Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
DDoS Attack Report Evaluation
Caricato da
Dewa AsmaraTitolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
DDoS Attack Report Evaluation
Caricato da
Dewa AsmaraCopyright:
Formati disponibili
DDoS Attacks Evaluation Report
Abbreviations 3
Executive Summary 4
What is a DoS/DDoS Attack? 5
Types of DDoS Attacks 5
Volumetric Attacks(Network) 6
Protocol Attacks 6
Application Attacks 7
Attack Motivations 7
True Stories 8
Service Provider (Anonymous): 1.7 Tbps / 2018 8
GitHub: 1.3 Tbps / 2018 8
Dyn: 1.2 Tbps / 2016 9
CloudFlare: 400 Gbps / 2014 9
SpamHaus: 300 Gbps / 2013 10
Various Statistics 11
Protection Approach 13
External 14
Edge 15
Internal 16
People and Process 17
DDoS Tests 17
LoDDoS 17
Conclusions 19
DDoS Attacks Evaluation Report 2
Abbreviations
DDoS : Distributed Denial of Service
IoT : Internet of Things
TCP : Transmission Control Protocol
UDP : User Datagram Protocol
NTP : Network Time Protocol
SSDP : Simple Service Discovery Protocol
SMTP : Simple Mail Transfer Protocol
OSI : Open Systems Interconnection
CDN : Content Delivery Network
Gbps : Giga bit per second
PPS : Packet Per Second
WAF : Web Application Firewall
IPS : Intrusion Prevention System
DNS : Domain Name System
DDoS Attacks Evaluation Report 3
Executive Summary
As DDoS attacks become increasingly complicated, it gets much easier and cost-efficient to
organize DDoS attacks. Attackers can organize DDoS attacks for quite low costs solely by
entering destination addresses and easily disable organization systems. Such easy and low-
cost DDoS attacks pose great risks for internet-driven organizations. Taken unawares by such
DDoS attacks, organizations may fail to serve for hours, even for days.
DDoS attacks may be risky for all web-based organizations. It is of great importance to get
prepared against such kind of attacks, to take any necessary technical and administrative
measures and to test DDoS durability of systems on regular basis in order to improve defense
mechanisms.
This report explains DDoS, types of DDoS, motives behind DDoS attacks, true stories of
major DDoS incidents, approach of protection against DDoS attacks and the importance of
DDoS tests.
DDoS Attacks Evaluation Report 4
What is a DoS/DDoS Attack?
Before describing the term “Distributed Denial of Service (DDoS)” Attack, it would be more
appropriate to define the term Denial of Service (DoS) Attack. DoS attack targets to prevent
legitimate users from accessing a targeted system. Such attacks exploit target system and
applications or other sources used in accessing such system and applications to make the
targets unavailable. In DDoS, attackers utilize multiple sources of distributed attacks for the
same purpose. The use of multiple number and type of attack resources (computer, mobile
phone, IoT etc.) targets both easily overcoming the easy prevention of attacks and faster and
easier exploitation of targeted system. Attackers typically seize internet-connected
information technology resources with malwares (zombie/bot) and prefer to deplete the
resources of targeted systems through a number of mechanisms (Command and
Control/C2/C&C), able to control such devices (botnet) in bulk.
Types of DDoS Attacks
Attackers typically use three types of DDoS attacks (Network, Protocol and Application) as
defined below:
Volumetri
c Attacks
Protocol
Attacks
Applicatio
n Attacks
Figure 1
DDoS Attacks Evaluation Report 5
Volumetric Attacks (Network)
Volumetric attacks are the most preferred type of attack by the attackers and target to flood
internet bandwidth used by targeted organizations. In this way, both the incoming and
outgoing network traffic of an organization are affected and fail to respond any legitimate
requests and eventually become unavailable. Finally, all parties that use the same internet
infrastructure will be affected and all internet-connected services will be disabled.
Examples to volumetric attacks are TCP/UDP Flood, DNS/NTP/Memcached Amplification.
Amplification Attacks: Amplification attacks are those that use DNS, NTP, SSDP,
Memcached etc. protocols on servers that serve large masses on the internet. While attacking
victim (target) systems, attackers act like making requests from victim systems (spoof) and
enable return packets access victim system to realize DDoS. In this type of attack, small
queries are sent to servers, which are not safely configurated, to ensure that victim system is
delivered large amount of inquiry packets. When victim systems fail to respond large-size and
amplified amount of inquiries, it becomes inaccessible.
Attacker
Victim
Figure 2
Protocol Attacks
These attacks typically target OSI L3/L4 protocols and use session information to target
Firewalls, Load Balancers, Routers etc. systems. This type of attack makes multiple login
requests and sends new inquiries before login is complete. In this way, it fills the session
tables of network and security devices to make them inaccessible.
DDoS Attacks Evaluation Report 6
Examples to protocol attacks are SYN/SYN-ACK/ACK Flood, Ping of Death etc.
Application Attacks
These attacks target web applications, DNS, SMTP etc. OSI L7 application services. Targeted
applications are overwhelmed by large range of inquiries beyond their capacities until their
resources are depleted and eventually, the system becomes unavailable.
Examples to application attacks are Flood attacks to HTTP, HTTPS, DNS and SMTP services.
The aforementioned attacks may either be performed singly by attackers or simultaneously
with multi-vector attacks. In this way, attackers make their attacks much more complexed
while targeting both to hinder the response teams and to complicate the efforts of security
devices for prevention.
Attack Motivations
It is likely that many motivation factors lie behind DDoS attacks. To address a few:
Money: The motivation that corresponds to an attack, which eventually leads to earning or
losing money. The reasons may include, but not limited to, to gain advantage over
competitors, racketing, decrease in share value etc.
Ideological: Due to political etc. reasons.
Attack Concealment: To prevent the original intention, i.e. detection of data leakage etc. by
distracting the personnel and devices of a targeted organization.
These are typically mentioned motivations and may include any further different motives.
DDoS Attacks Evaluation Report 7
True Events
Many organizations are exposed to DDoS attacks every single day. This topic will address
some of real attacks by their importance in the history.
Service Provider (Anonymous): 1.7 Tbps / 2018
NetScout reported that the largest DDoS attack was on March 5, 2018 of 1.7 Tbps size
utilizing Memcached Amplification that targeted a customer of a U.S.-based service provider.
It was confirmed that the attack had been avoided.
Figure 3
GitHub: 1.3 Tbps / 2018
GitHub, a platform where software developers store and share their applications, was the
victim of a DDoS attack that peaked at 1.35 Tbps in 2018. The attack was mitigated after
around 10 minutes of denial to website after which DDoS protection service was activated.
The attackers used Memcached amplification attack.
DDoS Attacks Evaluation Report 8
Figure 4
Dyn: 1.2 Tbps / 2016
Dyn, a DNS provider, was the victim of 1 Tbps-size DDoS attacks at several time periods
on October 21, 2016. These attacks used Mirai botnet, largely made of IoT devices, and
TCP and UDP traffic over port 53. The first attack could not be mitigated for 2,5 hours,
after when only new attacks were encountered. Many websites suffered from accessibility
during the attacks.
Figure 5
CloudFlare: 400 Gbps / 2014
CloudFlare is a Content Delivery Network (CDN) service provider. An organization serving
on CloudFlare became the victim of a 400Gbps attack in 2014, which attack even affected
CloudFlare’s own systems. Such attack used Network Time Protocol (NTP), a networking
protocol for clock synchronization between servers.
DDoS Attacks Evaluation Report 9
Figure 6
SpamHaus: 300 Gbps / 2013
In 2013, a 300 Gbps DDoS attack was launched against SpamHause, an anti-spam
organization. The largest DDoS attack in history then, this attack was stopped by SpamHaus’s
service provider.
Figure 7
As seen in the incidents above, even security providers may be affected by massive DDoS
attacks. The magnitudes of above attacks were tremendous, which sizes are rarely seen.
DDoS Attacks Evaluation Report 10
Various Statistics
The statistics obtained from a number of global reports published about DDoS attacks will be
useful to profile DDoS attacks in general.
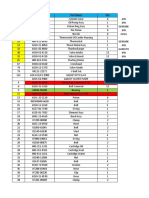
Two graphs in 2018 Corero Trends Report suggest that:
Figure 8
According to the graph above:
82% of DDoS attacks in 2018 were 1 Gbps or lower.
The ratio of attacks between 1 Gbps and 10 Gbps is 16%.
The ratio of attacks larger than 10 Gbps is 2% of total attacks.
This ratio corresponds to an increase of 100% compared to 2017.
Figure 9
Another significant graph in 2018 Corero Trends Report is provided above. According to this
graph:
81% of attacks in 2018 lasted for or less than 10 minutes
DDoS Attacks Evaluation Report 11
96% of DDoS attacks lasted for or less than 60 minutes.
Figure 10
According to Q4 2017 Global DDoS Threat Landscape Report, top targeted countries for
DDoS attacks include US, South Korea and China. In addition, Turkey ranks amongst the top
targeted countries with a ratio of 2.1%.
Figure 11
According to NETSCOUT Threat Intelligence Report published in 2018, 75.7% of DDoS
attacks were volumetric, 12.4% were application layered and 11.8% were protocol attacks.
DDoS Attacks Evaluation Report 12
Figure 12
The increase of use of mobile phones, expansion of processors and memories of mobile
phones and 24/7 availability of such devices make them vulnerable to active DDoS attacks.
The graph above illustrates that around 60% of recent DDoS incidents include mobile phones
as botnet members.
Protection Approach
As addressed in the topics above, DDoS attacks may be launched in various types and sizes.
Unfortunately, no single device or method is readily available to prevent all DDoS types. The
way to be resistant against DDoS attacks is to create a layered defense mechanism like in
other security activities.
Gartner’s “DDoS: A Comparison of Defense Approaches” report suggests a detection and
prevention method consisting of multiple defense layers as given below about how a defense
mechanism should be.
DDoS Attacks Evaluation Report 13
Figure 12
To address such layers;
External
We mentioned about the details of volumetric attacks above. If large size of volumetric
attacks can reach the organization network, in such a case the security measures of
organizations will unfortunately be poor to prevent the attack. Prevention or mitigation should
be realized before such attacks reach out to the organization network. At this point, Internet
Service Providers (ISP) or DDoS Protection Services provided by ISP’s come into play.
ISP’s, which are able to process large-size traffics, get activated to mitigate the effects of
DDoS attack in a short while (depending on ISP) after malicious traffic accesses the
organization network.
From this point of view, it is of great importance for organization to adopt a DDoS
Protection Service conforming to their business requirements.
DDoS Attacks Evaluation Report 14
ISP DDoS
Protection Service
Attacker
Organization
Figure 13
Edge
This layer consists of router, load balancer, firewall and similar edge network and security
device of organizations. Attackers exhaust session tables of such devices through protocol
attacks (TCP-SYN etc.) and may disable IP router, load balancer, firewall etc. devices.
DDoS Protection Devices, which have been developed to protect such networks and security
devices, are currently available in cyber security market. These devices offer technologies that
have been developed to prevent DDoS attacks launched against network and security devices
on session basis.
In order to protect the organization systems in edge layer, these devices must be positioned at
the external point of the organization nearest to the internet. Furthermore, certain DDoS
protection devices ensure signaling with devices in ISP and offer DDoS protection service to
enable a more effective DDoS protection mechanism.
DDoS Attacks Evaluation Report 15
ISP DDoS Protection
DDos Protection Device
Service
Attacker
Organization
Figure 14
Internal
Probably the most dangerous of DDoS attacks in types of network, protocol and application is
the application attack. These attacks are typically launched against web, e-mail, DNS etc.
applications that directly serve the user and make related application become unavailable. If,
in particular, DNS attack succeeds, all DNS-dependent applications will be inaccessible. IPS,
WAF etc. devices are used for protection against internet-based applications. These devices
help discover the configurations of applications and are capable of activating application-
specific protection mechanisms.
ISP DDoS DDos
DDoSProtection
Protection
ISP DDoS
Protection Service
Protection Service Device
Device
Attacker
Attacker
Organization
Organization
Figure 15
DDoS Attacks Evaluation Report 16
People and Process
Even if top-quality DDoS protection services and devices (state-of-the-art technology) are
adopted, all People-Process-Technology components should be cohesively used for an
effective cyber defense. At this point, People and Process factors are of great importance in
DDoS protection approach. In case of a DDoS attack, an incident management process should
have been soundly realized for an accurate and effective response. In a similar manner, the
response team and the team responsible from recovery in case of a failure should be
competent and prepared. Therefore, Emergency Action Plans must be prepared and checked
for currency and validity through regular drills.
DDoS Tests
DDoS tests include the activities, which are conducted to test the aforementioned DDoS
protection activities at certain intervals and/or after any major system/application changes and
to improve any performed protection activities according to such test results.
The activities, which are most appropriate to minimum exposure to DDoS attacks, were
mentioned under DDoS protection approach heading. The aforementioned people-process-
technology activities require not only time and money but also investment. It is quite
important to measure how such investments are effective and efficient in case of a real attack
and to remove any detected deficiencies. In this context, it will be necessary to test the
internet-connected services of the organization by generating large amount of traffic
(bandwidth and pps) through multiple bots across different geographic regions around the
world, like real attackers do. In particular, internet-connected applications must be tested
consistently and such tests must be repeated in case of any changes in existing applications or
starting new applications.
LoDDoS
It takes time and effort to conduct the necessary preparations to run DDoS tests. Technical
and administrative preparation phases of such tests take a long time. Both security and IT
teams should work in collaboration in order to prepare and configure the systems to be used in
DDoS testing. Upon completion of preparations, no instant watch is possible during the
implementation phase of testing and it takes time to generate reports after tests are completed.
Whether a test is conducted once or consistently, preparation phase of each test is performed
DDoS Attacks Evaluation Report 17
from the very beginning. Therefore, it became imperative to obtain automation for such
preparation and implementation phases through an application.
At this point, LoDDoS is a DDoS Simulation and Load Testing platform offered as a service.
This platform simulates any possible DDos attacks to an organization with real-attack
parameters. Moreover, it measures the resilience of internet-connected web applications to
high traffic.
Bots
Command-Control
Contractor
Central Management
Monitoring System
DDoS Attacks
TARGET
Customer
Operator
Figure 16
DDoS Simulation helps organizations test the limits and abilities of their DDoS prevention
systems without being exposed to a real DDoS attack. Tests can be monitored live, and can be
stopped at any time in a controlled manner, started over, reported instantly and reports may be
saved for further evaluation.
Load Testing helps quantifying to what extent the infrastructures may fulfill large number of
requests to web applications and performing any necessary improvements before a real load
occurs.
DDoS Attacks Evaluation Report 18
Conclusions
DDoS attacks become increasingly complicated and reach massive sizes. Even though it is not
inevitable for organizations to sustain DDoS attacks, they are not unavoidable. No matter how
large and complicated such attacks are, it is possible to be affected the least by such attacks if
necessary and sufficient preparations are in place. Case studies described under the heading
‘True Events’ are the best examples to this. Planned defense actions on the axis of People-
Process-Technology will have importance in corroborating the resilience of organizations
against DDoS attacks.
To summarize the main topics about DDoS protection and defense:
To ensure, to consistently monitor and to improve the security service and components
necessary at external, edge and middle layers;
To create and to keep up-to-date processes, procedures and directives for DDoS
protection;
To make sure that the personnel responsible from DDoS protection is technically and
administratively trained;
To test the systems and applications for DDoS and load testing after any major
changes or before commissioning any new applications or periodically; and
To test the components of people-process-technology through drills and to apply any
necessary improvements.
DDoS Attacks Evaluation Report 19
Mustafa Kemal Mahallesi. Nida Kule Alaşehir Kuzey İş Merkezi, Millenium Tower Floor 29.
Dumlupınar Bulvarı No:164, Barbaros Mahallesi, Begonya Sokak. No:3, Radarweg 29 1045 XN
Kerıtpark Ofis, Kat:4 Daire:06 Daire: 71/72 Alaşehir/İstanbul Amsterdam/Netherlands
Çankaya/Ankara
Phone: +90 (312) 235 44 41 Phone: +90 (216) 504 53 30 Phone: •3120 854 6146
Fax: +90 (312) 235 44 51 Fax: +90 (216) 504 53 32 E-mail: info@barikatbv.com
E-mail: bilgi@barikat.comtr E-mail: bilgi@barikalcom.tr
f lw / loddosglobal www.loddos-sec.com
Potrebbero piacerti anche
- Types of DDoS Attacks and Mitigation StrategiesDocumento6 pagineTypes of DDoS Attacks and Mitigation StrategiesVikNessuna valutazione finora
- Dyn DDOS CyberattackDocumento3 pagineDyn DDOS Cyberattackblob mlNessuna valutazione finora
- Reeves - ECE571 - Final ProjectDocumento8 pagineReeves - ECE571 - Final ProjecthaileyNessuna valutazione finora
- DDoS AttacksDocumento4 pagineDDoS AttacksNour BushNessuna valutazione finora
- Detection & Prevention of DDoS AttacksDocumento7 pagineDetection & Prevention of DDoS AttacksAliNessuna valutazione finora
- A Survey of Distributed Denial of Service Attacks and DefensesDocumento18 pagineA Survey of Distributed Denial of Service Attacks and Defensesdanilo.chagasNessuna valutazione finora
- CEH v12 Lesson 10 - Denial of Services TechniqDocumento56 pagineCEH v12 Lesson 10 - Denial of Services TechniqAbhay JainNessuna valutazione finora
- An Ultimate Guide To DDos Attack: Detection, Prevention and MitigationDocumento41 pagineAn Ultimate Guide To DDos Attack: Detection, Prevention and MitigationTechAppriseNessuna valutazione finora
- Denial of Service AttackDocumento27 pagineDenial of Service AttackMarcNessuna valutazione finora
- Volume Based Ddos Attacks and How To Mitigate Them: Alysson Celso de Almeida SilvaDocumento6 pagineVolume Based Ddos Attacks and How To Mitigate Them: Alysson Celso de Almeida SilvaAlyssonAlmeidaNessuna valutazione finora
- An Integrated Approach to Defend Against DDoS AttacksDocumento6 pagineAn Integrated Approach to Defend Against DDoS AttacksgdeepthiNessuna valutazione finora
- DDoS AttacksDocumento14 pagineDDoS AttacksViineeNessuna valutazione finora
- Seminar ReportdDocumento18 pagineSeminar Reportdbharat patelNessuna valutazione finora
- 6Documento6 pagine6Arnav GudduNessuna valutazione finora
- A - J. Seminar ReportDocumento22 pagineA - J. Seminar ReportShivani Ekant YadavNessuna valutazione finora
- Hadec: Hadoop-Based Live Ddos Detection Framework: Research Open AccessDocumento20 pagineHadec: Hadoop-Based Live Ddos Detection Framework: Research Open Accessamine boulakhrabiNessuna valutazione finora
- Ethical Hacking - SB L3Documento11 pagineEthical Hacking - SB L3Ayush KastNessuna valutazione finora
- Botnet AttacksDocumento2 pagineBotnet AttacksZohaib HassanNessuna valutazione finora
- DDoS AttacksDocumento6 pagineDDoS Attackscemerlang satuNessuna valutazione finora
- Denial of ServiceDocumento48 pagineDenial of ServiceViv EkNessuna valutazione finora
- Ddos Attacks, Detection Parameters and Mitigation in Cloud EnvironmentDocumento4 pagineDdos Attacks, Detection Parameters and Mitigation in Cloud EnvironmentAbere BalewNessuna valutazione finora
- CERT-EU Security Whitepaper DDoS 17-003Documento12 pagineCERT-EU Security Whitepaper DDoS 17-003sanapala84Nessuna valutazione finora
- Optimizing DDOS Attacks Using LCIADocumento7 pagineOptimizing DDOS Attacks Using LCIAInternational Journal of Application or Innovation in Engineering & ManagementNessuna valutazione finora
- Prop CukDocumento17 pagineProp CukWani irshadNessuna valutazione finora
- Distributed Denial of Service Attacks ExplainedDocumento37 pagineDistributed Denial of Service Attacks ExplainedAkash S NNessuna valutazione finora
- Machine Learning Based Ddos Attack Detection From Source Side in CloudDocumento7 pagineMachine Learning Based Ddos Attack Detection From Source Side in CloudseifeNessuna valutazione finora
- Radware - Top Ddos Attack To Prepare ForDocumento4 pagineRadware - Top Ddos Attack To Prepare ForUmitGNessuna valutazione finora
- Types of Ddos Attack: Enterprise It SecurityDocumento18 pagineTypes of Ddos Attack: Enterprise It SecurityMd Lutfar RahmanNessuna valutazione finora
- DdosDocumento23 pagineDdosSiddarth NyatiNessuna valutazione finora
- Dos (Disambiguation) Merged Discuss: Enial-Of-Service AttackDocumento5 pagineDos (Disambiguation) Merged Discuss: Enial-Of-Service AttackNour BushNessuna valutazione finora
- CSE DDos ReportDocumento19 pagineCSE DDos ReportAbhinavms AbhinavmsNessuna valutazione finora
- Denial of Service and PreventionDocumento5 pagineDenial of Service and PreventionGurdeep SidhuNessuna valutazione finora
- Denial of Service ThesisDocumento5 pagineDenial of Service Thesisafkngwetd100% (2)
- Defending against DoS and flooding attacksDocumento7 pagineDefending against DoS and flooding attacksDEANessuna valutazione finora
- Huawei Anti-DDoS Solution v-IsA Technical White PaperDocumento8 pagineHuawei Anti-DDoS Solution v-IsA Technical White PaperEmManuel ALdoNessuna valutazione finora
- Dos Attack ThesisDocumento8 pagineDos Attack Thesisuxgzruwff100% (2)
- ANS AssignmentDocumento25 pagineANS AssignmentAyesha ArshadNessuna valutazione finora
- Machine Learning Ddos Detection Using Stochastic Gradient BoostingDocumento9 pagineMachine Learning Ddos Detection Using Stochastic Gradient Boostingdevendra416Nessuna valutazione finora
- Distributed Hop Count Filtering and Round Trip Time Technique To Combat Ip Spoofing Based Distributed Denial of Service (Ddos) AttacksDocumento10 pagineDistributed Hop Count Filtering and Round Trip Time Technique To Combat Ip Spoofing Based Distributed Denial of Service (Ddos) Attackstuan_fet2005Nessuna valutazione finora
- Dos and Ddos Attacks: Impact, Analysis and Countermeasures: December 2013Documento7 pagineDos and Ddos Attacks: Impact, Analysis and Countermeasures: December 2013jramongvNessuna valutazione finora
- New Microsoft Office Word DocumentDocumento7 pagineNew Microsoft Office Word DocumentJyotsana SinghNessuna valutazione finora
- NSE3 FDD Complete UpdateLiteDocumento42 pagineNSE3 FDD Complete UpdateLiteBhanuka SenarathnaNessuna valutazione finora
- DDoS Attack Term PaperDocumento8 pagineDDoS Attack Term Paperprakhar20febNessuna valutazione finora
- Assignment#4Documento11 pagineAssignment#4Raja AliNessuna valutazione finora
- Cisco DDOS DetailsDocumento29 pagineCisco DDOS Detailsbakiz89Nessuna valutazione finora
- How To Avoid Party Chaos 1698257750912Documento8 pagineHow To Avoid Party Chaos 1698257750912Paul R. MessinaNessuna valutazione finora
- Man, Machine and Ddos Mitigation The Case For Human Cyber Security ExpertiseDocumento2 pagineMan, Machine and Ddos Mitigation The Case For Human Cyber Security Expertiseapi-258089043Nessuna valutazione finora
- DDoS Final PDCS PaperDocumento8 pagineDDoS Final PDCS PaperEduardo CANessuna valutazione finora
- Aamir-Zaidi2019 Article DDoSAttackDetectionWithFeatureDocumento25 pagineAamir-Zaidi2019 Article DDoSAttackDetectionWithFeatureadfafNessuna valutazione finora
- ReportDocumento29 pagineReportPritoj SinghNessuna valutazione finora
- Mitigation of Denial of Service AttackDocumento7 pagineMitigation of Denial of Service AttackZatin GuptaNessuna valutazione finora
- DEFENSE AGAINST DISTRIBUTED DDOSDocumento59 pagineDEFENSE AGAINST DISTRIBUTED DDOSPiyush MittalNessuna valutazione finora
- Password Based Scheme AND Group Testing FOR Defending Ddos AttacksDocumento13 paginePassword Based Scheme AND Group Testing FOR Defending Ddos AttacksAIRCC - IJNSANessuna valutazione finora
- Computational Intelligent Techniques To Detect DDOS Attacks: A SurveyDocumento18 pagineComputational Intelligent Techniques To Detect DDOS Attacks: A SurveyMaryam AldossaryNessuna valutazione finora
- Computational Intelligent Techniques To Detect DDOS Attacks: A SurveyDocumento18 pagineComputational Intelligent Techniques To Detect DDOS Attacks: A SurveyMaryam AldossaryNessuna valutazione finora
- Ddos Attack ThesisDocumento8 pagineDdos Attack ThesisNeedHelpWriteMyPaperUK100% (2)
- Ddos Attack DocumentDocumento56 pagineDdos Attack DocumentNagarjuna NagNessuna valutazione finora
- Web Application Security is a Stack: How to CYA (Cover Your Apps) CompletelyDa EverandWeb Application Security is a Stack: How to CYA (Cover Your Apps) CompletelyNessuna valutazione finora
- CEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021Da EverandCEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021Nessuna valutazione finora
- Cloud Computing Interview Questions You'll Most Likely Be Asked: Second EditionDa EverandCloud Computing Interview Questions You'll Most Likely Be Asked: Second EditionNessuna valutazione finora
- Rogue BT IMSI Catcher Detection Unit2Documento7 pagineRogue BT IMSI Catcher Detection Unit2Dewa AsmaraNessuna valutazione finora
- Unprecedented Access to Locked DevicesDocumento4 pagineUnprecedented Access to Locked DevicesDewa AsmaraNessuna valutazione finora
- MF AUTOMATE Enterprise OnePagerDocumento2 pagineMF AUTOMATE Enterprise OnePagerDewa AsmaraNessuna valutazione finora
- EPC217 08 SEPA Conversion TableDocumento16 pagineEPC217 08 SEPA Conversion TableDewa AsmaraNessuna valutazione finora
- Rev 2 - XTX-ZJ05-JammerDocumento2 pagineRev 2 - XTX-ZJ05-JammerDewa AsmaraNessuna valutazione finora
- MF IGNITE ProductBrief 8.5x11Documento1 paginaMF IGNITE ProductBrief 8.5x11Dewa AsmaraNessuna valutazione finora
- UFED-4PC BrochureDocumento2 pagineUFED-4PC BrochureDewa AsmaraNessuna valutazione finora
- Criminal Investigation (LEA) Use CaseDocumento2 pagineCriminal Investigation (LEA) Use CaseDewa AsmaraNessuna valutazione finora
- The SWIFT Global Payments Innovation Initiative: October, 2016Documento20 pagineThe SWIFT Global Payments Innovation Initiative: October, 2016Dewa AsmaraNessuna valutazione finora
- Whitepaper LTE BoxDocumento15 pagineWhitepaper LTE BoxDewa AsmaraNessuna valutazione finora
- SepaDirectDebit FromExcelToPain v1Documento3 pagineSepaDirectDebit FromExcelToPain v1Dewa AsmaraNessuna valutazione finora
- Cloud SOAR Solution Brief RGB FinalDocumento2 pagineCloud SOAR Solution Brief RGB FinalDewa AsmaraNessuna valutazione finora
- Marketing KIT Dan Rate Card Iklan 2017Documento14 pagineMarketing KIT Dan Rate Card Iklan 2017Dewa AsmaraNessuna valutazione finora
- The Use of Online Applications To Improve Chronic Wound Care in PDocumento37 pagineThe Use of Online Applications To Improve Chronic Wound Care in PDewa AsmaraNessuna valutazione finora
- Consolidated BBI Onboarding PackDocumento111 pagineConsolidated BBI Onboarding PackDewa AsmaraNessuna valutazione finora
- Proposal For Paytm Clone Script: Prepared By: DOD IT SolutionsDocumento22 pagineProposal For Paytm Clone Script: Prepared By: DOD IT SolutionsDODIT SolutionNessuna valutazione finora
- Skylock Product Description 2013 PDFDocumento25 pagineSkylock Product Description 2013 PDFCekidot GanNessuna valutazione finora
- CrossBorder PaymentsDocumento378 pagineCrossBorder PaymentsDewa AsmaraNessuna valutazione finora
- 1234 PDFDocumento36 pagine1234 PDFtân lê duyNessuna valutazione finora
- Technically Enabling SWIFT Gpi Universal Confirmations FM Global BRO 2008 105Documento4 pagineTechnically Enabling SWIFT Gpi Universal Confirmations FM Global BRO 2008 105Sushma V KumarNessuna valutazione finora
- Swift Universal Confirmation: Fusion Global PayplusDocumento2 pagineSwift Universal Confirmation: Fusion Global PayplusDewa AsmaraNessuna valutazione finora
- Proposal DdosDocumento4 pagineProposal DdosDewa AsmaraNessuna valutazione finora
- Free Faculty ToolsDocumento6 pagineFree Faculty ToolsYase BarbarNessuna valutazione finora
- Swift Ug DataDocumento726 pagineSwift Ug DataDewa AsmaraNessuna valutazione finora
- Deloitte SWIFT For Corporates BrochureDocumento16 pagineDeloitte SWIFT For Corporates BrochureLouisNessuna valutazione finora
- 5G Cybersecurity: Preparing A Secure Evolution To 5GDocumento23 pagine5G Cybersecurity: Preparing A Secure Evolution To 5GDewa AsmaraNessuna valutazione finora
- Work LifeDocumento26 pagineWork LifeDewa AsmaraNessuna valutazione finora
- Penetration Testing Sample Report 2013 PDFDocumento36 paginePenetration Testing Sample Report 2013 PDFBrandon GilchristNessuna valutazione finora
- NCSC 10 Steps To Cyber Security NCSCDocumento1 paginaNCSC 10 Steps To Cyber Security NCSCtomas_de_kempisNessuna valutazione finora
- ATV340 - Programming Manual - EN - NVE61643 - 06Documento628 pagineATV340 - Programming Manual - EN - NVE61643 - 06Hậu PhạmNessuna valutazione finora
- Computer Science & Engineering: Branch: All Branches of B.TechDocumento9 pagineComputer Science & Engineering: Branch: All Branches of B.TechBella HadidNessuna valutazione finora
- Acer Ferrari 3200 3400 1 Quanta ZI5 - Rev1ADocumento32 pagineAcer Ferrari 3200 3400 1 Quanta ZI5 - Rev1AdanielNessuna valutazione finora
- The Big Problem With Renewable EnergyDocumento2 pagineThe Big Problem With Renewable EnergyDiego Acevedo100% (1)
- A Seminar On Rotating BuildingDocumento20 pagineA Seminar On Rotating BuildingManoj Janardan Jayashree Terekar81% (16)
- Assembly-Line Balancing: A Valuable Tool For Increasing EfficiencyDocumento20 pagineAssembly-Line Balancing: A Valuable Tool For Increasing Efficiencyaqsa imranNessuna valutazione finora
- The Roles, Artifacts, Ceremonies and Benefits of Agile Scrum (38Documento14 pagineThe Roles, Artifacts, Ceremonies and Benefits of Agile Scrum (38Romali DasNessuna valutazione finora
- DCS LowresDocumento2 pagineDCS LowresLittle BigdoeuNessuna valutazione finora
- ITSM Awareness - McKinley - HandoutsDocumento54 pagineITSM Awareness - McKinley - HandoutsNinoslav MitićNessuna valutazione finora
- Service Manual DS-870 - DS-970 Rev CDocumento78 pagineService Manual DS-870 - DS-970 Rev CFelix Martinez PimentelNessuna valutazione finora
- Apple's Winning Marketing StrategiesDocumento99 pagineApple's Winning Marketing StrategiesJames JosipNessuna valutazione finora
- ANSI SLAS 4-2004 Standard for Microplate Well PositionsDocumento13 pagineANSI SLAS 4-2004 Standard for Microplate Well PositionsnikkiharNessuna valutazione finora
- Directview Classic CR Theory GuideDocumento113 pagineDirectview Classic CR Theory GuideMarckus Brody100% (1)
- Cassette Cool Only / Heat Pump 10 SEER R22Documento2 pagineCassette Cool Only / Heat Pump 10 SEER R22bram samyNessuna valutazione finora
- Angelicum Immanuel Montessori - ThesisDocumento60 pagineAngelicum Immanuel Montessori - ThesisIan GuevarraNessuna valutazione finora
- Data Download HGM410N HGM420N V1.2 enDocumento36 pagineData Download HGM410N HGM420N V1.2 enAnonymous vqsuRy100% (1)
- MC3425P1Documento13 pagineMC3425P1Syed Khawar MukhtarNessuna valutazione finora
- GS-KB55S Operating InstuctionsDocumento8 pagineGS-KB55S Operating InstuctionsPiero CaprettiNessuna valutazione finora
- Huawei HCNA-VC Certification TrainingDocumento3 pagineHuawei HCNA-VC Certification TrainingArvind JainNessuna valutazione finora
- Engine Parts Listing with 40 PartsDocumento9 pagineEngine Parts Listing with 40 PartsGeno CideNessuna valutazione finora
- Rewriting Continuous Ink Jet Printing RulesDocumento2 pagineRewriting Continuous Ink Jet Printing RulesAnastasia Lova DiantoroNessuna valutazione finora
- Chapter 3 PCM and TDMDocumento49 pagineChapter 3 PCM and TDMjudgelightNessuna valutazione finora
- Binder1 PDFDocumento94 pagineBinder1 PDFrakeshNessuna valutazione finora
- 4 Dipole Band III PanelDocumento1 pagina4 Dipole Band III PanelJina Paola Alvarez HernandezNessuna valutazione finora
- h8115 Vmware Vstorage Vmax WPDocumento0 pagineh8115 Vmware Vstorage Vmax WPAshish SinghNessuna valutazione finora
- 3G Counter LevelDocumento27 pagine3G Counter LevelDjungdjunan ArdyNessuna valutazione finora
- LIVE MIGRATION ANALYSIS IN DOCKER USING CRIUDocumento54 pagineLIVE MIGRATION ANALYSIS IN DOCKER USING CRIUmutiaraNessuna valutazione finora
- AMN ReportDocumento86 pagineAMN ReportHaniNessuna valutazione finora
- IISP 2020 - B K RoyDocumento37 pagineIISP 2020 - B K RoyHimangshu DekaNessuna valutazione finora
- Saes o 204Documento7 pagineSaes o 204suresh100% (1)