Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Go To and Click Sing Up To Register
Caricato da
Kamran MahmoodDescrizione originale:
Titolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Go To and Click Sing Up To Register
Caricato da
Kamran MahmoodCopyright:
Formati disponibili
Come & Join Us at VUSTUDENTS.
net
For Assignment Solution, GDB, Online Quizzes, Helping Study material,
Past Solved Papers, Solved MCQs, Current Papers, E-Books & more.
Go to http://www.vustudents.net and click Sing up to register.
VUSTUENTS.NET is a community formed to overcome the disadvantages of distant
learning and virtual environment, where pupils don’t have any formal contact with their
mentors, This community provides its members with the solution to current as well as the
past Assignments, Quizzes, GDBs, and Papers. This community also facilitates its
members in resolving the issues regarding subject and university matters, by providing
text e-books, notes, and helpful conversations in chat room as well as study groups. Only
members are privileged with the right to access all the material, so if you are not a
member yet, kindly SIGN UP to get access to the resources of VUSTUDENTS.NET
» » Regards » »
VUSTUDENTS.NET TEAM.
Virtual University of Pakistan
Come and Join Us at www.vustudents.ning.com
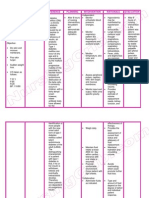
Cs507 Midterm Subjective
BY ADNAN AWAN
Adnanawan6@gmail.com
Question (2 marks)
Define centralized processing
Answer
Centralized Processing is performed in one computer or in a cluster of coupled computers
in a single location. Centralized processing was the architecture that evolved from the
very first computers
Question (Marks: 3) How can we make our password secure?
Answer
1: Keep secret
2: Don’t write anywhere
3: Always use the password with combination of letters, numbers, upper and lower cases
4: change password regular basis
Question (Mark 3)
How risks can be measured (3 marks)
Answer
There are two keys to good risk assessment. The first is better quality and more timely
information about the risks as they evolve, so that the element of surprise is reduced.
The second is tools such as risk-adjusted discount rates, simulations, scenario analysis,
and VAR to convert the raw data into risk measures.
Question Mark 3
List any three benefits of CRM.3
Answer
Following are the three benefits of CRM.
1. To achieve CRM, a company wide set of tools, technologies, and procedures promote the
Relationship with the customer to increase sales.
2. Its objectives are to increase profitability, revenue, and customer satisfaction.
3. Encourages customer loyalty
Question (marks 5)
Risk based audit approach
Answer
Risk Based Audit Approach
This approach to audit proceeds with following steps
1. Understanding the business process
2. Understanding the control structure built in the system
3. Understanding of inherent risks (risks which are covered through instituting)
controls, which can occur in the absence of controls e.g. Political legal factors affecting the business,
Nature of industry the organization exists
Come and Join Us at www.vustudents.ning.com
4. Risk assessment
5. Categorization of risks identified
Question (Marks: 2)
What are Active monitors? Define.
Answer:
This software serves the concurrent monitoring as the system is being used. They act as a guard against
viruses while the operating system is performing various functions e.g connected to internet, transferring
data, etc.
Question (Marks: 3)
Discuss characteristics of Flat organization.
Answer
Following are the characteristics of a flat organization.
• High number of subordinates per supervisor
• Short of chain of command
• Less number of levels
• Eliminates middle level managers
• Decentralizes authority to low level managers
Question Marks 3
What are the types of Supply Chain Management? (
Answer
Types of Supply Chains
Supply chain may exist in various forms depending on the need of the business:
1. Made to Store
Focuses on tracking customer demand in real time, so that the
production process can restock the finished goods inventory.
2. Continuous Replenishment
Focuses on constant replacement of inventory by
working closely with suppliers. Applicable to environments with stable demand patterns
3 Built to order
Focuses on careful management of component inventories and
delivery of needed supplies along the supply chain. A solution to this potential inventory
problem is to utilize many common components across several production lines and in
several locations
Question (Marks: 5)
Discuss the attributes on which Organizational Information Requirements depends
Answer
Organization & Information Requirements
Organizations have various attributes which distinguish them from each other. No two organizations are
similar in all respects. There have to have certain distinctive lines keeping them unique from each other.
Information requirements keep varying in accordance with
• Size of organization
• Its structure
• The Culture it follows
• Decision Making Structures
• Interested parties both internal and external
An organization should consider the above mentioned requirements while devising a system which tailors for
specific information needs.
Come and Join Us at www.vustudents.ning.com
Question (Marks 2)
Define objective?
Answer
Objectives
We just mentioned that a control mechanism should compare actual output with
expected/Ideal output. But before this is being done, there needs to be a list of specific
objectives which define expected output.
Question ( Marks: 3 )
What is access control? Give example
Answer
Access Controls
These controls establish the interface between the would-be user of the computer system and the computer
itself. These controls monitor the initial handshaking procedure of the user with the operating system. For
example when a customer enter the card and the pin code in an automatic teller machine (ATM), the access
controls are exercised by the system to block unwanted or illegitimate access.
Question ( Marks: 3 )
What are hackers?
Answer
Hackers
A hacker is a person who attempts to invade the privacy of the system. In fact he attempts
to gain unauthorized entry to a computer system by circumventing the system’s access
controls. Hackers are normally skilled programmers, and have been known to crack
system passwords, with quite an ease. Initially hackers used to aim at simply copying the
desired information from the system. But now the trend has been to corrupt the desired
information.
Question ( Marks: 5 )
Briefly describe the process of risk mitigation?
Answer
• Risk assumption: To accept the potential risk and continue operating the IT system or
to implement controls to lower the risk to an acceptable level.
• Risk Avoidance: To avoid the risk by eliminating the risk cause and e.g. forgo certain
functions of the system or shut down the system when risks are identified.
• Risk Limitation: To limit the risk by implementing controls that minimize the adverse
impact of a threat’s exercising vulnerability e.g. use of supporting preventive and
detective controls.
• Risk Planning: To manage risk by developing risk mitigation plant that predicts
implements and maintains controls.
• Research and acknowledgement: To lower the risk of loss by acknowledging
vulnerability or flaw and researching controls to correct the vulnerability.
• Risk Transference: To transfer the risk by using other options to compensate loss such
as purchasing insurance.
Question (Marks: 2)
What is information Quality Checklist?
Answer
Come and Join Us at www.vustudents.ning.com
The information can also be ranked in accordance with the qualities it has in it. The experts have devised
certain criteria to evaluate the quality of information. Those some points which are used to evaluate the
quality are known as quality checks
Question (Marks: 3)
Differentiate CRM from ERP?
Answer
ERP & CRM
Customer has become of critical importance in the modern day business. Early on, organizations used to
focus more on how much has been sold what has been produced. But now the focus is quite different.
Focus has been placed on the requirements of the customer, providing quality service and quickness of
response to customer queries. Analysis of the customer data from their personal habits to spending one’s
have become a crucial element of doing a successful business. ERP has this unique potential to improve the
quality of customer handling.
Question ( Marks: 3 )
What do u know about Key stroke Monitoring?
Answer
A record of every keystroke---- often called keystroke monitoring. Keystroke
monitoring is the process used to view or record both the keystrokes entered by a
computer user and the computer's response during an interactive session. Keystroke
monitoring is usually considered a special case of audit trails.
Question (Marks: 5)
List any five reasons that attract organizations to ERP?
Answer
1. Planning the operations
2. Integrated customer related information – order tracking with customer database, inventory and shipment
at different locations.
3. Standardized HR information – A company with multiple business units will require a
comprehensive and all-encompassing method of locating employees and communicating with them.
4. Integrated financial information and analysis.
5. Monitoring the operations including those of sub-vendors and manufacturers
Question (Marks: 2)
What are the physical threats for Information System?
Answer
Physical threats
The risks of physical damage render the computer hardware becomes useless due to the damage caused to it
by natural disasters (Fire, earth quake, flood), pollution-Dust, energy Variations. Reasonable measures
should be taken to avoid undesirable consequences.
Question (Marks 3)
What are the components of BCP?
Answer
Components of BCP
The business continuity plan includes:
1. The disaster recovery plan that is used to recover a facility rendered inoperable,
Come and Join Us at www.vustudents.ning.com
including relocating operation into a new location.
2. The operations plan that is to be followed by the business units while recovery is
taking place.
3. The restoration plan that is used to return operations to normality whether in a restored
or new facility.
Question ( Marks: 3 )
How the information is kept in the purchase system?
Answer
A simple example can be given of a purchase and sales system. In a typical purchase system information
related to purchase of materials is kept, for instance,
1. Orders for the purchase of various materials
2. Status of deliveries received against specific orders
3. Changes in the order quantity, time, day or other information
4. Quality inspection reports and whether they need to be communicated to the supplier
5. Updated status report of stock
6. Issues made out of the stock
Question (Marks: 5)
Incorporate Risk management SDLC? Identify its phases?
Answer
For each phase of SDLC, the process of risk management is no different. Rather it is iterative process
which can be performed at each major phase. Every step of development has its own risks which need to be
handled and addressed separately. Hence managing risk in SDLC means managing risk of each phase of
life cycle.
Phases of Risk Management
Following are various phases of SDLC
• System Characterization
• Threat Identification
• Vulnerability Identification
• Control Analysis
• Likelihood Determination
• Impact Analysis
• Risk Identification
• Control Recommendation
• Results Documentation
• Implementation
• Monitoring
Question Mark 2
What is web security threat?
Answer
Web Security Threats
There are two major classes of security threats
• Passive Attacks
• Active Attacks
Question Mark 3
What is antivirus software?
Come and Join Us at www.vustudents.ning.com
Answer
Use of antivirus software is another very important technical control against the spread of
Virus.
1) Scanners
2) Active monitors
3) Behavior blockers
4) Logical intrusion
Question Mark 5
Classify E-Commerce into different classes.
Answer
The most prevalent of E-Commerce models can be classified as under:
1. Business to Consumer (B2C)
2. Business to Business (B2B),
3. Business to Employee (B2E),
4. Consumer to Consumer (C2C) and
5. E-Government
6. Government to Citizens/Customers (G2C)
7. Government to Business (G2B)
8. Government to Government (G2G
Question ( Marks: 2 )
How threats are identified?
Answer
Threats can be identified on the basis of nature of Threat which can either be accidental-natural
occurrences/force major, or deliberate-intentional act of harm or on the basis of sources of threat which can
either be internal-threat caused within the organization, or external-threat from some one outside the
organization.
Question (Marks: 3)
What are the challenges to organizations for launching Ecommerce? Identify any three.
Answer
Security is the biggest challenge to for launching Ecommerce There is a consensus that the issue of
computer and data security is the biggest hurdle in the growth of ecommerce. Web servers also face this
security threat. Some other problems with launching e-commerce business is lack of trust of customers,
culture and languages problems.
Lengthy procedure of payment and receipt of products or services.
Question (Marks: 3)
Differentiate between Manual and Computer based Information system
Answer
Manual Vs Computerized Information Systems
As advancement was made in every field of life, manual information systems were converted to
computerized systems. In manual environment, the concept of transformation was difficult to apply, since
input of data into records was by itself the output which also included simple computations. Concept of
control mechanism grew stronger as computerized information systems emerged. Now the concept of
Information system exists with the usage and benefits of Computers as an inevitable part.
Question ( marks 5)
Discuss why firewall is the primary method keeping a computer can be secure
from intruders.
Come and Join Us at www.vustudents.ning.com
Answer
Firewall
Firewall is the primary method for keeping a computer secure from intruders. A firewall
allows or blocks traffic into and out of a private network or the user's computer. Firewalls
are widely used to give users secure access to the Internet as well as to separate a
company's public Web server from its internal network. Firewalls are also used to keep
internal network segments secure; for example, the accounting network might be
vulnerable to snooping from within the enterprise. In the home, a personal firewall
typically comes with or is installed in the user's computer. Personal firewalls may also
detect outbound traffic to guard against spy ware, which could be sending your surfing
habits to a Web site. They alert you when software makes an outbound request for the
first time. In the organization, a firewall can be a stand-alone machine or software in a
server. It can be as simple as a single server or it may comprise a combination of servers
each performing some type of firewall processing.
Question ( Marks: 2 )
List down the inputs to Risk Determination phase ?
Answer
Likelihood of threat exploitation, Magnitude of impact Adequacy of planned and current controls
Question (2 marks)
Define centralized processing
Answer
Centralized Processing is performed in one computer or in a cluster of coupled computers
in a single location. Centralized processing was the architecture that evolved from the
very first computers
Question ( Marks: 3 )
What should be the most important information required for large organization
in your opinion?
Answer
Information Requirements of Large Organizations
With such a large structure, it is inevitable that the detailed planning should be made for
proper management control, for both short term and long term.
Performance measurement against plans / targets
Question ( Marks: 3 )
What do you understand by ERD? Define briefly
Answer
Entity Relationship Diagram (ERD)
Another diagrammatical tool used in system design is ERD. ERD as shown below indicates simple
relationships. These relationships can be read as follows.
One department has one supervisor A department may have more than one employee
Or
An employee may be in more than one department
An employee may not be working on any project but a project must have at least one employee working on
it.
Question (Marks: 3)
Types of threats
Come and Join Us at www.vustudents.ning.com
Answer
Threats can be divided in to two broad categories
1. Physical threat
This refers to the damage caused to the physical infrastructure of the information
systems.
Examples are natural disasters (Fire, earth quake, flood), pollution, energy variations and
physical Intrusion.
2. Logical
This refers to damage caused to the software and data without physical presence.
Examples are viruses and worms, logical intrusion commonly referred to as hacking
Question ( Marks: 2 )
Identify leading ERP software vendors ?
Answer:
1-SAP
2-Oracale
3-QAD
4-PeopleSoft
5-Sag
Question ( Marks: 3 )
What is Data Driven Decision Support System?
Answer
Data driven DSS use large pool of data in major organizational systems. They help to extract information
from large quantities of data stored. These systems rely on Data Warehouses created from Transaction
Processing systems.
They use following techniques for data analysis
• Online analytical processing, and
• Data mining
Question ( Marks: 3 )
Differentiate between Incremental and iterative models with the help of one example each.
Answer
Incremental vs. Iterative
These sound similar, and sometimes are equated but there is a subtle difference:
• Incremental: add to the product at each phase
• Iterative: re-do the product at each phase
Example:
Building a House
• Incremental: Starts with a modest house, keep adding rooms and upgrades to it.
• Iterative: The design/construction map.
Question ( Marks: 5 )
Define the following: EC (E commerce) , B (E business)
Answer
EC (E commerce)
Electronic Commerce (e-commerce or EC) describes the buying, selling, and exchanging of products,
services, and information via computer network, primarily the internet. Some people view the term
commerce as describing transactions conducted between business partners.
EB (E business)
Come and Join Us at www.vustudents.ning.com
E-business means using the internet and online technologies to create operating efficiencies, and therefore
increase value to the customer. It is internally focused. All e-commerce is part of e-business. Not all e-
business is e-commerce.
Question ( Marks: 2 )
Define IDS
Answer
Intrusion Detection Systems (IDS)
Another element to securing networks is an intrusion detection system (IDS). IDS are
used in complement to firewalls. An IDS is works in conjunction with routers and
firewalls by monitoring network usage anomalies. It protects a company’s information
systems resources from external as well as internal misuse.
Question (Marks: 3)
What are hackers?
Answer:
A hacker is a person who attempts to invade the privacy of the system. In fact he attempts to gain
unauthorized entry to a computer system by circumventing the system’s access controls. Hackers are
normally skilled programmers, and have been known to crack system passwords, with quite an ease.
Initially hackers used to aim at simply copying the desired information from the system. But now the trend
has been to corrupt the desired information.
Question ( Marks: 3 )
Define Re-engineering?
Answer
Re engineering is the fundamental rethinking and redesigning of business process to achieve dramatic
improvement in critical, contemporary measures of performance, such as cost, quality, service and speed.
Question ( Marks: 5 )
Attributes of ERP, explain
Answer
Attributes of an ERP software
ERP applications address the complete business process. ERP applications are modular
generally covering all aspects of the business as each aspect is dependant upon the other.
Thus you will generally find certain standard modules as part of ERP software which are
manufacturing, supply chain, financials, CRM, human resources and warehouse
management. It may also be stated that depending upon business size , phased approach
may be opted to implement the ERP. A phased approach becomes necessary because of
business process realignment and implementation issues particulars relating to change in
habits of the users.
During the past, the software laid greater stress on financial transactions and their
cumulative result with information for other department being provided as a secondary
objective. ERP is extended to the enterprise level, encompassing not only the
organization but also the entities external to organization i.e. suppliers and customer.
Question ( Marks: 2 )
Describe Trojans virus
Answer
Come and Join Us at www.vustudents.ning.com
Trojan horse – Users execute the program written by the penetrate. The program
undertakes unauthorized activities e.g. a copy of the sensitive data.
Question (Marks: 3)
Differentiate object from class.
Answer
An object is an instance of some class. All objects are instances of some class. Instance also
carries connotations of the class to which the object belongs. For example, computers are the domain/Class
which can be divided into following sub-classes:
• Laptop computer
• Desktop computer
• Palmtop
Question (Marks: 3)
What are the objective/purposes of the DFDs?
Answer
Answer: The purpose of data flow diagrams is to provide a linking bridge between users and systems
developers. Data flow diagrams facilitate users to understand how the system operates. DFD’s also help
developers to better understand the system which helps in avoiding delays in proper designing,
development, etc. of projects.
Question ( Marks: 5 )
How the likelihood is determined? Enlist the factors.
Answer
Likelihood Determination
• This phase determines that a potential vulnerability could be exercised by a given
threat-source. Following table will help us to define and understand the likelihood
definitions. The input to this phase is
• Threat source motivation
• Threat capacity
• Nature of vulnerability
• Current Controls
The output to this phase is a likelihood rating to be used further in the risk assessment process.
Impact Analysis
This phase determines the adverse impact resulting from a successful threat exercise of
vulnerability. Following information is required before conducting an impact analysis.
1. System mission e.g. the process performed by IT system.
2. System and data criticality e.g. the system’s value or importance to an organization
3. System and data sensitivity
Question ( Marks: 2 )
Define CRM.
Answer
CRM Uses proven methodologies and e-business technologies to help companies to identify, select,
acquire, develop, and retain profitable customers, building the lasting relationships that are key to long-
term financial success.
Question ( Marks: 3 )
What are the change agents, explain their role in change
Answer
Change agents
Come and Join Us at www.vustudents.ning.com
A person or a team who leads a change project or business-wide initiative by defining,
researching, planning, building business support and carefully selecting volunteers to be
part of a change team.
Change Agent is comfortable with leading change initiatives with uncertain outcomes
and systematically considers new and better ways of doing things.
Question ( Marks: 5 )
Differentiate the following (Intrusion Detection vs. Variance Detection
Answer
Intrusion detection
Intrusion detection refers to the process of identifying attempts to penetrate a system and gain
unauthorized access. If audit trails have been designed and implemented to record appropriate
information, they can assist in intrusion detection. Intrusion detection system can be made part of
the regular security system to effectively detect intrusion. Real time intrusion detection is technical and
complex to achieve but reasonable extent can be attained. Real-time intrusion detection is primarily aimed
at outsiders attempting to gain unauthorized access to the system.
Variance detection and audit trails
Trends/variance-detection tools look for anomalies in user or system behavior. It is possible to
monitor usage trends and detect major variations. The log can be detected and analyzed to detect
the irregularity. For example, if a user typically logs in at 9 a.m., but appears at 4:30 a.m. one
morning, this may indicate either a security problem or a malfunctioning of the system clock, that may need
to be investigated. The log can be sorted/filtered for all log ins before 9 a.m. from that particular terminal
Question ( Marks: 2 )
What is cryptography?
Answer:
In literal terms, cryptography means science of coded writing. It is a security safeguard to render
information unintelligible if unauthorized individuals intercept the transmission. When the information is to
be used, it can be decoded. “The conversion of data into a secret code for the secure transmission over a
public network is called cryptography.”
Question ( Marks: 3 )
What is logical intrusion?
Answer
The skills needed to exploit logical exposures are more technical and complex as
compared to physical exposures.
Generally a similar term used in relation to logical intrusion is hacking.
In the 1990’s dotcom boom encouraged many organizations to use internet for executing
transactions. Initially internet used was more oriented to providing information to the
general public. With the enhanced focus of the organizations to reduce operational costs,
and increase sales, the use of internet started increasing.
Question ( Marks: 5 )
Describe security audit ?
Answer
Going online exposes an entity to more hazards than otherwise. This requires
implementation of effective controls and checks to secure both the company’s online data
from undesired manipulation, and the customer’s information and orders. The
organization may hire an audit firm to offer these services and check the integrity of the
website. Web audits help in gaining a web rating which enhances the credibility of the
audits. There are different levels of audits, tailored to your needs and your budget.
Come and Join Us at www.vustudents.ning.com
Among the issues we can carefully review on your site, resulting in a detailed report with
recommendations:
• Performance, page load time
• Graphics optimization
• Navigation usability, consistency
• Browser compatibility
• Content formatting consistency
• Accessibility compliance with ADA guidelines and Section 508 Standards
• Broken links
• Page errors, script errors
• search engine ranking
• interface layout
Question ( Marks: 2 )
What are the physical threats to the information systems?
Answer
This refers to the damage caused to the physical infrastructure of the information systems. Examples are
natural disasters (Fire, earth quake, flood), pollution, energy variations and physical Intrusion.
Question ( Marks: 3 )
What is access control? Give example
Answer
These controls establish the interface between the would-be user of the computer system and the computer
itself. These controls monitor the initial handshaking procedure of the user with the operating system. For
example when a customer enters the card and the pin code in an automatic teller machine (ATM), the
access controls are exercised by the system to block unwanted or illegitimate access.
Question ( Marks: 3 )
What is the data driven support system?
Answer
Data driven DSS is use large pool of data in major organizational systems. They help to
extract information from large quantities of data stored. These systems rely on Data
Warehouses created from Transaction Processing systems.
They use following techniques for data analysis
• Online analytical processing, and
• Data mining
Question ( Marks: 5 )
Identify the objective and scope of security.
Answer
The concept of security applies to all information. Security relates to the protection of valuable assets
against loss, disclosure, or damage. Valuable assets are the data or information recorded, processed, stored,
shared, transmitted, or retrieved from an electronic medium. The data or information must be protected
against harm from threats that will lead to its loss, inaccessibility, alteration or wrongful disclosure.
Question (Marks: 2)
Define centralized processing
Answer
Centralized Processing is performed in one computer or in a cluster of coupled computers
in a single location. Centralized processing was the architecture that evolved from the
Come and Join Us at www.vustudents.ning.com
very first computers
Question ( Marks: 3 )
What is difference between the Changing and Freezing?
Answer
Another view of phases
Change management phases can be classified in an alternative way:
• Unfreezing -- Preparing a situation for change by disconfirming existing attitudes and behaviors.
• Changing -- Taking action to modify a situation by altering the targets of change.
• Refreezing -- Maintaining and eventually institutionalizing the change.
Question ( Marks: 3 )
What are Object Oriented Analysis and Design (OOAD)?
Answer
Object Oriented Analysis and Design (OOAD)
The concept of object oriented analysis and design focuses on problems in terms of classes and objects.
This concept combines aspects of both entity relationship diagram and data flow diagrams. The object
oriented analysis and design tool has been devised to support the object oriented languages, for example
C++ and Java. The roots of the concept of object orientation evolved in late 60’s with the emergence of
first language “SIMULA 67” as the first object oriented language. Object oriented methodologies do not
replace traditional approaches (such as data flow, process flow, and state transition diagrams); they are
important new additions to the toolkit.
Question (Marks: 5)
What is focal Point? Complete
Answer
What is focal Point
A corporate-level facilitator may serve as a focal point for assessments throughout the company, including
those pertaining to information security because of familiarity with the tools and the reporting
requirements. Each business unit in an organization may have a designated individual responsible for the
business unit's risk assessment activities. The computer hardware and software company, may also create a
team for the purpose of improving the overall risk assessment process and reviewing results of risk
assessments in the hardware and software systems from the perspective of offering a better, reliable and
risk free product.
Question (Marks: 5)
What are the sources of critical success factor?
Answer
Sources of critical success factor
1. Industry CSFs resulting from specific industry characteristics;
2. CSF’s resulting from the chosen competitive strategy of the business e.g. quick
and timely delivery may be critical to courier service business
3. Environmental CSFs resulting from economic or technological changes; and
4. Temporal CSFs resulting from internal organizational needs and changes
Question ( Marks: 2 )
Define Clear Text ?
Answer
Clear text – it is the data to be encrypted.
Cipher text – it is the code created out of data after encryption
Come and Join Us at www.vustudents.ning.com
Question ( Marks: 3 )
What is the use of Default keyword in switch structure?
Answer
The default statement is used because, when dealing with switch, you will have many cases either returning
TRUE or FALSE.
If neither of those cases return true, then default will recognize the switch value. However, the default line
should be at the end of every case It’s a catch-all for any case that doesn't exist. Think of it as 'else' in a list
of if-else statements, if the switch doesn't match a listed case, the default case is used (if it exists).
Question ( Marks: 5 )
How will you differentiate CSF from KPI? Discuss briefly?
Answer
CSF vs. Key Performance Indicator
A critical success factor is not a key performance indicator or KPI. Critical Success Factors are elements
that are vital for a strategy to be successful. A KPI measures the achievements. The following example will
clarify the difference. A CSF for improved sales may be adopting a new sales strategy through better and
regularly arranged display of products in the shop windows. However, the KPI identified would be the
increased/decreased Average Revenue Per Customer as a result of the strategy. Key Performance Indicators
directly or indirectly measure the results of implementation of Critical Success Factors. KPI’s are measures
that quantify objectives and enable the measurement of strategic performance.
Come and Join Us at www.vustudents.ning.com
Potrebbero piacerti anche
- IS Auditor - Process of Auditing: Information Systems Auditor, #1Da EverandIS Auditor - Process of Auditing: Information Systems Auditor, #1Nessuna valutazione finora
- Security Of Computer Systems A Complete Guide - 2020 EditionDa EverandSecurity Of Computer Systems A Complete Guide - 2020 EditionNessuna valutazione finora
- CS507 Subjective QuestionsDocumento49 pagineCS507 Subjective QuestionsMiralkhan003 Miralkhan003Nessuna valutazione finora
- Final Assessment: Spring 2021Documento8 pagineFinal Assessment: Spring 2021Tanzia Afrin SaraNessuna valutazione finora
- Cs 507 Subjective Solved 2011 IDocumento23 pagineCs 507 Subjective Solved 2011 IMubashar HussainNessuna valutazione finora
- Cs507 Final Term Subjective by Adnan AwanDocumento15 pagineCs507 Final Term Subjective by Adnan Awanzahidwahla1Nessuna valutazione finora
- CS507 Final 2010 Subjective Solved: Answer: Information Requirements of Service SectorDocumento9 pagineCS507 Final 2010 Subjective Solved: Answer: Information Requirements of Service SectorSaad RazaNessuna valutazione finora
- BSBINM501Documento12 pagineBSBINM501ajayNessuna valutazione finora
- OpaudCh03-502E-Regunayan, M PDocumento5 pagineOpaudCh03-502E-Regunayan, M PMarco RegunayanNessuna valutazione finora
- Dss and Tps Case Assignment - Mansi VishnoiDocumento5 pagineDss and Tps Case Assignment - Mansi VishnoiIsmail shaikhNessuna valutazione finora
- CS507 - Final - Term - Solved - MCQs - Mega - File 232323 PDFDocumento130 pagineCS507 - Final - Term - Solved - MCQs - Mega - File 232323 PDFMOHSIN AKHTAR0% (1)
- A Comprehensive IT AuditDocumento4 pagineA Comprehensive IT AuditMazharRizviNessuna valutazione finora
- Kunci Jawaban Alan Denis (Exercises) 141Documento10 pagineKunci Jawaban Alan Denis (Exercises) 141Michael Christian GunawanNessuna valutazione finora
- Cs507 20 Midterm SolvedpapersDocumento69 pagineCs507 20 Midterm SolvedpapersKamran MahmoodNessuna valutazione finora
- BSBINM501 Manage An Information or Knowledge Management SystemDocumento5 pagineBSBINM501 Manage An Information or Knowledge Management SystemajayNessuna valutazione finora
- Assignno 7 160617174951Documento11 pagineAssignno 7 160617174951Swapneal ShashiNessuna valutazione finora
- Test 5Documento111 pagineTest 5JeejuNessuna valutazione finora
- 4856 Assignment# 6Documento4 pagine4856 Assignment# 6Harmanjot KaurNessuna valutazione finora
- Mock Exam - IB2420 2008Documento4 pagineMock Exam - IB2420 2008Apos Tolis Yeorgaroudakis-VallisNessuna valutazione finora
- Requirements AnalysisDocumento9 pagineRequirements AnalysisBella BabierraNessuna valutazione finora
- Comp4 (Accounting Information System)Documento8 pagineComp4 (Accounting Information System)Ren Flores ViluanNessuna valutazione finora
- CH 03Documento57 pagineCH 03Sukumar MokshagundamNessuna valutazione finora
- Model Question Paper (MS-205)Documento28 pagineModel Question Paper (MS-205)Abhishek JhaNessuna valutazione finora
- Systems AuditDocumento38 pagineSystems AuditSimon RuoroNessuna valutazione finora
- Top10 It Audit FindingsDocumento6 pagineTop10 It Audit FindingsaliorkunNessuna valutazione finora
- IT Audit Basics The IS Audit Process by S. Anantha Sayana, CISA, CIADocumento4 pagineIT Audit Basics The IS Audit Process by S. Anantha Sayana, CISA, CIAMaria Alexandra Campoverde PesantezNessuna valutazione finora
- Questionnairre: Choosing Respondents To QuestionnaireDocumento5 pagineQuestionnairre: Choosing Respondents To QuestionnairegauravNessuna valutazione finora
- Jurnal IS - Audit - ProcessDocumento4 pagineJurnal IS - Audit - ProcessLyle Walt0% (1)
- Is Security AuditDocumento52 pagineIs Security AuditNivithaNessuna valutazione finora
- Mc090403758 Muhammad Shahzad Qamar Assignment No. 02 Information Systems CS507Documento4 pagineMc090403758 Muhammad Shahzad Qamar Assignment No. 02 Information Systems CS507shahzadNessuna valutazione finora
- Chapter 3 SolutionsDocumento16 pagineChapter 3 SolutionsPrabhjot SinghNessuna valutazione finora
- System Development Life CycleDocumento12 pagineSystem Development Life CycleReiny Rose AutrizNessuna valutazione finora
- Network & System Security: Monday, 11 February 2008Documento7 pagineNetwork & System Security: Monday, 11 February 2008buyaka12Nessuna valutazione finora
- Information SystemsDocumento5 pagineInformation SystemsDumisani NyathiNessuna valutazione finora
- Yash Jani Roll No 18 MISDocumento26 pagineYash Jani Roll No 18 MISHardik PuchhadiyaNessuna valutazione finora
- IT - Information Systems AuditingDocumento4 pagineIT - Information Systems AuditingIlma Hudalina FumasaNessuna valutazione finora
- Requirement ElicitationDocumento6 pagineRequirement ElicitationJitesh Emmanuel100% (1)
- Software Defect PreventionDocumento48 pagineSoftware Defect PreventionTayyaba NiaziNessuna valutazione finora
- HRM543 Chapter3Documento53 pagineHRM543 Chapter3La LunaNessuna valutazione finora
- Role of It in A Supply Chain (Repaired)Documento21 pagineRole of It in A Supply Chain (Repaired)SEHAR ABBASINessuna valutazione finora
- Computing Notes - A LevelDocumento185 pagineComputing Notes - A Levelkeith magaka92% (12)
- School of Information TechnologyDocumento6 pagineSchool of Information Technologyhaggele haggeleNessuna valutazione finora
- CS507 Midterm Paper 2Documento6 pagineCS507 Midterm Paper 2Power GirlsNessuna valutazione finora
- SPRING 2014: Q.No.1 Professor A. Van Cauwenbergh of Antwerp University, in A Paper Presented at TheDocumento8 pagineSPRING 2014: Q.No.1 Professor A. Van Cauwenbergh of Antwerp University, in A Paper Presented at TheRituTiwariNessuna valutazione finora
- BBA (IT) Assignment Answer SheetDocumento5 pagineBBA (IT) Assignment Answer SheetDarsh MehtaNessuna valutazione finora
- Pre 5 - Preliminary ExaminationDocumento3 paginePre 5 - Preliminary ExaminationMarivic TolinNessuna valutazione finora
- System Audit ExplainedDocumento9 pagineSystem Audit Explainedtony mutuaNessuna valutazione finora
- Management Information System MISDocumento5 pagineManagement Information System MISSyeda hudaibiyaNessuna valutazione finora
- JointanddevelopmentDocumento4 pagineJointanddevelopmentrealna real100% (1)
- Prepared By: Melissa T. GuillermoDocumento37 paginePrepared By: Melissa T. GuillermomtguillermoNessuna valutazione finora
- GOV Finals 1Documento14 pagineGOV Finals 1수지Nessuna valutazione finora
- Mis Slide 04Documento68 pagineMis Slide 04Ismatullah ZazaiNessuna valutazione finora
- MGT422Documento8 pagineMGT422Uzair FarooqNessuna valutazione finora
- eSACModel PDFDocumento9 pagineeSACModel PDFHayri Can DuygunNessuna valutazione finora
- Interactive Learning: 1. Introduction and Objectives of The ProjectDocumento69 pagineInteractive Learning: 1. Introduction and Objectives of The ProjectThansiya ThansiNessuna valutazione finora
- Chapter 5 System Development and Program Change Activities PT 1Documento2 pagineChapter 5 System Development and Program Change Activities PT 1Hiraya ManawariNessuna valutazione finora
- TBIT Arpit TakDocumento5 pagineTBIT Arpit TakArpit TakNessuna valutazione finora
- System DevelopmentDocumento22 pagineSystem DevelopmentdiyaNessuna valutazione finora
- 1b Requirements EngineeringDocumento49 pagine1b Requirements EngineeringpnaronaNessuna valutazione finora
- Im1 - Chapter 4Documento5 pagineIm1 - Chapter 4Si EfNessuna valutazione finora
- 1) About The Pandemic COVID-19Documento2 pagine1) About The Pandemic COVID-19محسين اشيكNessuna valutazione finora
- Sc10 - Worksheet On Atoms and IonsDocumento6 pagineSc10 - Worksheet On Atoms and IonsAnmol AgarwalNessuna valutazione finora
- Unit 1 My Hobbies Lesson 1 Getting StartedDocumento14 pagineUnit 1 My Hobbies Lesson 1 Getting StartedhienNessuna valutazione finora
- #5-The Specialities in The Krithis of Muthuswamy DikshitharDocumento5 pagine#5-The Specialities in The Krithis of Muthuswamy DikshitharAnuradha MaheshNessuna valutazione finora
- MikroekonomiDocumento1 paginaMikroekonomiYudhaPrakosoIINessuna valutazione finora
- Letter For LACDocumento7 pagineLetter For LACDahlia G. MaglasangNessuna valutazione finora
- Class XI-Writing-Job ApplicationDocumento13 pagineClass XI-Writing-Job Applicationisnprincipal2020Nessuna valutazione finora
- GE Elec 7 UNIT-3 NoDocumento22 pagineGE Elec 7 UNIT-3 NoLyleNessuna valutazione finora
- Business ProposalDocumento35 pagineBusiness ProposalMJ MacapagalNessuna valutazione finora
- Copper For BusbarDocumento60 pagineCopper For BusbarSunil Gadekar100% (3)
- 2018-3-27 MIDAS Civil Presentation Curved BridgesDocumento57 pagine2018-3-27 MIDAS Civil Presentation Curved BridgesShishir Kumar NayakNessuna valutazione finora
- Design and Fabrication of Light Electric VehicleDocumento14 pagineDesign and Fabrication of Light Electric VehicleAshish NegiNessuna valutazione finora
- Rabbit Book PDFDocumento20 pagineRabbit Book PDFMatumelo Rebecca DaemaneNessuna valutazione finora
- Development and Application of "Green," Environmentally Friendly Refractory Materials For The High-Temperature Technologies in Iron and Steel ProductionDocumento6 pagineDevelopment and Application of "Green," Environmentally Friendly Refractory Materials For The High-Temperature Technologies in Iron and Steel ProductionJJNessuna valutazione finora
- Maxdb Backup RecoveryDocumento44 pagineMaxdb Backup Recoveryft1ft1Nessuna valutazione finora
- Sagan WaltzDocumento14 pagineSagan WaltzKathleen RoseNessuna valutazione finora
- MC-8002 Mixer 2Documento1 paginaMC-8002 Mixer 2JAIDEV KUMAR RANINessuna valutazione finora
- Year 10 English Unit Plan AdvertisingDocumento5 pagineYear 10 English Unit Plan Advertisingapi-333849174Nessuna valutazione finora
- CE - 441 - Environmental Engineering II Lecture # 11 11-Nov-106, IEER, UET LahoreDocumento8 pagineCE - 441 - Environmental Engineering II Lecture # 11 11-Nov-106, IEER, UET LahoreWasif RiazNessuna valutazione finora
- Ancient India: Book Recommendation: Indian Feudalism Urban Decay in India - RS SharmaDocumento5 pagineAncient India: Book Recommendation: Indian Feudalism Urban Decay in India - RS SharmaShraddha 7Nessuna valutazione finora
- Apspdcl PDFDocumento21 pagineApspdcl PDFK.sanjeev KumarNessuna valutazione finora
- Library SectionsDocumento4 pagineLibrary SectionsGello Sotnuiq100% (4)
- 6 1 Maxima and MinimaDocumento10 pagine6 1 Maxima and MinimaSebastian GarciaNessuna valutazione finora
- Nursing Care Plan Diabetes Mellitus Type 1Documento2 pagineNursing Care Plan Diabetes Mellitus Type 1deric85% (46)
- Minolta Spotmeter f-1 PDFDocumento50 pagineMinolta Spotmeter f-1 PDFmacpator100% (1)
- Pursanova IXC ManualDocumento16 paginePursanova IXC ManualHector Serrano MagañaNessuna valutazione finora
- Wec14 01 Rms 20230112Documento23 pagineWec14 01 Rms 20230112Shafay SheikhNessuna valutazione finora
- File Server Resource ManagerDocumento9 pagineFile Server Resource ManagerBùi Đình NhuNessuna valutazione finora
- Concor PI CCDS 11 All StrengthsDocumento10 pagineConcor PI CCDS 11 All Strengthsgigid afandiNessuna valutazione finora
- Concept of ConstitutionDocumento32 pagineConcept of ConstitutionDorepe Icon0% (1)