Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Public-Key Cryptography: Data and Network Security 1
Caricato da
asad0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
24 visualizzazioni15 pagineTitolo originale
7. cryptography-3
Copyright
© © All Rights Reserved
Formati disponibili
PDF, TXT o leggi online da Scribd
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
© All Rights Reserved
Formati disponibili
Scarica in formato PDF, TXT o leggi online su Scribd
0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
24 visualizzazioni15 paginePublic-Key Cryptography: Data and Network Security 1
Caricato da
asadCopyright:
© All Rights Reserved
Formati disponibili
Scarica in formato PDF, TXT o leggi online su Scribd
Sei sulla pagina 1di 15
Public-Key Cryptography
Data and Network Security 1
Public-Key Cryptography
Principles
• Based on mathematical functions
• The use of two keys has consequences in: key
distribution, confidentiality and authentication.
• Miscoceptions
• The scheme has six ingredients
– Plaintext
– Encryption algorithm
– Public and private key
– Ciphertext
– Decryption algorithm
Data and Network Security 2
Public-Key, essntial steps
1. Each user generates a pair of keys to be used for the
encryption and decryption of messages.
2. Each user places one of the two keys in a public
register or other accessible file. This is the public key.
The companion key is kept private. Each user maintains
a collection of public keys obtained from others.
3. If Bob wishes to send a private message to Alice, Bob
encrypts the message using Alice’s public key.
4. When Alice receives the message, she decrypts it using
her private key. No other recipient can decrypt the
message because only Alice knows Alice’s private key.
Data and Network Security 3
Public-Key
• With this approach, all participants have access to
public keys, and private keys are generated locally by
each participant and therefore need never be
distributed.
• As long as a user protects his or her private key,
incoming communication is secure.
• At any time, a user can change the private key and
publish the companion public key to replace the old
public key.
Data and Network Security 4
Encryption using Public-Key
system
Data and Network Security 5
Authentication using Public-
Key System
Data and Network Security 6
Applications for Public-Key
Cryptosystems
• Three categories:
– Encryption/decryption: The sender
encrypts a message with the recipient’s
public key.
– Digital signature: The sender ”signs” a
message with its private key.
– Key echange: Two sides cooperate two
exhange a session key.
Data and Network Security 7
Requirements for Public-
Key Cryptography
1. Computationally easy for a party B
to generate a pair (public key KUb,
private key KRb)
2. Easy for sender to generate
ciphertext: C EKUb (M )
3. Easy for the receiver to decrypt
ciphertect using private key:
M DKRb (C ) DKRb [ EKUb (M )]
Data and Network Security 8
Requirements for Public-
Key Cryptography
4. Computationally infeasible to determine
private key (KRb) knowing public key (KUb)
5. Computationally infeasible to recover
message M, knowing KUb and ciphertext C
6. Either of the two keys can be used for
encryption, with the other used for
decryption:
M DKRb [ EKUb (M )] DKUb[ EKRb (M )]
Data and Network Security 9
Public-Key Cryptographic
Algorithms
• RSA and Diffie-Hellman
• RSA - Ron Rives, Adi Shamir and Len
Adleman at MIT, in 1977.
– RSA is a block cipher
– The most widely implemented
• Diffie-Hellman
– Echange a secret key securely
– Compute discrete logarithms
Data and Network Security 10
The RSA Algorithm –
Key Generation
1. Select p,q p and q both prime
2. Calculate n = p x q
3. Calculate (n) ( p 1)(q 1)
4. Select integer e gcd( (n), e) 1; 1 e (n)
5. Calculate d d de mod (n)
6. Public Key KU = {e,n}
7. Private key KR = {d,n}
Data and Network Security 11
The RSA Algorithm -
Encryption
• Plaintext: M<n
• Ciphertext: C = Me (mod n)
Data and Network Security 12
The RSA Algorithm -
Decryption
• Ciphertext: C
• Plaintext: M = Cd (mod n)
Data and Network Security 13
Example of RSA Algorithm
Data and Network Security 14
Other Public-Key
Cryptographic Algorithms
• Digital Signature Standard (DSS)
– Makes use of the SHA-1
– Not for encryption or key echange
• Elliptic-Curve Cryptography (ECC)
– Good for smaller bit size
– Low confidence level, compared with RSA
– Very complex
Data and Network Security 15
Potrebbero piacerti anche
- Application and Implementation of DES Algorithm Based on FPGADa EverandApplication and Implementation of DES Algorithm Based on FPGANessuna valutazione finora
- Lecture 7: Modules 7.1-7.10 Network Security CSE 628/628A: Sandeep K. Shukla Indian Institute of Technology KanpurDocumento17 pagineLecture 7: Modules 7.1-7.10 Network Security CSE 628/628A: Sandeep K. Shukla Indian Institute of Technology KanpurHarpreet SinghNessuna valutazione finora
- New Frontiers in Cryptography: Quantum, Blockchain, Lightweight, Chaotic and DNADa EverandNew Frontiers in Cryptography: Quantum, Blockchain, Lightweight, Chaotic and DNANessuna valutazione finora
- Unit 3 Part ADocumento63 pagineUnit 3 Part Ateja mNessuna valutazione finora
- Public-Key EncryptionDocumento14 paginePublic-Key EncryptionteytytyuNessuna valutazione finora
- SecurityDocumento29 pagineSecurityMano KaliNessuna valutazione finora
- Lecture 9 - Week 9Documento40 pagineLecture 9 - Week 9Vishwa MoorthyNessuna valutazione finora
- Chapter 4Documento84 pagineChapter 4Ahmed MohammedNessuna valutazione finora
- Ch09+-+Public Key Cryptography and RSADocumento49 pagineCh09+-+Public Key Cryptography and RSASawsan TawfiqNessuna valutazione finora
- RSA Public Key Encryption AlgorithmDocumento77 pagineRSA Public Key Encryption AlgorithmPaksmilerNessuna valutazione finora
- The Golden Bough, Sir James George FrazerDocumento18 pagineThe Golden Bough, Sir James George Frazerjagmohan bishtNessuna valutazione finora
- CNS - M3 - Asymmetric, RSADocumento32 pagineCNS - M3 - Asymmetric, RSA65nsvgkzgdNessuna valutazione finora
- Unit 3Documento34 pagineUnit 3Mahesh ThallapelliNessuna valutazione finora
- 2.chapter - 9 - Public Key Cryptography and RSADocumento40 pagine2.chapter - 9 - Public Key Cryptography and RSAtt hhNessuna valutazione finora
- Public Key CryptographyDocumento21 paginePublic Key CryptographyAatmaj SalunkeNessuna valutazione finora
- UE20CS314 Unit3 SlidesDocumento238 pagineUE20CS314 Unit3 SlidesKoushiNessuna valutazione finora
- S10 Cryptography DetailedDocumento15 pagineS10 Cryptography DetailedVivek SinghNessuna valutazione finora
- Chapter 3 Public Key Crypto Digital Sign and CertDocumento78 pagineChapter 3 Public Key Crypto Digital Sign and CertNurlign YitbarekNessuna valutazione finora
- Conventional Encryption Message Confidentiality: Data and Network SecurityDocumento22 pagineConventional Encryption Message Confidentiality: Data and Network SecurityasadNessuna valutazione finora
- Public-Key Cryptography and RSADocumento25 paginePublic-Key Cryptography and RSASumaiya TasnimNessuna valutazione finora
- 07 Overview of Cryptography: SE 4C03 Winter 2003Documento22 pagine07 Overview of Cryptography: SE 4C03 Winter 2003JamesKJaakNessuna valutazione finora
- Public Key Cryptography and RSADocumento37 paginePublic Key Cryptography and RSAMulungi CephasNessuna valutazione finora
- EMTM 553: E-Commerce Systems: Lecture 6: Basic CryptographyDocumento60 pagineEMTM 553: E-Commerce Systems: Lecture 6: Basic CryptographySiya RathoreNessuna valutazione finora
- Week 6 - Cryptography - RSADocumento36 pagineWeek 6 - Cryptography - RSATahir BashirNessuna valutazione finora
- Chapter 3 Public Key Crypto Digital Sign and CertDocumento47 pagineChapter 3 Public Key Crypto Digital Sign and CertBeka BekoNessuna valutazione finora
- Modified RSA Public Key Cryptosystem Using Two Key PairsDocumento3 pagineModified RSA Public Key Cryptosystem Using Two Key PairsJainul AbudinNessuna valutazione finora
- Chapter 5 (Secure Messaging) - 1Documento44 pagineChapter 5 (Secure Messaging) - 1jahirkhan.ice.nstuNessuna valutazione finora
- CS#3 - 3Documento30 pagineCS#3 - 3faiza abdellaNessuna valutazione finora
- RSA Public Key CryptoDocumento12 pagineRSA Public Key CryptoHarpreet SinghNessuna valutazione finora
- Public-Key Cryptography and Message AuthenticationDocumento20 paginePublic-Key Cryptography and Message AuthenticationRajinder KaurNessuna valutazione finora
- Lecture2 PDFDocumento64 pagineLecture2 PDFVijayalakshmi JNessuna valutazione finora
- Unit 4 Note For IV CseDocumento17 pagineUnit 4 Note For IV CsetnagaviNessuna valutazione finora
- Chapter 9 RSADocumento25 pagineChapter 9 RSASOUMY PRAJAPATINessuna valutazione finora
- Network Security Concepts and MechanismsDocumento57 pagineNetwork Security Concepts and MechanismsGetaneh MeleseNessuna valutazione finora
- Crypto 1Documento19 pagineCrypto 1Saurabh SweetNessuna valutazione finora
- Security of C.N.: By: Eng. Ahmed K. DarajDocumento8 pagineSecurity of C.N.: By: Eng. Ahmed K. DarajAHMED DARAJNessuna valutazione finora
- Lec 7 - RSADocumento41 pagineLec 7 - RSAMoOez InamNessuna valutazione finora
- SWE 681 / ISA 681 Secure Software Design & Programming: Lecture 7: CryptographyDocumento90 pagineSWE 681 / ISA 681 Secure Software Design & Programming: Lecture 7: CryptographyAayushKumarNessuna valutazione finora
- InfoSec Lect 7Documento35 pagineInfoSec Lect 7Taha AhmedNessuna valutazione finora
- 13 EncryptionDocumento15 pagine13 EncryptionArunNessuna valutazione finora
- Cryptography and Network Security: Sixth Edition by William StallingsDocumento40 pagineCryptography and Network Security: Sixth Edition by William Stallingsاحمد ميسر فتحي كموشNessuna valutazione finora
- Ch09 Public-Key CryptosystemsDocumento20 pagineCh09 Public-Key CryptosystemsShashi SinghNessuna valutazione finora
- Public Key Cryptography and RSADocumento24 paginePublic Key Cryptography and RSAashwinikapse134891Nessuna valutazione finora
- S 4 - Cryptography and Encryption AlgorithmsDocumento28 pagineS 4 - Cryptography and Encryption AlgorithmsPPNessuna valutazione finora
- Fluency With Information Technology: Lawrence SnyderDocumento15 pagineFluency With Information Technology: Lawrence SnyderProf. Sudesh R. AgrawalNessuna valutazione finora
- Public Key Cryptography - Chapter 9Documento109 paginePublic Key Cryptography - Chapter 9sonyNessuna valutazione finora
- RSADocumento25 pagineRSARajesh KumarNessuna valutazione finora
- Cryptography and Network Security: Third Edition by William StallingsDocumento58 pagineCryptography and Network Security: Third Edition by William StallingsabyNessuna valutazione finora
- Sessions 15, 16Documento24 pagineSessions 15, 16Lõkèßh DåçhëpällìNessuna valutazione finora
- Chapter 9Documento19 pagineChapter 9Sibghat RehmanNessuna valutazione finora
- 12822.public Key CryptographyDocumento25 pagine12822.public Key CryptographySiddharthRawatNessuna valutazione finora
- Chapter 9 - Public Key Cryptography and RSADocumento21 pagineChapter 9 - Public Key Cryptography and RSArishabhdubeyNessuna valutazione finora
- CH 9Documento27 pagineCH 9thejaschandraNessuna valutazione finora
- Lecture BCA387&BCO327 18&19 Auth PKCDocumento26 pagineLecture BCA387&BCO327 18&19 Auth PKCwebsite3loginNessuna valutazione finora
- Introduction Graphic in PCDocumento43 pagineIntroduction Graphic in PChahajsNessuna valutazione finora
- Chapter 3 Public Key Crypto Digital Sign and CertDocumento82 pagineChapter 3 Public Key Crypto Digital Sign and Certcarraa DestaNessuna valutazione finora
- 9.public Key Cryptography and RSADocumento33 pagine9.public Key Cryptography and RSAemmanuelauko4Nessuna valutazione finora
- cns3 1Documento9 paginecns3 1gadidheerajreddy.20.itNessuna valutazione finora
- Public Key CryptographyDocumento16 paginePublic Key Cryptographymanoranjan harshNessuna valutazione finora
- Lecture - Network Security Techniques IIDocumento33 pagineLecture - Network Security Techniques IIAbdul ShirazNessuna valutazione finora
- Most Common Weaknesses in A Company: Data and Network Security 1Documento12 pagineMost Common Weaknesses in A Company: Data and Network Security 1asadNessuna valutazione finora
- Conventional Encryption Message Confidentiality: Data and Network SecurityDocumento22 pagineConventional Encryption Message Confidentiality: Data and Network SecurityasadNessuna valutazione finora
- Message Authentication Code: M. Abidoon QadirDocumento12 pagineMessage Authentication Code: M. Abidoon QadirasadNessuna valutazione finora
- Electronic Mail Security: Data and Network SecurityDocumento26 pagineElectronic Mail Security: Data and Network SecurityasadNessuna valutazione finora
- WEB Security: Data and Networks SecurityDocumento21 pagineWEB Security: Data and Networks SecurityasadNessuna valutazione finora
- IP Security: Data and Network Security 1Documento31 pagineIP Security: Data and Network Security 1asadNessuna valutazione finora
- Viruses and "Malicious Programs": Data and Network Security 1Documento11 pagineViruses and "Malicious Programs": Data and Network Security 1asadNessuna valutazione finora
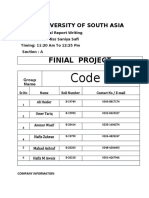
- Code X: Finial ProjectDocumento3 pagineCode X: Finial ProjectasadNessuna valutazione finora
- Police Station Management System: Project TitleDocumento53 paginePolice Station Management System: Project TitleasadNessuna valutazione finora
- Authentication Applications: Data and Network SecurityDocumento19 pagineAuthentication Applications: Data and Network SecurityasadNessuna valutazione finora
- University of South Asia: Tufail Road, Lahore, PakistanDocumento2 pagineUniversity of South Asia: Tufail Road, Lahore, PakistanasadNessuna valutazione finora
- Code X: Research EssayDocumento8 pagineCode X: Research EssayasadNessuna valutazione finora
- Distributed Systems: Department of Computer SciencesDocumento6 pagineDistributed Systems: Department of Computer SciencesasadNessuna valutazione finora
- CEHDocumento5 pagineCEHanil0% (1)
- Audit Security ChecklistDocumento4 pagineAudit Security ChecklistPeter George100% (1)
- 9 Best Next-Gen Firewalls For 2022Documento24 pagine9 Best Next-Gen Firewalls For 2022Hafa kaliNessuna valutazione finora
- Social Studies Techbook LoginDocumento1 paginaSocial Studies Techbook Loginapi-269909040Nessuna valutazione finora
- Cryptography and Network SecurityDocumento11 pagineCryptography and Network SecurityNil MaghNessuna valutazione finora
- CHAMPIONS TEAM BASE - GRASE - Batch - 1-2-3-4-5-6 - DetailsDocumento32 pagineCHAMPIONS TEAM BASE - GRASE - Batch - 1-2-3-4-5-6 - DetailsAgbeme WisdomNessuna valutazione finora
- Sorted - Rf-Website-4xx-Logs-11-09-21-13-09-21 2Documento44 pagineSorted - Rf-Website-4xx-Logs-11-09-21-13-09-21 2Arpit AwasthiNessuna valutazione finora
- Install Log SyslogDocumento6 pagineInstall Log SyslogJorge Jaramillo SanchezNessuna valutazione finora
- Is It Wrong To Try To Find APT Techniques in Ransomware Attack?Documento55 pagineIs It Wrong To Try To Find APT Techniques in Ransomware Attack?juanNessuna valutazione finora
- CS1014 Information Security QBDocumento3 pagineCS1014 Information Security QBVinodh KumarNessuna valutazione finora
- Username 9807654321Documento7 pagineUsername 9807654321drag1313dragNessuna valutazione finora
- Soal 1Documento3 pagineSoal 1Afif ZuhriNessuna valutazione finora
- Malware: CC101 - Introduction To ComputingDocumento11 pagineMalware: CC101 - Introduction To ComputingMelx UbaldeNessuna valutazione finora
- CYBER DEFENSE SYSTEM WilliamDocumento6 pagineCYBER DEFENSE SYSTEM WilliamCI WongNessuna valutazione finora
- Computer Security BasicsDocumento2 pagineComputer Security BasicsthienbinhduongNessuna valutazione finora
- Detailed Lesson Plan in ICTDocumento6 pagineDetailed Lesson Plan in ICTKathleen BorjaNessuna valutazione finora
- Final SowmyaDocumento15 pagineFinal SowmyasanthipradeepNessuna valutazione finora
- Free Proxy List - Just Checked Proxy ListDocumento4 pagineFree Proxy List - Just Checked Proxy ListHarish KumarNessuna valutazione finora
- Ciber SecurityDocumento24 pagineCiber SecurityRafaella KalilNessuna valutazione finora
- Common ColumnsDocumento44 pagineCommon ColumnsmeNessuna valutazione finora
- Cyber SecurityDocumento4 pagineCyber SecurityANessuna valutazione finora
- HITRUST CSF Authoritative Sources Cross-Reference v9.3.1Documento199 pagineHITRUST CSF Authoritative Sources Cross-Reference v9.3.1jayantchutkeNessuna valutazione finora
- Chapter 1 - 1: Prof. Joseph Wilfred Dela CruzDocumento9 pagineChapter 1 - 1: Prof. Joseph Wilfred Dela CruzKATHLENE CORPUSNessuna valutazione finora
- Live WireDocumento2 pagineLive Wireharshada kavdeNessuna valutazione finora
- Network Security and CryptographyDocumento17 pagineNetwork Security and Cryptographytharun0% (1)
- Unit 3 Nis 22620Documento6 pagineUnit 3 Nis 22620Komal JadhavNessuna valutazione finora
- Cyber Security Threats On The Internet and Possible SolutionsDocumento6 pagineCyber Security Threats On The Internet and Possible SolutionsAnita KatariaNessuna valutazione finora
- Hindu Institute of Management: Aruna KapoorDocumento10 pagineHindu Institute of Management: Aruna KapoorAruna KapoorNessuna valutazione finora
- Cybersecurity RoadmapDocumento1 paginaCybersecurity RoadmapislamelshahatNessuna valutazione finora
- SQL Server 2000 SecurityDocumento3 pagineSQL Server 2000 SecurityBirhanu AtnafuNessuna valutazione finora