in this figure.
In summary, the mathematical time delays to
encrypted N blocks of data for different types of AES
architectures, which are estimated in equations (1)-(9),
are summarized in Table 1. The results of our proposed
architecture are clearly outperformed the existing
structures in terms of throughput data rate.
and by replicating the round function hardware and
AES Total time Total time registering the intermediate data between rounds as in
Hardware for one block for 16 blocks Figure 6, where the data is moved through the round
Types (ns) (ns) execution resources. On each clock cycle, a new item of
General 719.3 1,150,880 data (4-bytes) is input and progresses over numerous
AES cycles through the pipeline resulting in the output of data
AES with 719.3 115,735 each cycle.
10
Pipeline
Proposed 214 104,035
AES
Table 1. Mathematical estimation time for three different
AES architectures.
3. FPGA HARDWARE DESIGN
The S-box is usually implemented as a look-up table
consisting of 256 entries; each entry is 8 bits wide; it is
fast and inexpensive in terms of power consumption, as Figure 6. AES S-box with pipelining Data Flow.
the study in [6]-[8] indicates. The most compact AES S- All blocks used to implement the S-BOX are
box implementations is the one based on inversion in the discussed and implemented using HDL Verilog. These
composite field over GF as in Figures 4-5, which are blocks are square unit, multiplication unit, inversion unit,
considered as a basis for our design. Thus, we used fully
XOR unit, Isomorphic ä, Isomorphic ä inverse, A
combinational logic implementation of inversion in
Isomorphic ä, A Isomorphic ä inverse, and MUX unit.
composite field as described in [8].
We also optimize the synthesization, gate implementation,
and the timing analysis for each S-Box block.
4. EXPERIMENTAL RESULTS AND
DISCUSSION
FPGA simulation results demonstrate similarities between
mathematical analysis and actual hardware
representations. Many synthesized optimizations
techniques were used and floor plan manual arrangement
Figure 4. S-box implementation suitable for encryption
of slices was follow in order to utilize the device cells and
and decryption.
minimize the routing. There was no global routing and
components were locally interconnects. Small variations
of timing were expected due to the device capacity and
cells structure which were summarized in Table 2, and in
Figure 13.
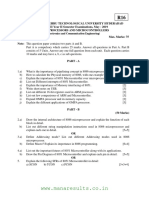
Case Design Time (ns)
1 General AES T=1,150,970
without
pipelining
Figure 5. Inversion in GF(24)2) 2 Fully pipelining T=116,867
AES
Consequently, the design of a fully pipelined 3 Fully pipelining T= 111,890
with sub pipelining AES using deep pipeline structure is with 10 sub
implemented. In this architecture each round contains 10 pipelining AES
stages of pipeline with 9-gate delay per stage; such that, Table 2. FPGA simulation results for total time 1600
each gate delay is provides 1.636 ns for ALTERA blocks AES encryptions.
MAX3000A device technology. The AES iterative
looping architecture must be converted into an adequate
and evenly form for deep pipelining. This is achieved by
removing all the loops to form a loop-unrolled design,
Total time to encrypt 1600 Blocks our proposed design is the solution to be adapted. One
of the draw back feature of the design is larger power
1,400,000 consumptions due to fully pipeline structure, and large
1,150,970
1,200,000
time consuming for synthesization and floor plan for
Time in nsec
1,000,000
800,000 hardware design.
600,000
400,000
116,867 111,890
200,000 6. REFERENCES
0
General AES Fully pipelining AES Fully pipelining with
without pipelining 10 sub pipelining [1] FIPS PUB 197, Advanced Encryption Standard (AES).
AES National Institute of Standards and Technology, U.S.
Design Name Department of Commerce, November 2001;
http://csrc.nist.gov/publications/fips/fips197/fips-197.pdf
Figure 13. Total time for 1600 blocks. [2] Kris Gaj, and Pawel Chodowiec, Hardware performance
of the AES finalist's survey and analysis of results. George
Mason University. Proc. 3rd Advanced Encryption Standard
As a result, the following observations can be depicted: (AES) Candidate Conference, New York, 2000:1-5.
[3] A. Elbirt, Recon_gurable Computing for Symmetric-Key
Al-gorithms, Ph.D. thesis, Department of Electrical
Throughput for fully pipelining AES is 89.846% Engineering, Worcester Polytechnic Institute, 2002.
times higher in than general AES without pipelining [4] Elena Trichina, and Tymur Kokishko, Secure AES
(iterative looping); however, the area is about Hardware Module for Resource Constrained Devices. Security
90.79% times larger than the general AES without in Ad-hoc and Sensor Networks. First European Workshop.
pipelining. ESAS 2004, Heidelberg ,Germany, August 6, 2004; (3313):215-
229.
Throughput for fully pipelining with ten sub [5] Sumio Morioka, and Akashi Satoh, An Optimized S-BOX
pipelining AES is 90.27% times higher than general Circuit Architecture for low power AES Design. IBM Research,
Tokyo Research laboratories, CHES 2002; (2523):172-186.
AES without pipelining, but the area is about 68.75%
[6] N. Sklavos, O. Koufopavlou, "Architectures and VLSI
times larger than the general AES without pipelining. Implementations of the AES-Proposal Rijndael," IEEE
Transactions on Computers, Vol. 51, Issue 12, pp. 1454-1459,
Throughput for fully pipelining with ten sub 2002.
pipelining AES is 4.25% times higher than fully [7] Akashi Satoh, and Sumio Morioka, Unified Hardware
pipelining AES; however, the area is about 56% Architecture for 128-Bits Block Ciphers AES and Camellia.
smaller than the fully pipelining AES IBM Research, Tokyo Research laboratories, CHES 2003;
(2779):304-318.
[8] Wolfram Drescher, Kay Bachmann 1, and Gerhard
Fettweis, VLSI Architecture for Non-Sequential Inversion Over
5. CONCLUSION GF(2m) Using the Euclidian Algorithm. Mobile
Communications Systems, Dresden University of Technology, D
New hardware architecture is proposed for AES - 01062 Dresden. sponsored in part by the Deutsche
algorithm over GF((2)4)2and compared against two AES Forschungsgemeinschaft within the Sonder for schung sbereich
hardware structures which are iterative looping and ten SFB 358.
rounds pipeline approach. The physical implementations [9] Joan Daemen and Vincent Rijmen, The Design of
of the three structures were conducted through FPGA Rijndael, AES - The Advanced Encryption Standard, Springer-
ALTER MAX3000A device. The comparison analysis Verlag 2002; 238.
[10] Pawel Chodowiec, and Kris Gaj, Very Compact FPGA
show that our proposed design has the advantage of
Implementation of the AES Algorithm. George Mason
saving area of about 56% over general ten AES round University, CHES 2003; (2779):319-333.
pipeline structure, and provides a higher throughput of [11] Tim Good, and Mohammad Benaissa, AES on FPGA
about 4.25%. Furthermore, it gives a superior From the Fastest to the Smallest. University of Sheffield,
throughput advantage over iterative looping AES Department of Electrical and computer Engineering, CHES
structure of about 90.27% rate; however, the area is 3.6 2005; (3659):427-440.
times larger than the iterative looping structure. [12] Amos R. Omondi, The Microarchitecture of Pipelined and
The main key advantage for saving area is the Superscalar Computers, Kluwer Academic Publishers, 1999.
rewording of ByteSub and ShiftRow which streamlines
the process of evaluating four bytes of data in parallel
rather than having 16 bytes in parallel with all required
hardware. Another key feature is having high throughput
by partitioning the AES into ten sub-blocks with
intermediate buffers between them; thus, creating a deep
pipelining structure for complete ten AES blocks.
As a result, for applications that starve for
increase instruction throughput and small area overhead,
Potrebbero piacerti anche
- Parallel AES Encryption EnginesDocumento12 pagineParallel AES Encryption EnginesmohamedNessuna valutazione finora
- Optimized Architecture For AESDocumento15 pagineOptimized Architecture For AESbit09486Nessuna valutazione finora
- Compact Core Aes: Efficient Design & Implementation OFDocumento50 pagineCompact Core Aes: Efficient Design & Implementation OFtaner56Nessuna valutazione finora
- 04 NPSC 39 Mostafa 39 - FastCrypto PDFDocumento12 pagine04 NPSC 39 Mostafa 39 - FastCrypto PDFDomenico ArgenzianoNessuna valutazione finora
- Circuit and System Design For Optimal Lightweight AES Encryption On FPGADocumento11 pagineCircuit and System Design For Optimal Lightweight AES Encryption On FPGAchaitanya sNessuna valutazione finora
- A Compact 8-Bit AES Crypto-Processor: F. Haghighizadeh, H. Attarzadeh, M. SharifkhaniDocumento5 pagineA Compact 8-Bit AES Crypto-Processor: F. Haghighizadeh, H. Attarzadeh, M. SharifkhaniVinayak KumarNessuna valutazione finora
- Ultra-Low Power S-Boxes Architecture For AES: Xing Ji-Peng, ZOU Xue-Cheng, Guo XuDocumento6 pagineUltra-Low Power S-Boxes Architecture For AES: Xing Ji-Peng, ZOU Xue-Cheng, Guo XuDam Minh TungNessuna valutazione finora
- S-Box Base PaperDocumento11 pagineS-Box Base PaperDon RajuNessuna valutazione finora
- 6614 Ijcsit 03Documento21 pagine6614 Ijcsit 03Anonymous Gl4IRRjzNNessuna valutazione finora
- Abstract - The Choice of A Platform, Software, ASIC Or: Ntroduction Algorithm Analysis and ImplementationDocumento4 pagineAbstract - The Choice of A Platform, Software, ASIC Or: Ntroduction Algorithm Analysis and ImplementationMustafamna Al SalamNessuna valutazione finora
- Pipeline Dae S With FeedbackDocumento10 paginePipeline Dae S With Feedbackyame asfiaNessuna valutazione finora
- A Scalable Decoder Architecture For IEEE 802.11n LDPC CodesDocumento5 pagineA Scalable Decoder Architecture For IEEE 802.11n LDPC CodesSiddhant MehraNessuna valutazione finora
- Low-Power and Area-Optimized VLSI Implementation of AES Coprocessor For Zigbee SystemDocumento6 pagineLow-Power and Area-Optimized VLSI Implementation of AES Coprocessor For Zigbee Systemjohan wahyudiNessuna valutazione finora
- Design and Implementation of Efficient Advanced Encryption Standard Composite S-Box With CM-ModeDocumento9 pagineDesign and Implementation of Efficient Advanced Encryption Standard Composite S-Box With CM-Modegunasekaran kNessuna valutazione finora
- Ins D 13 1975Documento16 pagineIns D 13 1975Azizul BaharNessuna valutazione finora
- High Performance and Scalable GPU Graph TraversalDocumento15 pagineHigh Performance and Scalable GPU Graph TraversalkumarabarbarianNessuna valutazione finora
- Transactions Letters: Efficient and Configurable Full-Search Block-Matching ProcessorsDocumento8 pagineTransactions Letters: Efficient and Configurable Full-Search Block-Matching ProcessorsrovillareNessuna valutazione finora
- Implementation of Aes and Rsa Algorithm On Hardware PlatformDocumento5 pagineImplementation of Aes and Rsa Algorithm On Hardware PlatformHanin TANessuna valutazione finora
- Architectures For Mixcolumn Transform For The Aes: P. Noo-Intara, S. Chantarawong, and S. ChoomchuayDocumento5 pagineArchitectures For Mixcolumn Transform For The Aes: P. Noo-Intara, S. Chantarawong, and S. ChoomchuayNgọc LợiNessuna valutazione finora
- Integrated Design of AES (Advanced Encryption Standard) Encrypter and DecrypterDocumento9 pagineIntegrated Design of AES (Advanced Encryption Standard) Encrypter and Decrypteruptcalc2007Nessuna valutazione finora
- Signal Intagrity Simulation of PCIE PDFDocumento5 pagineSignal Intagrity Simulation of PCIE PDFvijithacvijayanNessuna valutazione finora
- High-Throughput Multi-Key Elliptic Curve Cryptosystem Based On Residue Number SystemDocumento8 pagineHigh-Throughput Multi-Key Elliptic Curve Cryptosystem Based On Residue Number SystemRaúl AponteNessuna valutazione finora
- High-Speed and Energy-Efficient Carry Skip Adder Operating Under A Wide Range of Supply Voltage LevelsDocumento8 pagineHigh-Speed and Energy-Efficient Carry Skip Adder Operating Under A Wide Range of Supply Voltage LevelsTechnos_IncNessuna valutazione finora
- Answers:: Ans: (B) (B) It Point To The Next InstructionDocumento13 pagineAnswers:: Ans: (B) (B) It Point To The Next InstructionronyiutNessuna valutazione finora
- Parity Based Fault Detection Approach For The Low Power S-Box and Inverse S-BoxDocumento6 pagineParity Based Fault Detection Approach For The Low Power S-Box and Inverse S-BoxkasjaskdNessuna valutazione finora
- I E XY O - R D 2D M N C: Mproved Xtended N Chip Outing in Iametrical ESH ODocumento10 pagineI E XY O - R D 2D M N C: Mproved Xtended N Chip Outing in Iametrical ESH OAnonymous e4UpOQEPNessuna valutazione finora
- CRYPTACUS 2018 Paper 30 PDFDocumento4 pagineCRYPTACUS 2018 Paper 30 PDFMircea PetrescuNessuna valutazione finora
- Wireless Sensor NetworksDocumento5 pagineWireless Sensor NetworksBase Building AcademyNessuna valutazione finora
- An Efficient Hardware Design and Implementation of Advanced Encryption Standard (AES) AlgorithmDocumento5 pagineAn Efficient Hardware Design and Implementation of Advanced Encryption Standard (AES) AlgorithmmianNessuna valutazione finora
- Engineering Journal Implementation of AES AlgorithmDocumento5 pagineEngineering Journal Implementation of AES AlgorithmEngineering JournalNessuna valutazione finora
- Reference of LFSR AesDocumento21 pagineReference of LFSR AesK.KALAISELVI HICET STAFF ECENessuna valutazione finora
- VLSI Implementation of Advanced Encryption Standard Using Rijndael AlgorithmDocumento6 pagineVLSI Implementation of Advanced Encryption Standard Using Rijndael AlgorithmInternational Journal of Application or Innovation in Engineering & ManagementNessuna valutazione finora
- Optimal Power Calculation For The Cryptography Aes Algorithm Using Clock Gating TechniqueDocumento5 pagineOptimal Power Calculation For The Cryptography Aes Algorithm Using Clock Gating TechniqueIjesat JournalNessuna valutazione finora
- Implement Are SErpent PR FPGAJaroslawDocumento6 pagineImplement Are SErpent PR FPGAJaroslawghionoiucNessuna valutazione finora
- Factoring Large Numbers With The TWIRL DeviceDocumento26 pagineFactoring Large Numbers With The TWIRL DeviceCARLOSWAR101Nessuna valutazione finora
- Optimization of Advanced Encryption Standard (AES) Using Vivado High Level Synthesis (HLS)Documento9 pagineOptimization of Advanced Encryption Standard (AES) Using Vivado High Level Synthesis (HLS)Anand Parakkat ParambilNessuna valutazione finora
- Rate MatchingDocumento5 pagineRate MatchingvgguhaNessuna valutazione finora
- Flexible DSP Accelerator Architecture Exploiting Carry-Save ArithmeticDocumento5 pagineFlexible DSP Accelerator Architecture Exploiting Carry-Save ArithmeticSrinivas VuppanapalliNessuna valutazione finora
- Aes 256 FpgaDocumento4 pagineAes 256 FpgaabhishekNessuna valutazione finora
- AES Encryption Algorithm Hardware Implementation Architecture: Resource and Execution Time OptimizationDocumento9 pagineAES Encryption Algorithm Hardware Implementation Architecture: Resource and Execution Time OptimizationInternational Journal of Information and Network Security (IJINS)Nessuna valutazione finora
- 04721627Documento5 pagine04721627sunilsmcsNessuna valutazione finora
- Aes 512Documento6 pagineAes 512Rares PNessuna valutazione finora
- An Embedded Merging Scheme For H.264/Avc Motion Estimation: Chztun-Yu Cho, Shiung-Yang Huung Andjiu-Shung WangDocumento4 pagineAn Embedded Merging Scheme For H.264/Avc Motion Estimation: Chztun-Yu Cho, Shiung-Yang Huung Andjiu-Shung WangDam Minh TungNessuna valutazione finora
- TimGood AESonFPGADocumento14 pagineTimGood AESonFPGAMihai Alexandru OlaruNessuna valutazione finora
- SOC Implementation Wave-Pipelined: VenkataramaniDocumento8 pagineSOC Implementation Wave-Pipelined: VenkataramaniRamesh PrasadNessuna valutazione finora
- Design and Implementation of Real Time Aes-128 On Real Time Operating System For Multiple Fpga CommunicationDocumento6 pagineDesign and Implementation of Real Time Aes-128 On Real Time Operating System For Multiple Fpga Communicationmussadaqhussain8210Nessuna valutazione finora
- CN Lab Manual VTUDocumento68 pagineCN Lab Manual VTUSamarth YadavNessuna valutazione finora
- AES512-Bit Advanced Encryption Standard Algorithm Design and EvaluationDocumento6 pagineAES512-Bit Advanced Encryption Standard Algorithm Design and Evaluationmeghana etteNessuna valutazione finora
- Design and Implementation A Different Architectures of Mixcolumn in FPGADocumento12 pagineDesign and Implementation A Different Architectures of Mixcolumn in FPGAAnand Parakkat ParambilNessuna valutazione finora
- Arm Recognition Encryption by Using Aes AlgorithmDocumento5 pagineArm Recognition Encryption by Using Aes AlgorithmInternational Journal of Research in Engineering and TechnologyNessuna valutazione finora
- AES ConclusionDocumento1 paginaAES Conclusionmdwalunjkar3095Nessuna valutazione finora
- Scalable Elliptic Curve Cryptosystem FPGA Processor For NIST Prime CurvesDocumento4 pagineScalable Elliptic Curve Cryptosystem FPGA Processor For NIST Prime CurvesjanepriceNessuna valutazione finora
- Feasibility Presentation PPT Format (1) (Read-Only)Documento17 pagineFeasibility Presentation PPT Format (1) (Read-Only)Sudeepti D NandaNessuna valutazione finora
- Optimization of Noc Wrapper Design Under Bandwidth and Test Time ConstraintsDocumento6 pagineOptimization of Noc Wrapper Design Under Bandwidth and Test Time ConstraintsMarwan AhmedNessuna valutazione finora
- 603 PaperDocumento6 pagine603 PaperMaarij RaheemNessuna valutazione finora
- Constructing Symmetric Ciphers Using The CAST Design ProcedureDocumento34 pagineConstructing Symmetric Ciphers Using The CAST Design ProcedureHouda AbouzidNessuna valutazione finora
- Low Power and Delay Efficient 32 - Bit Hybrid Carry Skip Adder Implementation Using HDLDocumento4 pagineLow Power and Delay Efficient 32 - Bit Hybrid Carry Skip Adder Implementation Using HDLRahul SharmaNessuna valutazione finora
- FPGA Implementation of AES Encryption and DecryptionDocumento16 pagineFPGA Implementation of AES Encryption and DecryptionSatya NarayanaNessuna valutazione finora
- Pci E 3 - 0 J R: Xpress Itter EquirementsDocumento24 paginePci E 3 - 0 J R: Xpress Itter EquirementsasddasasddasNessuna valutazione finora
- E3.07 DSP 2000Documento20 pagineE3.07 DSP 2000Mustafamna Al SalamNessuna valutazione finora
- 2 Mark and 16 Mark II YearDocumento130 pagine2 Mark and 16 Mark II YearMustafamna Al SalamNessuna valutazione finora
- Advanced Digital Signal Processing Lecture 1Documento42 pagineAdvanced Digital Signal Processing Lecture 1Mustafamna Al Salam0% (1)
- Digital Signal Processing 2001: U Z U A AzDocumento16 pagineDigital Signal Processing 2001: U Z U A AzMustafamna Al SalamNessuna valutazione finora
- 6419 Mt1r13feb 14Documento58 pagine6419 Mt1r13feb 14Mustafamna Al SalamNessuna valutazione finora
- Compressed Sensing in Wireless Sensor Networks: Survey: January 2011Documento5 pagineCompressed Sensing in Wireless Sensor Networks: Survey: January 2011Mustafamna Al SalamNessuna valutazione finora
- Wireless Sensor Networks and The Internet Things: Selected ChallengesDocumento3 pagineWireless Sensor Networks and The Internet Things: Selected ChallengesMustafamna Al SalamNessuna valutazione finora
- Hardware Implementation of Aes-Ccm For Robust Secure Wireless NetworkDocumento8 pagineHardware Implementation of Aes-Ccm For Robust Secure Wireless NetworkMustafamna Al SalamNessuna valutazione finora
- Wireless Sensor Network Simulators A Survey and ComparisonsDocumento18 pagineWireless Sensor Network Simulators A Survey and ComparisonsMustafamna Al SalamNessuna valutazione finora
- A Target Localization Algorithm For Wireless Sensor Network Based On Compressed SensingDocumento11 pagineA Target Localization Algorithm For Wireless Sensor Network Based On Compressed SensingMustafamna Al SalamNessuna valutazione finora
- Virtual Reality's Technologies Use in E-Learning: December 2009Documento7 pagineVirtual Reality's Technologies Use in E-Learning: December 2009Mustafamna Al SalamNessuna valutazione finora
- SCMC: An Efficient Scheme For Minimizing Energy in Wsns Using A Set Cover ApproachDocumento18 pagineSCMC: An Efficient Scheme For Minimizing Energy in Wsns Using A Set Cover ApproachMustafamna Al SalamNessuna valutazione finora
- Designing An Effective E-Learning ExperienceDocumento116 pagineDesigning An Effective E-Learning ExperienceMustafamna Al SalamNessuna valutazione finora
- A Barrier Framework For Open E-Learning in Public AdministrationsDocumento3 pagineA Barrier Framework For Open E-Learning in Public AdministrationsMustafamna Al SalamNessuna valutazione finora
- Abstract - The Choice of A Platform, Software, ASIC Or: Ntroduction Algorithm Analysis and ImplementationDocumento4 pagineAbstract - The Choice of A Platform, Software, ASIC Or: Ntroduction Algorithm Analysis and ImplementationMustafamna Al SalamNessuna valutazione finora
- Design of AES Algorithm Using FPGA: International Conference On Advanced Computing, Communication and Networks'11Documento6 pagineDesign of AES Algorithm Using FPGA: International Conference On Advanced Computing, Communication and Networks'11Mustafamna Al SalamNessuna valutazione finora
- Dependability Assessment of Operating Systems in Multi-Core ArchitecturesDocumento2 pagineDependability Assessment of Operating Systems in Multi-Core ArchitecturesMustafamna Al SalamNessuna valutazione finora
- Architectures, Design Methodologies, and Service Composition Techniques For Grid Job and Resource ManagementDocumento40 pagineArchitectures, Design Methodologies, and Service Composition Techniques For Grid Job and Resource ManagementMustafamna Al SalamNessuna valutazione finora
- Fault-Injection and Dependability Benchmarking For Grid Computing MiddlewareDocumento10 pagineFault-Injection and Dependability Benchmarking For Grid Computing MiddlewareMustafamna Al SalamNessuna valutazione finora
- Fault Injection Testing Method of Software Implemented Fault Tolerance Mechanisms of Web Service SystemsDocumento163 pagineFault Injection Testing Method of Software Implemented Fault Tolerance Mechanisms of Web Service SystemsMustafamna Al SalamNessuna valutazione finora
- Digital Codes: Binary-to-Gray Code Conversion: Conversion Between Binary Code and Gray Code IsDocumento6 pagineDigital Codes: Binary-to-Gray Code Conversion: Conversion Between Binary Code and Gray Code IsMustafamna Al SalamNessuna valutazione finora
- Introduction To Machine LearningDocumento46 pagineIntroduction To Machine LearningMustafamna Al Salam100% (1)
- An Overview of Existing Tools For Fault-Injection and Dependability Benchmarking in GridsDocumento15 pagineAn Overview of Existing Tools For Fault-Injection and Dependability Benchmarking in GridsMustafamna Al SalamNessuna valutazione finora
- Dependency Analysis in Distributed Systems Using Fault Injection: Application To Problem Determination in An E-Commerce EnvironmentDocumento14 pagineDependency Analysis in Distributed Systems Using Fault Injection: Application To Problem Determination in An E-Commerce EnvironmentMustafamna Al SalamNessuna valutazione finora
- Easy Fault Injection and Stress Testing With FAIL-FCI: William Hoarau S Ebastien Tixeuil Fabien VauchellesDocumento20 pagineEasy Fault Injection and Stress Testing With FAIL-FCI: William Hoarau S Ebastien Tixeuil Fabien VauchellesMustafamna Al SalamNessuna valutazione finora
- Supervisad By:-: Dr. Hussein KittanDocumento48 pagineSupervisad By:-: Dr. Hussein KittanMustafamna Al SalamNessuna valutazione finora
- A Survey On Fault Injection TechniquesDocumento16 pagineA Survey On Fault Injection TechniquesMustafamna Al SalamNessuna valutazione finora
- Zealsound USB Microphone, Condenser Mic For PC Phone PS4&5 Tablet, WAdapter For Smartphone, MuteEchoGain, For Studio, ComputeDocumento1 paginaZealsound USB Microphone, Condenser Mic For PC Phone PS4&5 Tablet, WAdapter For Smartphone, MuteEchoGain, For Studio, Computelucasd5412Nessuna valutazione finora
- Performance: Internet Access Modem Telephone Line Internet Service Provider Routed Internet Telephone NetworkDocumento8 paginePerformance: Internet Access Modem Telephone Line Internet Service Provider Routed Internet Telephone NetworkRahul SharmaNessuna valutazione finora
- UPS HandbookDocumento355 pagineUPS HandbookAmmar Naseer100% (2)
- Temperature Control Design For The Substrate Holder of A High Vacuum Chamber, To Produce Semiconductor Films2 PDFDocumento7 pagineTemperature Control Design For The Substrate Holder of A High Vacuum Chamber, To Produce Semiconductor Films2 PDFcalchavNessuna valutazione finora
- Lenovo Ideapad V110-15AST - LV114A (15270-1 08A03)Documento64 pagineLenovo Ideapad V110-15AST - LV114A (15270-1 08A03)Mahmut KaralarNessuna valutazione finora
- Max Value Shove and CallDocumento613 pagineMax Value Shove and CallDragoș DragomirNessuna valutazione finora
- Quick ChargeDocumento6 pagineQuick ChargeUpendraJavaNessuna valutazione finora
- 3 Embedded Systems - Raj KamalDocumento37 pagine3 Embedded Systems - Raj KamalAshokkumar ManickamNessuna valutazione finora
- Zoom A3 Manual 475877 PDFDocumento44 pagineZoom A3 Manual 475877 PDFNPUIUNessuna valutazione finora
- 136CT052019Documento2 pagine136CT052019Murali BuchammagariNessuna valutazione finora
- 9 - SINCRO - 7a - EN - WIRING DIAGRAMSDocumento17 pagine9 - SINCRO - 7a - EN - WIRING DIAGRAMSBoldsaikhan Tavkhai100% (1)
- Corocam 6Hd: High Performance Daylight Corona Imaging CameraDocumento5 pagineCorocam 6Hd: High Performance Daylight Corona Imaging CamerajimNessuna valutazione finora
- 04 427Documento2 pagine04 427Eng-Mohammed Salem100% (1)
- Unit-II: Hardware and Software RequirementsDocumento10 pagineUnit-II: Hardware and Software RequirementsNavi KaurNessuna valutazione finora
- Roubik Gregorian-Introduction To CMOS OP-AMPs and Comparators-Wiley (1999)Documento369 pagineRoubik Gregorian-Introduction To CMOS OP-AMPs and Comparators-Wiley (1999)Maanas Khurana50% (2)
- Sim5360 Atc en v0.19Documento612 pagineSim5360 Atc en v0.19Thanks MarisaNessuna valutazione finora
- SeminarDocumento13 pagineSeminar17K41A0 440Nessuna valutazione finora
- Polysonics DCT7088 Flow Meter UltrasonicDocumento4 paginePolysonics DCT7088 Flow Meter UltrasonicAris SetyawanNessuna valutazione finora
- LTE TDD Basic Technology and Comparison With LTE FDD: LTE Product Import Team Wireless Product Service DeptDocumento42 pagineLTE TDD Basic Technology and Comparison With LTE FDD: LTE Product Import Team Wireless Product Service Deptmohamed fadl100% (1)
- Harness KenworthDocumento17 pagineHarness KenworthNembot AmedeNessuna valutazione finora
- LG 32lc7d 32lc55 32lc56 Chassis Ld73aDocumento44 pagineLG 32lc7d 32lc55 32lc56 Chassis Ld73awillorikerNessuna valutazione finora
- Saso 53 Graphical Symbols For Electrical Installation CircuitsDocumento23 pagineSaso 53 Graphical Symbols For Electrical Installation CircuitsMohamed AbdinNessuna valutazione finora
- Arduino Load Cell Scale PDFDocumento10 pagineArduino Load Cell Scale PDFduvanNessuna valutazione finora
- Recent Advances On Hybrid Integration of 2D Materials On Integrated Optics PlatformsDocumento24 pagineRecent Advances On Hybrid Integration of 2D Materials On Integrated Optics PlatformsArka GhoshNessuna valutazione finora
- Model 2400 Sourcemeter Model 2400 Sourcemeter: Service Manual Service ManualDocumento137 pagineModel 2400 Sourcemeter Model 2400 Sourcemeter: Service Manual Service ManualMinh CôngNessuna valutazione finora
- DX DiagDocumento45 pagineDX DiagAlex DragneNessuna valutazione finora
- MVH295BT Instruction ManualDocumento60 pagineMVH295BT Instruction ManualLeonardo San Andrés100% (1)
- Presentation 1Documento12 paginePresentation 1nitish dasNessuna valutazione finora
- Dit University Laboratory Manual Practical Instruction SheetDocumento4 pagineDit University Laboratory Manual Practical Instruction SheetDev Narayan UniyalNessuna valutazione finora
- Testing and Commissioning For Fire Alarm SystemDocumento2 pagineTesting and Commissioning For Fire Alarm SystemDong VanraNessuna valutazione finora