Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Store and Backup Files
Caricato da
nezclark0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
8 visualizzazioni2 pagineTitolo originale
Store and Backup Files.docx
Copyright
© © All Rights Reserved
Formati disponibili
DOCX, PDF, TXT o leggi online da Scribd
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
© All Rights Reserved
Formati disponibili
Scarica in formato DOCX, PDF, TXT o leggi online su Scribd
0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
8 visualizzazioni2 pagineStore and Backup Files
Caricato da
nezclarkCopyright:
© All Rights Reserved
Formati disponibili
Scarica in formato DOCX, PDF, TXT o leggi online su Scribd
Sei sulla pagina 1di 2
Store and Backup Files
Tens of researched papers have been published on related topics,
security research for CDS is still in its early stage. Here, we have
discussed the achievements in two research directions: secure
statistic CDS and secure dynamic CDS, from which our proposed
security framework benefits. In our work, we attempted to
provide a complete security service solution to secure the CDS.
To achieve our goal, we proposed MAS architecture for a security
service system that consists of five types of agents: User
Interface Agent (UIA), User Agent (UA), DER Agent (DERA), Data
Retrieval Agent (DRA) and Data Distribution Preparation Agent
(DDPA). UIA is acts as an effective bridge between the cloud user
and the rest of the agents. Such agents actively assist a user in
operating an interactive interface, recording the messages and
data shared among agents and serves as a data access point for
other agents, as well as cloud users.
DDPA is used to tolerate multiple failures in distributed storage
systems. In CDS, we rely on this agent to disperse the cloud data file
redundantly across a set of distributed servers. DRA is used to enable
the cloud user to reconstruct the original data by downloading the
cloud data vectors from the servers. UA is acts as a customer gateway
that makes features of MAS accessible to cloud users. It includes
responsibility of providing cloud users with real-time information of
entities residing in the MAS. UA also allows cloud users to control the
status of loads based on priority predefined by a cloud user. DERA is
responsible for storing associated DER information, DER information to
be stored may include DER identification number, type, local fuel
availability, cost function or price at which cloud users agree to sell,
as well as DER availability, more details in (Talib et al, 2010; Talib et
al, 2010). In (Wang et al., 2009), they investigated the problem of data
security in cloud data storage, which is essentially a distributed
storage system. To ensure the correctness of users’ data in cloud data
storage, they proposed an effective and flexible distributed scheme
with explicit dynamic data support, including block update, delete, and
append. They rely on erasure-correcting code in the file distribution
preparation to provide redundancy parity vectors and guarantee the
data dependability. By utilizing the homomorphic token with
distributed verification of erasure-coded data, their scheme achieves
the integration of storage correctness insurance and data error
localization, i.e.,
Potrebbero piacerti anche
- Manager ViewsDocumento2 pagineManager ViewsnezclarkNessuna valutazione finora
- Login User Type and Account SecurityDocumento1 paginaLogin User Type and Account SecuritynezclarkNessuna valutazione finora
- Restaurant ReportsDocumento2 pagineRestaurant ReportsnezclarkNessuna valutazione finora
- Food PromoDocumento3 pagineFood PromonezclarkNessuna valutazione finora
- Employee RecordsDocumento2 pagineEmployee RecordsnezclarkNessuna valutazione finora
- Manager Reshuffle EmployeeDocumento2 pagineManager Reshuffle EmployeenezclarkNessuna valutazione finora
- Receptionist ViewDocumento2 pagineReceptionist ViewnezclarkNessuna valutazione finora
- Admin ViewsDocumento2 pagineAdmin ViewsnezclarkNessuna valutazione finora
- User Forgot PasswordDocumento1 paginaUser Forgot PasswordnezclarkNessuna valutazione finora
- Front Desk ReportsDocumento1 paginaFront Desk ReportsnezclarkNessuna valutazione finora
- Manager Register EmployeeDocumento2 pagineManager Register EmployeenezclarkNessuna valutazione finora
- Restaurant Table inDocumento1 paginaRestaurant Table innezclarkNessuna valutazione finora
- User LoginDocumento1 paginaUser LoginnezclarkNessuna valutazione finora
- Front Desk Check in and Check OutDocumento1 paginaFront Desk Check in and Check OutnezclarkNessuna valutazione finora
- Manager Edit Employee InformationDocumento2 pagineManager Edit Employee InformationnezclarkNessuna valutazione finora
- Front Desk HousekeepingDocumento1 paginaFront Desk HousekeepingnezclarkNessuna valutazione finora
- Survey Questionnaires Were Followed As Part of Data Gathering Techniques and Data AnalysisDocumento1 paginaSurvey Questionnaires Were Followed As Part of Data Gathering Techniques and Data AnalysisnezclarkNessuna valutazione finora
- VermaDocumento1 paginaVermanezclarkNessuna valutazione finora
- Research InstrumentsDocumento2 pagineResearch InstrumentsnezclarkNessuna valutazione finora
- Through Detailed Security and Performance AnalysisDocumento1 paginaThrough Detailed Security and Performance AnalysisnezclarkNessuna valutazione finora
- Conceptual Framework of The StudyDocumento2 pagineConceptual Framework of The StudynezclarkNessuna valutazione finora
- This ProjectDocumento1 paginaThis ProjectnezclarkNessuna valutazione finora
- Through Detailed Security and Performance AnalysisDocumento1 paginaThrough Detailed Security and Performance AnalysisnezclarkNessuna valutazione finora
- Framework For Evaluation of Programming Language Examinations (2014) Recent Advancements in The Field of eDocumento2 pagineFramework For Evaluation of Programming Language Examinations (2014) Recent Advancements in The Field of enezclarkNessuna valutazione finora
- Manager Add and Remove Room PromoDocumento1 paginaManager Add and Remove Room PromonezclarkNessuna valutazione finora
- The Development ApproachDocumento1 paginaThe Development ApproachnezclarkNessuna valutazione finora
- Manager Add and Remove Food PromoDocumento1 paginaManager Add and Remove Food PromonezclarkNessuna valutazione finora
- Usability of Mobile Applications (2013) : Case Study of A Computer Based Examination System (2015)Documento2 pagineUsability of Mobile Applications (2013) : Case Study of A Computer Based Examination System (2015)nezclarkNessuna valutazione finora
- Manager Search Employee InformationDocumento1 paginaManager Search Employee InformationnezclarkNessuna valutazione finora
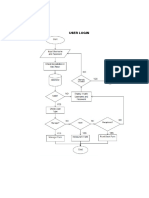
- Desgin PhaseDocumento1 paginaDesgin PhasenezclarkNessuna valutazione finora
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (400)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (266)
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (588)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (121)
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- Instructions: Dx100 OptionsDocumento29 pagineInstructions: Dx100 OptionsTran LeNessuna valutazione finora
- DEsign and Implementation of PID On FPGADocumento6 pagineDEsign and Implementation of PID On FPGAdhirendraNessuna valutazione finora
- 05st80 en 2012Documento612 pagine05st80 en 2012Vhsr Perfil UnoNessuna valutazione finora
- Wecon RtuDocumento16 pagineWecon RtuJoséAlexHuertasCastilloNessuna valutazione finora
- Fourth Quarterly Exam in Icf 8Documento2 pagineFourth Quarterly Exam in Icf 8Leewhy MacatimpagNessuna valutazione finora
- Microservice or Microservice ArchitectureDocumento3 pagineMicroservice or Microservice ArchitecturevicsukNessuna valutazione finora
- Hnas Pool and HDP Best PracticesDocumento29 pagineHnas Pool and HDP Best PracticesJugal ProhitNessuna valutazione finora
- Nagios For Windows - Nagwin Tutorial - 4sysopsDocumento10 pagineNagios For Windows - Nagwin Tutorial - 4sysopsAbdul GANessuna valutazione finora
- Cluster 4 TAP-Project - 25 09 2020 v1 3 - Checklist StudentDocumento21 pagineCluster 4 TAP-Project - 25 09 2020 v1 3 - Checklist StudentArthur InuguNessuna valutazione finora
- Airtel Information GuideDocumento3 pagineAirtel Information GuideRavi SoniNessuna valutazione finora
- Iot Based Doorbell Using Raspberry PiDocumento18 pagineIot Based Doorbell Using Raspberry PiSiri talasala100% (1)
- ENGLISHDocumento10 pagineENGLISHmarieNessuna valutazione finora
- Nokia Cloud Operations Manager - Data SheetDocumento3 pagineNokia Cloud Operations Manager - Data SheetChetan BhatNessuna valutazione finora
- Man Sys Sh-Asmm-2m-Asgg-2m Sen Ain v2Documento121 pagineMan Sys Sh-Asmm-2m-Asgg-2m Sen Ain v2Ali KaniNessuna valutazione finora
- Program Life Cycle: Steps To Follow in Writing or Creating A ProgramDocumento4 pagineProgram Life Cycle: Steps To Follow in Writing or Creating A ProgramPJ AranezNessuna valutazione finora
- W78E58B/W78E058B Data Sheet 8-Bit Microcontroller: Table of ContentsDocumento36 pagineW78E58B/W78E058B Data Sheet 8-Bit Microcontroller: Table of Contentskeyboard2014Nessuna valutazione finora
- Best Java IdeDocumento8 pagineBest Java IdePalak ParikhNessuna valutazione finora
- Software Quality Assurance Analyst Engineer in Austin TX Resume Erik StearnsDocumento5 pagineSoftware Quality Assurance Analyst Engineer in Austin TX Resume Erik StearnsErikStearnsNessuna valutazione finora
- Template 2Documento8 pagineTemplate 2Mhamad NasihNessuna valutazione finora
- 5 Lightweight Linux Distros Ideal For An Intel Atom Processor PCDocumento7 pagine5 Lightweight Linux Distros Ideal For An Intel Atom Processor PCDjordje DjoricNessuna valutazione finora
- Manual Versa ProDocumento309 pagineManual Versa ProFábio RibeiroNessuna valutazione finora
- Quick Start Manual Zeus 5.0Documento64 pagineQuick Start Manual Zeus 5.0comte6668991Nessuna valutazione finora
- Basic Network TroubleshootingDocumento9 pagineBasic Network TroubleshootingNeeraj Mishra50% (2)
- Dell XPS One 2720 Pegatron IPPLP-PL Rev 1.01Documento82 pagineDell XPS One 2720 Pegatron IPPLP-PL Rev 1.01Дамир АшеновNessuna valutazione finora
- Datastage - Basic Programming-1Documento37 pagineDatastage - Basic Programming-1sam2sung2Nessuna valutazione finora
- LogDocumento84 pagineLoghi manNessuna valutazione finora
- Logitech Rally Bar Mini: Data SheetDocumento4 pagineLogitech Rally Bar Mini: Data SheetraviezsoftNessuna valutazione finora
- Kenneth A. Lambert, The Fundamentals of Python: First Programs, 2011, Cengage Learning, ISBN: 978-1111822705. 2. 3. 4. 5Documento1 paginaKenneth A. Lambert, The Fundamentals of Python: First Programs, 2011, Cengage Learning, ISBN: 978-1111822705. 2. 3. 4. 5helloNessuna valutazione finora
- Calmotion Usb CNCDocumento17 pagineCalmotion Usb CNCErnesto ChavezNessuna valutazione finora
- Chapter-10 Standard Library Functions Type A: Very Short Answer QuestionsDocumento3 pagineChapter-10 Standard Library Functions Type A: Very Short Answer QuestionsRachna AnandNessuna valutazione finora