Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
DSS04 Manage Continuity
Caricato da
Pedro MirandaCopyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
DSS04 Manage Continuity
Caricato da
Pedro MirandaCopyright:
Formati disponibili
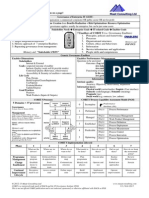
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
DSS04 – Process Setting
Process Description1
Establish and maintain a plan to enable the business and IT to respond to incidents and disruptions in order to continue operation of critical business processes
and required IT services and maintain availability of information at a level acceptable to the enterprise.
Process Purpose Statement1
Continue critical business operations and maintain availability of information at a level acceptable to the enterprise in the event of a significant disruption.
Process Objectives1
The objectives of this assessment are to determine that:
• Business-critical information is available to the business in line with minimum required service levels,
• Sufficient resilience is in place for critical services,
• Service continuity tests have verified the effectiveness of the plan,
• An up-to-date continuity plan reflects current business requirements,
• Internal and external parties have been trained in the continuity plan, and
• BCP changes are identified and implemented.
Process Risk Drivers2
• Accidental destruction of backup data
• Common incidents not solved properly
• Confidential information in the plans compromised
1 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
• Failed communication to internal and external stakeholders
• Failure of alternative decision-making processes
• Failure to recover as expected due to inadequate or outdated training
• Failure to recover business-critical systems and services in a timely manner
• Failure to recover IT systems and services in a timely manner
• Inability to follow up incident resolution
• Inability to locate backup tapes when needed
• Inappropriate recovery plans
• Inappropriate recovery steps and processes
• Incidents not resolved on a timely basis
• Incorrect information gathering
• Increased costs for continuity management
• Increased dependency on key individuals
• Inefficient use of resources
• Insufficient continuity practices
• IT continuity services not managed properly
• Lack of change control procedures
• Lack of required recovery resources
• Loss of data due to disaster
• Not all incidents tracked
• Objectives not met by the recovery plans
• Outdated training schedules
• Plans failing to reflect changes to business needs and technology
• Plans not accessible to all required parties
• Prioritization of incidents failing to reflect business needs
• Prioritization of services recovery not based on business needs
• Recovery plans failing to meet business needs
• Shortcomings in recovery plans
2 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
• Unavailability of backup data and media due to missing documentation in offsite storage
• Unavailability of critical IT resources
• Unavailability of service desk resources
• Upgrades of the plan not performed in a timely manner due to uncontrolled distribution strategies
DSS04 – Process Goal Assessment
DSS04.01 Management Practice1
Define the business continuity policy, objectives and scope. Define business continuity policy and scope aligned with enterprise and stakeholder objectives.
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
DSS04.01.01 - Critical Identify internal and outsourced Determine if the DRP identifies internal and outsourced business processes and service activities
Business Processes business processes and that are critical to the enterprise operations or necessary to meet legal and/or contractual
service activities that are critical obligations.
to the enterprise operations or
necessary to meet legal and/or
contractual obligations.
DSS04.01.02 - Key Identify key stakeholders, roles, Determine if the DRP has identified key stakeholders, roles, and responsibilities for defining and
Stakeholders and responsibilities for defining agreeing on continuity policy and scope.
and agreeing on continuity
policy and scope.
DSS04.01.03 - Continuity Define and document the 1. Determine if the DRP has defined and IT has documented the agreed-on minimum policy
Objectives and Scope agreed-on minimum policy objectives and scope for business continuity and embed the need for continuity planning in the
objectives and scope for enterprise culture.
business continuity and embed
3 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
the need for continuity planning 2. Distribute the questionnaire or ask it of the DRP leadership.
in the enterprise culture.
a. Is there a disaster recovery plan? If a plan exists, when was it last updated?
b. What are the procedures for updating the plan? When was it last changed?
c. Who is responsible for administration or coordination of the plan?
d. Is the plan administrator/coordinator responsible for keeping the plan up-to-date?
e. Is there a disaster recovery implementation team (i.e., the first response team members
who will react to the emergency with immediate action steps)?
f. Where is the disaster recovery plan stored?
g. Where is the implementation team contacts list stored?
h. Where is the backup facility site? Are there alternate sites?
i. What is your schedule for testing and training on the plan?
j. When was the last drill performed?
k. Did the drill include use of the backup facilities? If not, when were the backup facilities last
used? If over 1 year, how has the organization determined that its programs can still run on
the backup equipment?
l. What was the outcome of the drill? How did it improve preparedness?
m. What critical systems are covered by the plan?
n. What systems are not covered by the plan? Why not?
o. Does the plan operate under any assumptions? What are they?
p. What are the procedures for activation of the plan?
q. Are inventories as they relate to your critical systems kept (including LAN servers and
communication devices)?
r. If inventories are kept, where are they stored?
s. Are there formal procedures that specify backup procedures and responsibilities?
t. What functions/systems/components are covered under such procedures?
4 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
u. What training has been given to personnel in using backup equipment and established
procedures?
v. Where is the off-site storage site?
w. Is there a process to perform threat/vulnerability analysis to identify the source and
likelihood of occurrence of specific threats?
x. Have lead times for communication lines and equipment, specialized devices, power
hookups, construction, firewalls, computer configurations, and LAN implementation been
factored into the DRP?
y. Have training sessions been conducted for all relevant personnel on backup, recovery, and
contingency operating procedures?
z. Are there provisions in place to maintain the security of processing functions in case of an
emergency?
aa. Does the plan conform to regulatory and statutory requirements?
bb. Do users know how to recover processing when computing power is restored?
cc. Are listings of current emergency telephone numbers for police, fire department, medical
aid, and company officials strategically located throughout the facility and at off-site
locations?
dd. Has a "worst-case" scenario DRP to recover normal operations within prescribed
timeframes been implemented and tested?
ee. Who contacts the DR Coordinator in the event of a disaster? How about after hours? How
do they know that this is their responsibility?
ff. If there is not a current, fully functional DRP, what is the timeline to have one?
DSS04.01.04 - Essential Identify essential supporting Determine of the DRP has identified essential supporting business processes and related IT
Supporting Processes business processes and related services.
IT services.
5 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
DSS04.02 Management Practice1
Maintain a continuity strategy. Evaluate business continuity management options and choose a cost-effective and viable continuity strategy that will ensure
enterprise recovery and continuity in the face of a disaster or other major incident or disruption.
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
DSS04.02.01 - Potential Identify potential scenarios Determine if IT has identified essential supporting business processes and related IT services.
Scenarios likely to give rise to events that
could cause significant
disruptive incidents.
DSS04.02.02 - BIA Conduct a business impact Obtain and evaluate the business impact analysis that evaluates the impact over time of a
analysis to evaluate the impact disruption to critical business functions and the effect that a disruption would have on them.
over time of a disruption to
critical business functions and
the effect that a disruption
would have on them.
DSS04.02.03 - Recovery Establish the minimum time Understand if the DRP has established the minimum time required to recover a business process
Times required to recover a business and supporting IT based on an acceptable length of business interruption and maximum tolerable
process and supporting IT outage.
based on an acceptable length
of business interruption and
maximum tolerable outage.
DSS04.02.04 - Risk Assess the likelihood of threats 1. Assess whether IT has determined the likelihood of threats that could cause loss of business
Assessment that could cause loss of continuity.
business continuity and identify
measures that will reduce the 2. Determine if a risk analysis has identified measures that will reduce the likelihood and impact
likelihood and impact through through improved prevention and increased resilience.
6 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
improved prevention and
increased resilience.
DSS04.02.05 - Business and Analyze continuity Determine if the DRP has analyzed continuity requirements to identify the possible strategic
Technical Options requirements to identify the business and technical options.
possible strategic business and
technical options.
DSS04.02.06 - Key Decision Determine the conditions and Understand that the DRP determines the conditions and owners of key decisions that will cause
Makers owners of key decisions that the continuity plans to be invoked
will cause the continuity plans
to be invoked
DSS04.02.07 - Resources Identify resource requirements Determine if IT has identified resource requirements and costs for each strategic technical option
and costs for each strategic and make strategic recommendations
technical option and make
strategic recommendations.
DSS04.02.08 - Approvals Obtain executive business Determine if IT has sought and obtained executive business approval for selected strategic
approval for selected strategic options.
options.
7 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
DSS04.03 Management Practice1
Develop and implement a business continuity response. Develop a business continuity plan (BCP) based on the strategy that documents the procedures and
information in readiness for use in an incident to enable the enterprise to continue its critical activities.
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
DSS04.03.01 - Actions and Define the incident response 1. Determine if IT has defined the incident response actions and communications to be taken in
Communications actions and communications to the event of disruption.
be taken in the event of
disruption. Define related roles 2. Determine if there are related defined roles and responsibilities, including accountability for
and responsibilities, including policy and implementation.
accountability for policy and
implementation.
DSS04.03.02 - Operational Develop and maintain Determine if IT has developed and maintains operational BCPs containing the procedures to be
BCPs operational BCPs containing followed to enable continued operation of critical business processes and/or temporary processing
the procedures to be followed arrangements, including links to plans of outsourced service providers.
to enable continued operation
of critical business processes
and/or temporary processing
arrangements, including links to
plans of outsourced service
providers.
DSS04.03.03 - Suppliers and Ensure that key suppliers and 1. Determine if and how IT has ensured that key suppliers and outsource partners have effective
Partners outsource partners have continuity plans in place.
effective continuity plans in
place. Obtain audited evidence 2. Obtain audited evidence, if available.
as required.
8 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
DSS04.03.04 - Recovery Define the conditions and Determine if IT has defined the conditions and recovery procedures that would enable resumption
Procedures recovery procedures that would of business processing, including updating and reconciliation of information databases to preserve
enable resumption of business information integrity.
processing, including updating
and reconciliation of
information databases to
preserve information integrity.
DSS04.03.05 - Resource Define and document the Determine if IT has defined and documented the resources required to support the continuity and
Requirements resources required to support recovery procedures, considering people, facilities and IT infrastructure.
the continuity and recovery
procedures, considering
people, facilities and IT
infrastructure.
DSS04.03.06 - Backup Define and document the Understand that IT has defined and documented the information backup requirements required to
Requirements information backup support the plans, including plans and paper documents as well as data files, and consider the
requirements required to need for security and off-site storage.
support the plans, including
plans and paper documents as
well as data files, and consider
the need for security and off-
site storage.
DSS04.03.07 - Skill Determine required skills for Determine if IT has mapped the required skills for individuals involved in executing the plan and
Requirements individuals involved in procedures.
executing the plan and
procedures.
9 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
DSS04.03.08 - Distribute Distribute the plans and Determine if IT has distributed the plans and supporting documentation securely to appropriately
Plans supporting documentation authorized interested parties and make sure they are accessible under all disaster scenarios.
securely to appropriately
authorized interested parties
and make sure they are
accessible under all
disaster scenarios.
10 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
DSS04.04 Management Practice1
Exercise, test, and review the BCP. Test the continuity arrangements on a regular basis to exercise the recovery plans against predetermined outcomes and to
allow innovative solutions to be developed and help to verify over time that the plan will work as anticipated.
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
DSS04.04.01 - Testing Define objectives for exercising Define the objectives for exercising and testing the DRP plan to verify completeness of the BCP in
Objectives and testing the business, meeting business risk. See the plan in DSS04.04.04.
technical, logistical,
administrative, procedural and
operational systems of the plan
to verify completeness of the
BCP in meeting business risk.
DSS04.04.02 - Realistic Define and agree on with Define and agree on with stakeholders exercises that are realistic, validate continuity procedures,
Exercises stakeholders exercises that are and include roles, responsibilities, and data retention arrangements that cause minimum
realistic, validate continuity disruption to business processes. See the plan in DSS04.04.04.
procedures, and include roles,
responsibilities, and data
retention arrangements that
cause minimum disruption to
business processes.
DSS04.04.03 - Roles and Assign roles and Define roles and responsibilities for performing continuity plan exercises and tests. See that plan
Responsibilities responsibilities for performing at DSS04.04.04.
continuity plan exercises and
tests.
DSS04.04.04 - Schedule and Schedule exercises and test Determine if executive management has approved the funding for an alternate and testing of the
Test activities as defined in the disaster recovery plan. Either observe a test of the plan or develop a scenario and test the plan
11 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
continuity plan. through audit. If testing, develop a scenario and implement it. Scenarios are a critical piece of the
validation exercise for the disaster recovery plan.
No matter the scenario, the
following basic objectives Some of the criteria for selecting a scenario are:
apply:
1. To ensure that the 1. Realistic to engage the minds of the participants
continuity plan, or some part 2. Powerful enough to give the plan a thorough workout
of it, can be executed 3. Solvable so participants can work through a solution
2. To train and familiarize the 4. Broad enough to involve a sufficient number of business and functional units to make the
users and business exercise valuable, and
continuity staff with the plan 5. Specific enough to attain the objectives of the exercise. Unless the objective of the exercise
3. To demonstrate that the is a surprise "fire drill," the scenario should be developed using people from all of the
plan is accurate, thorough, functional groups that may be involved.
and complete
4. To validate the plan's The scenario that is picked can also serve as a tool in evaluating the exercise and the plan.
assumptions Participants can report on how effective the plan was in solving the problem posed by the
5. To show that the plan will scenario.
help the recovery of the
business processed in a
timely manner. A scenario is
a hypothetical situation that
gives the participants a
problem to work on. They
also give an exercise focus
and structure, and
(hopefully) a sense of
12 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
reality. Without some sort of
scenario, without a problem
to work through, the
validation exercise might
otherwise be useless.
DSS04.04.05 - Post Exercise Conduct a post-exercise Conduct a post-exercise debriefing and analysis to consider the achievement. See the plan at
Briefing debriefing and analysis to DSS04.04.04.
consider the achievement.
DSS04.04.06 - Develop recommendations for Develop recommendations for improving the current continuity plan based on the results of the
Improvements improving the current continuity review. See the plan at DSS04.04.04.
plan based on the results of the
review.
13 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
DSS04.05 Management Practice1
Review, maintain and improve the continuity plan. Conduct a management review of the continuity capability at regular intervals to ensure its continued
suitability, adequacy and effectiveness. Manage changes to the plan in accordance with the change control process to ensure that the continuity plan is kept up to
date and continually reflects actual business requirements.
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
DSS04.05.01 - Regular Review the continuity plan and Determine if and how frequently IT reviews the continuity plan and capability against any
Reviews capability on a regular basis assumptions made and current business operational and strategic objectives.
against any assumptions made
and current business
operational and strategic
objectives.
DSS04.05.02 - Revise BIA Consider whether a revised Determine if and how often IT considers whether a revised business impact assessment may be
business impact assessment required.
may be required, depending on
the nature of the change.
DSS04.05.03 - Changes Recommend and communicate Determine how IT manages the changes and communicates them (e.g., policy, plans, procedures,
changes in policy, plans, infrastructure, and roles and responsibilities).
procedures, infrastructure, and
roles and responsibilities for
management approval and
processing via the change
management process.
DSS04.05.04 - Post Change Review the continuity plan on a Determine how often IT reviews the continuity plan to consider the impact of new or major
Review regular basis to consider the changes to the enterprise organization, business processes, outsourcing arrangements,
impact of new or major technologies, infrastructure, operating systems and application systems.
14 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
changes to enterprise
organization, business
processes, outsourcing
arrangements, technologies,
infrastructure, operating
systems and application
systems.
15 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
DSS04.06 Management Practice1
Conduct continuity plan training. Provide all concerned internal and external parties with regular training sessions regarding the procedures and their roles and
responsibilities in case of disruption.
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
DSS04.06.01 - Training Define and maintain training Determine and analyze
requirements and plans for
those performing continuity 1. through interviews with key staff members whether regular training is performed.
planning, impact assessments, 2. whether and confirm that training needs and schedules are assessed and updated regularly.
risk assessments, media 3. schedules and training material to determine operating effectiveness.
communication and incident 4. through interviews with key staff members whether IT continuity awareness programs are
response. Ensure that the being performed on all levels.
training plans consider
frequency of training and
training delivery mechanisms.
DSS04.06.02 - Develop competencies based Determine how IT develops competencies.
Competencies on practical training including
participation in exercises and
tests.
DSS04.06.03 - Monitor Skills Monitor skills and Determine how IT monitors skills.
competencies based on the
exercise and test results.
16 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
DSS04.07 Management Practice1
Manage backup arrangements. Maintain availability of business-critical information.
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
DSS04.07.01 - Backup Backup systems, applications, Determine the backup schedule and strategy considering:
Strategy data and documentation
according to a defined • Frequency (monthly, weekly, daily, etc.)
schedule. • Mode of back up (e.g., disk mirroring for real-time backups, DVD ROM for long term
retention)
• Type of backup (e.g., full vs incremental)
• Type of media
• Automated online backups
• Data types (e.g., voice, optical)
• Creation of logs
• Critical end-user computing data (e.g., spreadsheets)
• Physical and logical allocation of data sources
• Security and access rights
• Encryption
DSS04.07.02 - Third-Party Ensure that systems, For third party systems hosting, determine the backup schedule and strategy.
Backup applications, data and
documentation maintained or
processed by third parties are
adequately backed up or
otherwise secured. Consider
requiring return of backups
from third parties. Consider
17 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
escrow or deposit
arrangements.
DSS04.07.03 - Off-Site Define requirements for on-site Determine the off-site storage facility and strategy.
Storage and off-site storage of backup
data that meet the business
requirements. Consider the
accessibility required to back
up data.
DSS04.07.04 - BCP Training Roll out BCP awareness and Determine how IT has rolled out BCP awareness and training.
training.
DSS04.07.05 - Backup Periodically test and refresh Determine if and how often IT tests and refreshes archived and backup data.
Testing archived and backup data.
18 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
DSS04.08 Management Practice1
Conduct post-resumption review. Assess the adequacy of the BCP following the successful resumption of business processes and services after a disruption.
Activity Title1 Activity Assessment Activity Assessment Step(s)2
Objectives1
DSS04.08.01 - BCP Assess adherence to the Review the results of the test of the disaster recovery plan. Determine if corrective action has
Assessment documented BCP. been taken on any problems incurred during the test
DSS04.08.02 - Effectiveness Determine the effectiveness of Determine if and how IT has determined the effectiveness of the plan, continuity capabilities, roles
of Plan the plan, continuity capabilities, and responsibilities, skills and competencies, resilience to the incident, technical infrastructure,
roles and responsibilities, skills and organizational structures and relationships
and competencies, resilience to
the incident, technical
infrastructure, and
organizational structures and
relationships.
DSS04.08.03 - Weaknesses Identify weaknesses or Review any weaknesses determined and tracked.
omissions in the plan and
capabilities and make
recommendations for
improvement.
DSS04.08.04 - Management Obtain management approval Understand how and if IT gains approval for changes.
Approval for any changes to the plan and
apply via the enterprise change
control process.
19 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
DSS04 Assessment Summary1
Management Practice Practice Description Practice Assessment Summary
Define the business continuity Define business continuity policy and scope
policy, objectives and scope. aligned with enterprise and stakeholder
objectives.
Maintain a continuity strategy. Evaluate business continuity management
options and choose a cost-effective and
viable continuity strategy that will ensure
enterprise recovery and continuity in the face
of a disaster or other major incident or
disruption.
Develop and implement a Develop a business continuity plan (BCP)
business continuity response. based on the strategy that documents the
procedures and information in readiness for
use in an incident to enable the enterprise to
continue its critical activities.
Exercise, test, and review the Test the continuity arrangements on a regular
BCP. basis to exercise the recovery plans against
predetermined outcomes and to allow
innovative solutions to be developed and help
to verify over time that the plan will work as
anticipated.
Review, maintain and improve the Conduct a management review of the
continuity plan. continuity capability at regular intervals to
ensure its continued suitability, adequacy and
effectiveness. Manage changes to the plan in
20 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
Management Practice Practice Description Practice Assessment Summary
accordance with the change control process
to ensure that the continuity plan is kept up to
date and continually reflects actual business
requirements.
Conduct continuity plan training. Provide all concerned internal and external
parties with regular training sessions
regarding the procedures and their roles and
responsibilities in case of disruption.
Manage backup arrangements. Maintain availability of business-critical
information.
Conduct post-resumption review. Assess the adequacy of the BCP following
the successful resumption of business
processes and services after a disruption.
21 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
DSS04 Risk Summary1
Create multiple risk scenarios for each risk identified in the summary above that affects achieving the objective.
Risk Scenario - Describe the risk/opportunity scenario, including a discussion of the negative and positive impact of the scenario. The description clarifies the threat/
vulnerability type and includes the actors, events, assets and time issues.
Risk Scenario Component Mark all that apply
Threat Type (Describe the nature of the event) ⃣ Malicious
⃣ Accidental
⃣ Error
⃣ Failure
⃣ Natural
⃣ External requirement
Actor (Who or what could trigger the threat that exploits a vulnerability) ⃣ Internal
⃣ External
⃣ Human
⃣ Non-Human
Event (Something that happens that was not supposed to happen, something does not happen ⃣ Disclosure
that was supposed to happen, or a change in circumstances. Events always have causes and ⃣ Interruption
usually have consequences. A consequence is the outcome of an event and has an impact on ⃣ Modification
objectives.) ⃣ Theft
⃣ Destruction
⃣ Ineffective design
⃣ Ineffective execution
⃣ Rules and regulations
⃣ Inappropriate use
22 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
COBIT® 5 Process Assessment Worksheet
Area: Management Domain: Deliver, Service and Support
Process: DSS04 – Manage Continuity
Risk Scenario Component Mark all that apply
Asset (An asset is something of tangible or intangible value that is worth and skills protecting, ⃣ Process
including people, systems, infrastructure, finances and reputation.) ⃣ People and Skills
⃣ Organizational Structure
⃣ Physical Infrastructure
⃣ IT Infrastructure
⃣ Information
⃣ Applications
Resource (A resource is anything that helps to achieve a goal.) ⃣ Process
⃣ People and Skills
⃣ Organizational Structure
⃣ Physical Infrastructure
⃣ IT Infrastructure
⃣ Information
⃣ Applications
Time Timing ⃣ Critical ⃣ Non-Critical
Duration ⃣ Short ⃣ Moderate ⃣ Extended
Detection ⃣ Slow ⃣ Moderate ⃣ Instant
Time lag ⃣ Immediate ⃣ Delayed
Velocity ⃣ Slowing ⃣ Constant ⃣ Increasing
Likelihood ⃣ Highly ⃣ Moderate ⃣ Unlikely
Impact ⃣ Great ⃣ Moderate ⃣ Little
Possible Risk Response Risk Avoidance:
Risk Acceptance:
Risk Sharing/Transfer:
Risk Mitigation:
23 1 - © 2012 ISACA. All rights reserved. COBIT® 5 is a registered trademark of the Information Systems Audit and Control Association (ISACA)
2 - © 2015 Wescott and Associates. All rights reserved.
Potrebbero piacerti anche
- Project Report of DISA 2.0 CourseDocumento32 pagineProject Report of DISA 2.0 Courset pandya0% (1)
- COBIT 5 AssessorDocumento2 pagineCOBIT 5 AssessoramitshdevNessuna valutazione finora
- Getting Started With Geit - RESDocumento52 pagineGetting Started With Geit - RESnicolepetrescu100% (2)
- Student Guide: COBIT® 2019 Design & ImplementationDocumento10 pagineStudent Guide: COBIT® 2019 Design & Implementationsamir sahliNessuna valutazione finora
- Auditing Business Continuity PlanDocumento2 pagineAuditing Business Continuity PlanRAJESH UPADHYAYNessuna valutazione finora
- APO10 Manage SuppliersDocumento17 pagineAPO10 Manage Suppliersnyamsuren.mncertNessuna valutazione finora
- IT Governance Standard FinalDocumento95 pagineIT Governance Standard Finalinyasi100% (1)
- Isaca: Cobit Assessment Programme (PAM) Tool Kit: Using COBIT 5Documento2 pagineIsaca: Cobit Assessment Programme (PAM) Tool Kit: Using COBIT 5lgaleanoc0% (1)
- ISO IEC 27001 Lead Implementer A Complete Guide - 2020 EditionDa EverandISO IEC 27001 Lead Implementer A Complete Guide - 2020 EditionNessuna valutazione finora
- ISO 27001-2022 Transition BookDocumento20 pagineISO 27001-2022 Transition BookzghibNessuna valutazione finora
- Lab 7Documento2 pagineLab 7Dao Manh Cong (K16HL)Nessuna valutazione finora
- Cobit Case Study - OracleDocumento11 pagineCobit Case Study - OracleAdil AbdelganiNessuna valutazione finora
- Modul-4 Enabling Processes COBIT 5Documento23 pagineModul-4 Enabling Processes COBIT 5Rangga AliNessuna valutazione finora
- COBIT 2019 Major Differences With COBIT 5 - v1.1Documento12 pagineCOBIT 2019 Major Differences With COBIT 5 - v1.1efrans christianNessuna valutazione finora
- COBIT 5 Foundation Exam Revision On A PageDocumento1 paginaCOBIT 5 Foundation Exam Revision On A PageSergiö Montoya100% (1)
- 15 COBIT5-FAQsDocumento4 pagine15 COBIT5-FAQsOzgur ErdoganNessuna valutazione finora
- COBIT 5 For Risk Laminate Res Eng 0913Documento8 pagineCOBIT 5 For Risk Laminate Res Eng 0913dandisdandisNessuna valutazione finora
- COBIT 2019 Exam PreparationDocumento61 pagineCOBIT 2019 Exam PreparationGyas Ahmad100% (1)
- COBIT 2019 Design Toolkit With Description - Group X.XLSX - DF6Documento8 pagineCOBIT 2019 Design Toolkit With Description - Group X.XLSX - DF6Aulia NisaNessuna valutazione finora
- Iso 27004 - 2016Documento11 pagineIso 27004 - 2016RNessuna valutazione finora
- COBIT 2019 Governance Management Objectives Practices Activities Nov2018Documento14 pagineCOBIT 2019 Governance Management Objectives Practices Activities Nov2018Nuñez Velez MelisaNessuna valutazione finora
- Effective Capability and Maturity Assessment Using COBIT 2019Documento7 pagineEffective Capability and Maturity Assessment Using COBIT 2019Mavis GayeNessuna valutazione finora
- COBIT 5-Self-Assessment Templates - BAI - 25 August 2015Documento97 pagineCOBIT 5-Self-Assessment Templates - BAI - 25 August 2015sannyNessuna valutazione finora
- Management Awareness Diagnostic 1-Controlling IT: COBIT 2019 Dominios y ObjetivossDocumento4 pagineManagement Awareness Diagnostic 1-Controlling IT: COBIT 2019 Dominios y Objetivossroger chavarriaNessuna valutazione finora
- COBIT Focus ISO 38500 Why Another Standard PDFDocumento3 pagineCOBIT Focus ISO 38500 Why Another Standard PDFMuhammad Yordanis Saifullah Ma'shumNessuna valutazione finora
- IT Application Controls ChecklistDocumento13 pagineIT Application Controls ChecklistGreen TayengwaNessuna valutazione finora
- COBIT 2019 Foundation ExamDocumento28 pagineCOBIT 2019 Foundation ExamVitor Suzarte100% (1)
- Enterprise GoalsDocumento5 pagineEnterprise GoalsMario ValladaresNessuna valutazione finora
- ISO-TS-22318-2021 InglesDocumento11 pagineISO-TS-22318-2021 InglesCarlos Ramos100% (1)
- Supply-Chain-Resilience-and-Continuity WHPBSC WHP Eng 0620Documento21 pagineSupply-Chain-Resilience-and-Continuity WHPBSC WHP Eng 0620yudha ekamarthaNessuna valutazione finora
- COBIT-5-Assurance Res Eng 1213Documento17 pagineCOBIT-5-Assurance Res Eng 1213sheryhanNessuna valutazione finora
- ACS-2821-001 Lecture Note 6 PDFDocumento32 pagineACS-2821-001 Lecture Note 6 PDFJohn MwaipopoNessuna valutazione finora
- GENERAL - COBIT - 2019 - FAQ - v1.1 110718Documento4 pagineGENERAL - COBIT - 2019 - FAQ - v1.1 110718Hani AlsebakhiNessuna valutazione finora
- TEMPLATE COBIT 2019 Assessment Gap Improvement - Group 4Documento10 pagineTEMPLATE COBIT 2019 Assessment Gap Improvement - Group 4Ferdiansyah KurniawanNessuna valutazione finora
- Cobit 5 Process Assessment Worksheet Area: Governance Domain: Evaluate, Direct and MonitorDocumento9 pagineCobit 5 Process Assessment Worksheet Area: Governance Domain: Evaluate, Direct and MonitornoneNessuna valutazione finora
- Cobit 2019 Design-Implementation Course Syllabus - New Look 2019 EN V1.0Documento13 pagineCobit 2019 Design-Implementation Course Syllabus - New Look 2019 EN V1.0Dipayan Chakraborty100% (1)
- COBIT 4 To 5 MappingDocumento19 pagineCOBIT 4 To 5 MappingWikeUlfianiAresa100% (1)
- A Business Continuity Management Maturity ModelDocumento118 pagineA Business Continuity Management Maturity ModelNelson RussoNessuna valutazione finora
- 005 Iso Iec 20000 WhitepaperDocumento10 pagine005 Iso Iec 20000 WhitepaperAntonio SeguraNessuna valutazione finora
- Audit Program IT Business Continuity Disaster RecoveryDocumento7 pagineAudit Program IT Business Continuity Disaster RecoveryGelo VidalNessuna valutazione finora
- Chapter 1-The Process of Auditing Information SystemsDocumento50 pagineChapter 1-The Process of Auditing Information SystemsSritrusta SukaridhotoNessuna valutazione finora
- DR PlanningDocumento21 pagineDR PlanningAlex DcostaNessuna valutazione finora
- Business Continuity Risk ManagementDocumento38 pagineBusiness Continuity Risk ManagementThilakPATHIRAGENessuna valutazione finora
- The HP Openview Approach To Help Desk and Problem ManagementDocumento21 pagineThe HP Openview Approach To Help Desk and Problem Managementsalman_ansari_pk4198Nessuna valutazione finora
- Cobit Audit Questionnaire: P01 Define A Strategic IT Plan: Confidential When Filled inDocumento5 pagineCobit Audit Questionnaire: P01 Define A Strategic IT Plan: Confidential When Filled inNielz TulalessyNessuna valutazione finora
- Tiered-SAM-Review Res Eng 1110Documento95 pagineTiered-SAM-Review Res Eng 1110sathish kumar100% (1)
- Itscore For Business Continu 2053103Documento16 pagineItscore For Business Continu 2053103Marcos FreitasNessuna valutazione finora
- ISMS Technical Proposal - KaisenProsDocumento35 pagineISMS Technical Proposal - KaisenProsAhmad NawazNessuna valutazione finora
- Analysing IT Governance Maturity Level Using COBIT 2019 Framework A Case Study of Small Size Higher Education Institute XYZ-eduDocumento6 pagineAnalysing IT Governance Maturity Level Using COBIT 2019 Framework A Case Study of Small Size Higher Education Institute XYZ-eduzoom 1234Nessuna valutazione finora
- Information Technology-Governance of IT For The OrganizationDocumento7 pagineInformation Technology-Governance of IT For The OrganizationggcvbcNessuna valutazione finora
- JIS IT Governance PolicyDocumento6 pagineJIS IT Governance PolicyrudynelNessuna valutazione finora
- Cobit 2019 - IsO20K MappingDocumento1 paginaCobit 2019 - IsO20K MappingAnish KumarNessuna valutazione finora
- CSCF Assessment Template For Mandatory Controls (Version2022) v1.2Documento179 pagineCSCF Assessment Template For Mandatory Controls (Version2022) v1.2PetrrNessuna valutazione finora
- COBIT 2019 Design Guide PDFDocumento151 pagineCOBIT 2019 Design Guide PDFRushab khopade100% (1)
- COBIT 2019 Design Toolkit TKT Eng 1218 (AutoRecovered)Documento56 pagineCOBIT 2019 Design Toolkit TKT Eng 1218 (AutoRecovered)ahnisNessuna valutazione finora
- University of Georgia Long-Term IT Master PlanDocumento24 pagineUniversity of Georgia Long-Term IT Master PlanaccidentalcioNessuna valutazione finora
- GTAG 21 Auditing ApplicationsDocumento36 pagineGTAG 21 Auditing ApplicationsFarid AbdelkaderNessuna valutazione finora
- QAF GuideDocumento12 pagineQAF GuideShubham GoyalNessuna valutazione finora
- Business Impact Analysis FormDocumento12 pagineBusiness Impact Analysis FormSapaNessuna valutazione finora
- Digital Risk Management A Complete Guide - 2019 EditionDa EverandDigital Risk Management A Complete Guide - 2019 EditionNessuna valutazione finora
- BMIS 414 Information Technology ManagementDocumento7 pagineBMIS 414 Information Technology ManagementNate NyamasvisvaNessuna valutazione finora
- ITIL v3 PresentationDocumento211 pagineITIL v3 Presentationkommareddy164835100% (1)
- Moving Office ChecklistDocumento9 pagineMoving Office ChecklistSoegiyat RamelanNessuna valutazione finora
- Iso 31000 - 2018Documento10 pagineIso 31000 - 2018vdimeskaNessuna valutazione finora
- Business Impact Analysis BIA Information Security - (13p)Documento13 pagineBusiness Impact Analysis BIA Information Security - (13p)Rodrigo BenaventeNessuna valutazione finora
- R-Business Continuity Plan Examining of Multi-Usable FrameworkDocumento8 pagineR-Business Continuity Plan Examining of Multi-Usable FrameworkJosé Manuel Sánchez Murga100% (1)
- Policy On Disclosure of Material Events - InformationDocumento7 paginePolicy On Disclosure of Material Events - InformationArun KCNessuna valutazione finora
- Audit of Business Continuity Planning PDFDocumento22 pagineAudit of Business Continuity Planning PDFNishimaNessuna valutazione finora
- Business Continuity Advice 10 Minute Assessment Questionnaire PDFDocumento6 pagineBusiness Continuity Advice 10 Minute Assessment Questionnaire PDFroalan1Nessuna valutazione finora
- CCMv4 0AuditingGuidelinesDocumento79 pagineCCMv4 0AuditingGuidelinesMousumi Utkarsh RayNessuna valutazione finora
- Domain 1 - Security and Risk ManagementDocumento43 pagineDomain 1 - Security and Risk ManagementAnas InamNessuna valutazione finora
- ITIL NotesDocumento7 pagineITIL NotesTreb CabreraNessuna valutazione finora
- Red Team: Improving Organizational ResilienceDocumento13 pagineRed Team: Improving Organizational ResilienceSky WalkerNessuna valutazione finora
- A Business Continuity Management Maturity ModelDocumento13 pagineA Business Continuity Management Maturity ModelNelson Russo100% (1)
- Computer Forensics PresentationDocumento231 pagineComputer Forensics PresentationJozoNessuna valutazione finora
- Cism Certified Information Security Manager All in One Exam Guide 2Nd Edition Peter H Gregory Full ChapterDocumento67 pagineCism Certified Information Security Manager All in One Exam Guide 2Nd Edition Peter H Gregory Full Chapterchristopher.wakley213100% (7)
- CAIQ v3.0.1-09-16-2019Documento728 pagineCAIQ v3.0.1-09-16-2019casa nanosNessuna valutazione finora
- HB 293-2006 Executive Guide To Business Continuity ManagementDocumento7 pagineHB 293-2006 Executive Guide To Business Continuity ManagementSAI Global - APACNessuna valutazione finora
- Accelerating Digital Transformation: Key Risk Oversight Issues For Bank BoardsDocumento12 pagineAccelerating Digital Transformation: Key Risk Oversight Issues For Bank BoardsakashNessuna valutazione finora
- ENISA IT Business Continuity ManagementDocumento127 pagineENISA IT Business Continuity ManagementCristian ȘtefanNessuna valutazione finora
- If You Fail To Plan, Then You Should Plan To Fail: This Course Is Suited ForDocumento1 paginaIf You Fail To Plan, Then You Should Plan To Fail: This Course Is Suited ForKausalyah NookaiahNessuna valutazione finora
- Tieman 2017Documento21 pagineTieman 2017Belajar Jangan rebahan ajaNessuna valutazione finora
- Terms of Reference Ferry ProjectDocumento41 pagineTerms of Reference Ferry Projectsaket-mehta100% (1)
- BPO Whitepaper Six Risk Management Best Practices Third Party Providers Global in House Centers 0413 1Documento10 pagineBPO Whitepaper Six Risk Management Best Practices Third Party Providers Global in House Centers 0413 1SanjeevNessuna valutazione finora
- Case StudyDocumento2 pagineCase StudyDivya Khandelwal50% (2)
- 14 - Guideline of Business Continuity Management in Digital GDocumento44 pagine14 - Guideline of Business Continuity Management in Digital GZee NapNessuna valutazione finora
- (Ioannis S. Akkizidis, Vivianne Bouchereau) Guide PDFDocumento436 pagine(Ioannis S. Akkizidis, Vivianne Bouchereau) Guide PDFARMANDO MESTASNessuna valutazione finora