Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
IP Fragmentation With Examples
Caricato da
Nio Zi FengTitolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
IP Fragmentation With Examples
Caricato da
Nio Zi FengCopyright:
Formati disponibili
CW568-4 Computer Networks for Aircraft March 2020
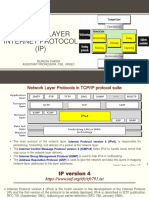
Internet Protocol (IP) version 4.0 Fragmentation and Reassembly
http://www.wildpackets.com/resources/compendium/tcp_ip/ip_fragmentation
The following is an explanation of the IP Fragmentation and Reassembly process used by IP
version 4.0. It will examine the purpose of IP Fragmentation, the relevant fields contained
within the IP Header and the role of Maximum Transmission Unit (MTU) in determining
when IP Fragmentation will be used.
As specified in RFC 791 (Internet Protocol - DARPA Internet Program Protocol
Specification, Sept. 1981), the IP Fragmentation and Reassembly process occurs at the IP
layer and is transparent to the Upper Layer Protocols (ULP). As a block of data is prepared
for transmission, the sending or forwarding device examines the MTU for the network the
data is to be sent or forwarded across. If the size of the block of data is less than the MTU for
that Network, the data is transmitted in accordance with the rules for that particular network.
But what happens when the amount of data is greater than the MTU for the network? It is at
this point that one of the functions of the IP Layer, commonly referred to as Fragmentation
and Reassembly, will come into play.
Maximum Transmission Unit (MTU)
There are a number of different network transmission architectures, with each having a
physical limit of the number of data bytes that may be contained within a given frame. This
physical limit is described in numerous specifications and is referred to as the Maximum
Transmission Unit or MTU of the network. An example of such an MTU would be IEEE
802.3 Ethernet; according to the specifications, the maximum number of data bytes that can
be contained within a frame is 1500. The following table lists the MTU of several common
network types (from RFC 1191 - MTU Path Discovery, Nov 1990):
Network Architecture MTU in Bytes
802.3 Ethernet 1500
4 Mb Token Ring 4464
16 Mb Token Ring 17914
FDDI 4352
X.25 576
There are two principle situations in which MTU becomes important:
The first is when the size of the block of data being transmitted is greater than the MTU. An
example of this would be when data is being read using Sun's Network File System (NFS)
which reads data in 8-kilobyte blocks.
The second situation would arise when data must traverse across multiple network
architectures, each with a different MTU. Just such an example would be if the data
originated on a 16Mb Token Ring network (MTU = 17914 Bytes) that was connected to
another 16Mb Token Ring network (MTU = 17914 Bytes) via an Ethernet network (MTU =
1500 Bytes).
Regardless of which situation occurs, the rules that IP Fragmentation follows remain the
same and will be discussed later.
Keith Smyth Page 1 of 6
CW568-4 Computer Networks for Aircraft March 2020
IP version 4 Fragmentation Fields
Type of
Versio Header
Service or Total Length
n Length
Diffserv
Identifier X D M Fragment Offset
Time to Live Protocol Header Checksum
Source Address
Destination Address
Options Padding
IPv4 Header
The three fields concerned with IP Fragmentation are:
RFC 791 Field Name Size Other Reference Names
Identification 16 bit Identification Field
Flags 3 bit Fragmentation Flags
Fragmentation Offset 13 bit Fragment Offset
Identification - This 16-bit field contains a unique number used to identify the frame and any
associated fragments for reassembly.
Given the increasing complexity of networks, it is theoretically possible that fragments from
multiple blocks of data might travel along different paths to the destination, possibly arriving
out of sequence in relation to one another. That is, it is possible a fragment from block
number one might arrive intermixed with the data stream for block number 2 or vice versa.
While the function of the Fragment Offset Field is to identify the relative position of each
fragment, it is the Identification Field that serves to allow the receiving device to sort out
which fragments comprise what block of data. Each fragment from a particular data stream
will have the same Identification Field, thus uniquely identifying which block it belongs to. If
one or more fragments are lost, the buffer of the device performing the reassembly process
will time out and discard all of the fragments. In the event of such a time out, the data will
then have to be retransmitted by the sending device.
Flags - This 3-bit field contains the flags that specify the function of the frame in terms of
whether fragmentation has been employed, additional fragments are coming, or this is the
final fragment.
Bit Indicator RFC 791 Definition
0xx Reserved
x0x May Fragment
x1x Do Not Fragment
xx0 Last Fragment
xx1 More Fragments
Keith Smyth Page 2 of 6
CW568-4 Computer Networks for Aircraft March 2020
When a receiving station processes each frame, one of the operations it performs is to review
the Flags field. Depending on the value indicated by this field, several possible actions are
then initiated, including:
(xx1) More Fragments - Indicates that there are additional IP Fragments that comprise the
data associated with that specific Identification Field. The receiving device will allocate
buffer resources for reassembly and pass all frames containing that unique Identification
Field to the buffer.
(xx0) Last Fragment - Indicates that this fragment is the final frame for the data block
identified by the Identification Field. The receiving device will now attempt to reassemble the
fragments in the order specified by the Fragment Offset field.
Fragment Offset - This 13-bit field indicates the position of a particular fragment's data in
relation to the first byte of data (offset 0).
Because it is entirely possible that the fragments that comprise a block of data might travel
along different paths to the destination, it is possible they might arrive out of sequence. While
the Identification Field serve to mark which IP fragments belong to which block of data, it is
the Fragment Offset Field, sometimes referred to as the Fragmentation Offset Field, that tells
the receiving device which order to reassemble them in.
During the IP Fragmentation Reassembly process, if a particular fragment is found to be
missing, as indicated by the Fragmentation Offset count, the buffer will enter a wait state
until either the missing piece(s) are received or a time out occurs. In the event of such a time
out, the buffer simply discards the fragments.
IP Fragmentation and IP Fragmentation Reassembly Procedure
IP Fragmentation
Regardless of what situation occurs that requires IP Fragmentation, the procedure followed
by the device performing the fragmentation must be as follows:
The device attempting to transmit the block of data will first examine the Flag field to
see if the field is set to the value of (x0x or x1x). If the value is equal to (x1x) this
indicates that the data may not be fragmented, forcing the transmitting device to
discard that data. Depending on the specific configuration of the device, an Internet
Control Message Protocol (ICMP) Destination Unreachable -> Fragmentation
required and Do Not Fragment Bit Set message may be generated.
Assuming the flag field is set to (x0x), the device computes the number of fragments
required to transmit the amount of data in by dividing the amount of data by the
MTU. This will result in "X" number of frames with all but the final frame being
equal to the MTU for that network.
It will then create the required number of IP packets and copies the IP header into
each of these packets so that each packet will have the same identifying information,
including the Identification Field.
The Flag field in the first packet, and all subsequent packets except the final packet,
will be set to "More Fragments." The final packets Flag Field will instead be set to
"Last Fragment."
The Fragment Offset will be set for each packet to record the relative position of the
data contained within that packet.
The packets will then be transmitted according to the rules for that network
architecture.
Keith Smyth Page 3 of 6
CW568-4 Computer Networks for Aircraft March 2020
IP Fragment Reassembly
If a receiving device detects that IP Fragmentation has been employed, the procedure
followed by the device performing the Reassembly must be as follows:
The device receiving the data detects the Flag Field set to "More Fragments."
It will then examine all incoming packets for the same Identification number
contained in the packet.
It will store all of these identified fragments in a buffer in the sequence specified by
the Fragment Offset Field.
Once the final fragment, as indicated by the Flag Field, is set to "Last Fragment," the
device will attempt to reassemble that data in offset order.
If reassembly is successful, the packet is then sent to the ULP in accordance with the
rules for that device.
If reassembly is unsuccessful, perhaps due to one or more lost fragments, the device
will eventually time out and all of the fragments will be discarded.
The transmitting device will then have to attempt to retransmit the data in accordance
with its own procedures.
Security and IP Fragments
The IP version 4 Fragmentation and Reassembly process suffers from a particular weakness
that can be utilized to trigger a Denial of Service Attack (DOS). The receiving device will
attempt reassembly following receipt of a frame containing a Flag field set to (xx1),
indicating more fragments to follow. Recall that receipt of such a frame causes the receiving
device to allocate buffer resources for reassembly.
So what happens if a device is flooded with separate frames, each with the Flag field set to
(xx1), but each has the Identification Field set to a different value? According to the rules for
IP version 4 Fragmentation and Reassembly, the device would attempt to allocate resources
to each separate fragment in preparation for reassembly. However, given a flood of such
fragments, the receiving device would quickly exhaust its available resources while waiting
for buffer time-outs to occur. The result, of course, would be that possible valid fragments
would be lost or encounter insufficient resources to support reassembly. The common term
for this type of artificially induced shortage of resources is "Denial of Service Attack".
To defend against just such DOS attempts, many network security features now include
specific rules implemented at the Firewall that change the time-out value for how long they
will hold incoming fragments before discarding them.
Keith Smyth Page 4 of 6
CW568-4 Computer Networks for Aircraft March 2020
Example 1.
In the diagram below a PC is uploading a file to a server over a WAN connection. Assume
that the PC has a 1400 byte segment to send to the server.
The table attached shows the packet before and after fragmentation. Complete the highlighted
fields in the packets after fragmentation.
Keith Smyth Page 5 of 6
CW568-4 Computer Networks for Aircraft March 2020
Before fragmentation
Start of Header
Identifier = Z x 0 0 Offset = 0
Rest of Header
1400 bytes
After fragmentation
Packet 1
Start of Header
Identifier = x Offset =
Rest of Header
_____ bytes
Packet 2
Start of Header
Identifier = x Offset =
Rest of Header
_____ bytes
Packet 3
Start of Header
Identifier = x Offset =
Rest of Header
______ bytes
Packet 4
Start of Header
Identifier = x Offset =
Rest of Header
______ bytes
Keith Smyth Page 6 of 6
Potrebbero piacerti anche
- 2019 Book DataScienceAndBigDataAnalyticsDocumento418 pagine2019 Book DataScienceAndBigDataAnalyticsfrmalthus100% (6)
- All-In-One Devnet Associate Exam: Devasc Exam 200-901 V1.0 Cert GuideDocumento29 pagineAll-In-One Devnet Associate Exam: Devasc Exam 200-901 V1.0 Cert GuideJean Carlos MercadoNessuna valutazione finora
- Aricent Electrical Utility WhitepaperDocumento9 pagineAricent Electrical Utility Whitepaperap_venezuelaNessuna valutazione finora
- EASA 66 Module 8 Questions.Documento45 pagineEASA 66 Module 8 Questions.Nio Zi Feng88% (8)
- Computer NetworksDocumento21 pagineComputer NetworksAran UtkarshNessuna valutazione finora
- CAN System Engineering - From Theory To Practical ApplicationsDocumento375 pagineCAN System Engineering - From Theory To Practical ApplicationsFlavio Sajama100% (1)
- API Traffic Management 101Documento83 pagineAPI Traffic Management 101Andi Haidar Ali100% (2)
- Omnipeek GettingStartedDocumento85 pagineOmnipeek GettingStartedchris100% (1)
- HUAWEI UDM 21.3.0 PGW MML Command ProtocolDocumento1.056 pagineHUAWEI UDM 21.3.0 PGW MML Command ProtocolErvin Palencia100% (2)
- 03-HUAWEI Cloud Datacenter Sales Specialist Training V2.0Documento40 pagine03-HUAWEI Cloud Datacenter Sales Specialist Training V2.0Yasmine BoudhinaNessuna valutazione finora
- Network Layer - IP - MukeshDocumento19 pagineNetwork Layer - IP - MukeshMukesh100% (2)
- Assignment Cs349 WiresharkDocumento8 pagineAssignment Cs349 WiresharkRitvik SarafNessuna valutazione finora
- Winter 2012 Master of Computer Application (MCA) - Semester 6 MC0087 - Internetworking With TCP/IP - 4 Credits (60 Marks) 1. What Is Fragmentation? Explain Its SignificanceDocumento8 pagineWinter 2012 Master of Computer Application (MCA) - Semester 6 MC0087 - Internetworking With TCP/IP - 4 Credits (60 Marks) 1. What Is Fragmentation? Explain Its SignificancelifeofnameNessuna valutazione finora
- RARP: Reverse Address Resolution ProtocolDocumento8 pagineRARP: Reverse Address Resolution ProtocolMitchel Jammal SNessuna valutazione finora
- Network Viva Questions and AnswersDocumento29 pagineNetwork Viva Questions and AnswersAditya HebbarNessuna valutazione finora
- 6.7 Ipv4 Datagram: Presented By: Shubhangi DesaiDocumento23 pagine6.7 Ipv4 Datagram: Presented By: Shubhangi DesaiShubhangiNessuna valutazione finora
- Structure of Ethernet Frames: How Data is Organized for Network TransferDocumento3 pagineStructure of Ethernet Frames: How Data is Organized for Network TransferReyan RanaNessuna valutazione finora
- OSI Model ConceptsDocumento2 pagineOSI Model ConceptsAbhishek kapoorNessuna valutazione finora
- IP HeaderDocumento4 pagineIP HeaderNio Zi FengNessuna valutazione finora
- Internet Protocol - IP IP FeaturesDocumento9 pagineInternet Protocol - IP IP FeaturesDAHRAOUI Mohamed RiadNessuna valutazione finora
- INTERNETWORKING PROTOCOLSDocumento4 pagineINTERNETWORKING PROTOCOLSPrathana PhukonNessuna valutazione finora
- Network Viva Questions and AnswersDocumento29 pagineNetwork Viva Questions and Answersreshmaitagi50% (2)
- Unit-1 (Part 1) PDFDocumento36 pagineUnit-1 (Part 1) PDFPranjal NagarNessuna valutazione finora
- Networking NotesDocumento11 pagineNetworking NotesTest AletheNessuna valutazione finora
- SummaryDocumento14 pagineSummaryAbdullah MohammadNessuna valutazione finora
- TCP-IP Part-1Documento38 pagineTCP-IP Part-1Aadya SharmaNessuna valutazione finora
- The Internet NotesDocumento91 pagineThe Internet NotesTejas Raghavendra Bhat MNessuna valutazione finora
- Ieee 802.3,4,5Documento5 pagineIeee 802.3,4,5Sajan AntonyNessuna valutazione finora
- 2 Link Layer Technologies: T.O.P. Businessinteractive GMBH Page 1 of 18Documento18 pagine2 Link Layer Technologies: T.O.P. Businessinteractive GMBH Page 1 of 18Daniel CafuNessuna valutazione finora
- Packet Formats To RememberDocumento18 paginePacket Formats To RememberVansh MalikNessuna valutazione finora
- Pmtud IpfragDocumento30 paginePmtud IpfragVarisai Maideen Beevi JNessuna valutazione finora
- Presentation On TCP-IP VulnerabilitiesDocumento35 paginePresentation On TCP-IP Vulnerabilitiesmohit_kohli673988% (8)
- 1.5 Getting The Latest Version of This DocumentDocumento42 pagine1.5 Getting The Latest Version of This DocumentmusaNessuna valutazione finora
- Lecture 7Documento5 pagineLecture 7owronrawan74Nessuna valutazione finora
- ISO/OSI AND TCP/IP NETWORK MODELSDocumento3 pagineISO/OSI AND TCP/IP NETWORK MODELSPratik D. PatelNessuna valutazione finora
- Pmtud Ipfrag PDFDocumento25 paginePmtud Ipfrag PDFDenis SNessuna valutazione finora
- Gate Cse Notes: Joyoshish SahaDocumento21 pagineGate Cse Notes: Joyoshish SahaPavanNessuna valutazione finora
- IPv4 NetworkDocumento19 pagineIPv4 Networkbackbencher kiddoNessuna valutazione finora
- CSE-433 Computer Networks Mid Semester Examination 2020-21Documento8 pagineCSE-433 Computer Networks Mid Semester Examination 2020-21Kumar shivamNessuna valutazione finora
- IPv4 - Packet StructureDocumento2 pagineIPv4 - Packet StructureshivNessuna valutazione finora
- Pmtud IpfragDocumento26 paginePmtud IpfragYaroslav SinegubkinNessuna valutazione finora
- MODULE 10 - Routing Fundamentals and SubnetsDocumento6 pagineMODULE 10 - Routing Fundamentals and SubnetsGrecu GianiNessuna valutazione finora
- CN AssignmnetDocumento10 pagineCN AssignmnetPranava PranuNessuna valutazione finora
- Experiment4 A: Pysical LayerDocumento3 pagineExperiment4 A: Pysical LayerSALIM TADVINessuna valutazione finora
- Computer Networks Chapter 3Documento26 pagineComputer Networks Chapter 3bhavya gNessuna valutazione finora
- Ethernet Chapter: Protocols, Addressing, and SwitchingDocumento16 pagineEthernet Chapter: Protocols, Addressing, and SwitchingRafael SilveraNessuna valutazione finora
- Difference Between Segments, Packets & Frames 17.01.2024Documento2 pagineDifference Between Segments, Packets & Frames 17.01.2024aloishp36Nessuna valutazione finora
- Understanding IP Fragmentation. Fragmentation Occurs When An IP - by Gary Hoffman - PortUnreachableDocumento3 pagineUnderstanding IP Fragmentation. Fragmentation Occurs When An IP - by Gary Hoffman - PortUnreachableshivNessuna valutazione finora
- IPv4 Overview in 40 CharactersDocumento24 pagineIPv4 Overview in 40 CharactersusamaNessuna valutazione finora
- IPv4 - Packet Structure - TutorialspointDocumento2 pagineIPv4 - Packet Structure - Tutorialspointaisha SinghNessuna valutazione finora
- Packet Sniffer Project Document PDF FreeDocumento90 paginePacket Sniffer Project Document PDF FreeSurendra ChoudharyNessuna valutazione finora
- Ethernet Communication Frame FormatsDocumento2 pagineEthernet Communication Frame Formatsmrinalkanti392971Nessuna valutazione finora
- ProtocolsDocumento22 pagineProtocolssharkapproachNessuna valutazione finora
- IEEE Standards4Documento29 pagineIEEE Standards4Ruchi AgrawalNessuna valutazione finora
- Investigacion Modelo OSI, IP HeaderDocumento5 pagineInvestigacion Modelo OSI, IP HeaderKnowhereDLNessuna valutazione finora
- TCP Ip NotesDocumento14 pagineTCP Ip Notesjoshwaaa_hotmailcomNessuna valutazione finora
- 3.1.2 - IP Behavior I - FragmentationDocumento41 pagine3.1.2 - IP Behavior I - FragmentationClaudio StroeNessuna valutazione finora
- Network Layer Internet ProtocolDocumento23 pagineNetwork Layer Internet ProtocolCh Saqib ShabbirNessuna valutazione finora
- IP Datagram General FormatDocumento8 pagineIP Datagram General FormatNoorjahan BeegamNessuna valutazione finora
- Presentation On TCP-IP VulnerabilitiesDocumento34 paginePresentation On TCP-IP Vulnerabilitiesmohit_kohli6739100% (1)
- Computer Communication Networks CS-418: Lecture 8 - 1 Network Layer - Routing ProtocolsDocumento19 pagineComputer Communication Networks CS-418: Lecture 8 - 1 Network Layer - Routing ProtocolsAli MemonNessuna valutazione finora
- CIR 209 (Lecture 4f) OSI - ModelDocumento16 pagineCIR 209 (Lecture 4f) OSI - Modeldancanongori9Nessuna valutazione finora
- Physical Layer Data Link Layer: Logical Link Control (LLC) Media Access Control (MAC)Documento44 paginePhysical Layer Data Link Layer: Logical Link Control (LLC) Media Access Control (MAC)GauravNessuna valutazione finora
- Chapter 2Documento47 pagineChapter 2papiNessuna valutazione finora
- IPv4 - Quick GuideDocumento21 pagineIPv4 - Quick GuidemispanshieNessuna valutazione finora
- TCP IpDocumento206 pagineTCP IpSahil AhujaNessuna valutazione finora
- Unit-4: Iot Architecture and ProtocolsDocumento22 pagineUnit-4: Iot Architecture and ProtocolsMahesh ChauhanNessuna valutazione finora
- Introduction to Internet & Web Technology: Internet & Web TechnologyDa EverandIntroduction to Internet & Web Technology: Internet & Web TechnologyNessuna valutazione finora
- Airworthiness Directives PresentationDocumento4 pagineAirworthiness Directives PresentationNio Zi FengNessuna valutazione finora
- ShortcutsDocumento1 paginaShortcutsNio Zi FengNessuna valutazione finora
- 3D MAINTENANCE RESERVES 2019-20 Slides For BlackboardDocumento14 pagine3D MAINTENANCE RESERVES 2019-20 Slides For BlackboardNio Zi FengNessuna valutazione finora
- AVR Microcontroller Architecture - TechniCodesDocumento4 pagineAVR Microcontroller Architecture - TechniCodesNio Zi FengNessuna valutazione finora
- IP HeaderDocumento4 pagineIP HeaderNio Zi FengNessuna valutazione finora
- Commercial Pilot Licence (CPL) : Your Ticket To A Career in AviationDocumento18 pagineCommercial Pilot Licence (CPL) : Your Ticket To A Career in AviationNio Zi FengNessuna valutazione finora
- ICAO Aviation LegislationDocumento14 pagineICAO Aviation LegislationNio Zi FengNessuna valutazione finora
- Commercial Pilot Licence (CPL) : Your Ticket To A Career in AviationDocumento18 pagineCommercial Pilot Licence (CPL) : Your Ticket To A Career in AviationNio Zi FengNessuna valutazione finora
- Aircraft Leg DocumentsDocumento77 pagineAircraft Leg DocumentsNio Zi FengNessuna valutazione finora
- Commercial Pilot Licence (CPL) : Your Ticket To A Career in AviationDocumento18 pagineCommercial Pilot Licence (CPL) : Your Ticket To A Career in AviationNio Zi FengNessuna valutazione finora
- 18W Aviation Legislation Reading ListDocumento5 pagine18W Aviation Legislation Reading ListNio Zi FengNessuna valutazione finora
- X-Plane Installer LogDocumento14 pagineX-Plane Installer LogNio Zi FengNessuna valutazione finora
- Commercial Pilot Licence (CPL) : Your Ticket To A Career in AviationDocumento18 pagineCommercial Pilot Licence (CPL) : Your Ticket To A Career in AviationNio Zi FengNessuna valutazione finora
- Netflix RecommendationDocumento1 paginaNetflix RecommendationNio Zi FengNessuna valutazione finora
- Components LinkDocumento1 paginaComponents LinkNio Zi FengNessuna valutazione finora
- Conference Template A4Documento3 pagineConference Template A4anthonyNessuna valutazione finora
- Brake SystemDocumento2 pagineBrake SystemNio Zi FengNessuna valutazione finora
- Easa Oct 2014 ExamDocumento6 pagineEasa Oct 2014 ExamNio Zi FengNessuna valutazione finora
- Wifi IssueDocumento1 paginaWifi IssueNio Zi FengNessuna valutazione finora
- Ans - Rev QuestionDocumento36 pagineAns - Rev QuestionNio Zi FengNessuna valutazione finora
- Committee ChartDocumento1 paginaCommittee ChartNio Zi FengNessuna valutazione finora
- VCL 1400 PDFDocumento4 pagineVCL 1400 PDFJavier CuzcoNessuna valutazione finora
- Wifi ConfigurationDocumento5 pagineWifi ConfigurationGregor PurdieNessuna valutazione finora
- Set router/Wi-Fi/wireless Access Point/repeater ConfigurationDocumento13 pagineSet router/Wi-Fi/wireless Access Point/repeater ConfigurationNinja ni Zack PrimoNessuna valutazione finora
- Instructor Materials Chapter 2: Configure A Network Operating SystemDocumento20 pagineInstructor Materials Chapter 2: Configure A Network Operating SystemHoney ShineNessuna valutazione finora
- Arista Precision Data Analysis With DANZ WhitePaperDocumento11 pagineArista Precision Data Analysis With DANZ WhitePaperZekNessuna valutazione finora
- OPC Employee HandbookDocumento19 pagineOPC Employee HandbookhcopelandNessuna valutazione finora
- SSC600 ProdInt Pres 758993 ENaDocumento17 pagineSSC600 ProdInt Pres 758993 ENaVamanNessuna valutazione finora
- HD77 Installation Guide 1Documento36 pagineHD77 Installation Guide 1Ioan MirceaNessuna valutazione finora
- BioStar 2 Revision Notes for Version 2.7.5Documento16 pagineBioStar 2 Revision Notes for Version 2.7.5juioNessuna valutazione finora
- Introduction To Packet TracerDocumento13 pagineIntroduction To Packet TracerRJ GieNessuna valutazione finora
- TMP1700 600 DatasheetDocumento10 pagineTMP1700 600 DatasheetDianita Sarango NarváezNessuna valutazione finora
- ORPAK ForeFuel Brochure WBSTDocumento4 pagineORPAK ForeFuel Brochure WBSTdelson2206Nessuna valutazione finora
- h10741 VNX Data Movers WP PDFDocumento28 pagineh10741 VNX Data Movers WP PDFChristian CutaranNessuna valutazione finora
- Ip Address in Networking 1663653009231Documento7 pagineIp Address in Networking 1663653009231Jerry RoshanNessuna valutazione finora
- 3gpp 29214-g40Documento105 pagine3gpp 29214-g40miniscribdloginNessuna valutazione finora
- Understanding Networking Concepts and ProtocolsDocumento22 pagineUnderstanding Networking Concepts and ProtocolsVivek Kumar SinhaNessuna valutazione finora
- AI/ML and GCP developer tools cheat sheetDocumento1 paginaAI/ML and GCP developer tools cheat sheetArul Elvis JNessuna valutazione finora
- Axisware SYLK Manual: FactoryLink Driver For Square D SY/LINK ManualDocumento54 pagineAxisware SYLK Manual: FactoryLink Driver For Square D SY/LINK ManualAxisware LLCNessuna valutazione finora
- CH 01Documento8 pagineCH 01andrewiles88Nessuna valutazione finora
- Auditing Gray 2015 CH 8 System Work Basic Ideas 2Documento55 pagineAuditing Gray 2015 CH 8 System Work Basic Ideas 2Tyara LaraswatiNessuna valutazione finora
- Modbus Protocol UGDocumento33 pagineModbus Protocol UGMuhammad Sa'ad100% (1)
- Authentication Applications: Data and Network SecurityDocumento19 pagineAuthentication Applications: Data and Network SecurityasadNessuna valutazione finora