Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
QUIZ 1 Lessons 1-3
Caricato da
AileenD.Enriquez50%(2)Il 50% ha trovato utile questo documento (2 voti)
2K visualizzazioni2 pagineQuiz
Titolo originale
QUIZ 1 lessons 1-3
Copyright
© © All Rights Reserved
Formati disponibili
DOCX, PDF, TXT o leggi online da Scribd
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoQuiz
Copyright:
© All Rights Reserved
Formati disponibili
Scarica in formato DOCX, PDF, TXT o leggi online su Scribd
50%(2)Il 50% ha trovato utile questo documento (2 voti)
2K visualizzazioni2 pagineQUIZ 1 Lessons 1-3
Caricato da
AileenD.EnriquezQuiz
Copyright:
© All Rights Reserved
Formati disponibili
Scarica in formato DOCX, PDF, TXT o leggi online su Scribd
Sei sulla pagina 1di 2
QUIZ 1: EMPOWERMENT TECHNOLOGIES
WRITE TRUE OR FALSE (T OR F)
1. ICT stands for Information and Communication Technology
2. International companies call Philippines as the “ICT Hub of Asia”
3. Convergence is the synergy of technological advancement to work on a
similar goal.
4. Social Media is a website that enables users to create, discuss and exchange
user generated content.
5. A virus is a malware that multiplies and infects other computer through flash
drives.
6. Android is an operating system for mobile phones.
7. Blackberry OS are intended only for Blackberry phones.
8. Symbian is smartphone OS use by Nokia devices.
9. Social News can allow user to post news item or link from other news sources.
10. Microblogging are sites that focus on short updates from the user.
WRITE THE LETTER OF THE CORRECT ANSWER.
11. What online platform does the figure represents?
a. Collaboration c. Social Media
b. Blogging d. Image
e. /Video Hosting
12. What online platform is a website that contains online personal reflections,
comments, and often hyperlinks, videos, and photographs provided by the
writer?
a. Presentation / c. E-learning
Visualization d. Blogging
b. Web page creation
13. 6. What online platform does Google Drive, Trello, Kanban, Slack, and
Skype applications represents?
a. Collaboration c. Blogging
b. Cloud computing d. Web page creation
14. 10. Which statement is true to describe Social Media Platform?
A. Social Media Platform is a collective of online communications channels
dedicated to community-based input, interaction, content-sharing and
collaboration.
B. Social Media Platforms are websites and applications dedicated to forums,
micro-blogging, social networking, social bookmarking and social curation
a. A and B are both true c. A is false, B is true
b. A is true, B is false d. A and B are both false
15. What is cloud computing?
a. The practice of using a network of remote servers hosted on the
Internet to store, manage, and process data.
b. The tools that focus on a model that emphasizes the collaborative
nature of the web
c. The art of storing data locally.
d. The process of saving data to the local network.
16. One of the major benefit of using online platforms is to free-up hardware
usage.t
a. true c. maybe
b. false
17. a provider that transports information electronically and can encompass
public and private companies in telecom, internet, cable, satellite and
managed system service
a. online banking c. payment system
b. communication d. cloud computing
services
18. an online platform that allows users to create and manage campaigns,
generate reports and retrieve information
a. online banking c. payment system
b. advertisement d. cloud computing
platforms
19. online platforms where we can create presentations more creatively
a. creative content c. payment system
outlets d. cloud computing
b. online banking
20. designed to search information on the world wide web
a. creative content c. payment system
outlets d. web search engines
b. online banking
LESSON 3 Online Safety, Security, Ethics
WRITE TRUE OR FALSE (T OR F)
21. Do not use pirated software.
22. Think before you click
23. Do not just accept terms and conditions; read it.
24. Do not share your password to anyone.
25. Don’t post anything about future vacation.
26. Add friends you know in real life.
27. Avoid visiting untrusted website.
28. Make your Wi-Fi password private.
29. Do not reply to a suspicious e-mail.
30. Do not talk to strangers’ weather online or face to face.
LESSON 3 Online Safety, Security, Ethics
WRITE THE LETTER OF THE CORRECT ANSWER
31. Designed to send you advertisement.
a. adware b. trojan c. internet d. pharming
32. Replicates and can transfer from one computer to another.
a. virus b. spyware c. spam d. malware.
33. Exploit the DNS system.
a. pharming b. rogue c. malware d. spam
34. Runs in the background and monitors what you are doing. a. spyware b. spam
c. trojan d. keylogger
35. Unwanted emails, mostly from bots.
a. spam b. rogue c. malware d. net
36. Disguise as a useful program but it’s not.
a. trojan b. rogue c. keylogger d. worm
37. A malicious software. a. malware b. spyware c. spam d. keylogger
38. Used to record the keystrokes done by the user. a. keylogger b. spam c. trojan
d. worm
39. Malicious program like “LOVE BUG” created by a Filipino programmer. a. worm
b. virus c. malware d. trojan
40. Tricks the user into posting that is a security software. a. Phishing b. virus c.
Pharming d. spam
Potrebbero piacerti anche
- Midterm Exam in e Tech 2Documento3 pagineMidterm Exam in e Tech 2einrevNessuna valutazione finora
- Empowerment Technologies Prelim 1st QuarterDocumento4 pagineEmpowerment Technologies Prelim 1st QuarterArcane Haste100% (1)
- Summative For Empowerment TechnologyDocumento5 pagineSummative For Empowerment Technologycristine mundo100% (1)
- Final - Exam - in - Empowerment - Technologies-ANSWER KEYDocumento2 pagineFinal - Exam - in - Empowerment - Technologies-ANSWER KEYBernardAbuloc100% (5)
- Final Exam in Empowerment TechnologiesDocumento3 pagineFinal Exam in Empowerment TechnologiesBernardAbuloc100% (1)
- Final - Exam - in - Empowerment - Technologies End Term (AutoRecovered) Answer KeyDocumento3 pagineFinal - Exam - in - Empowerment - Technologies End Term (AutoRecovered) Answer KeyBernardAbulocNessuna valutazione finora
- 3rd Quarterly Exam On Empowerment Technologies (WITH ANSWER)Documento3 pagine3rd Quarterly Exam On Empowerment Technologies (WITH ANSWER)JanCarlBriones75% (8)
- EMPOWERMENT OF TECHNOLOGIES 40 Item SUMMATIVE TESTDocumento2 pagineEMPOWERMENT OF TECHNOLOGIES 40 Item SUMMATIVE TESTJhun PegardsNessuna valutazione finora
- Summative Test in Etech q1 Week 1-2Documento7 pagineSummative Test in Etech q1 Week 1-2Frances A. PalecNessuna valutazione finora
- 1st Quarter Exam For 2nd Semester - Empowerment TechnologyDocumento7 pagine1st Quarter Exam For 2nd Semester - Empowerment TechnologyGraciously ElleNessuna valutazione finora
- Final Exam in Empowerment TechnologiesDocumento3 pagineFinal Exam in Empowerment TechnologiesPangangan NHS100% (3)
- Empowerment Tech MidtermDocumento4 pagineEmpowerment Tech MidtermcocopitlabmixNessuna valutazione finora
- Pre Test in Empowerment TechnologiesDocumento3 paginePre Test in Empowerment TechnologiesLouigene Tinao Donato75% (8)
- Empowerment With KeyDocumento3 pagineEmpowerment With KeyChawNessuna valutazione finora
- 1st Summative E-Tech 2019-2020Documento2 pagine1st Summative E-Tech 2019-2020Edinyn Chavez EscardaNessuna valutazione finora
- Empowerment Technologies 1st Quarter ExamDocumento2 pagineEmpowerment Technologies 1st Quarter ExamEi100% (1)
- EmTech TG Acad v5 112316Documento87 pagineEmTech TG Acad v5 112316Arvin Barrientos Bernesto67% (3)
- Grade 11 EmTech Exam 4th FINALDocumento6 pagineGrade 11 EmTech Exam 4th FINALBill VillonNessuna valutazione finora
- Empowerment Technologies 1st Periodical TestDocumento6 pagineEmpowerment Technologies 1st Periodical TestApril Claire Pineda Manlangit83% (6)
- Empowerment Technologies SyllabusDocumento6 pagineEmpowerment Technologies SyllabusJonalyn Laroya Reoliquio89% (9)
- Grade 11 EmTech Exam 3rd FINALDocumento7 pagineGrade 11 EmTech Exam 3rd FINALBill VillonNessuna valutazione finora
- Emtech First Quarter ExamDocumento3 pagineEmtech First Quarter ExamGemmaAlejandroNessuna valutazione finora
- Empowerment Technologies (E-Tech) - Introduction To ICTDocumento2 pagineEmpowerment Technologies (E-Tech) - Introduction To ICTGeorge Silandote85% (59)
- EMPOWERMENT TECHNOLOGY Lesson 1Documento80 pagineEMPOWERMENT TECHNOLOGY Lesson 1row row100% (5)
- 1st Quarter Exam Empowerment TechDocumento3 pagine1st Quarter Exam Empowerment TechPrinCe Daryl GarCia100% (4)
- Empowerment Technologies Semi Lesson PlanDocumento4 pagineEmpowerment Technologies Semi Lesson PlanBrecht Agnila Tampus100% (2)
- Empowerment Technologies Final ExamDocumento2 pagineEmpowerment Technologies Final ExamLoixeLicawanCańete90% (71)
- Empowerment Final ExamDocumento3 pagineEmpowerment Final ExamChristan P. Ondevilla100% (1)
- 1st SUMMATIVE TEST IN-EMPOWERMENT-TECHNOLOGIESDocumento3 pagine1st SUMMATIVE TEST IN-EMPOWERMENT-TECHNOLOGIESAileenD.Enriquez88% (8)
- Midterm Examination in Empowerment TechnologiesDocumento3 pagineMidterm Examination in Empowerment TechnologiesRowel Elca90% (21)
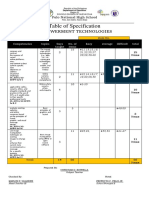
- TOS EmpowermentDocumento6 pagineTOS EmpowermentWendell Hernandez94% (17)
- Final Exam in Emp. Tech.Documento3 pagineFinal Exam in Emp. Tech.Rowel Elca100% (1)
- Final Exam in Empowerment Technologies Version 2Documento2 pagineFinal Exam in Empowerment Technologies Version 2Pangangan NHSNessuna valutazione finora
- Module - 3 - Empowerment Technology - Week 3-4Documento11 pagineModule - 3 - Empowerment Technology - Week 3-4Jay Dhel75% (4)
- LAS in EMPOWERMENT TECHNOLOGY QUARTER 2 Week 1-2 FINALDocumento12 pagineLAS in EMPOWERMENT TECHNOLOGY QUARTER 2 Week 1-2 FINALAldrin Dela CruzNessuna valutazione finora
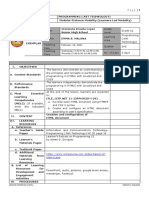
- Empowerment Technology Lesson 1 DLLDocumento3 pagineEmpowerment Technology Lesson 1 DLLGian Carlos Bolaños100% (1)
- Empowerment Technologies - Lesson 3Documento8 pagineEmpowerment Technologies - Lesson 3Imie Omamalin100% (6)
- Summative Test in Empowerment Week 1 4Documento4 pagineSummative Test in Empowerment Week 1 4Fatima Norean G. NavaltaNessuna valutazione finora
- First Quarter Assessment Empowerment Technology 12Documento4 pagineFirst Quarter Assessment Empowerment Technology 12ANTHONY AQUINONessuna valutazione finora
- Empowerment Technologies: Quarter 2 - Module 6: Multimedia and ICTDocumento16 pagineEmpowerment Technologies: Quarter 2 - Module 6: Multimedia and ICTEarl Lawrence Lacubtan0% (1)
- Table of Specification: Empowerment TechnologiesDocumento1 paginaTable of Specification: Empowerment TechnologiesChristian D. Estrella100% (1)
- Summative Test in E-Tech 3rd QuarterDocumento1 paginaSummative Test in E-Tech 3rd QuarterMej AC100% (1)
- 2nd Quarter Exam Empowerment - TechnologiesDocumento3 pagine2nd Quarter Exam Empowerment - Technologieskathryn soriano100% (10)
- Principles of Visual Message Design Using InfographicsDocumento28 paginePrinciples of Visual Message Design Using InfographicsLR TechNessuna valutazione finora
- Lesson Plan in Empowerment Technologies Grade 11 I. ObjectivesDocumento2 pagineLesson Plan in Empowerment Technologies Grade 11 I. ObjectivesJayram JavierNessuna valutazione finora
- 2nd Quarter Exam With TOS MIL Grade 12Documento1 pagina2nd Quarter Exam With TOS MIL Grade 12Ki KhaiiNessuna valutazione finora
- Lesson-2 EMPOWERMENT TECHNOLOGYDocumento40 pagineLesson-2 EMPOWERMENT TECHNOLOGYeldefonso lagulay100% (6)
- Quarter/Week Most Essential Learning Competencies Quarter 1 Week 1 To Week 4Documento2 pagineQuarter/Week Most Essential Learning Competencies Quarter 1 Week 1 To Week 4Kristel Gail Santiago Basilio100% (31)
- EMPOWERMENT TECHNOLOGY Q2 COT (Autosaved)Documento19 pagineEMPOWERMENT TECHNOLOGY Q2 COT (Autosaved)Arvin Barrientos Bernesto100% (1)
- Etech 1ST QTRDocumento4 pagineEtech 1ST QTRJohnArgielLaurenteVictor100% (4)
- EMPOWERMENT TECHNOLOGY Lesson 1 - Introduction To Empowerment TechnologyDocumento10 pagineEMPOWERMENT TECHNOLOGY Lesson 1 - Introduction To Empowerment TechnologyRioLeongson100% (2)
- Rich Content in The Online Environment and The User ExperienceDocumento6 pagineRich Content in The Online Environment and The User ExperienceDina Navarro Diestro100% (2)
- Rich Content in The Online Environment and The User ExperienceDocumento14 pagineRich Content in The Online Environment and The User ExperienceJunela CharisNessuna valutazione finora
- DAILY LESSON PLAN EmpowermentDocumento2 pagineDAILY LESSON PLAN EmpowermentNiel Colis100% (2)
- 2nd Quarter Examination Grade 11 - Empowerment Technologies: Dr. Cecilio Putong National High SchoolDocumento2 pagine2nd Quarter Examination Grade 11 - Empowerment Technologies: Dr. Cecilio Putong National High SchoolBrian C. RosalNessuna valutazione finora
- ET - Midterm 2023 2024Documento2 pagineET - Midterm 2023 2024Paul AniceteNessuna valutazione finora
- TQ in EMPOWERMENTDocumento6 pagineTQ in EMPOWERMENTVanessa HaoNessuna valutazione finora
- EMPOWERMENT TECHNOLOGIES 1stSUMMATIVEDocumento2 pagineEMPOWERMENT TECHNOLOGIES 1stSUMMATIVEChristian Lloyd ReandinoNessuna valutazione finora
- Empowerment Tech Summative Test 1stQDocumento4 pagineEmpowerment Tech Summative Test 1stQAlzen GalaponNessuna valutazione finora
- 01 QuizDocumento3 pagine01 QuizKent Luis C. BactolNessuna valutazione finora
- Be Our Partner!: You May Help Us Reach Out To More Learners byDocumento1 paginaBe Our Partner!: You May Help Us Reach Out To More Learners byAileenD.EnriquezNessuna valutazione finora
- Mil - Weekly Home Learning Plan For Modular Distance LearningDocumento9 pagineMil - Weekly Home Learning Plan For Modular Distance LearningChi de la Torre100% (1)
- The Big Five Training and Assessment Center. Inc.: Welcome!Documento14 pagineThe Big Five Training and Assessment Center. Inc.: Welcome!AileenD.EnriquezNessuna valutazione finora
- Modified Learner Enrollment and Survey Form: Grade Level and School InformationDocumento3 pagineModified Learner Enrollment and Survey Form: Grade Level and School InformationAileenD.EnriquezNessuna valutazione finora
- Lesson Exemplar Java Programming ENRIQUEZDocumento19 pagineLesson Exemplar Java Programming ENRIQUEZAileenD.EnriquezNessuna valutazione finora
- Competency Based Learning MaterialDocumento52 pagineCompetency Based Learning MaterialAileenD.Enriquez33% (3)
- Lesson Exemplar Java Programming ENRIQUEZDocumento19 pagineLesson Exemplar Java Programming ENRIQUEZAileenD.EnriquezNessuna valutazione finora
- SHS Weekly Home Learning PlanDocumento8 pagineSHS Weekly Home Learning PlanAileenD.EnriquezNessuna valutazione finora
- Lesson Exemplar Programming 12 Quarter 4 Week 1 and 2Documento3 pagineLesson Exemplar Programming 12 Quarter 4 Week 1 and 2AileenD.Enriquez100% (1)
- Lesson Exemplar Programming 12 Quarter 4 Week 3 and 4Documento4 pagineLesson Exemplar Programming 12 Quarter 4 Week 3 and 4AileenD.EnriquezNessuna valutazione finora
- PROGRAMMING in .Net Technology (LAS) QUARTER 2 - For LearnersDocumento29 paginePROGRAMMING in .Net Technology (LAS) QUARTER 2 - For LearnersAileenD.EnriquezNessuna valutazione finora
- LE - Weeks 7-9 Programming 12 (.Net Technology Programming)Documento10 pagineLE - Weeks 7-9 Programming 12 (.Net Technology Programming)AileenD.EnriquezNessuna valutazione finora
- Lesson Exemplar Programming 12 Quarter 4 Week 6 and 7Documento3 pagineLesson Exemplar Programming 12 Quarter 4 Week 6 and 7AileenD.EnriquezNessuna valutazione finora
- Lesson Exemplar Programming 12 Quarter 4 Week 5Documento5 pagineLesson Exemplar Programming 12 Quarter 4 Week 5AileenD.EnriquezNessuna valutazione finora
- ICT Week 3-6 LPDocumento21 pagineICT Week 3-6 LPAileenD.EnriquezNessuna valutazione finora
- ICT Week 3-6 LPDocumento21 pagineICT Week 3-6 LPAileenD.EnriquezNessuna valutazione finora
- Everyone Should Learn To DesignDocumento1 paginaEveryone Should Learn To DesignAileenD.EnriquezNessuna valutazione finora
- Everyone Should Learn To DesignDocumento1 paginaEveryone Should Learn To DesignAileenD.EnriquezNessuna valutazione finora
- Le Precal q2 A.enriquezDocumento5 pagineLe Precal q2 A.enriquezAileenD.EnriquezNessuna valutazione finora
- Le Precal q2 A.enriquezDocumento5 pagineLe Precal q2 A.enriquezAileenD.EnriquezNessuna valutazione finora
- Programming 12 Week 1 LP (Edited)Documento8 pagineProgramming 12 Week 1 LP (Edited)AileenD.EnriquezNessuna valutazione finora
- Number System Conversions: Name: DateDocumento2 pagineNumber System Conversions: Name: DateAileenD.EnriquezNessuna valutazione finora
- Programming .Net Week 1 LPDocumento38 pagineProgramming .Net Week 1 LPAileenD.EnriquezNessuna valutazione finora
- Programming .Net Week 1 and 2 LP For PrintingDocumento28 pagineProgramming .Net Week 1 and 2 LP For PrintingAileenD.EnriquezNessuna valutazione finora
- Guess The WordDocumento33 pagineGuess The WordAileenD.EnriquezNessuna valutazione finora
- Programming 11 Week 1 LP (Edited)Documento8 pagineProgramming 11 Week 1 LP (Edited)AileenD.EnriquezNessuna valutazione finora
- Programming .Net Week 1 LPDocumento38 pagineProgramming .Net Week 1 LPAileenD.EnriquezNessuna valutazione finora
- Programming .Net Week 1 LPDocumento38 pagineProgramming .Net Week 1 LPAileenD.EnriquezNessuna valutazione finora
- Exercise 1 Use CaseDocumento3 pagineExercise 1 Use CaseAileenD.EnriquezNessuna valutazione finora
- C++ Programming 3RD Quarter TestDocumento2 pagineC++ Programming 3RD Quarter TestAileenD.EnriquezNessuna valutazione finora
- By: Prof. Riyaz A. SheikhDocumento14 pagineBy: Prof. Riyaz A. SheikhcatchriyazNessuna valutazione finora
- Uc4 User Guide PDFDocumento268 pagineUc4 User Guide PDFAjay SinghNessuna valutazione finora
- MODULE 3 Week 4 Image Editing TLE 025 Introduction To ICT Specialization 2Documento22 pagineMODULE 3 Week 4 Image Editing TLE 025 Introduction To ICT Specialization 2Claresa AlbesaNessuna valutazione finora
- Kon Boot HelpDocumento33 pagineKon Boot Helptmv003Nessuna valutazione finora
- Tech Note FBB E325727 FleetOne SW Release 125 Rev BDocumento5 pagineTech Note FBB E325727 FleetOne SW Release 125 Rev BCarlos CoelhoNessuna valutazione finora
- Github CheatsheetDocumento6 pagineGithub CheatsheetjohnNessuna valutazione finora
- Form 9 2023, SSM (CTC)Documento2 pagineForm 9 2023, SSM (CTC)Manisa LaalNessuna valutazione finora
- GDSGDocumento2 pagineGDSGNoorul HuqNessuna valutazione finora
- 48x36 ResearchPosterDocumento1 pagina48x36 ResearchPosterAbbas ChokorNessuna valutazione finora
- Test Preparation Group (Electrical & Electronics)Documento1 paginaTest Preparation Group (Electrical & Electronics)AmirSaeedNessuna valutazione finora
- CCBU Ordering GuideDocumento202 pagineCCBU Ordering GuideHugo Cesar Flores OrtizNessuna valutazione finora
- Modify The Mouse Settings From The Command Line - Ghacks Tech NewsDocumento4 pagineModify The Mouse Settings From The Command Line - Ghacks Tech NewsxibulaNessuna valutazione finora
- 111Documento1 pagina111Rakesh KumarNessuna valutazione finora
- Final Year Project List Class Name BSCSDocumento2 pagineFinal Year Project List Class Name BSCSHamna HamnaNessuna valutazione finora
- U5-01 Content Calendar enDocumento11 pagineU5-01 Content Calendar enRosy RuizNessuna valutazione finora
- Apex DT-250Documento50 pagineApex DT-250Lawrence RamseyNessuna valutazione finora
- Sysmon: How To Install, Upgrade, and UninstallDocumento6 pagineSysmon: How To Install, Upgrade, and UninstallDanielNessuna valutazione finora
- Porn FactsDocumento2 paginePorn FactskeithworksNessuna valutazione finora
- Online Pharmacy Store Managment System Project ReportDocumento52 pagineOnline Pharmacy Store Managment System Project ReportpmtallyNessuna valutazione finora
- Setting Up Squid Proxy ServerDocumento22 pagineSetting Up Squid Proxy ServerRamesh Kumar VaradharajanNessuna valutazione finora
- E-Business Suite Accreditation Assessment - MOS19Documento5 pagineE-Business Suite Accreditation Assessment - MOS19jamliNessuna valutazione finora
- Google Play App - Google SearchDocumento1 paginaGoogle Play App - Google SearchMehdi JafariNessuna valutazione finora
- Power Center WebServices UserGuideDocumento78 paginePower Center WebServices UserGuideLakshmi ShenoyNessuna valutazione finora
- InstagramHacks Guide enDocumento9 pagineInstagramHacks Guide enPenelope MeloNessuna valutazione finora
- Types of Operating SystemsDocumento4 pagineTypes of Operating Systemsamna sadiqNessuna valutazione finora
- Guide To Using The SAP Integration PlugDocumento6 pagineGuide To Using The SAP Integration PlugloribeNessuna valutazione finora
- KMSpico v5.2.1 Instructions InfoDocumento3 pagineKMSpico v5.2.1 Instructions InfoRadwan AhmedNessuna valutazione finora
- Sound Editing LAB: Digital Audio WorkstationsDocumento11 pagineSound Editing LAB: Digital Audio Workstationsapi-427379542Nessuna valutazione finora
- Window 8Documento203 pagineWindow 8Thet Naing HtooNessuna valutazione finora
- Ip 7137 ManualDocumento72 pagineIp 7137 ManualSixtoNessuna valutazione finora