Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Progr Pic16 PDF
Caricato da
curzTitolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Progr Pic16 PDF
Caricato da
curzCopyright:
Formati disponibili
PIC12F609/12F615/12F617/16F610/16F616 AND
PIC12HV609/12HV615/16HV610/16HV616
Flash Memory Programming Specification
1.0 DEVICE OVERVIEW 2.1 Hardware Requirements
This document includes the programming These devices require one power supply for VDD, see
specifications for the following devices: Table 7-1 VDD, and one for VPP, see Table 7-1 VIHH.
2.2 Program/Verify Mode
• PIC12F615 • PIC12HV615
The Program/Verify mode for these devices allows pro-
• PIC12F609 • PIC12HV609 gramming of user program memory, user ID locations,
• PIC12F617 • PIC16HV616 Calibration Word and the Configuration Word.
• PIC16F616 • PIC16HV610
• PIC16F610
Note 1: All references to the PIC12F615 parts
refer to the PIC12HV615 parts as well
(unless otherwise specified).
2: All references to the PIC16F616 parts
refer to the PIC16HV616 as well (unless
otherwise specified).
3: All references to the PIC12F609 parts
refer to the PIC12HV609 as well (unless
otherwise specified).
4: All references to the PIC16F610 parts
refer to the PIC16HV610 as well (unless
otherwise specified).
5: Any references in this programming
specification to PORTA and RAn refer to
GPIO and GPn, respectively.
2.0 PROGRAMMING THE
PIC12F609/12F615/12F617/
16F610/16F616 AND
PIC12HV609/12HV615/16HV610/
16HV616 DEVICES
The PIC12F609/12F615/12F617/16F610/16F616 and
PIC12HV609/12HV615/16HV610/16HV616 devices are
programmed using a serial method. The Serial mode will
allow these devices to be programmed while in the user’s
system. These programming specifications apply to all of
the above devices in all packages.
2010 Microchip Technology Inc. DS41284E-page 1
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
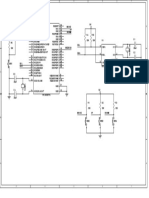
FIGURE 2-1: 8-PIN, 14-PIN, AND 16-PIN PROGRAMMING PINS DIAGRAM FOR PIC12F609/
12F615/12F617/16F610/16F616(1)
8-Pin PDIP, SOIC, MSOP, DFN VDD 1 8 VSS
PIC12F615/609
GP5 2 7 GP0/ICSPDAT
PIC12F617
GP4 3 6 GP1/ICSPCLK
GP3/MCLR/VPP 4 5 GP2
14-Pin PDIP, SOIC, TSSOP
VDD 1 14 VSS
RA5 2 13 RA0/ICSPDAT
PIC16F616/610
RA4 3 12 RA1/ICSPCLK
RA3/MCLR/VPP 4 11 RA2
RC5 5 10 RC0
RC4 6 9 RC1
RC3 7
VDD 8 RC2
VSS
NC
NC
16-Pin QFN
16
6 PIC16F616/HV616 15
14
13
RA5 12 RA0/ICSPDAT
PIC16F610/HV610
1
RA4 2 11 RA1/ICSPCLK
RA3/MCLR/VPP 3 10 RA2
RC5 4 9 RC0
5
8
RC4
RC3
RC2
RC1
Note 1: Please see specific data sheets for alternate pin functionality.
TABLE 2-1: PIN DESCRIPTIONS IN PROGRAM/VERIFY MODE: PIC12F609/12F615/12F617/
16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
During Programming
Pin Name
Function Pin Type Pin Description
GP1/RA1 ICSPCLK I Clock input – Schmitt Trigger input
GP0/RA0 ICSPDAT I/O Data input/output – Schmitt Trigger input
MCLR Program/Verify mode P(1) Program Mode Select
VDD VDD P Power Supply
VSS VSS P Ground
Legend: I = Input, O = Output, P = Power
Note 1: In the PIC12F609/12F615/12F617/16F610/16F616 and PIC12HV609/12HV615/16HV610/16HV616, the
programming high voltage is internally generated. To activate the Program/Verify mode, voltage of VIHH
and a current of IIHH (see Table 7-1) needs to be applied to MCLR input.
DS41284E-page 2 2010 Microchip Technology Inc.
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
3.0 MEMORY DESCRIPTION 3.3 Calibration Word
For all of the devices covered in this document, the
3.1 Program Memory Map 4/8 MHz Internal Oscillator (INTOSC) module is fac-
The user memory space extends from 0x0000 to tory calibrated. This value is stored in the Calibration
0x1FFF. In Program/Verify mode, the program memory Word (0x2008). See the applicable device data sheet
space extends from 0x0000 to 0x3FFF, with the first for more information.
half (0x0000-0x1FFF) being user program memory and The Calibration Word does not necessarily participate
the second half (0x2000-0x3FFF) being configuration in the erase operation unless a specific procedure is
memory. The Program Counter (PC) will increment executed. Therefore, the device can be erased without
from 0x0000 to 0x1FFF and wrap to 0x0000. If the PC affecting the Calibration Word. This simplifies the erase
is between 0x2000 to 0x3FFF it will wrap around to procedure since these values do not need to be read
0x2000 (not to 0x0000). Once in configuration memory, and restored after the device is erased.
the highest bit of the PC stays a ‘1’, thus always point-
ing to the configuration memory. The only way to point
to user program memory is to reset the part and re-
enter Program/Verify mode as described in
Section 4.0 “Program/Verify Mode”.
For all of the devices covered in this document, the
configuration memory space, 0x2000 to 0x2008, is
physically implemented. However, only locations
0x2000 to 0x2003, 0x2007 and 0x2008 are available.
Other locations are reserved.
3.2 User ID Locations
A user may store identification information (user ID) in
four designated locations. The user ID locations are
mapped in 0x2000 to 0x2003. It is recommended that
the user use only the seven Least Significant bits
(LSbs) of each user ID location. The user ID locations
read out normally, even after code protection is
enabled. It is recommended that ID locations are writ-
ten as ‘xx xxxx xbbb bbbb’ where ‘bbb bbbb’ is the
user ID information.
The 14 bits may be programmed, but only the 7 LSbs
are read and displayed by MPLAB® IDE.
2010 Microchip Technology Inc. DS41284E-page 3
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
FIGURE 3-1: PIC12F615/HV615, PIC12F609/HV609, PIC16F610/HV610 PROGRAM MEMORY
MAPPING
1 KW
Implemented
03FF
Program Memory
Maps to
User ID Location 0-3FF
2000
2001 User ID Location
1FFF
2002 User ID Location
2000
Implemented
2003 User ID Location 2040
2004 Reserved
2005 Reserved
Maps to Configuration Memory
Device ID 2000-203F
2006
2007 Configuration Word
2008 Calibration Word
2009-203F Reserved 3FFF
DS41284E-page 4 2010 Microchip Technology Inc.
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
FIGURE 3-2: PIC12F617/PIC16F616/HV616 PROGRAM MEMORY MAPPING
2 KW
Implemented
07FF
Program Memory
Maps to
User ID Location 0-7FF
2000
2001 User ID Location
1FFF
2002 User ID Location
2000
Implemented
2003 User ID Location 2040
2070(1)
2004 Reserved
2005 Reserved
Maps to Configuration Memory
Device ID 2000-203F
2006
2000-206F(1)
2007 Configuration Word
2008 Calibration Word
2009-203F Reserved 3FFF
2009-206F(1)
Note 1: Applies to the PIC12F617 only.
2010 Microchip Technology Inc. DS41284E-page 5
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
4.0 PROGRAM/VERIFY MODE FIGURE 4-2: VDD-FIRST PROGRAM/
VERIFY MODE ENTRY
Two methods are available to enter Program/Verify
mode. “VPP-first” is entered by holding ICSPDAT and THLD0 TPPDP
ICSPCLK low while raising the MCLR pin from VIL to
VIHH (high voltage), then applying VDD and data. This
method can be used for any Configuration Word selec-
tion and must be used if the INTOSC and internal VPP
MCLR options are selected (FOSC<2:0> = 100 or 101
and MCLRE = 0). The VPP-first entry prevents the VDD
device from executing code prior to entering Program/
Verify mode. See the timing diagram in Figure 4-1. ICSPDAT
The second entry method, “VDD-first”, is entered by
applying VDD, holding ICSPDAT and ICSPCLK low, ICSPCLK
then raising MCLR pin from VIL to VIHH (high voltage),
Note: This method of entry is valid if INTOSC
followed by data. This method can be used for any
and internal MCLR are not selected.
Configuration Word selection except when INTOSC
and internal MCLR options are selected (FOSC<2:0> =
100 or 101 and MCLRE = 0). This technique is useful FIGURE 4-3: PROGRAM/VERIFY MODE
when programming the device when VDD is already EXIT
applied, for it is not necessary to disconnect VDD to
enter Program/Verify mode. See the timing diagram in THLD0
Figure 4-2.
VPP
Once in Program/Verify mode, the program memory
and configuration memory can be accessed and
programmed in serial fashion. ICSPDAT and ICSPCLK VDD
are Schmitt Trigger inputs in this mode. RA4 is tri-state
regardless of fuse setting.
The sequence that enters the device into the Program/ ICSPDAT
Verify mode places all other logic into the Reset state
(the MCLR pin was initially at VIL). Therefore, all I/Os ICSPCLK
are in the Reset state (high-impedance inputs) and the
PC is cleared.
To prevent a device configured with INTOSC and 4.1 Program/Erase Algorithms
internal MCLR from executing after exiting Program/
Verify mode, VDD needs to power down before VPP. The PIC16F616/PIC12F617 program memory may be
See Figure 4-3 for the timing. written in two ways. The fastest method writes four
words at a time. However, one-word writes are also
supported for backward compatibility with previous 8-
FIGURE 4-1: VPP-FIRST PROGRAM/
pin and 14-pin Flash devices. The four-word algorithm
VERIFY MODE ENTRY is used to program the program memory only. The one-
TPPDP THLD0 word algorithm can write any available memory
location (i.e., program memory, configuration memory
and calibration memory).
VPP
Note: The PIC12F615, PIC12F609, PIC16F610
program memories must be written in
one-word writes only.
VDD
After writing the array, the PC may be reset and read
ICSPDAT back to verify the write. It is not possible to verify
immediately following the write because the PC can
ICSPCLK only increment, not decrement.
A device Reset will clear the PC and set the address to
Note: This method of entry is valid, regardless
of Configuration Word selected.
‘0’. The Increment Address command will increment
the PC. The Load Configuration command will set the
PC to 0x2000. The available commands are shown in
Table 4-1.
DS41284E-page 6 2010 Microchip Technology Inc.
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
4.1.1 ONE-WORD PROGRAMMING 4.1.2 FOUR-WORD PROGRAMMING
The PIC12F615, PIC12F609, PIC16F616 and The PIC16F616/PIC12F617 program memory can be
PIC16F610 program memories can be written one written four words at a time using the four-word algo-
word at a time to allow compatibility with other 8-pin rithm. Configuration memory (addresses >0x2000) and
and 14-pin Flash PIC® devices. Configuration memory non-aligned (addresses modulo 4 not equal to zero)
(>0x2000) must be written one word (or byte) at a time. starting addresses must use the one-word
The sequences for programming one word of program programming algorithm.
memory at a time is: This algorithm writes four sequential addresses in
1. Load a word at the current program memory program memory. The four addresses must point to a
address using the Load Data For Program four-word block which address modulo 4 of 0, 1, 2 and
Memory command. 3. For example, programming address 4 through 7 can
be programmed together. Programming addresses 2
2. Issue a Begin Programming (externally timed)
through 5 will create an unexpected result.
command.
3. Wait TPROG1. The sequence for programming four words of program
memory at a time is:
4. Issue End Programming command.
5. Issue an Increment Address command. 1. Load a word at the current program memory
address using the Load Data For Program Mem-
6. Repeat this sequence as required to write
ory command. This location must be address
program, calibration or configuration memory.
modulo 4 equal to 0.
See Figure 4-12 for more information. 2. Issue an Increment Address command to point
to the next address in the block.
3. Load a word at the current program memory
address using the Load Data For Program
Memory command.
4. Issue an Increment Address command to point
to the next address in the block.
5. Load a word at the current program memory
address using the Load Data For Programming
Memory command.
6. Issue and Increment Address command to point
to the next address in the book.
7. Load a word at the current program memory
address using the Load Data For Programming
Memory command.
8. Issue a Begin Programming command
externally timed.
9. Wait TPROG1.
10. Issue End Programming.
11. Wait TDIS.
12. Issue an Increment Address command to point
to the start of the next block of addresses.
13. Repeat steps 1 through 12 as required to write
the desired range of program memory.
See Figure 4-12 for more information.
Note: Only the PIC16F616 and PIC12F617 pro-
gram memory can be written to using the
four-word programming algorithm.
2010 Microchip Technology Inc. DS41284E-page 7
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
4.1.3 ERASE ALGORITHMS 4.1.4 SERIAL PROGRAM/VERIFY
The PIC12F609/12F615/12F617/16F610/16F616 and OPERATION
PIC12HV609/12HV615/16HV610/16HV616 devices will The ICSPCLK pin is used as a clock input and the
erase different memory locations depending on the PC ICSPDAT pin is used for entering command bits and
and CP. The following sequences can be used to erase data input/output during serial operation. To input a
noted memory locations. To erase the program memory command, ICSPCLK is cycled six times. Each
and Configuration Word (0x2007), the following sequence command bit is latched on the falling edge of the clock
must be performed. Note the Calibration Word (0x2008) with the LSb of the command being input first. The data
and User ID (0x2000-0x2003) will not be erased. input onto the ICSPDAT pin is required to have a mini-
1. Do a Bulk Erase Program Memory command. mum setup and hold time (see Table 7-1), with respect
to the falling edge of the clock. Commands that have
2. Wait TERA to complete erase.
data associated with them (Read and Load) are
To erase the User ID (0x2000-0x2003), Configuration specified to have a minimum delay of 1 s between the
Word (0x2007) and program memory, use the following command and the data. After this delay, the clock pin is
sequence. Note that the Calibration Word (0x2008) will cycled 16 times with the first cycle being a Start bit and
not be erased. the last cycle being a Stop bit.
1. Perform Load Configuration with dummy data to During a read operation, the LSb will be transmitted
point the PC to 0x2000. onto the ICSPDAT pin on the rising edge of the second
2. Perform a Bulk Erase Program Memory cycle. For a load operation, the LSb will be latched on
command. the falling edge of the second cycle. A minimum 1 s
3. Wait TERA to complete erase. delay is also specified between consecutive
commands, except for the End Programming
command, which requires a 100 s (TDIS).
All commands and data words are transmitted LSb first.
Data is transmitted on the rising edge and latched on
the falling edge of the ICSPCLK. To allow for decoding
of commands and reversal of data pin configuration, a
time separation of at least 1 s (TDLY1) is required
between a command and a data word.
The commands that are available are described in
Table 4-1.
DS41284E-page 8 2010 Microchip Technology Inc.
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
TABLE 4-1: COMMAND MAPPING FOR PIC12F609/12F615/12F617/16F610/16F616 AND
PIC12HV609/12HV615/16HV610/16HV616
Command Mapping (MSb … LSb) Data
Load Configuration x x 0 0 0 0 0, data (14), 0
Load Data for Program Memory x x 0 0 1 0 0, data (14), 0
Read Data from Program Memory x x 0 1 0 0 0, data (14), 0
Increment Address x x 0 1 1 0
Begin Programming x 1 1 0 0 0 Externally Timed
End Programming x 0 1 0 1 0
Bulk Erase Program Memory x x 1 0 0 1 Internally Timed
Row Erase Program Memory x 1 0 0 0 1 Internally Timed
4.1.4.1 Load Configuration
The Load Configuration command is used to access
the Configuration Word (0x2007), User ID (0x2000-
0x2003) and Calibration Word (0x2008). This
command sets the PC to address 0x2000 and loads the
data latches with one word of data.
To access the configuration memory, send the Load
Configuration command. Individual words within the
configuration memory can be accessed by sending
Increment Address commands and using load or read
data for program memory.
After the 6-bit command is input, the ICSPCLK pin is
cycled an additional 16 times for the Start bit, 14 bits of
data and the Stop bit (see Figure 4-4).
After the configuration memory is entered, the only way
to get back to the program memory is to exit the
Program/Verify mode by taking MCLR low (VIL).
FIGURE 4-4: LOAD CONFIGURATION COMMAND
TDLY2
1 2 3 4 5 6 1 2 3 4 5 15 16
ICSPCLK
0 00 0 0 X X strt_bit LSb MSb stp_bit
ICSPDAT
TDLY1 TSET1
THLD1
2010 Microchip Technology Inc. DS41284E-page 9
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
4.1.4.2 Load Data For Program Memory
After receiving this command, the chip will load in a
14-bit “data word” when 16 cycles are applied, as
described in Section 4.1.4.1 “Load Configuration”.
A timing diagram of this command is shown in
Figure 4-5.
FIGURE 4-5: LOAD DATA FOR PROGRAM MEMORY COMMAND
TDLY2
1 2 3 4 5 6 1 2 3 4 5 15 16
ICSPCLK
0 1 0 0 X X strt_bit LSb MSb stp_bit
ICSPDAT
TSET1 TDLY1 TSET1
THLD1 THLD1
4.1.4.3 Read Data From Program Memory
After receiving this command, the chip will transmit
data bits out of the program memory (user or configu-
ration) currently accessed, starting with the second
rising edge of the clock input. The data pin will go into
Output mode on the second rising clock edge, and it
will revert to Input mode (high-impedance) after the
16th rising edge.
If the program memory is code-protected (CP = 0), the
data is read as zeros.
A timing diagram of this command is shown in Figure 4-6.
FIGURE 4-6: READ DATA FROM PROGRAM MEMORY COMMAND
TDLY2
1 2 3 4 5 6 1 2 3 4 5 15 16
ICSPCLK
TDLY3
1 0 0 1 0 X X MSb stp_bit
ICSPDAT strt_bit
LSb
TSET1
THLD1 TDLY1
input output input
DS41284E-page 10 2010 Microchip Technology Inc.
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
4.1.4.4 Increment Address
The PC is incremented when this command is
received. A timing diagram of this command is shown
in Figure 4-7.
It is not possible to decrement the address counter. To
reset this counter, the user should exit and re-enter
Program/Verify mode.
FIGURE 4-7: INCREMENT ADDRESS COMMAND (PROGRAM/VERIFY)
TDLY2
Next Command
1 2 3 4 5 6 1 2
ICSPCLK
0 1 1 0 X X X 0
ICSPDAT
TSET1
THLD1
TDLY1
4.1.4.5 Begin Programming (Externally
Timed)
A Load command must be given before every Begin
Programming command. Programming of the
appropriate memory (program memory, configuration or
calibration memory) will begin after this command is
received and decoded. Programming requires (TPROG)
time and is terminated using an End Programming
command. A timing diagram for this command is shown
in Figure 4-8.
The addressed locations are not erased before
programming.
FIGURE 4-8: BEGIN PROGRAMMING (EXTERNALLY TIMED)
VIHH
MCLR TPROG
End Programming Command
1 2 3 4 5 6 1 2
ICSPCLK
ICSPDAT 0 0 0 1 1 X X 0
TSET1
THLD1
2010 Microchip Technology Inc. DS41284E-page 11
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
4.1.4.6 End Programming
After this command is performed, the write procedure
will stop. A timing diagram of this command is shown in
Figure 4-9.
FIGURE 4-9: END PROGRAMMING (SERIAL PROGRAM/VERIFY)
VIHH
MCLR
Next Command
1 2 3 4 5 6 1 2
ICSPCLK
ICSPDAT 0 1 0 1 0 X X 0
TDIS
TSET1
THLD1
4.1.4.7 Bulk Erase Program Memory
After this command is performed, the entire program
memory and Configuration Word (0x2007) is erased.
The user ID and calibration memory may also be
erased, depending on the value of the PC. See
Section 4.1.3 “Erase Algorithms” for erase
sequences. A timing diagram for this command is
shown in Figure 4-10.
FIGURE 4-10: BULK ERASE PROGRAM MEMORY COMMAND
TERA
Next Command
1 2 3 4 5 6 1 2
ICSPCLK
1 0 0 1 X X X 0
ICSPDAT
TSET1 TSET1
THLD1 THLD1
DS41284E-page 12 2010 Microchip Technology Inc.
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
4.1.4.8 Row Erase Program Memory
This command erases the 16-word row of program
memory pointed to by PC<11:4>. If the program mem-
ory array is protected (CP = 0) or the PC points to the
configuration memory (>0x2000), the command is
ignored.
To perform a Row Erase Program Memory, the
following sequence must be performed.
1. Execute a Row Erase Program Memory
command.
2. Wait TERA to complete a row erase.
FIGURE 4-11: ROW ERASE PROGRAM MEMORY COMMAND
TERA
Next Command
1 2 3 4 5 6 1 2
ICSPCLK
1 0 0 0 1 x x 0
ICSPDAT
2010 Microchip Technology Inc. DS41284E-page 13
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
FIGURE 4-12: ONE-WORD PROGRAMMING FLOWCHART (PIC12F61X/16F61X AND
PIC12F609)
Start
Read and Store
Calibration Memory
Values
(Figure 4-16)
Bulk Erase
Program Program Cycle
Memory(1,2)
Load Data
for
One-word Program Memory
Program Cycle
Begin
Read Data Programming
from Command
Program Memory (Externally timed)
Report
No
Data Correct? Programming
Wait TPROG
Failure
Yes
Increment End
No All Locations
Address Programming
Done?
Command
Yes
Program
User ID/Config. bits Wait TDIS
Read and Verify
Calibration Memory
Values
(Figure 4-16)
Done
Note 1: This step is optional if the device has already been erased or has not been previously programmed.
2: If the device is code-protected or must be completely erased, then Bulk Erase the device per Figure 4-15.
DS41284E-page 14 2010 Microchip Technology Inc.
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
FIGURE 4-13: FOUR-WORD PROGRAMMING FLOWCHART (PIC12F617/PIC16F616)
Program Cycle
Load Data
for
Start Program Memory
Read and Store
Calibration Memory Increment
Values Address
(Figure 4-16) Command
Bulk Erase
Load Data
Program
for
Memory(1), (2)
Program Memory
Four-word Increment
Program Cycle Address
Command
Increment Load Data
No All Locations
Address for
Done?
Command Program Memory
Yes
Increment
Program
Address
User ID/Config. bits
Command
Read and Verify Load Data
Calibration Memory
for
Values
(Figure 4-16) Program Memory
Begin
Done
Programming
Command
(Externally timed)
Wait TPROG
End
Programming
Wait TDIS
Note 1: This step is optional if the device is erased or not previously programmed.
2: If the device is code-protected or must be completely erased, then Bulk Erase the device per Figure 4-15.
2010 Microchip Technology Inc. DS41284E-page 15
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
FIGURE 4-14: PROGRAM FLOWCHART – CONFIGURATION MEMORY
Start
PROGRAM CYCLE
Load
Configuration Load Data
for
Program Memory
One-word
Program Cycle
(User ID) Begin
Programming
Command
Read Data (Externally timed)
From Program
Memory Command
Wait TPROG
No Report
Data Correct? Programming
Failure
End
Yes Programming
Increment
Address
Command
Wait TDIS
Increment
No Address = Yes
Address
0x2004?
Command
Increment
Address
Command
Increment
Address
Command
One-word
Program Cycle
(Config. bits)
Read Data
From Program
Memory Command
Report
No
Data Correct? Programming
Failure
Yes
Done
DS41284E-page 16 2010 Microchip Technology Inc.
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
FIGURE 4-15: PROGRAM FLOWCHART – ERASE FLASH DEVICE
Start
Read and Store
Calibration Memory
Values
(Figure 4-16)
Load Configuration
Bulk Erase(1)
Program Memory
Read and Verify
Calibration Memory
Values
(Figure 4-16)
Done
Note 1: See Section 4.1.4.7 “Bulk Erase Program Memory” for more information on the Bulk Erase procedure.
2010 Microchip Technology Inc. DS41284E-page 17
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
FIGURE 4-16: CALIBRATION WORD VERIFICATION FLOWCHART
Start
Load Configuration
Increment Address
Command
Address = No
0x2008?
Yes
Read and Store
Calibration Word
Calibration No
Word Fail
is Valid?(1,2)
Yes
Done
Note 1: This step is not required for the Read and Store Calibration Memory Values procedure.
2: The device should not be used if verification of the Calibration Word locations fails. This information
should be reported to the user through the user interface of the device programmer.
DS41284E-page 18 2010 Microchip Technology Inc.
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
5.0 CONFIGURATION WORD
The PIC12F609/12F615/12F617/16F610/16F616 and
PIC12HV609/12HV615/16HV610/16HV616 devices
have several Configuration bits. These bits can be
programmed (reads ‘0’) or left unchanged (reads ‘1’), to
select various device configurations.
REGISTER 5-1: CONFIG: CONFIGURATION WORD (ADDRESS: 2007h)
U-1 U-1 U-1 U-1 R/P-1 R/P-1 R/P-1
— — — — BOREN1 BOREN0 IOSCFS
bit 13
R/P-1 R/P-1 R/P-1 R/P-1 R/P-1 R/P-1 R/P-1
CP MCLRE PWRTE WDTE FOSC2 FOSC1 FOSC0
bit 6
Legend: x = Bit is unknown P = Programmable bit
R = Readable bit W = Writable bit U = Unimplemented bit, read as ‘0’
-n = Value at POR ‘1’ = Bit is set ‘0’ = Bit is cleared
bit 13-10 Unimplemented: Read as ‘1’
bit 9-8 BOREN<1:0>: Brown-out Reset Enable bits
11 = BOR enabled
10 = BOR enabled while running and disabled in Sleep
0x = BOR disabled
bit 7 IOSCFS: Internal Oscillator Frequency Select bit
1 = 8 MHz
0 = 4 MHz
bit 6 CP: Code Protection bit
1 = Program memory is not code-protected
0 = Program memory is external read and write-protected
bit 5 MCLRE: MCLR Pin Function Select bit
1 = MCLR pin is MCLR function and weak internal pull-up is enabled
0 = MCLR pin is alternate function, MCLR function is internally disabled
bit 4 PWRTE: Power-up Timer Enable bit(1)
1 = PWRT disabled
0 = PWRT enabled
bit 3 WDTE: Watchdog Timer Enable bit
1 = WDT enabled
0 = WDT disabled
bit 2-0 FOSC<2:0>: Oscillator Selection bits
000 = LP oscillator: Low-power crystal on RA5/GP5 and RA4/GP4
001 = XT oscillator: Crystal/resonator on RA5/GP5 and RA4/GP4
010 = HS oscillator: High-speed crystal/resonator on RA5/GP5 and RA4/GP4
011 = EC: I/O function on RA4/GP4, CLKIN on RA5/GP5
100 = INTOSCIO oscillator: I/O function on RA4/GP4, I/O function on RA5/GP5
101 = INTOSC oscillator: CLKOUT function on RA4/GP4, I/O function on RA5/GP5
110 = EXTRCIO oscillator: I/O function on RA4/GP4, RC on RA5/GP5
111 = EXTRC oscillator: CLKOUT function on RA4/GP4, RC on RA5/GP5
Note 1: Enabling Brown-out Reset does not automatically enable Power-up Timer.
2010 Microchip Technology Inc. DS41284E-page 19
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
REGISTER 5-2: CONFIG: CONFIGURATION WORD (ADDRESS: 2007h) FOR PIC12F617 ONLY
U-1 U-1 U-1 U-1 R/P-1 R/P-1 R/P-1
— — WRT1 WRT0 BOREN1 BOREN0 IOSCFS
bit 13
R/P-1 R/P-1 R/P-1 R/P-1 R/P-1 R/P-1 R/P-1
CP MCLRE PWRTE WDTE FOSC2 FOSC1 FOSC0
bit 6
Legend: x = Bit is unknown P = Programmable bit
R = Readable bit W = Writable bit U = Unimplemented bit, read as ‘0’
-n = Value at POR ‘1’ = Bit is set ‘0’ = Bit is cleared
bit 13-12 Unimplemented: Read as ‘1’
bit 11-10 WRT<1:0>: Flash Program Memory Self Write Enable bit
11 =Write protection off
10 =000h to 1FFh write-protected, 200h to 7FFh may be modified by PMCON1 control
01 =000h to 3FFh write-protected, 400h to 7FFh may be modified by PMCON1 control
00 =000h to 7FFh write-protected, entire program memory is write-protected
bit 9-8 BOREN<1:0>: Brown-out Reset Enable bit
11 =BOR enabled
10 =BOR disabled during Sleep and enabled during operation
0X =BOR disabled
bit 7 IOSCFS: Internal Oscillator Frequency Select
1 = 8 MHz
0 = 4 MHz
bit 6 CP: Code Protection
1 = Program memory is not code-protected
0 = Program memory is external read and write-protected
bit 5 MCLRE: MCLR Pin Function Select
1 = MCLR pin is MCLR function and weak internal pull-up is enabled
0 = MCLR pin is alternate function, MCLR function is internally disabled
bit 4 PWRTE: Power-up Timer Enable bit(1)
1 = PWRT disabled
0 = PWRT enabled
bit 3 WDTE: Watchdog Timer Enable bit
1 = WDT enabled
0 = WDT disabled
Note 1: Enabling Brown-out Reset does not automatically enable Power-up Timer (PWRT).
DS41284E-page 20 2010 Microchip Technology Inc.
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
REGISTER 5-2: CONFIG: CONFIGURATION WORD (ADDRESS: 2007h) (CONTINUED)FOR
bit 2-0 FOSC<2:0>: Oscillator Selection bits
000 = LP oscillator: Low-power crystal on RA5/T1CKI/OSC1/CLKIN and
RA4/AN3/T1G/OSC2/CLKOUT
001 = XT oscillator: Crystal/resonator on RA5/T1CKI/OSC1/CLKIN and
RA4/AN3/T1G/OSC2/CLKOUT
010 = HS oscillator: High-speed crystal/resonator on RA5/T1CKI/OSC1/CLKIN and
RA4/AN3/T1G/OSC2/CLKOUT
011 = EC: I/O function on RA4/AN3/T1G/OSC2/CLKOUT, CLKIN on RA5/T1CKI/OSC1/CLKIN
100 = INTOSCIO oscillator: I/O function on RA4/AN3/T1G/OSC2/CLKOUT, I/O function on
RA5/T1CKI/OSC1/CLKIN
101 = INTOSC oscillator: CLKOUT function on RA4/AN3/T1G/OSC2/CLKOUT, I/O function on
RA5/T1CKI/OSC1/CLKIN
110 = EXTRCIO oscillator: I/O function on RA4/AN3/T1G/OSC2/CLKOUT, RC on
RA5/T1CKI/OSC1/CLKIN
111 = EXTRC oscillator: CLKOUT function on RA4/AN3/T1G/OSC2/CLKOUT, RC on
RA5/T1CKI/OSC1/CLKIN
Note 1: Enabling Brown-out Reset does not automatically enable Power-up Timer (PWRT).
5.1 Device ID Word
The device ID word for the PIC12F609/12F615/
12F617/16F610/16F616 and PIC12HV609/12HV615/
16HV610/16HV616 is loaded at 2006h. This location
can not be erased.
TABLE 5-1: DEVICE ID VALUES
Device ID Values
Device
Dev Rev
PIC12F615 10 0001 100 x xxxx
PIC12HV615 10 0001 101 x xxxx
PIC12F617 01 0011 011 x xxxx
PIC16F616 01 0010 010 x xxxx
PIC16HV616 01 0010 011 x xxxx
PIC12F609 10 0010 010 x xxxx
PIC12HV609 10 0010 100 x xxxx
PIC16F610 10 0010 011 x xxxx
PIC16HV610 10 0010 101 x xxxx
2010 Microchip Technology Inc. DS41284E-page 21
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
6.0 CODE PROTECTION 6.3 Checksum Computation
For PIC12F609/12F615/12F617/16F610/16F616 and 6.3.1 CHECKSUM
PIC12HV609/12HV615/16HV610/16HV616, once the
CP bit is programmed to ‘0’, all program memory locations Checksum is calculated by reading the contents of the
read all ‘0’s. The user ID locations and the Configuration program memory locations and adding up the opcodes
Word read out in an unprotected fashion. Further up to the maximum user addressable location (e.g.,
programming is disabled for the entire program memory. 0x7FF for the PIC16F616). Any carry bits exceeding 16
bits are neglected. Finally, the Configuration Word
The user ID locations and the Configuration Word can (appropriately masked) is added to the checksum. The
be programmed regardless of the state of the CP bit. checksum computation for the PIC12F609/12F615/
12F617/16F610/16F616 and PIC12HV609/12HV615/
6.1 Disabling Code Protection 16HV610/16HV616 devices is shown in Table 6-1.
It is recommended to use the procedure in Figure 4-15 The checksum is calculated by summing the following:
to disable code protection of the device. This sequence • The contents of all program memory locations
will erase the program memory, Configuration Word • The Configuration Word, appropriately masked
(0x2007) and user ID locations (0x2000-0x2003). The
• Masked user ID locations (when applicable)
Calibration Word (0x2008) will not be erased.
The Least Significant 16 bits of this sum is the
6.2 Embedding Configuration Word checksum.
and User ID Information in the Hex Table 6-1 describes how to calculate the checksum for
File each device. Note that the checksum calculation differs
depending on the code-protect setting. Since the
To allow portability of code, the programmer is required program memory locations read out zeroes when code-
to read the Configuration Word and user ID locations protected, the table describes how to manipulate the
from the hex file when loading the hex file. If Configura- actual program memory values to simulate values that
tion Word information was not present in the hex file, a would be read from a protected device. When calculat-
simple warning message may be issued. Similarly, ing a checksum by reading a device, the entire program
while saving a hex file, Configuration Word and user ID memory can simply be read and summed. The
information must be included. An option to not include Configuration Word and user ID locations can always
this information may be provided. be read regardless of code-protect setting.
Microchip Technology Incorporated feels strongly that Note: Some older devices have an additional
this feature is important for the benefit of the end value added in the checksum. This is to
customer. maintain compatibility with older device
programmer checksums.
DS41284E-page 22 2010 Microchip Technology Inc.
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
TABLE 6-1: CHECKSUM COMPUTATIONS
0x25E6 at 0
Code Blank
Device Checksum* and Max.
Protect Value
Address
PIC12F615/HV615 CP = 1 SUM[0x000:0x03FF] + (CFGW & 0x03FF) 0xFFFF 0xCBCD
CP = 0 (CFGW & 0x03FF) + SUM_ID 0x03BE 0xCF8C
PIC12F617 CP = 1 SUM[0x000:0x07FF] + (CFGW & 0x03FF) 0xFBFF 0xC7CD
CP = 0 (CFGW & 0x03FF) + SUM_ID 0x03BE 0xCF8C
PIC12F609/HV609 CP = 1 SUM[0x000:0x03FF] + (CFGW & 0x03FF) 0xFFFF 0xCBCD
CP = 0 (CFGW &0x03FF) + SUM_ID 0x03BE 0xCF8C
PIC16F610/HV610 CP = 1 SUM[0x000:0x03FF] + (CFGW & 0x03FF) 0xFFFF 0xCBCD
CP = 0 (CFGW & 0x03FF) + SUM_ID 0x03BE 0xCF8C
PIC16F616/HV616 CP = 1 SUM[0x000:0x07FF] + (CFGW & 0x03FF) 0xFBFF 0xC7CD
CP = 0 (CFGW & 0x03FF) + SUM_ID 0x03BE 0xCF8C
Legend: CFGW = Configuration Word. Example calculations assume Configuration Word is erased (all ‘1’s).
SUM[a:b] = [Sum of locations a to b inclusive]
SUM_ID = User ID locations masked by 0xF then made into a 16-bit value with ID0 as the Most Significant
nibble. For example, ID0 = 0x1, ID1 = 0x2, ID3 = 0x3, ID4 = 0x4, then SUM_ID = 0x1234. The 4 LSb’s of
the unprotected checksum is used for the example calculations.
*Checksum = [Sum of all the individual expressions] MODULO [0xFFFF]
+ = Addition
& = Bitwise AND
2010 Microchip Technology Inc. DS41284E-page 23
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
7.0 PROGRAM/VERIFY MODE ELECTRICAL CHARACTERISTICS
TABLE 7-1: AC/DC CHARACTERISTICS TIMING REQUIREMENTS FOR PROGRAM/VERIFY
MODE
Standard Operating Conditions (unless otherwise stated)
AC/DC CHARACTERISTICS Operating Temperature -40°C TA +85°C
Operating Voltage 4.5V VDD 5.5V
Sym. Characteristics Min. Typ. Max. Units Conditions/Comments
General
VDD VDD level for read/write operations, 2.0 — 5.5 V PIC16F616/F610,
program and data memory PIC12F615/F617/F609
2.0 — 4.7(1) V PIC16HV616/HV610,
PIC12HV615/HV609
2.0 — 5.25(2) V PIC16HV616/HV610,
PIC12HV615/HV609
VDD level for Bulk Erase operations, 4.5 — 5.5 V PIC16F616/F610,
program and data memory PIC12F615/F617/F609
4.5 — 4.7(1) V PIC16HV616/HV610,
PIC12HV615/HV609
4.5 — 5.25(2) V PIC16HV616/HV610,
PIC12HV615/HV609
VIHH High voltage on MCLR for 10 — 13 V
Program/Verify mode entry
IIHH MCLR current during programming — 300 1000 A
TVHHR MCLR rise time (VSS to VHH) for — — 1.0 s
Program/Verify mode entry
TPPDP Hold time after VPPchanges 5 — — s
VIH1 (ICSPCLK, ICSPDAT) input high level 0.8 VDD — — V
VIL1 (ICSPCLK, ICSPDAT) input low level 0.2 VDD — — V
TSET0 ICSPCLK, ICSPDAT setup time 100 — — ns
before MCLR (Program/Verify mode
selection pattern setup time)
THLD0 Hold time after VDD changes 5 — — s
Serial Program/Verify
TSET1 Data in setup time before clock 100 — — ns
THLD1 Data in hold time after clock 100 — — ns
TDLY1 Data input not driven to next clock 1.0 — — s
input (delay required between
command/data or command/
command)
TDLY2 Delay between clockto clockof 1.0 — — s
next command or data
TDLY3 Clock to data out valid (during a — — 80 ns
Read Data command)
TERA Erase cycle time — 5 6 ms
TPROG Programming cycle time 3 — — ms 10°C TA +40°C
TDIS Time delay from program to compare 100 — — s
(HV discharge time)
Note 1: Maximum VDD voltage when programming the device without a current limiting series resistor. Voltages above this level
will cause the shunt regulator to draw excessive current and damage the device.
2: Limiting the current through the shunt regulator to within max shunt current (device electrical characteristic SR02) with
either a series resistor or with a current limited supply.
DS41284E-page 24 2010 Microchip Technology Inc.
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
APPENDIX A: REVISION HISTORY
Revision A (2/06)
Original release.
Revision B (11/06)
Section 1.0 “Device Overview”Added devices.
Section 2.1 “Hardware Requirements”Reworded.
Section 2.2 “Program/Verify Mode”Deleted data
memory.
Figure 2-1 Added 16 pin and note 1.
Figure 2-1 Reworded Note 1.
Section 3.3 “Calibration Word”Changed to 8 MHz.
Figure 3-1 Changed title.
Section 4.1 “Program/Erase Algorithms”Added text
under note.
Section 4.1.3 “Erase Algorithms”Moved One word
programming to section 4.1.1.
Figure 4-12 Changed title.
Figure 4-13 Changed title.
Register Added GP4 and GP5, added note.
Register 5.1 Bit 13 and bits 5-0 changed to unim-
plemented read as “1”.
Section 6.3.1 “Checksum”Changed Lease to Least.
Changed CARRY to lowercase.
Revision C (05/07)
Changed device family name
Section 2.1 Revised Section 2.1
Section 3.1 Changed 0x000 to 0x0000
Table 6-1 Changed 1FFF to 0x03FF
Table 7-1 Revised VDD section
Revised Note 1 and Added Note 2
Revision D (12/09)
Updated sections 2.2, 3.3, 4.1.3, 4.1.4.1; Updated
Figures 4-11, 4-12, 4-13, 4-14; Added Figure 4-15.
Revision E (04/10)
Added PIC12F617 part number; minor edits.
This document replaces DS41396.
2010 Microchip Technology Inc. DS41284E-page 25
PIC12F609/12F615/12F617/16F610/16F616 AND PIC12HV609/12HV615/16HV610/16HV616
NOTES:
DS41284E-page 26 2010 Microchip Technology Inc.
Note the following details of the code protection feature on Microchip devices:
• Microchip products meet the specification contained in their particular Microchip Data Sheet.
• Microchip believes that its family of products is one of the most secure families of its kind on the market today, when used in the
intended manner and under normal conditions.
• There are dishonest and possibly illegal methods used to breach the code protection feature. All of these methods, to our
knowledge, require using the Microchip products in a manner outside the operating specifications contained in Microchip’s Data
Sheets. Most likely, the person doing so is engaged in theft of intellectual property.
• Microchip is willing to work with the customer who is concerned about the integrity of their code.
• Neither Microchip nor any other semiconductor manufacturer can guarantee the security of their code. Code protection does not
mean that we are guaranteeing the product as “unbreakable.”
Code protection is constantly evolving. We at Microchip are committed to continuously improving the code protection features of our
products. Attempts to break Microchip’s code protection feature may be a violation of the Digital Millennium Copyright Act. If such acts
allow unauthorized access to your software or other copyrighted work, you may have a right to sue for relief under that Act.
Information contained in this publication regarding device Trademarks
applications and the like is provided only for your convenience
The Microchip name and logo, the Microchip logo, dsPIC,
and may be superseded by updates. It is your responsibility to
KEELOQ, KEELOQ logo, MPLAB, PIC, PICmicro, PICSTART,
ensure that your application meets with your specifications.
PIC32 logo, rfPIC and UNI/O are registered trademarks of
MICROCHIP MAKES NO REPRESENTATIONS OR
Microchip Technology Incorporated in the U.S.A. and other
WARRANTIES OF ANY KIND WHETHER EXPRESS OR countries.
IMPLIED, WRITTEN OR ORAL, STATUTORY OR
OTHERWISE, RELATED TO THE INFORMATION, FilterLab, Hampshire, HI-TECH C, Linear Active Thermistor,
INCLUDING BUT NOT LIMITED TO ITS CONDITION, MXDEV, MXLAB, SEEVAL and The Embedded Control
QUALITY, PERFORMANCE, MERCHANTABILITY OR Solutions Company are registered trademarks of Microchip
FITNESS FOR PURPOSE. Microchip disclaims all liability Technology Incorporated in the U.S.A.
arising from this information and its use. Use of Microchip Analog-for-the-Digital Age, Application Maestro, CodeGuard,
devices in life support and/or safety applications is entirely at dsPICDEM, dsPICDEM.net, dsPICworks, dsSPEAK, ECAN,
the buyer’s risk, and the buyer agrees to defend, indemnify and ECONOMONITOR, FanSense, HI-TIDE, In-Circuit Serial
hold harmless Microchip from any and all damages, claims, Programming, ICSP, Mindi, MiWi, MPASM, MPLAB Certified
suits, or expenses resulting from such use. No licenses are logo, MPLIB, MPLINK, mTouch, Octopus, Omniscient Code
conveyed, implicitly or otherwise, under any Microchip Generation, PICC, PICC-18, PICDEM, PICDEM.net, PICkit,
intellectual property rights. PICtail, REAL ICE, rfLAB, Select Mode, Total Endurance,
TSHARC, UniWinDriver, WiperLock and ZENA are
trademarks of Microchip Technology Incorporated in the
U.S.A. and other countries.
SQTP is a service mark of Microchip Technology Incorporated
in the U.S.A.
All other trademarks mentioned herein are property of their
respective companies.
© 2010, Microchip Technology Incorporated, Printed in the
U.S.A., All Rights Reserved.
Printed on recycled paper.
ISBN: 978-1-60932-165-9
Microchip received ISO/TS-16949:2002 certification for its worldwide
headquarters, design and wafer fabrication facilities in Chandler and
Tempe, Arizona; Gresham, Oregon and design centers in California
and India. The Company’s quality system processes and procedures
are for its PIC® MCUs and dsPIC® DSCs, KEELOQ® code hopping
devices, Serial EEPROMs, microperipherals, nonvolatile memory and
analog products. In addition, Microchip’s quality system for the design
and manufacture of development systems is ISO 9001:2000 certified.
2010 Microchip Technology Inc. DS41284E-page 27
WORLDWIDE SALES AND SERVICE
AMERICAS ASIA/PACIFIC ASIA/PACIFIC EUROPE
Corporate Office Asia Pacific Office India - Bangalore Austria - Wels
2355 West Chandler Blvd. Suites 3707-14, 37th Floor Tel: 91-80-3090-4444 Tel: 43-7242-2244-39
Chandler, AZ 85224-6199 Tower 6, The Gateway Fax: 91-80-3090-4123 Fax: 43-7242-2244-393
Tel: 480-792-7200 Harbour City, Kowloon Denmark - Copenhagen
India - New Delhi
Fax: 480-792-7277 Hong Kong Tel: 45-4450-2828
Tel: 91-11-4160-8631
Technical Support: Tel: 852-2401-1200 Fax: 45-4485-2829
Fax: 91-11-4160-8632
http://support.microchip.com Fax: 852-2401-3431
India - Pune France - Paris
Web Address:
Australia - Sydney Tel: 91-20-2566-1512 Tel: 33-1-69-53-63-20
www.microchip.com
Tel: 61-2-9868-6733 Fax: 91-20-2566-1513 Fax: 33-1-69-30-90-79
Atlanta Fax: 61-2-9868-6755
Japan - Yokohama Germany - Munich
Duluth, GA
China - Beijing Tel: 49-89-627-144-0
Tel: 678-957-9614 Tel: 81-45-471- 6166
Tel: 86-10-8528-2100 Fax: 49-89-627-144-44
Fax: 678-957-1455 Fax: 81-45-471-6122
Fax: 86-10-8528-2104 Italy - Milan
Boston Korea - Daegu
China - Chengdu Tel: 39-0331-742611
Westborough, MA Tel: 82-53-744-4301
Tel: 86-28-8665-5511 Fax: 39-0331-466781
Tel: 774-760-0087 Fax: 82-53-744-4302
Fax: 86-28-8665-7889 Netherlands - Drunen
Fax: 774-760-0088 Korea - Seoul
China - Chongqing Tel: 82-2-554-7200 Tel: 31-416-690399
Chicago
Tel: 86-23-8980-9588 Fax: 82-2-558-5932 or Fax: 31-416-690340
Itasca, IL
Tel: 630-285-0071 Fax: 86-23-8980-9500 82-2-558-5934 Spain - Madrid
Fax: 630-285-0075 China - Hong Kong SAR Tel: 34-91-708-08-90
Malaysia - Kuala Lumpur
Tel: 852-2401-1200 Tel: 60-3-6201-9857 Fax: 34-91-708-08-91
Cleveland
Independence, OH Fax: 852-2401-3431 Fax: 60-3-6201-9859 UK - Wokingham
Tel: 216-447-0464 China - Nanjing Tel: 44-118-921-5869
Malaysia - Penang
Fax: 216-447-0643 Tel: 86-25-8473-2460 Fax: 44-118-921-5820
Tel: 60-4-227-8870
Dallas Fax: 86-25-8473-2470 Fax: 60-4-227-4068
Addison, TX China - Qingdao Philippines - Manila
Tel: 972-818-7423 Tel: 86-532-8502-7355 Tel: 63-2-634-9065
Fax: 972-818-2924 Fax: 86-532-8502-7205 Fax: 63-2-634-9069
Detroit China - Shanghai Singapore
Farmington Hills, MI Tel: 86-21-5407-5533 Tel: 65-6334-8870
Tel: 248-538-2250 Fax: 86-21-5407-5066 Fax: 65-6334-8850
Fax: 248-538-2260
China - Shenyang Taiwan - Hsin Chu
Kokomo Tel: 86-24-2334-2829 Tel: 886-3-6578-300
Kokomo, IN Fax: 86-24-2334-2393 Fax: 886-3-6578-370
Tel: 765-864-8360
Fax: 765-864-8387 China - Shenzhen Taiwan - Kaohsiung
Tel: 86-755-8203-2660 Tel: 886-7-536-4818
Los Angeles Fax: 86-755-8203-1760 Fax: 886-7-536-4803
Mission Viejo, CA
Tel: 949-462-9523 China - Wuhan Taiwan - Taipei
Fax: 949-462-9608 Tel: 86-27-5980-5300 Tel: 886-2-2500-6610
Fax: 86-27-5980-5118 Fax: 886-2-2508-0102
Santa Clara
Santa Clara, CA China - Xian Thailand - Bangkok
Tel: 408-961-6444 Tel: 86-29-8833-7252 Tel: 66-2-694-1351
Fax: 408-961-6445 Fax: 86-29-8833-7256 Fax: 66-2-694-1350
Toronto China - Xiamen
Mississauga, Ontario, Tel: 86-592-2388138
Canada Fax: 86-592-2388130
Tel: 905-673-0699 China - Zhuhai
Fax: 905-673-6509 Tel: 86-756-3210040
Fax: 86-756-3210049
01/05/10
DS41284E-page 28 2010 Microchip Technology Inc.
Potrebbero piacerti anche
- PICmem Prog SpecDocumento38 paginePICmem Prog SpecdkelicNessuna valutazione finora
- 16F88Documento24 pagine16F88thetkhinechoNessuna valutazione finora
- PIC16F88X Memory Programming SpecificationDocumento36 paginePIC16F88X Memory Programming Specificationwin.halongNessuna valutazione finora
- PIC16F87XA Data Sheet: 28/40-Pin Enhanced FLASH MicrocontrollersDocumento56 paginePIC16F87XA Data Sheet: 28/40-Pin Enhanced FLASH MicrocontrollersXinantecatl L SolaresNessuna valutazione finora
- PIC16F88X Memory Programming Specification PDFDocumento36 paginePIC16F88X Memory Programming Specification PDFMarcio FreitasNessuna valutazione finora
- 41208CDocumento16 pagine41208CFernando ANessuna valutazione finora
- Pic 16 C 54 CDocumento5 paginePic 16 C 54 Ccuaco_ibm5328Nessuna valutazione finora
- Lector de Bus de Datos IÂ CDocumento4 pagineLector de Bus de Datos IÂ CGiancarloRichardRivadeneyraMiranda100% (1)
- BAI 1 - Led Don - 7 DoanDocumento7 pagineBAI 1 - Led Don - 7 DoanTrần Ngọc Thiên DiNessuna valutazione finora
- Programming Pic Microcontrollers Using Pickit 2 / 3 ProgrammersDocumento1 paginaProgramming Pic Microcontrollers Using Pickit 2 / 3 Programmerscmlcaldeira10Nessuna valutazione finora
- PIC16C5XX: EPROM/ROM Memory Programming/Verify SpecificationDocumento16 paginePIC16C5XX: EPROM/ROM Memory Programming/Verify SpecificationdamarcrazyNessuna valutazione finora
- PIC16C5X: EPROM/ROM-Based 8-Bit CMOS Microcontroller SeriesDocumento158 paginePIC16C5X: EPROM/ROM-Based 8-Bit CMOS Microcontroller SeriesfrancescoNessuna valutazione finora
- PIC18FXX2/XX8: Flash Microcontroller Programming SpecificationDocumento36 paginePIC18FXX2/XX8: Flash Microcontroller Programming Specificationhkn89Nessuna valutazione finora
- ©ramandeep Singh 2004: Nokia 3310 LCD To PIC16F628 InterfaceDocumento1 pagina©ramandeep Singh 2004: Nokia 3310 LCD To PIC16F628 InterfaceAnonymous GxeR0L100% (2)
- DatasheetDocumento202 pagineDatasheetMohammed amine kissiNessuna valutazione finora
- Interfacing Keypad With PIC 16F877A MicrocontrollerDocumento6 pagineInterfacing Keypad With PIC 16F877A MicrocontrollerEysha qureshi100% (1)
- Da DKCNDocumento3 pagineDa DKCNTrọng LêNessuna valutazione finora
- Pic 16c5xxDocumento220 paginePic 16c5xxshishir_2895Nessuna valutazione finora
- SDNL 1Documento1 paginaSDNL 1Trọng LêNessuna valutazione finora
- Hard BootDocumento1 paginaHard BootJairo Andrés Quiñones Buitrago100% (2)
- Pin Diagrams: 28-Pin Pdip, Soic, SsopDocumento2 paginePin Diagrams: 28-Pin Pdip, Soic, SsopAlita2822Nessuna valutazione finora
- Gesture Controlled Slide NavigatorDocumento17 pagineGesture Controlled Slide NavigatorAnkur GuptaNessuna valutazione finora
- GLCD TestDocumento1 paginaGLCD TestTran Chi QuyetNessuna valutazione finora
- Reset: 20MHZ X1 15pF C1 15pF C2Documento1 paginaReset: 20MHZ X1 15pF C1 15pF C2Chiton AguirreNessuna valutazione finora
- PIC16C55X (A) DatasheetDocumento96 paginePIC16C55X (A) DatasheetWarr SteelNessuna valutazione finora
- BAI 2 - Timer - Counter - Interrupt - LCDDocumento11 pagineBAI 2 - Timer - Counter - Interrupt - LCDTrần Ngọc Thiên DiNessuna valutazione finora
- ZZZZDocumento1 paginaZZZZid musicNessuna valutazione finora
- KS31203 Embedded System: LECTURE 6 - Working With Time: Interrupts and TimersDocumento32 pagineKS31203 Embedded System: LECTURE 6 - Working With Time: Interrupts and TimersZulhaily ZhafranNessuna valutazione finora
- Esque Matic oDocumento1 paginaEsque Matic oGusTavo Villalobos AvilaNessuna valutazione finora
- 16 C 57 CDocumento192 pagine16 C 57 Cepahk3631Nessuna valutazione finora
- Drill 2.0 Basic I-O Switching TheoryDocumento13 pagineDrill 2.0 Basic I-O Switching TheoryDuaneNessuna valutazione finora
- 16FUSB Schematic-1.2 PDFDocumento1 pagina16FUSB Schematic-1.2 PDFgermanmkurylo100% (1)
- Exemplo KetyDocumento2 pagineExemplo Ketyric1988lealNessuna valutazione finora
- X-10 Data-Stream MonitorDocumento4 pagineX-10 Data-Stream MonitorGustavo PiaiNessuna valutazione finora
- TermometroDocumento1 paginaTermometroRafael Macfú100% (1)
- Pickit2 Clone 1Documento1 paginaPickit2 Clone 1Lorgio Chura Carrillo100% (1)
- Proteus LEDDocumento3 pagineProteus LEDMuhammad Zikri AbdillahNessuna valutazione finora
- Project 07aDocumento1 paginaProject 07aPushpa kumaraNessuna valutazione finora
- VCC GND SCL Sda Xda XCL Ado Int: U1 (RA7/OSC1/CLKIN)Documento1 paginaVCC GND SCL Sda Xda XCL Ado Int: U1 (RA7/OSC1/CLKIN)Donaldo Ruiz PeñaNessuna valutazione finora
- New ProjectDocumento1 paginaNew ProjectSahariar Bin ShafiqueNessuna valutazione finora
- QLdsPIC3 User's ManualDocumento43 pagineQLdsPIC3 User's ManualJohnny Romero MiliánNessuna valutazione finora
- Vh-2C Programador de Pics Realizado Por: Víctor Hugo CaizaDocumento1 paginaVh-2C Programador de Pics Realizado Por: Víctor Hugo CaizaJuan Luis Carr100% (1)
- 3921 Fig 02Documento1 pagina3921 Fig 02Matheus Régis Dias100% (2)
- Datasheet Search Site PDFDocumento192 pagineDatasheet Search Site PDFALEXSAHDRNessuna valutazione finora
- Microcontroller With 2/4K Bytes In-System Programmable FlashDocumento22 pagineMicrocontroller With 2/4K Bytes In-System Programmable FlashRicardoNessuna valutazione finora
- PicKit2 Clone CompletoDocumento7 paginePicKit2 Clone CompletoJason David Valverde MezarinaNessuna valutazione finora
- PIC16F87X: 28/40-Pin 8-Bit CMOS FLASH MicrocontrollersDocumento201 paginePIC16F87X: 28/40-Pin 8-Bit CMOS FLASH MicrocontrollerscricsoNessuna valutazione finora
- PIC PWM ControllerDocumento10 paginePIC PWM Controllerkeitabando100% (2)
- PIC TutorialDocumento979 paginePIC TutorialKamaldeep Singh ChouhanNessuna valutazione finora
- 16F87X Datasheet - Version ResumidaDocumento69 pagine16F87X Datasheet - Version ResumidamowliwhiteNessuna valutazione finora
- PIC16C5X - EPROM/ROM-Based 8-Bit CMOS Microcontroller Series - 30453cDocumento158 paginePIC16C5X - EPROM/ROM-Based 8-Bit CMOS Microcontroller Series - 30453cGuillermo HernandezNessuna valutazione finora
- KeypadDocumento1 paginaKeypadPhap Nguyen100% (1)
- 16F877 Data SheetDocumento201 pagine16F877 Data Sheetjohn11221Nessuna valutazione finora
- FSR Tool Kit Parts RaDocumento1 paginaFSR Tool Kit Parts RaMauricio Pablo Leonar GonzalezNessuna valutazione finora
- 10 EMI 04 The PIC Micro ControllerDocumento20 pagine10 EMI 04 The PIC Micro Controllerapi-3707706100% (1)
- Alarme GSM Sim900Documento1 paginaAlarme GSM Sim900EliasNessuna valutazione finora
- CNC-fabtroller SchematicDocumento1 paginaCNC-fabtroller SchematicTomi OzzyNessuna valutazione finora
- 8051 Microcontroller: An Applications Based IntroductionDa Everand8051 Microcontroller: An Applications Based IntroductionValutazione: 5 su 5 stelle5/5 (6)
- CCTV Surveillance: Video Practices and TechnologyDa EverandCCTV Surveillance: Video Practices and TechnologyValutazione: 4 su 5 stelle4/5 (1)
- Presto enDocumento100 paginePresto encurzNessuna valutazione finora
- Horizon Compact Plus Loss of Management After 208 Days - TN-000041-01-En-02Documento5 pagineHorizon Compact Plus Loss of Management After 208 Days - TN-000041-01-En-02curzNessuna valutazione finora
- Manual Do ProdutoDocumento26 pagineManual Do ProdutocurzNessuna valutazione finora
- (At Command) Usr Tcp232 E2 at Command Set - v1.0.0Documento22 pagine(At Command) Usr Tcp232 E2 at Command Set - v1.0.0curzNessuna valutazione finora
- Resumen SW NewDocumento20 pagineResumen SW NewcurzNessuna valutazione finora
- Cambium PTP 650 Series User Guide: System Release 650-01-00Documento196 pagineCambium PTP 650 Series User Guide: System Release 650-01-00curzNessuna valutazione finora
- Manual Do ProdutoDocumento26 pagineManual Do ProdutocurzNessuna valutazione finora
- Important Notice: Kind RegardsDocumento15 pagineImportant Notice: Kind RegardscurzNessuna valutazione finora
- Manual Do ProdutoDocumento26 pagineManual Do ProdutocurzNessuna valutazione finora
- 50650.installation Guide 2061303Documento39 pagine50650.installation Guide 2061303curzNessuna valutazione finora
- LTC 4252Documento37 pagineLTC 4252curzNessuna valutazione finora
- Customer Release Notes 07 01 83 7 1 Phase I - RGMDocumento18 pagineCustomer Release Notes 07 01 83 7 1 Phase I - RGMcurzNessuna valutazione finora
- TS922, TS922A: Rail-To-Rail, High Output Current Dual Operational AmplifierDocumento24 pagineTS922, TS922A: Rail-To-Rail, High Output Current Dual Operational AmplifiercurzNessuna valutazione finora
- Sofix Power Cable AssembliesDocumento2 pagineSofix Power Cable AssembliescurzNessuna valutazione finora
- HA178L00 Series: 3-Terminal Fixed Voltage RegulatorsDocumento22 pagineHA178L00 Series: 3-Terminal Fixed Voltage RegulatorscurzNessuna valutazione finora
- UPC2762TB: Bipolar Analog Integrated CircuitDocumento6 pagineUPC2762TB: Bipolar Analog Integrated CircuitcurzNessuna valutazione finora
- VI-200 / VI-J00 Family: Design Guide & Applications ManualDocumento97 pagineVI-200 / VI-J00 Family: Design Guide & Applications ManualcurzNessuna valutazione finora
- 2.5-6.0/5.0-12.0 GHZ Gaas Mmic Active Doubler: Features Chip Device Layout X1002-BdDocumento5 pagine2.5-6.0/5.0-12.0 GHZ Gaas Mmic Active Doubler: Features Chip Device Layout X1002-BdcurzNessuna valutazione finora
- Rtcclient Tool Quick Guide: Date Jan. 25, 2011Documento3 pagineRtcclient Tool Quick Guide: Date Jan. 25, 2011curzNessuna valutazione finora
- Customer Release Notes 07 01 83 7 1 Phase I - RGMDocumento17 pagineCustomer Release Notes 07 01 83 7 1 Phase I - RGMcurzNessuna valutazione finora
- Europe Power Cord Specs PDFDocumento9 pagineEurope Power Cord Specs PDFcurzNessuna valutazione finora
- Credenziali ARIADocumento1 paginaCredenziali ARIAcurzNessuna valutazione finora
- Key Features: Bias: VD 5 V & 7 V, Idq 1.05 ADocumento18 pagineKey Features: Bias: VD 5 V & 7 V, Idq 1.05 AcurzNessuna valutazione finora
- Microsoft Windows: Types of Operating SystemsDocumento17 pagineMicrosoft Windows: Types of Operating SystemsAnonymous VHWPQErC3Nessuna valutazione finora
- CH 1 Notes FullDocumento21 pagineCH 1 Notes FullSeif MahmoudNessuna valutazione finora
- A6V10097438Documento120 pagineA6V10097438ABI RAJESH GANESHA RAJANessuna valutazione finora
- Honeywell Acm 72Documento8 pagineHoneywell Acm 72Delbert RicardoNessuna valutazione finora
- S7-300 Module Data - Analog IO Module SM 334Documento7 pagineS7-300 Module Data - Analog IO Module SM 334dragon_tudvnNessuna valutazione finora
- OS Unit-1 NotesDocumento23 pagineOS Unit-1 Notesanjali sowmyaNessuna valutazione finora
- SA80-PM-031 - Saturn 8000 1717V Service Manual - 1.2 - VW - 1.3 - 20211014 - NO GMP - Old AddressDocumento45 pagineSA80-PM-031 - Saturn 8000 1717V Service Manual - 1.2 - VW - 1.3 - 20211014 - NO GMP - Old AddressArllette MeridaNessuna valutazione finora
- QuickSilver Controls QCI-DS031 QCI-N2-IXDocumento14 pagineQuickSilver Controls QCI-DS031 QCI-N2-IXElectromateNessuna valutazione finora
- Prof. Zoltan Francisc Baruch: Computer Science Department Technical University of Cluj-NapocaDocumento28 pagineProf. Zoltan Francisc Baruch: Computer Science Department Technical University of Cluj-NapocaAlex TăbușcăNessuna valutazione finora
- Chapter 9. Embedded Systems: Computer OrganizationDocumento20 pagineChapter 9. Embedded Systems: Computer Organizationapi-3723664Nessuna valutazione finora
- Liebert Ac4 User Manual PDFDocumento89 pagineLiebert Ac4 User Manual PDFMohamedNessuna valutazione finora
- Rainfall Prediction Based On Rainfall Statistical DataDocumento6 pagineRainfall Prediction Based On Rainfall Statistical DataEditor IJRITCCNessuna valutazione finora
- Pre-Commissioning & Commissioning of Card Access Control SystemDocumento3 paginePre-Commissioning & Commissioning of Card Access Control SystemKarim Amer100% (1)
- Abastecimiento de Agua y Alcantarillado - A. Regal Part 3 de 3Documento38 pagineAbastecimiento de Agua y Alcantarillado - A. Regal Part 3 de 3Walter Ortega Espinoza100% (1)
- ICT Input Output Devices 12Documento7 pagineICT Input Output Devices 12jasujunkNessuna valutazione finora
- 25P40VP STMicroelectronicsDocumento35 pagine25P40VP STMicroelectronicsJulio MartinezNessuna valutazione finora
- SCADAPack 6601 Hardware Manual PDFDocumento94 pagineSCADAPack 6601 Hardware Manual PDFMustapha AljameelNessuna valutazione finora
- 62543en1 PDFDocumento519 pagine62543en1 PDFroshan lal100% (1)
- Lab 1 Input, Processing, and OutputDocumento8 pagineLab 1 Input, Processing, and OutputGhost BKNessuna valutazione finora
- Computer Fundamentals TutorialDocumento93 pagineComputer Fundamentals TutorialJoy MaryNessuna valutazione finora
- Introduction To OsDocumento34 pagineIntroduction To OsAman E.Nessuna valutazione finora
- Part 6: String ManipulationDocumento58 paginePart 6: String ManipulationSummer Festival HONOLULUNessuna valutazione finora
- WASD VP3 User Manual: DescriptionDocumento4 pagineWASD VP3 User Manual: DescriptionGrant ParkNessuna valutazione finora
- Troubleshooting Failure To Reach I/O Status A7: GE Power Systems Training and DevelopmentDocumento15 pagineTroubleshooting Failure To Reach I/O Status A7: GE Power Systems Training and DevelopmentIsmail Djeghoubbi100% (1)
- CyPro User Manual v47Documento65 pagineCyPro User Manual v47mehifa7514Nessuna valutazione finora
- 2-Wire Serial EEPROM Smart Card Module: FeaturesDocumento12 pagine2-Wire Serial EEPROM Smart Card Module: FeaturesMaikol DominguezNessuna valutazione finora
- 8018 Operation Manual Rev CB EnglishDocumento122 pagine8018 Operation Manual Rev CB EnglishDritan Bakaj67% (3)
- Profibus On The QUICC Engine Block: Application NoteDocumento24 pagineProfibus On The QUICC Engine Block: Application NoteSaasiNessuna valutazione finora
- K Pos Compact DP or Joystick ControllerDocumento2 pagineK Pos Compact DP or Joystick ControllereajNessuna valutazione finora
- SEPM ReportDocumento65 pagineSEPM ReportAkshay GuptaNessuna valutazione finora