Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Lab #4: Perform A Qualitative Risk Assessment For An It Infrastructure
Caricato da
Hờ Bờ LờDescrizione originale:
Titolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Lab #4: Perform A Qualitative Risk Assessment For An It Infrastructure
Caricato da
Hờ Bờ LờCopyright:
Formati disponibili
Lab #4: PERFORM A QUALITATIVE RISK
ASSESSMENT FOR AN IT
INFRASTRUCTURE
Course Name: IAA202
Student Name: TRAN THANH HUNG
Instructor Name: MAI HOANG DINH
Lab Due Date: 1/25/2020
Overview :
The following risks, threats, and vulnerabilities were found in an IT infrastructure.
Your Instructor will assign you one of four different scenarios and vertical
industries each of which is under a unique compliance law.
1. Scenario/Vertical Industry:
a. Healthcare provider under HIPPA compliance law
b. Regional bank under GLBA compliance law
c. Nationwide retailer under PCI DSS standard requirements
d. Higher-education institution under FERPA compliance law
2. Given the list, perform a qualitative risk assessment by assigning a risk
impact/risk factor to each of identified risks, threats, and vulnerabilities
throughout the seven domains of a typical IT infrastructure that the risk,
threat, or vulnerability resides.
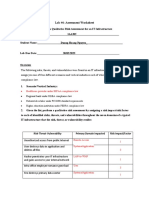
Risk – Threat – Vulnerability Primary Domain Impacted Risk Impact/Factor
Unauthorized access from pubic Internet Remote Access Domain 1
User destroys data in application and deletes System/Application Domain 3
all files
Hacker penetrates your IT infrastructure LAN-to-WAN Domain 1
and gains access to your internal network
Intra-office employee romance gone bad User Domain 3
Fire destroys primary data center System/Application Domain 1
Service provider SLA is not achieved WAN Domain 3
Workstation OS has a known software Workstation Domain 2
vulnerability
Unauthorized access to organization owned Workstation Domain 1
workstations
Lab Assessment Questions:
Loss of production data System/Application Domain 2
Denial of service attack on organization LAN-to-WAN Domain 1
DMZ and e-mail server
Remote communications from home office Remote Access Domain 2
LAN server OS has a known software LAN Domain 2
vulnerability
User downloads and clicks on an unknown User Domain 1
unknown e-mail attachment
Workstation browser has software vulnerability Workstation Domain 3
Mobile employee needs secure browser access Remote Access Domain
to sales order entry system
Service provider has a major network outage WAN Domain 2
Weak ingress/egress traffic filtering LAN-to-WAN Domain 3
degrades performance
User inserts CDs and USB hard drives User Domain 2
with personal photos, music, and videos on
organization owned computers
VPN tunneling between remote computer LAN-to-WAN Domain 2
Risk – Threat – Vulnerability Primary Domain Impacted Risk Impact/Factor
DoS/DDoS attack from the WAN/Internet WAN Domain 1
3. For each of the identified risks, threats, and vulnerabilities, prioritize them
by listing a “1”, “2”, and “3” next to each risk, threat, vulnerability found
within each of the seven domains of a typical IT infrastructure. “1” =
Critical, “2” = Major, “3” = Minor. Define the following qualitative risk
impact/risk factor metrics:
“1” Critical – a risk, threat, or vulnerability that impacts compliance (i.e.,
privacy law requirement for securing privacy data and implementing proper
security controls, etc.) and places the organization in a position of increased
liability.
“2”Major – a risk, threat, or vulnerability that impacts the C-I-A of an
organization’s intellectual property assets and IT infrastructure.
“3”Minor – a risk, threat, or vulnerability that can impact user or employee
productivity or availability of the IT infrastructure.
User Domain Risk Impacts: 5
Workstation Domain Risk Impacts: 3
LAN Domain Risk Impacts: 2
LAN-to-WAN Domain Risk Impacts: 2
WAN Domain Risk Impacts: 4
Remote Access Domain Risk Impacts: 2
Systems/Applications Domain Risk Impacts: 3
4. Craft an executive summary for management using the following 4-
paragraph format. The executive summary must address the following
topics:
Paragraph #1: Summary of findings: risks, threats, and
vulnerabilities found throughout the seven domains of a typical
IT infrastructure
Paragraph #2: Approach and prioritization of critical, major,
minor risk assessment elements
Paragraph #3: Risk assessment and risk impact summary to the
seven domains of a typical IT infrastructure
Paragraph #4: Recommendations and next steps for executive
management
Overview
Answer the following Assessment Worksheet questions pertaining to your
qualitative IT risk assessment you performed.
Lab Assessment Questions & Answers
1. What is the goal or objective of an IT risk assessment?
The goal of the RA is to identify and mitigate risks.
2. Why is it difficult to conduct a qualitative risk assessment for an IT
infrastructure?
It is difficult to conduct a qualitative risk assessment for an IT infrastructure
because it is hard to tell what kind of impact a given attack will have on the
infrastructure.
3. What was your rationale in assigning “1” risk impact/ risk factor value of
“Critical” for an identified risk, threat, or vulnerability?
Assigned critical impact values for threats that severely compromise patient
data or that made the system useless such as DoS attacks.
4. When you assembled all of the “1” and “2” and “3” risk impact/risk factor
values to the identified risks, threats, and vulnerabilities, how did you
prioritize the “1”, “2”, and “3” risk elements? What would you say to
executive management in regards to your final recommended
prioritization?
Management should acquire a SLA so that our systems will always be
functioning optimally. I would also recommend that the appropriate
countermeasures for threats are in place.
5. Identify a risk mitigation solution for each of the following risk
factors:
User downloads and clicks on an unknown e-mail attachment –
Attachments are a significant security risk associated with emails.
Effective email attachment filtering and restrictions reduce the likelihood
of malicious content entering the network.
Workstation OS has a known software vulnerability – Define a
workstation operating system vulnerability window policy definition.
Start periodic workstation domain vulnerability tests to find all
vulnerabilities.
Need to prevent eavesdropping on WLAN due to customer privacy data
access – Use WLAN network keys that require a password for wireless
access. Turn of broadcasting of WAPs,require second level authentication
prior to granting WLAN access
Weak ingress/egress traffic filtering degrades performance – Apply
WAN optimization and data compression solutions when accessing
remote systems; applications and data. Enable Access Control lists
(ACLs) on outbound router WAN interfaces in keeping with policy.
DoS/DDoS attack from the WAN/Internet – Apply filter on exterior IP
stateful firewalls an IP router WAN interfaces to block TCP SYN and
ICMP (ping). Alert your ISP provider to put theproper filters on its IP
router WAN interfaces in accordance with CERT Advisory CA- 1996-21.
Remote access from home office – Apply first level and second level
security for remote access tosensitive systems, applications and data.
Production server corrupts database – Implement daily data backups and
off-site data storage for monthly data archiving. Define data recovery
procedures based on defined RTOs.
Potrebbero piacerti anche
- Healthcare Provider Under HIPPA Compliance LawDocumento8 pagineHealthcare Provider Under HIPPA Compliance LawDuong Chi Hung (K15 HCM)100% (1)
- IAA4Documento4 pagineIAA4na100% (1)
- Lab #1: Assessment WorksheetDocumento5 pagineLab #1: Assessment WorksheetnaNessuna valutazione finora
- Lab 3Documento4 pagineLab 3Nguyen Dinh Quan (K15 HCM)Nessuna valutazione finora
- Risk - Threat - Vulnerability Primary Domain ImpactedDocumento4 pagineRisk - Threat - Vulnerability Primary Domain ImpactedDuong Chi Hung (K15 HCM)Nessuna valutazione finora
- Lab9 IAP202 IA1503 Se150582 NGUYENVIETQUANGVUDocumento3 pagineLab9 IAP202 IA1503 Se150582 NGUYENVIETQUANGVUNguyen Viet Quang Vu (K15 HCM)Nessuna valutazione finora
- Iaa202 Lab6 Se140442Documento17 pagineIaa202 Lab6 Se140442Đinh Khánh LinhNessuna valutazione finora
- IS3110 Unit 2 LabDocumento5 pagineIS3110 Unit 2 LabBri Duq0% (2)
- Lab 3Documento4 pagineLab 3Nguyen Dinh Quan (K15 HCM)Nessuna valutazione finora
- Assessment Worksheet Develop A Risk Mitigation Plan Outline For An It InfrastructureDocumento4 pagineAssessment Worksheet Develop A Risk Mitigation Plan Outline For An It InfrastructureHờ Bờ Lờ100% (1)
- Lab #5: How To Identify Risks, Threats & Vulnerabilities in An It Infrastructure Using Zenmap Gui (Nmap) & Nessus® ReportsDocumento4 pagineLab #5: How To Identify Risks, Threats & Vulnerabilities in An It Infrastructure Using Zenmap Gui (Nmap) & Nessus® ReportsHờ Bờ Lờ100% (1)
- Iaa202 Lab2 Se140442Documento6 pagineIaa202 Lab2 Se140442Đinh Khánh LinhNessuna valutazione finora
- Dương Chí Hùng SE151235 Lab05Documento3 pagineDương Chí Hùng SE151235 Lab05Duong Chi Hung (K15 HCM)Nessuna valutazione finora
- Iaa 2Documento7 pagineIaa 2naNessuna valutazione finora
- Lab #6 - Assessment Worksheet Elements of a Remote Access Domain Policy Course Name: IAA202 Student Name: Dương Chí Hùng Instructor Name: Hồ Hải Lab Due Date: 27/6/2021Documento9 pagineLab #6 - Assessment Worksheet Elements of a Remote Access Domain Policy Course Name: IAA202 Student Name: Dương Chí Hùng Instructor Name: Hồ Hải Lab Due Date: 27/6/2021Duong Chi Hung (K15 HCM)Nessuna valutazione finora
- Lab #3 - Assessment Worksheet: A. Healthcare Provider Under HIPPA Compliance LawDocumento5 pagineLab #3 - Assessment Worksheet: A. Healthcare Provider Under HIPPA Compliance LawDuong Chi Hung (K15 HCM)Nessuna valutazione finora
- Chapter 1 of Computer SecurityDocumento44 pagineChapter 1 of Computer SecurityQasim BhatiaNessuna valutazione finora
- Lab2 IAA202Documento7 pagineLab2 IAA202Đào Mạnh CôngNessuna valutazione finora
- IAA202 - LAB4 - SE140442: A. Healthcare Provider Under HIPPA Compliance LawDocumento6 pagineIAA202 - LAB4 - SE140442: A. Healthcare Provider Under HIPPA Compliance LawĐinh Khánh LinhNessuna valutazione finora
- IAA Lab4 HuynhMinhHaDocumento4 pagineIAA Lab4 HuynhMinhHaHuynh Minh Ha (K16HCM)Nessuna valutazione finora
- Lab4 IAA202Documento5 pagineLab4 IAA202Đào Mạnh CôngNessuna valutazione finora
- IAA Lab6 HuynhMinhHaDocumento4 pagineIAA Lab6 HuynhMinhHaHuynh Minh Ha (K16HCM)Nessuna valutazione finora
- Iaa202 - Lab 4 - Nguyentuanlinh - Se130002 - 26012021Documento9 pagineIaa202 - Lab 4 - Nguyentuanlinh - Se130002 - 26012021Dang Viet My MyNessuna valutazione finora
- Lab #4Documento6 pagineLab #4Trần Mỹ LinhNessuna valutazione finora
- Lab 4: Perform A Qualitative Risk Assessment For An IT InfrastructureDocumento4 pagineLab 4: Perform A Qualitative Risk Assessment For An IT InfrastructureBí RẩyNessuna valutazione finora
- Iaa202 Lab 04 Iam302Documento9 pagineIaa202 Lab 04 Iam302Nguyen Tuan Cuong QP3044Nessuna valutazione finora
- Lab 1 - IAA202Documento4 pagineLab 1 - IAA202Hoàng NguyênNessuna valutazione finora
- LAB 4-Phạm Trần Trung Dũng SE150718Documento4 pagineLAB 4-Phạm Trần Trung Dũng SE150718Dũng PhạmNessuna valutazione finora
- Lab 2 Assessment Worksheet Align Risk THDocumento18 pagineLab 2 Assessment Worksheet Align Risk THChau Minh Khanh (K14 HCM)Nessuna valutazione finora
- Lab 6 Identify Threats and Vulnerabilities in An IT Infrastructure Object of LAB6Documento3 pagineLab 6 Identify Threats and Vulnerabilities in An IT Infrastructure Object of LAB6Henry WiliamNessuna valutazione finora
- Lab #1Documento3 pagineLab #1Trần Mỹ LinhNessuna valutazione finora
- Lab #1: Assessment Worksheet Course Name: IAA202 Student Name: Chế Công Đại Instructor Name: Mai Hoang Dinh Lab Due Date: 7/1/2022Documento4 pagineLab #1: Assessment Worksheet Course Name: IAA202 Student Name: Chế Công Đại Instructor Name: Mai Hoang Dinh Lab Due Date: 7/1/2022Mlem MlemNessuna valutazione finora
- Lab1 IAA202Documento8 pagineLab1 IAA202Đào Mạnh CôngNessuna valutazione finora
- Lab 4Documento6 pagineLab 4Hoàng NguyênNessuna valutazione finora
- IAA202-LAB - 1-SE151495 - Nguyễn Huỳnh Minh ĐanDocumento4 pagineIAA202-LAB - 1-SE151495 - Nguyễn Huỳnh Minh ĐanBí RẩyNessuna valutazione finora
- Lab6 IAA202Documento18 pagineLab6 IAA202Đào Mạnh CôngNessuna valutazione finora
- Risk - Threat - Vulnerability Primary Domain ImpactedDocumento5 pagineRisk - Threat - Vulnerability Primary Domain ImpactedVinh Huynh K14 HCMNessuna valutazione finora
- Part A - List of Risks, Threats, and Vulnerabilities Commonly Found in An IT InfrastructureDocumento4 paginePart A - List of Risks, Threats, and Vulnerabilities Commonly Found in An IT InfrastructureNguyen Viet Quang Vu (K15 HCM)Nessuna valutazione finora
- IAA202 Lab1 SE140723Documento4 pagineIAA202 Lab1 SE140723bui lamNessuna valutazione finora
- Lab 6 ReportDocumento8 pagineLab 6 ReportNguyen Thi Bang Chau (K16 HCM)Nessuna valutazione finora
- Managing Risk in Information Systems: Student Lab ManualDocumento9 pagineManaging Risk in Information Systems: Student Lab Manualnguyen hong haNessuna valutazione finora
- Risk-Threat-Vulnerability Primary Domain Impacted Risk Impact/FactorDocumento6 pagineRisk-Threat-Vulnerability Primary Domain Impacted Risk Impact/FactorDang Viet My MyNessuna valutazione finora
- Iaa202 Lab6Documento17 pagineIaa202 Lab6Dao Manh Cong (K16HL)Nessuna valutazione finora
- Lab 1Documento6 pagineLab 1Nguyễn Thành Đạt (Nguyễn Thành Đạt)Nessuna valutazione finora
- Lab 03Documento6 pagineLab 03truongvg2003Nessuna valutazione finora
- IAA202 - LAB06 - Ngô Hiến Hào - SE161178Documento13 pagineIAA202 - LAB06 - Ngô Hiến Hào - SE161178Hào NgôNessuna valutazione finora
- Lab3 IAP301Documento11 pagineLab3 IAP301thuyptmhe171100Nessuna valutazione finora
- Course Name: IAA202 Student Name: Chế Công Đại Instructor Name: Mai Hoang Dinh Lab Due Date: 9/2/2022Documento8 pagineCourse Name: IAA202 Student Name: Chế Công Đại Instructor Name: Mai Hoang Dinh Lab Due Date: 9/2/2022Công ĐạiNessuna valutazione finora
- IS3110 Lab 1 How To Identify Threats & Vulnerabilities in An IT InfrastructureDocumento3 pagineIS3110 Lab 1 How To Identify Threats & Vulnerabilities in An IT InfrastructureAdriennel40100% (7)
- Lab3 SE150956Documento4 pagineLab3 SE150956Nhật TrầnNessuna valutazione finora
- IAP301 SE161501 Lab3Documento6 pagineIAP301 SE161501 Lab3Le Trung Son (K16HCM)Nessuna valutazione finora
- Lab #3 - Assessment WorksheetDocumento4 pagineLab #3 - Assessment WorksheetLe Quang Vu (K16HCM)Nessuna valutazione finora
- Lab 2 IAA202Documento4 pagineLab 2 IAA202Anh DucNessuna valutazione finora
- (IS3110) Week 1 - LabDocumento4 pagine(IS3110) Week 1 - Labrussell nielsen0% (1)
- An Exampleof ICTRisk ManagementDocumento10 pagineAn Exampleof ICTRisk ManagementMOHAMED SHARKAWINessuna valutazione finora
- 1.4.1.1 Lab - Researching Network Attacks and Security Audit ToolsDocumento4 pagine1.4.1.1 Lab - Researching Network Attacks and Security Audit Toolssafwan eshamasulNessuna valutazione finora
- Chapter 4 SMCDocumento16 pagineChapter 4 SMCNorazlina AbdullahNessuna valutazione finora
- IAA202 Lab2 SE140810Documento3 pagineIAA202 Lab2 SE140810Vinh Huynh K14 HCMNessuna valutazione finora
- Endpoint SecurityDocumento12 pagineEndpoint SecurityCagatay alpNessuna valutazione finora
- Chapter Six: IS Network and Telecommunications RisksDocumento34 pagineChapter Six: IS Network and Telecommunications RisksJay ManNessuna valutazione finora
- Course Name: IAA202 Student Name: Tran Thanh Hung Instructor Name: MAI HOANG DINH Lab Due Date: 03/16/2020Documento5 pagineCourse Name: IAA202 Student Name: Tran Thanh Hung Instructor Name: MAI HOANG DINH Lab Due Date: 03/16/2020Hờ Bờ LờNessuna valutazione finora
- Lab #8: Develop An Outline For A Business Continuity Plan For An It InfrastructureDocumento6 pagineLab #8: Develop An Outline For A Business Continuity Plan For An It InfrastructureHờ Bờ LờNessuna valutazione finora
- Lab #10: Create A Cirt Response Plan For A Typical It InfrastructureDocumento3 pagineLab #10: Create A Cirt Response Plan For A Typical It InfrastructureHờ Bờ LờNessuna valutazione finora
- Develop Disaster Recovery Back-Up Procedures and Recovery InstructionsDocumento4 pagineDevelop Disaster Recovery Back-Up Procedures and Recovery InstructionsHờ Bờ LờNessuna valutazione finora
- Assessment Worksheet Develop A Risk Mitigation Plan Outline For An It InfrastructureDocumento4 pagineAssessment Worksheet Develop A Risk Mitigation Plan Outline For An It InfrastructureHờ Bờ Lờ100% (1)
- Lab #5: How To Identify Risks, Threats & Vulnerabilities in An It Infrastructure Using Zenmap Gui (Nmap) & Nessus® ReportsDocumento4 pagineLab #5: How To Identify Risks, Threats & Vulnerabilities in An It Infrastructure Using Zenmap Gui (Nmap) & Nessus® ReportsHờ Bờ Lờ100% (1)
- Assignment #2 Analyze The Vulnerability AND THE BENEFIT OF USING THE Microsoft Exchange, THE E-MAIL, THE Microsoft OutlookDocumento5 pagineAssignment #2 Analyze The Vulnerability AND THE BENEFIT OF USING THE Microsoft Exchange, THE E-MAIL, THE Microsoft OutlookHờ Bờ LờNessuna valutazione finora
- Pentest Studyguide Pt0-001 SamplelessonDocumento44 paginePentest Studyguide Pt0-001 SamplelessonAnwar Jumoorty0% (1)
- Cryptography Hash Functions: STD Code Full Name Class MarksDocumento21 pagineCryptography Hash Functions: STD Code Full Name Class MarksBrikhov XNessuna valutazione finora
- IT Sec Net Sec Cyber Sec IT LawDocumento27 pagineIT Sec Net Sec Cyber Sec IT LawCha DechavezNessuna valutazione finora
- Security Model ExamDocumento18 pagineSecurity Model ExamEyoabNessuna valutazione finora
- Kumar MA SCS Converted by AbcdpdfDocumento142 pagineKumar MA SCS Converted by AbcdpdfAnkita RanaNessuna valutazione finora
- SQL InjectionDocumento3 pagineSQL Injectiondanieldamalie9Nessuna valutazione finora
- OWASP: Testing Guide v4 Checklist: Information Gathering Test NameDocumento26 pagineOWASP: Testing Guide v4 Checklist: Information Gathering Test NameasasaNessuna valutazione finora
- DEF CON Safe Mode - Erik Hunstad - Domain Fronting Is Dead Long Live Domain FrontingDocumento65 pagineDEF CON Safe Mode - Erik Hunstad - Domain Fronting Is Dead Long Live Domain FrontingasdfNessuna valutazione finora
- Fireeye Threat Analytics PlatformDocumento2 pagineFireeye Threat Analytics Platformlingo.chichalaNessuna valutazione finora
- Account Statement From 8 Aug 2021 To 31 Aug 2021: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceDocumento3 pagineAccount Statement From 8 Aug 2021 To 31 Aug 2021: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceMEER MUSTAFA ALINessuna valutazione finora
- Security+ Lab AnswersDocumento160 pagineSecurity+ Lab Answersdeepholm0% (1)
- Iso 27002 Information SecurityDocumento4 pagineIso 27002 Information SecurityNorah Al-ShamriNessuna valutazione finora
- HS09 Homomorphic Tallying With PaillierDocumento10 pagineHS09 Homomorphic Tallying With PaillierTere RereNessuna valutazione finora
- Best Free Antivirus For Windows 10Documento10 pagineBest Free Antivirus For Windows 10Kirtan DaveNessuna valutazione finora
- SIPROTEC 5 V7 8 - en PDFDocumento28 pagineSIPROTEC 5 V7 8 - en PDFJose Antonio Huamani ChuquirimayNessuna valutazione finora
- Pin Block Formats: David TushieDocumento3 paginePin Block Formats: David TushieJinay SanganiNessuna valutazione finora
- Foot PrintingDocumento16 pagineFoot PrintingadmingandaNessuna valutazione finora
- O2 Chapter 8Documento7 pagineO2 Chapter 8SamNessuna valutazione finora
- Creatrix Campus GDPR - V1Documento7 pagineCreatrix Campus GDPR - V1Ajesh PillaiNessuna valutazione finora
- Assignment 1Documento1 paginaAssignment 1Anish Sachdeva0% (1)
- Khudra: A New Lightweight Block Cipher For FpgasDocumento18 pagineKhudra: A New Lightweight Block Cipher For FpgasAnonymous sskjn1A7xNessuna valutazione finora
- How To Set Up A SOCKS Proxy Using Putty & SSHDocumento3 pagineHow To Set Up A SOCKS Proxy Using Putty & SSHjohn100% (1)
- Latex Report CodeDocumento15 pagineLatex Report CodeAbhiNessuna valutazione finora
- Prosecco ProposalDocumento43 pagineProsecco ProposalAshwin Josiah SamuelNessuna valutazione finora
- Digital/Cyber LiteracyDocumento8 pagineDigital/Cyber LiteracyPia GabitaNessuna valutazione finora
- OpenVPN SettingsDocumento3 pagineOpenVPN SettingsreeNessuna valutazione finora
- Anonymised Web and Infrastructure Penetration Testing ReportDocumento38 pagineAnonymised Web and Infrastructure Penetration Testing ReportRSA ArcherNessuna valutazione finora
- Vertias System Command Using PuttyDocumento1 paginaVertias System Command Using PuttyVijayaraghavan JANGETTI SANJEEVINessuna valutazione finora
- OpenOTP QuickStartDocumento19 pagineOpenOTP QuickStartdjrozsomakNessuna valutazione finora
- Nozomi Networks OT IoT Security Report 2021 02Documento54 pagineNozomi Networks OT IoT Security Report 2021 02Com DigfulNessuna valutazione finora