Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
ISACA - Rethinking-Data-Governance-and-Data-Management - WHP - Eng - 0220
Caricato da
Marco Antonio Salcedo HuarcayaTitolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
ISACA - Rethinking-Data-Governance-and-Data-Management - WHP - Eng - 0220
Caricato da
Marco Antonio Salcedo HuarcayaCopyright:
Formati disponibili
G O V E R N A N C E
RETHINKING
D ATA G O V E R N A N C E
AND MANAGEMENT
A Practical Approach for Data-Driven Enterprises
Personal Copy of Marco Salcedo (ISACA ID: 876747)
2 RETHINKING DATA GOVERNANCE AND MANAGEMENT
CONTENTS
4 The Business and Its Data 18 / Ad hoc Data Quality Issue
4 Data Governance: Common Challenges Management
5 A Hypothetical Case Study 18 / Work on Data Cleansing Against the
6 / A Practical Data Governance and Data Standard
Management Strategy 19 Stage 4. Realize Data Democratization
6 Stage 1. Establish a Data Governance 19 Stage 5. Focus on Data Analytics
Foundation 19 / Overview
7 / WHAT—Data Classification and Data 20 / Prototyping of Data Analytics
Taxonomy Capability
8 / WHEN—The Data Life Cycle and 20 / Develop Data Services for Business
Mapping with Data Governance Activities Purposes
10 / WHO—The Data Governance 20 / Create Data Labels for Better Use of
Structure and Data Stewardship The Data
12 / HOW — Data Governance Policies 20 / Data Visualization and Storytelling
and Standards for Better Business Results
13 Stage 2. Establish and Evolve the Data 21 / Value Comes from Business Insights
Architecture by Using the Data
13 / Data Standardization Requirements 21 Conclusion
14 / Data Models to be Standardized 22 Appendix A: Data Stewardship—Three
15 / Establish and Standardize Metadata Key Roles
and Master Data 22 / Data Owner
16 / Publish and Apply the Data 22 / Data Steward
Standards 23 / Data Custodian
16 Stage 3. Define, Execute, Assure Data 23 Appendix B: Mapping to COBIT 2019
Quality and Clean Polluted Data 23 Appendix C: Mapping to DMM 2.0
16 / Good Metadata Strategy Leads to 24 Appendix D: Mapping to DAMA-DMBOK
Good Data Quality 2.0
16 / Define Data Quality Criteria 25 Suggestions for Further Reading
17 / Execute Data Quality 26 Acknowledgments
18 / Regular Data Quality Assessment
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
3 RETHINKING DATA GOVERNANCE AND MANAGEMENT
ABSTRACT
It is never too late for any enterprise to start a data governance program, but it cannot be
successful without a sound implementation strategy that is fully aligned with the
enterprise business objectives.
This white paper uses a hypothetical use case to propose an approach for data
governance and standardization, and improved strategic planning and decision making
for data-driven digital transformation.
This white paper offers focused guidance on the following topics:
• Data governance foundation
• Data architecture
• Data quality and data cleansing
• Data democratization
• Data analytics
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
4 RETHINKING DATA GOVERNANCE AND MANAGEMENT
The Business and Its Data
Many enterprises strive to realize the potential value of the supports decision making. In China, a recent hot topic is
data they possess or that can legally be obtained from the business middle-platform and data middle-platform
outside sources. For example, digital retailers use data for architecture approach to data governance, which was
precision marketing, and city management uses data to introduced by Alibaba.3 This approach recognizes the
3
dynamically optimize traffic controls. Harnessing data important relationship that is established between two
effectively can bring new value to businesses in the form paradigms: the business paradigm, which can benefit
of improved strategic planning and decision making. from data insights, and the data paradigm, which accrues
from and shapes the business.4 This architecture allows
4
According to McKinsey & Company, data governance is a
Alibaba to gain data insights that powers the business to
key enabler when an enterprise begins the kind of data
be a differentiator and helps to ensure that the business
transformation that is necessary to use big data and
creates, analyzes and consumes premium-quality data.
advanced analytics for competitive differentiation.1 1
FIGURE 1: Reciprocal Relationship Between the Business and
McKinsey & Company states, “Before embarking on digital
Data
transformation, data governance needs to be developed
and embedded throughout the process. Leaders need to
BUSINESS CONTEXTS
clarify the policies and standards required to ensure
effective data management, and they must define Business transactions leave data tracks.
dedicated roles and responsibilities across the
organization.”2 2
BUSINESS DATA
It is meaningful to rethink the relationship between the
business and data in the context of digital transformation Data insights support business decisions.
(figure 1). In the modern digital environment, all business
transactions or activities leave data tracks. The method in The architecture approach is supported by the growing
which the business intends to use the data ultimately understanding of the important inter-relationship between
provides the mechanism to describe the purpose of the business and data. This white paper does not include a
data. Conversely, the data created while conducting detailed discussion on the definition and details of this
business has its own intended business purpose, which architecture, but the concept is important to understand.
Data Governance: Common Challenges
Although the importance of data governance and management • Enterprises often cannot easily perceive the value of data
has been emphasized, many enterprises still face challenges in governance, which results in a lack of management
commitment, because the benefits are difficult to quantify.
this area. Some common challenges include:
1
1
“Getting your data house in order.,” July 2018, https://www.mckinsey.com/industries/consumer-packaged-goods/our-insights/digital-and-analytics-in-
consumer/capabilities/getting-your-data-house-in-order
2
2
Ibid.
3
3
Alibaba is a leader in data governance practices globally and especially in China. They developed the business middle-platform and data middle-
platform architecture approach. The business uses data and data must be managed in business context.
4
4
Zhong Hua; (Enterprise IT Architecture Transformation Approach: Alibaba’s Strategy and
Philosophy in Middle-platform and its Architecture Practices), Alibaba, China, 2017
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
5 RETHINKING DATA GOVERNANCE AND MANAGEMENT
• Data ownership is often not clearly defined due to the • Data deluge can result in quality problems. Big data is of no
misconception that data management is technical work and, value if it cannot be harnessed for better business decision
therefore, the responsibility of the IT department. making. Effective decisions cannot be made based on poor-
• Marketing or other departments can obtain the data needed by quality data. In addition, more complex and unstructured data
their business units without considering the costs or risk are being introduced, which can strain data governance efforts.
associated with using the data. • Lack of skilled staff to conduct data analysis creates a barrier to
• Evolving regulatory requirements impact data governance. The effective data governance. A good working knowledge of data
number of data-related regulations is trending upward (e.g., analytics becomes critical to the success of an enterprise. The
California Consumer Privacy Act [CCPA], General Data best resources should be able to identify hidden patterns and
Protection Regulation [GDPR] on privacy protection and China unknown correlations, draw conclusions, make inferences and
Cybersecurity Law on data localization). The lack of a clear data predict future trends.
governance structure makes it harder to respond to emerging or
To address these challenges, successful enterprises can
changing international data laws.
employ a phased, multistage approach to data
• Enterprises often identify a need for workflow changes, which has
management, with a well-designed data governance
an impact on enterprise architecture. Opportunities to standardize,
foundation, appropriately implemented data architecture,
interoperate and re-architect current processes and systems must
be taken. Proper change management, data protection and data quality and data cleansing efforts, and data analytics
executive sponsorship are necessary to make data governance a that improve decision making. In addition, strong data
reality, particularly in heavily regulated environments. security and privacy processes bolster the overall data
• Siloed department and organizational structures result in management approach by helping to reduce risk that is
disaggregated datasets and data analytics challenges. introduced when these challenges go unaddressed.
A Hypothetical Case Study
Zero Attitude, Inc. (ZA) has a global footprint and grew from FIGURE 2: A Hypothetical Data Governance Approach
acquisitions made over the past several years, which has
resulted in a hybrid of system and data environments.5 As a 5
result, ZA operates in various jurisdictions and currently uses
a variety of data sources and datasets. Different Different
jurisdictions business
ZA designs and produces consumer products (busines-to- units
consumer) and intermediate products to other enterprises
(business-to-business). ZA defined aggressive digital Zero
Attitude, Inc.
transformation goals to grow its business. ZA executives
have committed to the investment, knowing IT must play
an important role in achieving these goals. One of the
foundational objectives is to make better use of data to
support business decision making. This case study
focuses on helping ZA design and deploy an effective data Different data sources and datasets
governance and management program (figure 2).
5
5
It was difficult to find a case that included all aspects of data governance, so this hypothetical case study is based upon several real-life enterprises.
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
6 RETHINKING DATA GOVERNANCE AND MANAGEMENT
A Practical Data Governance internal/external data provider management) should be
considered and aligned at each of the five stages. Since
and Management Strategy the scope of work with ZA is focused on establishing a
There is no one-size-fits-all strategy for developing a data foundation for data governance and data architecture to
governance program. For ZA, a two-phase process is proposed enable data analytics and data sciences, data security,
to achieve its objectives, using a practical data framework. privacy and operations are not covered in this case study.
First, ZA will establish a data governance framework and
Various data management frameworks or disciplines may
subsequently cleanse the data against quality standards. Next,
have unique requirements for each of these stages, which
ZA will implement a data management platform, which
can be tailored based on the enterprise (see Appendices B
provides better insights for business decision making.
through D for more information). In addition, it can be
Five adoption stages are to be executed across the two difficult to depict the interdependencies of each stage
phases (figure 3). As these stages are completed, they will linearly, so ZA executives are advised to expect these
serve to mature the program in each phase.6 These five 6
stages of adoption to follow a natural, sequential logic
stages continuously turn raw data into business value. with some degree of interaction. For example, data
governance cannot be successfully achieved if data
Data security, privacy and operations (including
quality requirements are not considered early.
requirements definition, data life cycle management, and
FIGURE 3: Data Governance and Management Strategy: Five Stages of Adoption
Phase 1—Design and Deploy a Data Governance Strategy
Stage 1. Establish a data governance foundation to define beneficial data uses and the legal requirements of using that data.
Stage 2: Establish and evolve the data architecture.
Stage 3: Define, execute and assure data quality, and conduct data cleansing.
Phase 2—Implement a Data Management Platform
Stage 4: Realize data democratization.
Stage 5: Focus on data analytics.
Stage 1. Establish a Data
Governance Foundation
A good data governance foundation sets the groundwork collection also need to be understood. For example, the
to collect and use data. This foundation includes enterprise can employ mechanisms that include culture,
addressing legal, business intellectual property and roles and responsibilities, organizational structure, skills
customer sensitivity considerations. Laws and regulations and knowledge, and performance measures.7 7
require that certain data are not collected or stored, and The ZA executive leadership team expects that the
that data use and storage are well controlled. Customer following benefits will be achieved with the
sensitivity to collection and storage and difficulty in implementation of the data governance structure:
6
6
Here we referred to Huawei and some other organizations’ data governance practices: phase 1 – establish a data governance foundation, realize data
cleansing, improve the accuracy of financial statements, interoperate with business flows; and phase 2 – implement a data pedestal, provide data
services, support the digital transformation.
7
7
ISACA; COBIT® 2019 Framework: Governance and Management Objectives, USA, 2019, https://www.isaca.org/COBIT/Pages/COBIT-2019-Framework-
Governance-and-Management-Objectives.aspx
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
7 RETHINKING DATA GOVERNANCE AND MANAGEMENT
• Manage data as an asset and capture value from the data. location data, electronic identifiers or one or more specific
• Define data ownership, stewardship and roles and elements of the physical, physiological, genetic, mental,
responsibilities. economic, cultural or social identity of that natural
• Implement data governance as a practice area that will mature person.10 Data can be categorized using any taxonomy
10
over time. as long as it does not conflict with the principles of the
The holistic data governance foundation to be designed GDPR (e.g., biometric, health and/or genetic data).
for ZA should answer four questions: Consideration should be made regarding the safety of the
data, because the same data, after being processed will
1. What data does ZA have and need to use?
generate information that ZA will use to profile their
• The data classification and data taxonomy need to be
customers.11 11
defined.
2. When are data governance practices taking place through the Because ZA is a multinational enterprise, compliance with
ZA data life cycle? ISO/IEC 27001: Information Security Management, ISO/IEC
• A consistent data life cycle model, mapped to data 27002:2013: Information technology—Security
management activities, needs to be tailored to ZA. techniques—Code of practice for information security
3. Who is responsible for ZA governance? controls and ISO 27701:2019: Security techniques—
• A data governance structure, accountability and Extension to ISO/IEC 27001 and ISO/IEC 27002 for privacy
responsibility of ownership, stewardship, and information management—Requirements and guidelines is
custodianship roles need to be defined. advised to help ensure that ZA data are secure according
4. How will data be managed in ZA? to its taxonomy. GDPR requires data subjects to take the
• Data management policies, standards for implementation, effective and necessary measures to ensure data security
and required technology and metrics need to be through its Article 32, Security in Treatment. An example
documented. of data classification and taxonomy is shown in figure 4.
WHAT—Data Classification and FIGURE 4: Illustrative Data Classification/Taxonomy
Data Taxonomy Data taxonomy
Defining the taxonomy, the amount of data collected and the
classification of the information is extremely important for
ZA to consider to ensure that it is in compliance with the
MANUFACTURING DATA
applicable laws and regulations of the countries in which it
operates. Data classification8 is important from a security
8
and privacy perspective, because it identifies sensitive and
confidential data categories to promote effective data PRODUCT DATA
protection requirements. The data taxonomy provides
enterprisewide data categories and hierarchy, which lay HR DATA
down a foundation for defining the business glossary and
FINANCIAL DATA
the data dictionary.9 9
According to GDPR, personal data refers to information
relating to an identified or identifiable natural person (data Data
subject). A natural person is an individual who can be classification
Public Internal Confidential Sensitive
identified, directly or indirectly, in particular by reference to
an identifier, such as a name, identification number,
,
8
8
Data classification is commonly known in information security management as the process of organizing data assets.
9
9
Data scientists or academics may prefer “business terminology” or “data dictionary.” Easy-to-understand terms were intentionally chosen for business
background professionals and IT generalists.
10
10
European Commission; “What is considered personal data under the EU GDPR?” https://gdpr.eu/eu-gdpr-personal-data/
11
11
Additional resources that may assist ZA in ensuring the safety and correct use of data include NIST Special Publication 800-37, Guide for Applying the
Risk Management Framework to Federal Information Systems: A Security Life Cycle Approach, https://csrc.nist.gov/publications/detail/
sp/800-37/ rev-1/archive/2014-06-05, and NIST Special Publication 800-53: National Vulnerability Database, https://nvd.nist.gov/800-53..
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
8 RETHINKING DATA GOVERNANCE AND MANAGEMENT
WHEN—The Data Life Cycle and enterprises and cannot be easily elaborated using one
common model. Enterprises need to define their own data
Mapping with Data Governance governance activities and these activities must be
Activities addressed at each stage of the data life cycle (figure 6).
The data life cycle provides a high-level overview of the Figure 7 illustrates a possible mapping between ZA’s data
steps involved in the successful management and life cycle and key security/privacy management activities.
preservation of data for use/reuse. The proposed data life
cycle for ZA is based on the model described in COBIT 5: ZA should look at all stages of the data collection process
Enabling Processes (figure 5). and describe a model of the type of data that it is collecting.
Security requirements are required to ensure data
FIGURE 5: The Data Life Cycle Model confidentiality, integrity and availability, according to data
usage. For example, data used in application development
should follow principles, such as privacy by design and by
PLAN/ default. A framework that validates data from the point of its
DESIGN collection, transformation, analysis and reporting ensures
that data do not contain information that can identify or be
ARCHIVE/ BUILD/ used against customers. To ensure confidentiality,
DESTROY ACQUIRE
development environments should mask production data
during validation and apply privacy-by-design and privacy-by-
default principles.
ZA must take the necessary measures to ensure data
SHARE STORE
storage security, such as data encryption through hash
tables, K-Anonymity systems and using encrypted and
mostly separate databases using pointers (i.e., the name
USE
is not in the same table as the address, credit card
number or tax document, etc.).
Source: Adapted from ISACA, COBIT 5: Enabling Information, USA, 2013
Subcontractors must also adopt security measures for the
ZA needs to standardize its data life cycle model across storage of data to help ensure that they are not accessed by
all business functions to ensure that a single taxonomy is or transferred to third parties. For guidance, ZA can refer to
consistently followed and defined, to create insights and NIST 800-37, NIST 800-57, ISO 27001 and GDPR.
value for the business. The activities vary across
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
9 RETHINKING DATA GOVERNANCE AND MANAGEMENT
FIGURE 6: Data Life Cycle Mapping with Data Governance Activities
ARCHIVE/
PLAN/DESIGN BUILD/ACQUIRE STORE USE SHARE
DESTROY
Data architecture
Data quality
Data democratization
Data analytics and visualization
Security and privacy
FIGURE 7: Data Life Cycle Mapping with Security/Privacy Management Activities
ARCHIVE/
PLAN/DESIGN BUILD/ACQUIRE STORE USE SHARE
DESTROY
Monitor and Ensure compliance
Identify security/ Implement data
Validate data control data with laws/ Data wiping
privacy requirements protection
access regulations
Implement
Identify data
data-retention
classification rules
Design security/
privacy framework
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
10 RETHINKING DATA GOVERNANCE AND MANAGEMENT
WHO—The Data Governance joint data governance structure to review and approve
data governance initiatives, and resolve outstanding
Structure and Data Stewardship issues, especially for data quality (figure 8). Then they
used the data governance meetings/committees to
The ZA data governance structure should be created to
prioritize data-related decisions. According to COBIT,12
align business priorities across the enterprise to increase
such a governance structure provides a regular meeting
trust in data. Inconsistent business process definition and
cadence for evaluating, directing and monitoring data
misalignment across various business units adversely
governance activities. This governance structure ensures
impacts data. For ZA, a history of acquisitions resulted in
that ZA data assets are complete and accurate, and are
inconsistent business processes and varying datasets. As
compliant with ZA data governance policies, processes
a result, the ZA main business and IT department installed a
and applicable standards.
FIGURE 8: Data Governance and Data Management Model (Based on the COBIT Core Model)
DATA GOVERNANCE
Evaluate
Direct Monitor
DATA MANAGEMENT ACTIVITIES
APO14.01 Define and communicate the organization’s data management strategy and roles and responsibilities.
APO14.02 Define and maintain a consistent business glossary.
APO14.03 Establish the processes and infrastructure for metadata management.
APO14.04 Define a data quality strategy.
APO14.05 Establish data profiling methodologies, processes and tools.
APO14.06 Ensure a data quality assessment approach.
APO14.07 Define the data cleansing approach.
APO14.08 Manage the life cycle of data assets.
APO14.09 Support data archiving and retention.
APO14.10 Manage data backup and restore arrangements.
Next, ZA established a data stewardship structure that for data management activities. An example of a
provided a central point of contact for data knowledge, suggested RACI chart and conceptual data stewardship
visibility, accessibility and services. A good data structure are shown in figure 9 and figure 10. The roles in
stewardship structure defines roles and responsibilities the figures are not intended to be all-inclusive.
12
Op cit ISACA, COBIT 2019 Framework: Governance and Management Objectives
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
11 RETHINKING DATA GOVERNANCE AND MANAGEMENT
FIGURE 9: Data Stewardship Structure–A Conceptual Model (Part 1)
LIFE CYCLE DATA DATA DATA
ACTIVITIES ...
PHASE OWNER STEWARD CUSTODIAN
Identify security/privacy
Plan/Design A R R
requirements
Determine data
Plan/Design A R I
classification
Design security/privacy
Plan/Design A C R
framework
Validate data Build/Acquire C A/R C
Implement data protection Store A R R
Implement data retention
Store A C R
rules
Monitor and control data
Use C R A/R
access
Ensure compliance with
Share A R R
laws and regulations
Data wiping Archive/Destroy I C A/R
FIGURE 10: Data stewardship structure–A Conceptual Model (Part 2)
VIEW 1: DATA STEWARDSHIP VIEW 2: DATA USE
DATA OWNER(S) DATA REGULATORS
Decisions Regulation Regulation
DATA STEWARDS(S) Data
DATA PRODUCERS DATA USERS
Support
DATA CUSTODIAN(S)
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
12 RETHINKING DATA GOVERNANCE AND MANAGEMENT
FIGURE 11: Data Stewardship Cycle–A Conceptional Model
HOW—Data Governance
Policies and Standards
Step 5: The data Step 1: New
A risk assessment is a helpful step to take for data
steward approves dataset is identified
governance and helps to identify the technology gaps, who can access by the stakeholder.
which address the security element in the data, as the new dataset.
detailed in COBIT 5: Enabling Information.13 It is also
12
critical to identify the regulations and laws that require
Step 4: Data classification Step 2: Identify the
certain controls to be incorporated into the data
and categories are data owner, data
governance approach, such as GDPR. After these are identified and documented steward and
determined, ZA should look at the technology elements, along with associated data custodian.
business process(es).
the ability to collect data through the system or data
warehouse, etc. The output of this analysis are data
Step 3: Data steward and
governance policies, which include data stewardship, data
data custodian assess
quality, security/privacy, data architecture, etc. the proposed new dataset
against data classification
The data governance processes should be tightly based and data taxonomy.
on IT tools. For example, marketing or other business
units may introduce external datasets or data sources Step 6: The data steward reviews
and improves data quality.
with dynamic data at ZA. In this situation, the following
data stewardship steps (figure 11) should be taken:
• Step 1: The stakeholder (producer, user, or anyone else) Step 7: Data governance compliance is monitored.
identifies new datasets.
• Step 2: The data owner, data steward, and data custodian are
identified. Some key considerations to this governance process are:
• Step 3: The data steward and data custodian assess the 1. Ensuring that taxonomy and classification align with those
proposed new dataset against the data classification and the previously defined by the enterprise
data taxonomy. 2. Identifying the actors responsible for data storage, data
• Step 4: Data classification and category are identified, processing and data classification
documented and associated. 3. Storing and processing data access and classifying the new
• Step 5: The data steward approves who can access the new data according to the taxonomy defined by the enterprise
dataset. 4. Allotting sufficient time for the enterprise to document the new
• Step 6: The data steward reviews and improves data quality. data according to taxonomy and classification
• Step 7: Data governance compliance is monitored. 5. Defining access rules according to NIST 800-53 and ISO 27001
and creating a properly documented CRUD (create, read, update
and delete) matrix
6. Reviewing and correcting the data as necessary, so they can be
put in place
7. Establishing governance, risk and compliance (GRC) processes
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
13 RETHINKING DATA GOVERNANCE AND MANAGEMENT
Stage 2. Establish and Evolve the
Data Architecture
According to The Open Group Architecture Framework Without a proper definition of the desired data
(TOGAF), data architecture is a description of the structure architecture, it is unclear as to what ZA should do in
and interaction of the major types and sources of data, logical regard to achieving systems, processes and data
data assets, physical data assets and data management optimization and consolidation. Data cleansing terms
resources of the enterprise.14 Stage 2 discusses the data
13
are used here to highlight the focus on data itself.
standardization considerations that are important in the However, system re-architecting, integration and
establishment and evolution of the data architecture. optimization should also be considered. According
to TOGAF15 , there are five tactics to achieve
14
architecture optimization:
Data Standardization
• Re-platform: Migration of systems/data to virtualized or a cloud
Requirements platform without significantly changing the business features
ZA has a lot of polluted data that may inhibit its ability to and functions
properly analyze the data. To cleanse the data, ZA must • Refactor: Code optimization to improve the run-time efficiency
first standardize the data rules. This stage can be time of an application
consuming because there are many areas to consider • Replace: Provide a framework to replace existing
when establishing data rules. Data rules should include systems/datasets with standard ones
data modeling, master data management, data dictionary, • Retire: Decommission legacy systems, historical data from
etc., but should be customized to meet the needs of the current architecture landscape
enterprise. Careful consideration must be given to this • Re-architect: Extracting business objects from current systems
step, because it is cheaper to define good rules at the and using to develop new ones
beginning than to have to make changes later. ZA must
ZA will see two main benefits after this new data
analyze this standardization effort from a cost-benefit
architecture is established — standardized data
perspective and should start with the most critical
management for the future and cleansed datasets for the
systems and datasets so as not to spend time in areas
historical data.
where value will not be derived.
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
14 RETHINKING DATA GOVERNANCE AND MANAGEMENT
Data Models to be Standardized ZA starts with conceptual modeling, which refers to the
industrial data reference model for the data encoding
Data objects encompass entities and attributes. They are
standard. There is a range of choices for industries on the
different relationships among the entities. ZA uses data
data reference model, such as the ARTS reference
object populations to group different data objects, and it
model16 for the retail industry. The reference model
15
uses subject areas to group different entities. Data
provides a standard means by which data may be
modeling schemes assume data object populations are
described, categorized and shared.17 These are reflected
16
strictly disjoined, which means an individual member of a
within the three standardization areas of the data
data object population cannot be a member of another
reference model:
one. However, this is not always true; for example, a
1. Data context: Facilitates the discovery of data through an
Person can be Employee, Customer and Stakeholder.
approach to the categorization of data according to taxonomies,
In terms of data modeling, ZA identifies three distinct and enables the definition of authoritative data assets within a
levels (figure 12): community of interest.
• Conceptual—This is the highest level, encompassing the 2. Data description: Provides a means to uniformly describe data,
enterprisewide or business functions view of ZA and the thereby supporting its discovery and sharing.
abstract model(s) that target the business architecture layer. 3. Data sharing: Supports the access and exchange of data where
• Logical—This level adds details to the conceptual level, free of access consists of ad hoc requests (such as a query of a data
physical implementation details, which do not contribute to the asset), and exchange consists of fixed, re-occurring transactions
use of the logical level, and targets the application architecture between parties.
layer.
Data sharing is enabled by capabilities provided by data
• Physical—This level addresses how data are going to be
context and data description. For details of data modeling
encoded and stored in a database (e.g., SQL and NoSQL), and
and design, refer to the Data Management Body of
deals with processing performance (denormalization of the
Knowledge V2.18 17
database) and its partitioning and distribution (e.g., cloud
storage), which targets the technology architecture layer.
For ZA, the inputs to data modeling are (figure 13):
• As-is and To-be business processes
FIGURE 12: Data Modeling Across Enterprise Architecture • Redundant data objects existing among current business
applications
• Data objects from manual business processing without
BUSINESS CONCEPTUAL applications’ support
ARCHITECTURE MODELING • Data objects to be added for future business requirements
• Available common data reference model for ZA
LOGICAL The outputs from data modeling are:
APPLICATION
ARCHITECTURE MODELING • Data map (enterprisewide key data entities)
• The mapping of business process model (BPM) and data map
• Data models
TECHNOLOGY PHYSICAL
ARCHITECTURE MODELING
DATA ARCHITECTURE
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
15 RETHINKING DATA GOVERNANCE AND MANAGEMENT
FIGURE 13: Mapping Relationship Between the Business Process Model and the Data Map
INPUTS INPUTS INPUTS DATA MAP
DATA ENTITY
BUSINESS BUSINESS BUSINESS
DATA ENTITY
PROCESS PROCESS PROCESS
(LEVEL X) (LEVEL X) (LEVEL X)
DATA ENTITY
DATA ENTITY
OUTPUTS OUTPUTS OUTPUTS
Data quality management entails the establishment and Master data are the core data needed to uniquely define
deployment of roles, responsibilities, policies and objects (e.g., Customer, Partner, Supplier, Person, Product
procedures concerning the acquisition, maintenance, or Service, Ledger and Asset). It is infrequently changed
dissemination and disposition of data. and is often referenced by business processes and
associated with other data types. Data sharing is why the
Establish and Standardize master data exists. Metadata are data that describe
various facets of data assets to improve its usability
Metadata and Master Data throughout the data life cycle.
The data map can be divided into five categories:
common master data; domain master data; transaction Benefits from implementing master data management
data; summary data, which is dedicated for Business include:
Intelligence (BI); and metadata (figure 14). • Enhanced data sharing across business lines
FIGURE 14: Data Map, Master Data and Metadata • Centralized single source of key data for item definition and
enrichment
• Improved item setup workflows, transparency in status and
COMMON MASTER DATA
approval process
• Agility to support new business models
Domain 1 Domain 2 Domain 3 Domain n • Enhanced capabilities to support global growth
master data master data master data master data
• Process consolidation to improve cycle time and go-to-market
time
... • Hierarchy management and association with items
Customer master data serve as the single source of key data
Domain 1 Domain 2 Domain 3 Domain n
transaction transaction transaction
about ZA’s customers. It validates and enhances internal
transaction
data data data data data with external sources to provide the most precise
customer view. It assigns customers to the right customer
hierarchy using the name provided on the customer record.
SUMMARY DATA Customer name inputs are validated against a repository of
standardized company names furnished by trusted external
METADATA
data providers. It should also be checked against the up-to-
date customer’s legal entities.
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
16 RETHINKING DATA GOVERNANCE AND MANAGEMENT
FIGURE 15: Data Dictionary Structure
Publish and Apply the Data
Standards Data encoding
Data classification
Data taxonomy
standard
The data dictionary is created based on already developed Master data
data taxonomy, business terminology and data models. It Conceptual
models
is a central repository where detailed data definitions can
be found as the single source of trust. The data dictionary Logical
Metadata
models
varies in its components across organizations, but it is
commonly agreed that the data dictionary is the Physical ...
... models ...
cornerstone for data standardization (figure 15).
DATA STANDARD SCOPE
Stage 3. Define, Execute, Assure
Data Quality and Clean Polluted Data
After the standards around data classification and taxonomy • Manage metadata repositories
are established, ZA can build on that foundation by • Distribute metadata
developing and executing a solid metadata strategy. • Query, report and analyze metadata
• Data sensitivity in metadata
Good Metadata Strategy Leads In most cases, the metadata strategy focuses on the data
warehouse or data lake because it is where the most data
to Good Data Quality
needs to be shared. The development of a data
Metadata is closely related to data quality. Metadata
warehouse/data lake helps reduce the amount of
summarizes basic data about data, which can make
metadata to be managed, which removes the complexity
finding and working with particular instances of data
and narrows the work scope.
easier. Author, date created, date modified and file size are
examples of basic ZA document metadata. Having the
ability to filter through that metadata makes it much Define Data Quality Criteria
easier for someone to locate a specific document.
Following COBIT, a well-developed data quality model19 18
A good metadata strategy includes the following: defines three main quality criteria and 15 subcriteria. For
• Understand metadata requirements ZA, four criteria are prioritized: accuracy, completeness,
• Define the metadata architecture currency and consistent representation (figure 16):
• Define and maintain metadata standards • Accuracy: Does the data reflect the dataset or data standard?
• Implement a managed metadata environment Check for specified value(s) to examine the degree to which the
• Create and maintain metadata data mirror the characteristics of the real-world object or
• Integrate metadata objects it represents.
19
18
We used aspects from both COBIT® 5: Enabling Information and COBIT 2019.
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
17 RETHINKING DATA GOVERNANCE AND MANAGEMENT
• Completeness: Are all datasets and data items recorded? Do • Consistent representation: Can the dataset be matched across
the attributes associated with the measure contain the data stores? Is a data attribute used consistently in the system
expected valid values? Are the attributes complete, meaning do of record, or can it have multiple meanings in the system of
they contain values or are there NULL values in the data set? record? Are the data used as intended in external applications,
• Currency: Are the data available from the required point in time or does is it have a different meaning externally?
according to defined service level agreement?
FIGURE 16: Quality Model
INTRINSIC CONTEXTUAL SECURITY/ACCESSIBILITY
Consistent Availability
Accuracy Relevancy
representation
Objectivity Completeness Interpretability Restricted Access
Believability Currency Understandability
Appropriate Easy of
Reputation
amount manipulation
Concise
representation
Selected as prioritized data-quality criteria
Source: Adapted from ISACA, COBIT 5: Enabling Information, USA, 2013
Data quality criteria and the thresholds are selected based • Business analyst: conveys the business requirements, including
on the business context, requirements, levels of risk, etc. detailed data quality requirements. In addition, the business
Each dimension is likely to have a different weighting in analyst reflects the requirements in the data models and the
requirements for new dataset acquisition processes.
order to obtain an accurate data quality measure.
• Project manager: is responsible for the program or individual
projects and ensures that the program/project is consistent with
Execute Data Quality data quality requirements during system design, development and
implementation. The project manager sets the tone with respect to
ZA business and IT parties should jointly manage the data
data quality and interacts with data stewards to establish
quality on an ongoing basis. The business parties are
program/project level data quality requirements.
responsible for establishing the business rules that govern
the data and are ultimately responsible for verifying the A successful data quality program has both proactive and
data quality. IT is responsible for establishing and reactive components. The proactive components diminish
managing the technical environment. the potential for new problems to arise, and the reactive
components address problems that already exist. That
Key data quality roles and responsibilities include: is why a regular meeting cadence should be set up to
• Data steward: is responsible for managing data as a corporate report and discuss data quality issues at the data
asset. stewardship level.
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
18 RETHINKING DATA GOVERNANCE AND MANAGEMENT
Regular Data Quality • Formalize an approach for identifying data quality expectations
and defining data quality rules against which the data can be
Assessment validated.
Data quality issues can be identified and resolved as part • Have individuals/teams identified to support the data quality
of an ongoing assessment program. A regular measurement and improvement and define the RACI for
assessment program helps to ensure that data clean up ongoing maintenance of the quality.
efforts stay evergreen. A typical data quality assessment • Baseline the levels of data quality and provide a mechanism to
approach includes the following steps: identify leakages as well as analyze root causes of data failures.
1. Identify the data owner(s) for the data items.
2. Work with the data owner(s) to identify which data items are Work on Data Cleansing Against
deemed critical and need to be assessed for data quality.
3. Establish business thresholds identified by the data
the Data Standard
After finalizing the data standard, the biggest challenge is
owners/users.
full implementation of the data standard. A possible
4. Assess which data quality aspects to be used and their
approach for data cleansing follows:
associated weighting.
5. Define data quality assurance rules. • At the business/data architecture layer, business processes and
6. Define values or ranges representing good and bad quality data, terminology need to be updated, reflecting the defined
for each data quality aspect. standards.
7. Define and agree on quality assessment results reporting. • At the application/data architecture layer, data encoding, data
8. Apply the assessment criteria to the data items. models, master data and metadata standards need to be built
9. Review the results and determine if data quality is acceptable or into application systems. Possible integration opportunities
not based on the above-established business thresholds. need to be reviewed and considered. Use extract, transform,
10. Take corrective actions, such as cleaning the data and and load (ETL) to integrate different data sources with the data
improving data handling processes to prevent future warehouse or data lake to form a basis for data ingestion
recurrences. prepared for subsequent data analytics.
11. Repeat the above steps on a periodic basis to monitor trends in • At the technology/data architecture layer, ensure data storage,
data quality. operations, and security/privacy are incorporated into re-
12. Make any needed update to business data requirements. architecting work.
Executive sponsorship and practical change management
Ad hoc Data Quality Issue strategies throughout the ZA organization are critical to
the success of the data cleansing efforts.
Management
To ensure that data quality issues do not negatively affect
the data architecture, it is necessary to:
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
19 RETHINKING DATA GOVERNANCE AND MANAGEMENT
Stage 4. Realize Data Democratization
During the ZA implementation, there is a lack of visibility ZA uses the platform to show to its data users:
into where datasets exist, what data objects exist, who • Object name
owns them and where they are located. Furthermore, it is • Title, Description
difficult to understand how to access them. This gap • Top users, Stewards
reduces the business productivity and decision-making • Quality flags/ Trust check
capability. Therefore, it is recommended that ZA create an • Tags, Article references
enterprisewide platform, where permitted users can • Listing of sub-object pages with contextual information21 20
access the data. This effort is called data
Individual data owners are established to create
democratization, which facilitates the sharing of data and
accountability for fulfilling best practices and maintaining
insights across the enterpreise, providing a single source
data catalog content. Data can be searched, providing
of reference to search curated data and data-related
self-service capabilities. Access to the catalog and user
expertise.20 It can be achieved through a data catalog
19
experience is persona driven.
platform built in-house or support by a purchased
commercial product. Data security and privacy is fundamental to data
democratization. Data democratization relies heavily on
ZA wants to use such a platform to achieve
the ability to secure data properly for end-user access. In
these objectives:
some cases, users are not allowed to see certain data.
• Enable the data users to easily search but with proper access to Another aspect is securing rows of data in the database
the trusted data for specific user groups. This requires the development of
• Enable a better understanding of the data in a related and more reporting solutions that only allow the users to see
friendly data format specific rows of data based on their credentials.22 21
Stage 5. Focus on Data Analytics
Overview patterns and unknown correlations, draw conclusions
and predict the likelihood of future events and
Data analytics adds much value to the business; for
trends. Data visualization is the graphical representation
example, a financial institution can leverage data analytics
of data by using visual elements. There are various
and data visualization in different capacities, from
data analytics and data visualization tools
targeted marketing for financial products to detecting
available in the market for an enterpriseto assist in
credit card fraud. Data analytics is used to examine
this area.
data and apply statistical methods to identify hidden
20
19
Marr, B.; “What Is Data Democratization? A Super Simple Explanation and the Key Pros and Cons,” Forbes, 24 July 2017,
https://www.forbes.com/sites/bernardmarr/2017/07/24/what-is-data-democratization-a-super-simple-explanation-and-the-key-pros-and-
cons/#646484476013
21
20
Alation, https://www.alation.com
22
21
Wilson, M.; “What to Consider When Building Your Data Democratization Strategy,” Ironside Group, January 15, 2019,
www.ironsidegroup.com/2019/01/15/what-to-consider-when-building-your-data-democratization-strategy/
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
20 RETHINKING DATA GOVERNANCE AND MANAGEMENT
The data analytics team works across multiple functions
Create Data Labels for Better
to accelerate business transformation powered by data-
driven decision making. It is a problem-solving capability
Use of The Data
that combines business, applied math and technologies. Data science drives diagnostic, predictive and prescriptive
projects working with structured and unstructured
There are three types of data analytics: descriptive,
datasets and leverages artificial intelligence (AI)/machine
diagnostic, predictive and prescriptive. Data analytics has
learning (ML) methods. It focuses on high-impact
an iterative cycle to seize the value. The main focus areas
business problems that deliver measurable value to the
of data analytics are:
enterprise and enable the acceleration towards a data-
• Descriptive statistics: Enables data-driven decision making with driven business.23 22
interactive data services
Typically, unlabeled data consists of samples of natural or
• Statistical modeling and AI: Enables business outcomes
human-created artifacts that can be obtained relatively
through diagnostic, predictive and prescriptive analytics
easily. Labeled data typically takes a set of unlabeled data
delivered at scale
and augments each piece with some sort of meaningful
label (or tag) that is somehow informative or desirable
Prototyping of Data Analytics to know.
Capability
Labels are often obtained by asking humans to make
Prototyping delivers a quick impact assessment proof-of-
judgments about a given piece of unlabeled data. After
concept for targeted use cases. This enables measurable
obtaining a labeled dataset, ML models can be applied to
business impacts as well as scaled services to
the dataset.
operationalize decision support tools that leverage and
contribute to data analytics within the enterprise.
Data Visualization and
Develop Data Services for Storytelling for Better Business
Business Purposes Results
In business, a good story can grab people’s attention and
Data services deliver analytical solutions that impact the
makes it easier to inspire, motivate or persuade them.
critical needs of the enterprise. Standardization should be
Some considerations for using storytelling include:24
focused around delivering analytics at-scale using the latest
23
analytical paradigms (e.g., natural language 1. What is the business context? There are too much data, so the
processing/natural language generation) across all scope of data gathering needs to be narrowed down.
consumption channels. This also included developing and 2. Know your audience: what do they really care about?
deploying application programming interfaces (APIs) for other 3. Construct a story from your data and make an emotional
organization applications to consume analytics at-scale. connection between your story and the audience.
4. Visualize the story.
The data services can be requested through a process.
5. Tell a story with real examples; make impacts specific to solving
The business is requested to identify their data service
the audience’s problem(s) using everyday language.
requirements. Then the data analytics team
acknowledges the request and develops an appropriate
solution possibly through a data warehouse or data lake.
23
22
Google Cloud, “AI Platform Data Labeling Service,” 22 November 2019, https://cloud.google.com/data-labeling/docs/
24
23
Qlik International AB, 5 Steps for Effective Data Storytelling, 2017, https://www.qlik.com/us/-/media/files/resource-library/global-us/register/ebooks/eb-
5-steps-for-effective-data-storytelling-en.pdf
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
21 RETHINKING DATA GOVERNANCE AND MANAGEMENT
FIGURE 17: Data Maturity Model for Value-Based Decision
Value Comes from Business Making
Insights by Using the Data VALUE
Classifying the data in a business-oriented manner rather
Data visualization
than via taxonomy can improve data value. However, it is
important that there are sound criteria for classification, Labeled data
such as the mission criticality of the data. The value of
the data will always be measured in accordance with ZA Data services
business context. IT has several ways of providing value
Data analytics
to the business. Figure 17 shows the simple model
acknowledged in the ZA case. Data platform
Business intelligence (BI)
Security and privacy
Conclusion
Data are ubiquitous, making data governance a challenge. management are important for businesses that want to
Adopting many of the best practices employed by the make use of data to create value for their stakeholders
hypothetical enterprise highlighted in this white paper can while also minimizing risk. For an enterprise to gain
contribute to the success of any enterprise data meaningful insights from data, strong data governance
governance program. Data governance and data strategies and practices need to be in place.
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
22 RETHINKING DATA GOVERNANCE AND MANAGEMENT
Appendix A: Data Stewardship—
Three Key Roles
Data Owner data. Stewards facilitate consensus about data
definitions, quality and usage. Stewards guide the work
A data owner has the responsibility and related authority
needed to complete metadata, improve data quality,
to make decisions about data as well as its business
ensure regulatory compliance and ensure that data is fit
definitions. A good data owner knows the data, knows the
for the specific business purpose. Stewards are also
business, and understands the regulations and policies
responsible for making recommendations about data
related to the data. A data owner is primarily concerned
access security, distribution and retention to data owners
with value, risk, quality and utility of data. The data owner
and custodians.
should be a senior-level business role.
At the data steward level, the governance structure can be
At the data-owner level, the governance structure can be
named the tactical data governance committee, which
named the strategic data governance committee, which
serves as the tactical level focal point with accountability
serves as the strategic level focal point with accountability
and responsibility to drive process, data governance policy
for any given data subject. It is recommended to form this
and DOC recommendations in the respective business
committee with senior stakeholders coming from both
unit and/or cross-functionally. A data steward should be
business units and IT.
nominated and named for prioritized data domains. These
Key data owner responsibilities include: individuals are accountable for maintaining data quality
• Approves vision, objectives, strategies and data governance and have the decision rights to help people enforce
policies agreed-upon data governance policy. And these data
• Defines, documents and communicates data governance policies stewards should also work collaboratively on cross-
• Accountable for the data taxonomy and the definitions, data functional issues.
quality criteria, security and privacy
Key data steward responsibilities include:
• Accountable for policy compliance of the data subjects
• Provides governing body for organizationwide data subjects to
• Provides mandate and serves as the final authority in the
the other stakeholders, including data producers and
escalation chain
data users
• Provides organizationwide oversight of the data subjects
• Aligns each business unit with organizationwide unified data
• Reviews and analyzes available reporting regarding compliance
governance framework
with data governance policies
• Influences digital transformation and data services creation
• Reports data quality and data governance policy compliance
Data Steward • Assesses security/privacy
A data steward is an individual or group who ensure data • Identifies opportunities to improve data quality
assets are used and adopted properly. They serve as the • Provides change management of data governance policies
primary point of contact and understand the day-to-day • Monitors and controls data governance by using metrics and
use of a data domain as well as the value derived from the providing feedback
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
23 RETHINKING DATA GOVERNANCE AND MANAGEMENT
Data Custodian operational data governance committee, which serves as
the operational level focal point with accountability and
A data custodian is an individual or group who is
responsibility for IT tools.
responsible for ensuring the IT controls and safeguards
for the data, and providing guidance and insight into the Key data custodian responsibilities include:
technical environment, the structure of the data and the • Implements IT capabilities with applications, data tools and
architecture of the environment. Data custodians are the technologies to support data governance policy
visible, action-oriented engine of an information • Ensures the optimal and simplified IT architecture across the
governance effort. Data custodianship is ideally a organization
technical role. It is the primary point of responsibility, • Ensures availability, continuity, capacity and performance levels
accountability and activity for assessing, improving and and well-managed access
evaluating our critical data sources. At data custodian • Documents/logs all data handling activities
level, the governance structure can be named the • Assists in diagnosing data related issues and inquiries
Appendix B: Mapping to COBIT 2019
Rethinking Data Governance and Management COBIT 2019 Governance and Management Practices
1. Introduction APO14 - Managed Data
2. Data Governance Foundation APO14 - Managed Data
EDM01 - Ensured Governance Framework Setting and Maintenance
3. Data Standardization APO14 - Managed Data
APO03 - Managed Enterprise Architecture
4. Data Quality APO14 - Managed Data
APO11 - Managed Quality
5. Data Democratization BAI09 - Managed Assets
6. Data, Analytics & Visualization APO04 - Managed Innovation
7. Conclusion APO14 - Managed Data
Appendix C: Mapping to DMM 2.0
Rethinking Data Governance and Management DMM 2.0 Process Areas
1. Introduction
2. Data Governance Foundation Data Management Function
Governance Management
Data Requirements Definition
Data Life Cycle Management
3. Data Standardization Business Glossary
Meta-data Management
Data Cleansing
Architectural Approach
Architectural Standards
4. Data Quality Data Quality Strategy
Data Quality Assessment
5. Data Democratization Data Management Platform
6. Data, Analytics & Visualization
7. Conclusion Risk Management
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
24 RETHINKING DATA GOVERNANCE AND MANAGEMENT
Appendix D: Mapping to DAMA-DMBOK 2.0
Rethinking Data Governance and Management DMBOK 2.0 Knowledge Areas
1. Introduction Data Security
2. Data Governance Foundation Data Governance
3. Data Standardization Data Architecture
Data Modeling & Design
Reference & Master Data
Meta-Data
Data Integration & Interoperability
4. Data Quality Data Quality
5. Data Democratization
6. Data, Analytics & Visualization
7. Conclusion
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
25
Suggestions for Further Reading
ARTS, “ARTS Data Model Version 7.3,” 1 December 2016, Eve, Bob; “Data Preparation Plus Data Governance Equals
https://www.omg.org/retail-depository/arts-odm-73/ Better Analysis,” Cisco Blogs, 30 November 2015, https://
blogs.cisco.com/analytics-automation/data-preparation-
CEB Enterprise Architecture Leadership Council; Data
plus-data-governance-equals-better-analysis
Governance: Step-By-Step Guide, USA, 2015
ISACA; China Construction Bank;
CMMI Institute; Data Management Maturity (DMM) Model,
(IT Governance Best Practice in Banking Industry), USA,
USA, 2019
2019
DAMA International, Data Management Body of Knowledge
Morgan, Lisa; “3 Data Governance Challenges Today’s
(DMBOK) Version 2. USA, 2017
Companies Face,” Information Week, 21 March 2017,
“Data Democratization,” www.informationweek.com/big-data/3-data-governance-
www.techopedia.com/definition/32637/data- challenges-todays-companies-face/a/d-id/1328449
democratization
Import. io, “Data Discovery Explained” December 31, 2019,
European Commission; “Data Protection in the EU,” https://www.import.io/post/data-discovery-explained/
https://ec.europa.eu/info/law/law-topic/data-protection/
data-protection-eu_en
Personal Copy of Marco Salcedo (ISACA ID: 876747)
26 RETHINKING DATA GOVERNANCE AND MANAGEMENT
Acknowledgments
ISACA would like to acknowledge:
Lead Developer Expert Reviewers (cont.)
Guodong Zou Junlei Cai Kevin Schaaff
CGEIT, CRISC, CISA, CISM, CBRM, TOGAF CISA, CISM, CRISC, CGEIT, Cybersecurity CHMLA, PMP-ACP, ICP, LSSBB, CSQE
Certified, EBDP, PMP, PgMP, PfMP Audit, CIPT, CIPM, CISSP, ISO 27001 LA Principal Engineer
Manager & Sr. Consultant Vice President CMMI Institute, USA
Shanghai, China China International Fund Management
Beverly Thomas
Co, Ltd., China
CISA, CITP, CPA, CGMA, ISO9001
Expert Reviewers Daniel Ferreira Senior Manager
Mais Barouqa CISA, CISSP UMWA H&R, USA
CISA, CRISC, COBIT 5 FL, GRCP ITIL, ISO CEO
Kevin Wegryn
27001 LA PFCJ, Portugal
PMP, Security+, PfMP
Manager, IT Risk & Assurance Ping (Jack) Gao, Ph.D. Technology Operational Risk Manager
Deloitte & Touche, Jordan Director of DMM Program, Data Scientist Wells Fargo, USA
Veronique Barrotteaux Shanghai Data Exchange Corp, China
James Sun ZhenHua
PMP, CAMS, CSPO Ron Lear CISA, CIPM, CIPT
Operational Risk Consultant CHMLA, CMQ/OE Information Security and Compliance
Wells Fargo, USA Director of IP Development, Chief Manager
Architect Universal Beijing Theme Park and Resort,
CMMI Institute, USA China
Board of Directors
Brennan Baybeck, Chair Gabriela Reynaga Chris K. Dimitriadis, Ph.D.
CISA, CRISC, CISM, CISSP CISA, CRISC, COBIT 5 Foundation, GRCP ISACA Board Chair, 2015-2017
Oracle Corporation, USA Holistics GRC, Mexico CISA, CRISC, CISM
INTRALOT, Greece
Rolf von Roessing, Vice-Chair Gregory Touhill
CISA, CISM, CGEIT, CISSP, FBCI CISM, CISSP Greg Grocholski
FORFA Consulting AG, Switzerland Cyxtera Federal Group, USA ISACA Board Chair, 2012-2013
CISA
Tracey Dedrick Asaf Weisberg
Saudi Basic Industries Corporation, USA
Former Chief Risk Officer with Hudson CISA, CRISC, CISM, CGEIT
City Bancorp, USA introSight Ltd., Israel David Samuelson
Pam Nigro Chief Executive Officer, ISACA, USA
Rob Clyde
CISA, CRISC, CGEIT, CRMA ISACA Board Chair, 2018-2019
Health Care Service Corporation, USA CISM
R.V. Raghu Board Director, Titus and Executive Chair,
White Cloud Security, USA
CISA, CRISC
Versatilist Consulting India Pvt. Ltd., India
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
27 RETHINKING DATA GOVERNANCE AND MANAGEMENT
About ISACA
For more than 50 years, ISACA® (www.isaca.org) has advanced the best
1700 E. Golf Road, Suite 400
talent, expertise and learning in technology. ISACA equips individuals with
Schaumburg, IL 60173, USA
knowledge, credentials, education and community to progress their careers
and transform their organizations, and enables enterprises to train and build
Phone: +1.847.660.5505
quality teams. ISACA is a global professional association and learning
organization that leverages the expertise of its 145,000 members who work in Fax: +1.847.253.1755
information security, governance, assurance, risk and privacy to drive
Support: support.isaca.org
innovation through technology. It has a presence in 188 countries, including
more than 220 chapters worldwide. Website: www.isaca.org
DISCLAIMER
ISACA has designed and created Rethinking Data Governance and
Management: A Practical Approach for Data-Driven Organizations (the “Work”) Provide Feedback:
primarily as an educational resource for professionals. ISACA makes no claim www.isaca.org/rethinking-data-
governance
that use of any of the Work will assure a successful outcome. The Work
should not be considered inclusive of all proper information, procedures and Participate in the ISACA Online
tests or exclusive of other information, procedures and tests that are Forums:
reasonably directed to obtaining the same results. In determining the propriety https://engage.isaca.org/onlineforums
of any specific information, procedure or test, professionals should apply their Twitter:
www.twitter.com/ISACANews
own professional judgment to the specific circumstances presented by the
particular systems or information technology environment. LinkedIn:
www.linkedin.com/company/
isaca
RESERVATION OF RIGHTS Facebook:
www.facebook.com/ISACAGlobal
© 2020 ISACA. All rights reserved.
Instagram:
www.instagram.com/isacanews/
Rethinking Data Governance and Management: A Practical Approach for Data-Driven Organizations
© 2020 ISACA. All Rights Reserved.
Personal Copy of Marco Salcedo (ISACA ID: 876747)
Potrebbero piacerti anche
- Data Management Complete Study GuideDocumento122 pagineData Management Complete Study GuiderajeshOtwani100% (5)
- Data Governance PlaybookDocumento168 pagineData Governance PlaybookVinh Tran100% (13)
- DAMA DMBOK2 Framework V2 20140317 FINAL PDFDocumento27 pagineDAMA DMBOK2 Framework V2 20140317 FINAL PDFingetakuya100% (4)
- DAMA-DMBOK: Data Management Body of Knowledge: 2nd Edition - Management Information SystemsDocumento6 pagineDAMA-DMBOK: Data Management Body of Knowledge: 2nd Edition - Management Information Systemsgufaxite0% (6)
- MDM and Data GovernanceDocumento66 pagineMDM and Data Governancejramki100% (4)
- Data Governance ToolkitDocumento29 pagineData Governance Toolkitjakpyke100% (6)
- The IBM Data Governance Unified Process: Driving Business Value with IBM Software and Best PracticesDa EverandThe IBM Data Governance Unified Process: Driving Business Value with IBM Software and Best PracticesValutazione: 4 su 5 stelle4/5 (1)
- Dama Phoenix Dmbok2Documento50 pagineDama Phoenix Dmbok2breakscutum0% (1)
- Data Governance. A Handy Book For LaymansDocumento63 pagineData Governance. A Handy Book For LaymansSaad Khan88% (8)
- IBM - Data Governance Council - Maturity ModelDocumento16 pagineIBM - Data Governance Council - Maturity Modelajulien100% (3)
- Enterprise Data Management Data Governance PlanDocumento36 pagineEnterprise Data Management Data Governance PlanSujin Prabhakar89% (9)
- PwC Data Governance FrameworkDocumento3 paginePwC Data Governance FrameworkVictor Ho100% (6)
- Sas Data Governance Framework 107325Documento12 pagineSas Data Governance Framework 107325Daniel Softjoy MontjoyNessuna valutazione finora
- Data Governance Plan PDFDocumento36 pagineData Governance Plan PDFSuresh Suresetti100% (2)
- Data Governance CharterDocumento3 pagineData Governance Charterenrilei100% (2)
- CDMP Study Group: Session 7 - Data Management Capability Maturity ModelsDocumento25 pagineCDMP Study Group: Session 7 - Data Management Capability Maturity ModelsprogisNessuna valutazione finora
- Data Management: THE CookbookDocumento33 pagineData Management: THE CookbookRobert Waters100% (5)
- BCBS239 - A Roadmap For Data Governance - 04202016Documento40 pagineBCBS239 - A Roadmap For Data Governance - 04202016sgjathar100% (3)
- Data Governance Maturity Model Assessment ToolsDocumento20 pagineData Governance Maturity Model Assessment ToolsAdi Nakamura100% (4)
- Role of Data GovernanceDocumento12 pagineRole of Data GovernanceAlberto HayekNessuna valutazione finora
- Data Governance A Business Value-Driven ApproachDocumento16 pagineData Governance A Business Value-Driven ApproachLuis BarriosNessuna valutazione finora
- Data Strategy TemplateDocumento18 pagineData Strategy TemplateGuillermo Solis50% (2)
- Adley@dmadvisors - Co.uk: Christopher Bradley VP Professional DevelopmentDocumento28 pagineAdley@dmadvisors - Co.uk: Christopher Bradley VP Professional DevelopmentJovo50% (2)
- Sell Digital ProductsDocumento6 pagineSell Digital ProductsJohn CenaNessuna valutazione finora
- Data Governance Stewardship EbookDocumento15 pagineData Governance Stewardship EbookAjay Kumar100% (1)
- The Data Governance Maturity ModelDocumento11 pagineThe Data Governance Maturity ModelSaranik MahapatraNessuna valutazione finora
- OCIO DBHIDS Data Governance Framework Strategic Plan v2Documento65 pagineOCIO DBHIDS Data Governance Framework Strategic Plan v2rosalina paramitaNessuna valutazione finora
- Business Metadata: Capturing Enterprise KnowledgeDa EverandBusiness Metadata: Capturing Enterprise KnowledgeValutazione: 4 su 5 stelle4/5 (3)
- Data Quality: Empowering Businesses with Analytics and AIDa EverandData Quality: Empowering Businesses with Analytics and AINessuna valutazione finora
- Data Governance Best PracticesDocumento50 pagineData Governance Best Practicesmboya2100% (1)
- Leading Practices for Strategic Data GovernanceDocumento4 pagineLeading Practices for Strategic Data GovernanceAbrahamNdewingo100% (1)
- Data Governance Keystone of Information Management InitiativesDocumento102 pagineData Governance Keystone of Information Management InitiativesAlan McSweeney100% (2)
- Fds Data Governance PlaybookDocumento14 pagineFds Data Governance PlaybookJohannes Eagle100% (1)
- DAMA Data Governance 90 Min PDFDocumento58 pagineDAMA Data Governance 90 Min PDFJack Danields67% (3)
- Creating An Enterprise Data Strategy - FinalDocumento42 pagineCreating An Enterprise Data Strategy - Finalconsultunnikrishnan1850100% (1)
- Data Governance Ebook FinalDocumento56 pagineData Governance Ebook FinalTodd Henley100% (2)
- Alation Data Governance Methodology OverviewDocumento11 pagineAlation Data Governance Methodology Overviewho_siew_teng100% (3)
- Understanding Data GovernanceDocumento28 pagineUnderstanding Data GovernanceJoe leninja100% (1)
- Data GovernanceDocumento15 pagineData Governanceuma.madhav8841Nessuna valutazione finora
- Data Governance Checklist - 0Documento5 pagineData Governance Checklist - 0Muhammad Ammad100% (1)
- Data Governance: Building A Framework For MDMDocumento27 pagineData Governance: Building A Framework For MDMdesijnk86% (7)
- Dmbok2keynotev Phpapp02Documento51 pagineDmbok2keynotev Phpapp02rockogt0% (1)
- How To Become A: Data Governance ExpertDocumento18 pagineHow To Become A: Data Governance Expertrutger mcgeekNessuna valutazione finora
- Data Governance WorkbookDocumento36 pagineData Governance WorkbookEvrim AY100% (1)
- DG Expert Ebook2019 V1 2 2Documento39 pagineDG Expert Ebook2019 V1 2 2salimmanzur100% (4)
- Data GovernanceDocumento7 pagineData GovernancesamydogNessuna valutazione finora
- Tactical Vs Strategic Data GovernanceDocumento32 pagineTactical Vs Strategic Data GovernanceFirst San Francisco Partners100% (4)
- Data Governance Your Number One PriorityDocumento15 pagineData Governance Your Number One Priority1enterprisearchitectNessuna valutazione finora
- Whitepaper 7steps To Data GovernanceDocumento16 pagineWhitepaper 7steps To Data GovernancejramkiNessuna valutazione finora
- Data Audit Approach To Developing An Enterprise Data StrategyDocumento66 pagineData Audit Approach To Developing An Enterprise Data StrategyAlan McSweeneyNessuna valutazione finora
- TDWI Checklist Modern Data GovernanceDocumento12 pagineTDWI Checklist Modern Data GovernanceMarcelo CousillasNessuna valutazione finora
- CDMPDocumento33 pagineCDMPharishkode100% (2)
- Implementing A Data Governance Program - Chalker 2014 PDFDocumento22 pagineImplementing A Data Governance Program - Chalker 2014 PDFChristen Castillo100% (2)
- Data Governance vs. Data Management - Principles, Processes and Frameworks ExplainedDocumento8 pagineData Governance vs. Data Management - Principles, Processes and Frameworks Explainedjose albertNessuna valutazione finora
- CDMP Study Group Next Steps and Exam QuestionsDocumento13 pagineCDMP Study Group Next Steps and Exam QuestionsdoanhieuneuNessuna valutazione finora
- Data Governance The Way ForwardDocumento41 pagineData Governance The Way ForwardC. Plummer100% (1)
- An Introduction To Data StrategyDocumento8 pagineAn Introduction To Data StrategyLuis Lopez100% (3)
- Best Practices For Data QualityDocumento37 pagineBest Practices For Data QualityFrancois de Villiers100% (1)
- Revistas-Indexadas - Otras DisciplinasDocumento45 pagineRevistas-Indexadas - Otras DisciplinasMarco Antonio Salcedo HuarcayaNessuna valutazione finora
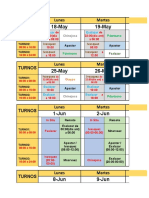
- Horario OPERACIONES - SEDAPALDocumento15 pagineHorario OPERACIONES - SEDAPALMarco Antonio Salcedo HuarcayaNessuna valutazione finora
- Preview ISO+IEC+27032-2012 PDFDocumento6 paginePreview ISO+IEC+27032-2012 PDFMarco Antonio Salcedo HuarcayaNessuna valutazione finora
- Preview ISO+IEC+27032-2012 PDFDocumento6 paginePreview ISO+IEC+27032-2012 PDFMarco Antonio Salcedo HuarcayaNessuna valutazione finora
- Shifts in The: Low Touch EconomyDocumento35 pagineShifts in The: Low Touch EconomyGabriel HayonNessuna valutazione finora
- TOGAF 9.1 QuickstartDocumento53 pagineTOGAF 9.1 QuickstartstrikerjaxNessuna valutazione finora
- LinkDocumento1 paginaLinkMarco Antonio Salcedo HuarcayaNessuna valutazione finora
- White Paper Togaf 9 Itil v3 Sept09Documento16 pagineWhite Paper Togaf 9 Itil v3 Sept09Felipe Alzate RoldanNessuna valutazione finora
- c5g Controller UnitDocumento254 paginec5g Controller UnitElyNessuna valutazione finora
- Solving LCM HCF Remainder ProblemsDocumento10 pagineSolving LCM HCF Remainder ProblemshadhaiNessuna valutazione finora
- Data Science Batch 8 PDFDocumento19 pagineData Science Batch 8 PDFAhmad FajarNessuna valutazione finora
- EPM Data Sync With FDMEE 11.1.2.4Documento11 pagineEPM Data Sync With FDMEE 11.1.2.4Aravind AllamNessuna valutazione finora
- Carel Pco - SeriesDocumento84 pagineCarel Pco - SeriesAli Bin SaeedNessuna valutazione finora
- An Efficient Approach of Taking Quick and Simple Notes in The Air Through Smart Note TakerDocumento9 pagineAn Efficient Approach of Taking Quick and Simple Notes in The Air Through Smart Note TakerRoney George100% (1)
- Question Total Quality ManagementDocumento4 pagineQuestion Total Quality ManagementAztvNessuna valutazione finora
- Sandip University: End Semester Examinations-June 2021Documento1 paginaSandip University: End Semester Examinations-June 2021Industrial Training Institute ITI,SilvassaNessuna valutazione finora
- Advanced SAS Interview Questions You'll Most Likely Be AskedDocumento27 pagineAdvanced SAS Interview Questions You'll Most Likely Be AskedVibrant PublishersNessuna valutazione finora
- AZ - D361BC00001 Evening Diary eCOA Handheld ScreenshotsDocumento4 pagineAZ - D361BC00001 Evening Diary eCOA Handheld ScreenshotsIslam TahaNessuna valutazione finora
- Rais12 SM CH17Documento23 pagineRais12 SM CH17Anton VitaliNessuna valutazione finora
- Literature Review of Online Registration SystemDocumento8 pagineLiterature Review of Online Registration Systemzepewib1k0w3100% (1)
- Mock - 3sDocumento20 pagineMock - 3sPichuRangerNessuna valutazione finora
- LIT1126 ACT20M Datasheet 03 14Documento16 pagineLIT1126 ACT20M Datasheet 03 14alltheloveintheworldNessuna valutazione finora
- Maintenance Manual: MANUAL NUMBER 006-15545-0002 REVISION 2, December, 1999Documento181 pagineMaintenance Manual: MANUAL NUMBER 006-15545-0002 REVISION 2, December, 1999AndrewNessuna valutazione finora
- CSS 10-Summative TEST 1Documento4 pagineCSS 10-Summative TEST 1herbert reblora100% (1)
- SM-A260F Common Tshoo 7 PDFDocumento24 pagineSM-A260F Common Tshoo 7 PDFRamíro ChocotecóNessuna valutazione finora
- FSP150-50LE Is An Industrial Level of Switching Power Supply - SpecificationDocumento1 paginaFSP150-50LE Is An Industrial Level of Switching Power Supply - SpecificationJohn HallowsNessuna valutazione finora
- Hangzhou Silan Microelectronics SD6861 - C87751Documento12 pagineHangzhou Silan Microelectronics SD6861 - C87751youcef88Nessuna valutazione finora
- Winsteps ManualDocumento615 pagineWinsteps Manualandresote33100% (1)
- RSRed DS RS200L Mod v5Documento2 pagineRSRed DS RS200L Mod v5liebherrmanNessuna valutazione finora
- Winfiol CommandDocumento18 pagineWinfiol Commandhjk6500Nessuna valutazione finora
- Fourier Series: Yi Cheng Cal Poly PomonaDocumento46 pagineFourier Series: Yi Cheng Cal Poly PomonaJesusSQANessuna valutazione finora
- 0240813073Documento265 pagine0240813073Fundación Una Sola Mano Fsm100% (1)
- CCFL Inverter ZXDocumento26 pagineCCFL Inverter ZXcuzquilloNessuna valutazione finora
- Jazler VideoStar 2 User ManualDocumento28 pagineJazler VideoStar 2 User ManualARSENENessuna valutazione finora
- Database design fundamentalsDocumento19 pagineDatabase design fundamentalsArun Kumar T KNessuna valutazione finora
- Guidebook On Technologies For Disaster Preparedness and Mitigation ISRO Satyabrata SahuDocumento102 pagineGuidebook On Technologies For Disaster Preparedness and Mitigation ISRO Satyabrata SahuS.Alec KnowleNessuna valutazione finora
- Access Token Stealing On WindowsDocumento11 pagineAccess Token Stealing On Windows@4e4enNessuna valutazione finora