Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
TABK Pert10pROCESS cONTROL
Caricato da
Aisyah Maharani0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
23 visualizzazioni15 pagineCopyright
© © All Rights Reserved
Formati disponibili
PDF, TXT o leggi online da Scribd
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
© All Rights Reserved
Formati disponibili
Scarica in formato PDF, TXT o leggi online su Scribd
0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
23 visualizzazioni15 pagineTABK Pert10pROCESS cONTROL
Caricato da
Aisyah MaharaniCopyright:
© All Rights Reserved
Formati disponibili
Scarica in formato PDF, TXT o leggi online su Scribd
Sei sulla pagina 1di 15
Process control
• Bagaimana terjadinya pengendalian proses
• Komponen apa dari sistem Informasi yang
bertanggung jawab akan pengendalian
process
Processing controls
• Processing control subsystem is responsible
for computing, sorting, classifying, and
summarizing data.
• Major Components are
– Central Processing on which programs are
executed
– Real and Virtual memory in which program and
data are stored
– Operating System that manages system
resources
– Application program that execute instructions to
achieve specific user requirements
10/4/11 ROn Weber, Information System
Control and Audits
Processing controls:
Central Processing
• Four type of controls are used to reduce expected
looses from errors and irregularities associated with
the central processor.
• Four type of control are used
– Error processors can be detected via parity checks or be
corrected by attempting to execute failed instructions
again.
– To prevent irregularities, privileged instruction can be
executed only if the processor is in a supervisor state.
– Timing controls can be used to prevent the processors
remaining in an endless loop because of a program error
– Processor components can be replicated to allow
processing to continue in the event that a processor
component fails
10/4/11 ROn Weber, Information System
Control and Audits
Processing controls
Real and Virtual memory
• Two type of controls are used to reduce
expected looses from errors and irregularities
associated with real memory.
• Two type of controls
– Memory errors can be detected via parity check
and hamming codes. Hamming codes also allow
errors to be corrected
– Access control, which are implemented via
boundary registered can be used to ensure one
process does not gain authorized access to the
real memory assigned to another process
10/4/11 ROn Weber, Information System
Control and Audits
Processing controls
Real and Virtual memory
• Virtual memory exist when the addressable
storage space is larger than the available real
memory space.
• Two type of controls can be exercised over
blocks of virtual memory.
– The addressing mechanism should be check that
the memory reference is within the bounds of the
block allocated to the process.
– An access control mechanism should check to
see that the actions a process want to exercise
on a block are within allowed set of privileges.
10/4/11 ROn Weber, Information System
Control and Audits
Processing Controls
Operating System
• A reliable operating system achieves five
goals
– It protects itself from user process
– It protects users from one another
– It protects user from themselves
– It protects itself from itself
– It brings operation to an orderly halt in the
event of environment failure
10/4/11 ROn Weber, Information System
Control and Audits
Processing controls
Operating System
• There are four type of threats to operating
system integrity
– Privileged personnel abuse their powers
– Would be penetrators deceived privilege personnel
into giving them special powers
– Special devices are used to detect electromagnetic
radiation, emit electromagnetic radiation or wiretap
communication line
– Would be penetrators interact with an operating
system to determine and exploit a flaw in the system
10/4/11 ROn Weber, Information System
Control and Audits
Processing controls
Operating System
• Operating system integrity can be
breached via two types of covert
channel
– A process can communicate
confidential information to another
process by changing the value of any
state variables in the system
– Process by changing the time that the
system take to complete a function.
10/4/11 ROn Weber, Information System
Control and Audits
Processing controls
• Operating system flaw (cacat) arise for two
reasons
– Access control policy designed for the system
is defective
– Access control policy is implemented
incorrectly in the operating system
10/4/11 ROn Weber, Information System
Control and Audits
Processing controls
• To improve the design and implementation of
the security features in an operating system,
reference monitors area sometimes used.
• Reference monitor is an abstract mechanism
that check ach request by a subject to user
an object compiles with a security policy.
• A reference monitors is implemented via a
security kernel, which is a mechanism
supported by either hardware, firmware or
software
10/4/11 ROn Weber, Information System
Control and Audits
Processing controls
• Application software can exercised three
levels of checks in the processing subsystem
– Field checks which evaluate whether field
overflow or out of range values have occurred
– Record check which evaluate whether the content
of a field are reasonable or whether a field has
the correct sign
– File Check which employ cross footing and
control totals to check overall processing is
accurate and complete.
10/4/11 ROn Weber, Information System
Control and Audits
Processing controls
• The reliability of application software can be improved if
programmer use good programming style in the software they
write.
– They should handle rounding correctly when the level of
precision required for an arithmetic is less than the level of
precocious actually calculated
– Print run to run control totals to allow users to check the
accuracy and completeness of application program processing
– Minimize human intervention in providing parameter values to
determine the type of processing to undertaken
– Understand hardware/software numerical hazard when writing
program that undertake numerical calculations
– Use redundant routine to cross check the accuracy of complex
numerical calculation
– Avoid closed routine that assume the existence of a values when
the test for all other values fails
10/4/11 ROn Weber, Information System
Control and Audits
Processing controls
• Accounting audit trail in the
processing subsystem must allow
processing to be traced and
replicated. If transaction are triggered
by some event, the audit trail must
show the event that triggered the
transaction and the nature of the
processing undertake as a result
10/4/11 ROn Weber, Information System
Control and Audits
Processing controls
• An important existence control in the
processing subsystem is a checkpoint/restart
facility. Checkpoint/restart facilities allow
programs to be established at some period.
Valid intermediate point in their processing
and restarted from that point. data does not
have to be processed from scratch, Careful
control must exercised over
checkpoint/restart logs. However, because
unauthorized change to a log can result in
integrity breaches
10/4/11 ROn Weber, Information System
Control and Audits
Potrebbero piacerti anche
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (121)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (588)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (400)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2259)
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (345)
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (895)
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (74)
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- SLT Replication TechonologyDocumento53 pagineSLT Replication TechonologyKoushik Pal100% (1)
- NIOS CLIGuide 8.2 PDFDocumento234 pagineNIOS CLIGuide 8.2 PDFrhideNessuna valutazione finora
- Principles of Unix System Management - Solaris 8Documento186 paginePrinciples of Unix System Management - Solaris 8Venkateswara Reddy VNessuna valutazione finora
- Tessent Ijtag ManualDocumento10 pagineTessent Ijtag ManualJecsNessuna valutazione finora
- Confidential NOT FOR External USE: Operator'S ManualDocumento142 pagineConfidential NOT FOR External USE: Operator'S ManualEnrique Potrero100% (1)
- Vyos Routing, Failover - Networking - SpiceworksDocumento4 pagineVyos Routing, Failover - Networking - SpiceworksDavyAvicenneNessuna valutazione finora
- Lab Session # 3 Complex Logic Design (Code Converter) : Figure 1: Multi-Input To Multi-Output CircuitDocumento10 pagineLab Session # 3 Complex Logic Design (Code Converter) : Figure 1: Multi-Input To Multi-Output CircuitAhmad M. HammadNessuna valutazione finora
- Kubernetes 1Documento3 pagineKubernetes 1AymenNessuna valutazione finora
- Aspire 5670 (Quanta ZB1) SchematicsDocumento50 pagineAspire 5670 (Quanta ZB1) SchematicsjeanpellNessuna valutazione finora
- Seminar - Adiabatic Logic DesignDocumento24 pagineSeminar - Adiabatic Logic DesignLakshmi Sri K VNessuna valutazione finora
- Type ScriptDocumento119 pagineType ScriptTrung TrungNessuna valutazione finora
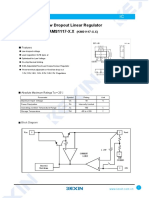
- SMD Type IC: Low Dropout Linear Regulator AMS1117-X.XDocumento3 pagineSMD Type IC: Low Dropout Linear Regulator AMS1117-X.XcarlosmarciosfreitasNessuna valutazione finora
- AUTOSAR RS SystemTemplateDocumento25 pagineAUTOSAR RS SystemTemplateAkinwumi Mayowa OtunbqNessuna valutazione finora
- Mips ReferenceDocumento24 pagineMips ReferencethắngNessuna valutazione finora
- Exp 5 Intro To AC Phase ControlDocumento8 pagineExp 5 Intro To AC Phase Controlusmpowerlab67% (3)
- Self Study Guidelines To JAVA SEDocumento4 pagineSelf Study Guidelines To JAVA SEAnjana Jayasekara100% (1)
- Datasheet SQ R 2.41Documento2 pagineDatasheet SQ R 2.41Alejandro CarhuacusmaNessuna valutazione finora
- OT ES .IN: Mobile Computing (Ecs-087)Documento63 pagineOT ES .IN: Mobile Computing (Ecs-087)Ankur KUMAR AGGARWAL100% (1)
- Lab Experiment # 9: Implementation and Verification of Truth Table of 8x3 EncoderDocumento3 pagineLab Experiment # 9: Implementation and Verification of Truth Table of 8x3 EncoderSaad khanNessuna valutazione finora
- Dmesg TutorialDocumento2 pagineDmesg TutorialSlim ShadyNessuna valutazione finora
- Int CATALOGUE TransmetteursDocumento23 pagineInt CATALOGUE TransmetteurssarahrouNessuna valutazione finora
- Tellegen's Theorem: Basic Electrical Engineering ProjectDocumento13 pagineTellegen's Theorem: Basic Electrical Engineering Projectbrock lesnarNessuna valutazione finora
- Oracle 1z0 1084 20 PDFDocumento6 pagineOracle 1z0 1084 20 PDFSaquib.MahmoodNessuna valutazione finora
- Fortigate Cookbook 504Documento220 pagineFortigate Cookbook 504regabriNessuna valutazione finora
- Ogdcl Test 2018Documento8 pagineOgdcl Test 2018MuhammadNaveed100% (1)
- Lab Assignment-6Documento8 pagineLab Assignment-6Arjun ArjunNessuna valutazione finora
- Ds Gs78lxx (F) Rev 1.0Documento9 pagineDs Gs78lxx (F) Rev 1.0Juan Manuel Ibarra ZapataNessuna valutazione finora
- Module-Week 5Documento2 pagineModule-Week 5Maria Christina ManzanoNessuna valutazione finora
- Hdwacsuauts V3.1Documento51 pagineHdwacsuauts V3.1VALERIE JADE PIAOANNessuna valutazione finora
- Study Finds That To Fully Understand Potential Cloud Performance Requires Looking at More Than SPECrate 2017 Integer ScoresDocumento3 pagineStudy Finds That To Fully Understand Potential Cloud Performance Requires Looking at More Than SPECrate 2017 Integer ScoresPR.comNessuna valutazione finora