Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Tut 4
Caricato da
Bibek ShresthaDescrizione originale:
Titolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Tut 4
Caricato da
Bibek ShresthaCopyright:
Formati disponibili
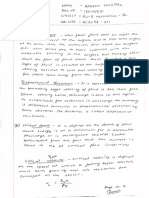
Q1. What are the essential ingredients of a symmetric cipher?
= Plaintext, encryption algorithm, secret key, cipher text, decryption algorithm.
Q2. What are the two basic functions used in encryption algorithms?
= Permutation and substitution.
Q3. How many keys are required for two people to communicate via a symmetric cipher? How many
keys are required for n people to communicate with each other securely?
= One secret key. N (n-1)/2 keys
Q4. What is the difference between a block cipher and a stream cipher?
= A stream cipher is one that encrypts a digital data stream one bit or one byte at a time. A block
cipher is one in which a block of plaintext is treated as a whole and used to produce a cipher text block
of equal length.
Q5. What are the two general approaches to attacking a cipher?
= Cryptanalysis and brute force.
Q6.List and briefly define types of cryptanalytic attacks based on what is known to the attacker.
Type of attack Known To Cryptanalyst
. Cipher text only . Encryption algorithm
. Cipher text to be decoded
. Known plaintext . Encryption algorithm
. Cipher text to be decoded
. one or more plaintext-cipher text pairs formed
with the secret key
. Chosen plaintext . Encryption algorithm
. Cipher text to be decoded
.Plaintext message chosen by cryptanalyst,
together with its corresponding cipher text
generated with the secret key
. Chosen cipher text . Encryption algorithm
. Cipher text to be decoded
. Purported cipher text chosen by cryptanalyst,
together with its corresponding decrypted
plaintext generated with the secret key
. Chosen text . Encryption algorithm
. Cipher text to be decoded
.Plaintext message chosen by cryptanalyst,
together with its corresponding cipher text
generated with the secret key
. Purported cipher text chosen by cryptanalyst,
together with its corresponding decrypted
plaintext generated with the secret key
7) What are two problems with the one-time pad?
1. The one time pad needs to be truly random. Pseudo random generates are quick however
they can be predicated.
2. The second is practicability of being able to transmit the number of keys securely to the
receiver. For every bit of plain text, there is also 1bit of key.
8) What are the drawbacks of steganography?
1. The confidentiality of information is maintained by the algorithms, and if the algorithms are
known then this technique is of no use.
2. Password leakage may occur and it leads to the unauthorized access of data.
9) Explain each component in the cryptography. (E.g. Cipher, cipher text, plain text, etc.)
a) Plaintext- It is the original message.
b) Cipher text- The coded message
c) Enciphering or encryption- Process of converting from plain text to cipher text.
d) Deciphering or decryption- Restoring the plaintext from the cipher text.
e) Cryptography- Study of encryption.
Task2
1. One way to solve the key distribution problem is to use a line from a book that both the sender
and the receiver possess. Typically, at least in spy novels, the first sentence of a book serves
as the key. The particular scheme discussed in this problem is from one of the best suspense
novels involving secret codes, talking to Strange Men, by Ruth Rendell. Work this problem
without consulting that book! Consider the following message: SIDKHKDM AF HCRKIABIE
SHIMC KD LFEAILA This cipher text was produced using the first sentence of The Other Side of
Silence (a book about the spy Kim Philby)
The sentence is: The snow lay thick on the steps and the snowflakes driven by the wind looked black
in the headlights of the cars. A simple substitution cipher was used.
a. What is the encryption algorithm?
b. How secure is it?
c. To make the key distribution problem simple, both parties can agree to use the first or last sentence
of a book as the key. To change the key, they simply need to agree on a new book. The use of the first
sentence would be preferable to the use of the last. Why?
ANSWER: a. the first letter t corresponds to A, the second letter h corresponds to B, e is C, s is D, and
so on. Second and subsequent occurrences of a letter in the key sentence are ignored. The result:
cipher text: SIDKHKDM AF HCRKIABIE SHIMC KD LFEAILA
Plaintext: basilisk to leviathan blake is contact
b. It is a monalphabetic cipher and so easily breakable.
c. The last sentence may not contain all the letters of the alphabet. If the first sentence is used, the
second and subsequent sentences may also be used until all 26 letters are encountered.
Potrebbero piacerti anche
- Computer Security AsDocumento4 pagineComputer Security AsHagos gebreslasieNessuna valutazione finora
- Advanced Encryption Standards (Aes)Documento13 pagineAdvanced Encryption Standards (Aes)pulikondaNessuna valutazione finora
- Presented By: Shibani Sarangi IT Branch, Regd No. 1001289324 Guided By: Prof. XDocumento22 paginePresented By: Shibani Sarangi IT Branch, Regd No. 1001289324 Guided By: Prof. XChandra ShekarNessuna valutazione finora
- Cryptography and CryptanalysisDocumento10 pagineCryptography and CryptanalysisDharma ReddyNessuna valutazione finora
- CryptographyDocumento37 pagineCryptographySamir JhaNessuna valutazione finora
- Lecture Number 1Documento20 pagineLecture Number 1AnAs FFNessuna valutazione finora
- Symmetric Ciphers: Data Encryption & Security (CEN-451) Spring 2020, BUKCDocumento26 pagineSymmetric Ciphers: Data Encryption & Security (CEN-451) Spring 2020, BUKCMuhammad RehanNessuna valutazione finora
- Cryptography TechknowxpressDocumento28 pagineCryptography TechknowxpressMeet SindhalNessuna valutazione finora
- ReportDocumento60 pagineReportHema SudhakarNessuna valutazione finora
- Is PTSSSS: AxssanboyDocumento3 pagineIs PTSSSS: AxssanboyCabdi Fitaax KulmiyeNessuna valutazione finora
- Classical Encryption CipherDocumento164 pagineClassical Encryption CipherShahriarNessuna valutazione finora
- Computer Security: Computer Threats and EncryptionDocumento21 pagineComputer Security: Computer Threats and EncryptionPro NebyuNessuna valutazione finora
- CryptographyDocumento23 pagineCryptographyAnubhav KumarNessuna valutazione finora
- Chapter Two - Fundamentals of CryptographyDocumento107 pagineChapter Two - Fundamentals of CryptographyJONAS J JONASNessuna valutazione finora
- Lecture 1Documento54 pagineLecture 1sottathalaNessuna valutazione finora
- Classical CryptographyDocumento19 pagineClassical CryptographyMahiya Rahman RafaNessuna valutazione finora
- Ciphertext - WikipediaDocumento6 pagineCiphertext - WikipediaRommelBaldagoNessuna valutazione finora
- Unit - Ii: Traditional Symmetric-Key CiphersDocumento124 pagineUnit - Ii: Traditional Symmetric-Key Cipherssanthosh RNessuna valutazione finora
- Unit 3Documento47 pagineUnit 3Andualem BegunoNessuna valutazione finora
- CryptographyDocumento43 pagineCryptographyDENNIS AMANKWAHNessuna valutazione finora
- Classical Encryption Techniques: M. Odeo LecturerDocumento39 pagineClassical Encryption Techniques: M. Odeo LecturerSNessuna valutazione finora
- 2 Classical Encryption TechniquesDocumento10 pagine2 Classical Encryption TechniquesAbdulrahman EidNessuna valutazione finora
- Unit 3 Cryptography and Public Key InfrastrucutreDocumento34 pagineUnit 3 Cryptography and Public Key InfrastrucutreDarshit ChhatbarNessuna valutazione finora
- Ise Chapter 3 CryptographyDocumento26 pagineIse Chapter 3 Cryptographylovelychawla30Nessuna valutazione finora
- Chapter 2Documento91 pagineChapter 2Destaye Sole WonideNessuna valutazione finora
- What Is Cryptography?: Decryption Secret KeyDocumento7 pagineWhat Is Cryptography?: Decryption Secret KeyalvincardonaNessuna valutazione finora
- CryptographyDocumento30 pagineCryptographychelesani ngwenyaNessuna valutazione finora
- Module 3 - CryptographyDocumento25 pagineModule 3 - CryptographyDon JinoNessuna valutazione finora
- CH 2 ISDocumento12 pagineCH 2 IStiwarisapana036Nessuna valutazione finora
- Cryptography (Encryption Techniques) : TerminologyDocumento69 pagineCryptography (Encryption Techniques) : TerminologyBelachew ZerihunNessuna valutazione finora
- A.J.Cipher: Aakash Jitendra Kumar Soni Bharti SharmaDocumento6 pagineA.J.Cipher: Aakash Jitendra Kumar Soni Bharti Sharmairfan123456Nessuna valutazione finora
- CryptoDocumento24 pagineCryptoshivani.cs1995Nessuna valutazione finora
- CryptanalysisDocumento13 pagineCryptanalysisRahmatullah MehrabiNessuna valutazione finora
- Chapter 8 - Cryptographic Tools Algorithms and ProtocolDocumento17 pagineChapter 8 - Cryptographic Tools Algorithms and ProtocolJasminNessuna valutazione finora
- What Is Cryptography?: Cryptography Is The Science of Using Mathematics To Encrypt and Decrypt DataDocumento10 pagineWhat Is Cryptography?: Cryptography Is The Science of Using Mathematics To Encrypt and Decrypt Datadivya6990Nessuna valutazione finora
- Need of Cryptography Types of Attacks Techniques of Cryptography Encryption AlgorithmDocumento31 pagineNeed of Cryptography Types of Attacks Techniques of Cryptography Encryption AlgorithmMin Min ZawNessuna valutazione finora
- ch2 CryptograpyDocumento73 paginech2 Cryptograpyfarahchihi15Nessuna valutazione finora
- CryptographyDocumento11 pagineCryptographyMahak AhujaNessuna valutazione finora
- Lesson 7Documento42 pagineLesson 7Nithya NairNessuna valutazione finora
- Chapter 2 CyptographyDocumento52 pagineChapter 2 CyptographyEsta AmeNessuna valutazione finora
- Python For Offensive PenTest A Practical Guide To ... - (Chapter 6 Abuse of Cryptography by Malware)Documento19 paginePython For Offensive PenTest A Practical Guide To ... - (Chapter 6 Abuse of Cryptography by Malware)Darryl Martin MirandaNessuna valutazione finora
- Chapter 2 & 3Documento20 pagineChapter 2 & 3Yakubu AliuNessuna valutazione finora
- A10 CryptographyDocumento20 pagineA10 CryptographyMohammed Arbaz Salim KhanNessuna valutazione finora
- Crypto IntroductionDocumento26 pagineCrypto Introductionunknown studentNessuna valutazione finora
- CH 3Documento46 pagineCH 3አርቲስቶቹ Artistochu animation sitcom by habeshan memeNessuna valutazione finora
- Report PDFDocumento35 pagineReport PDFPramod KumarNessuna valutazione finora
- Lecture 9Documento86 pagineLecture 9Alhussain DarbiNessuna valutazione finora
- 02 Symmetric CiphersDocumento73 pagine02 Symmetric CiphersGeorgeStenNessuna valutazione finora
- U21CS601 CT Unit 123 Part B QADocumento13 pagineU21CS601 CT Unit 123 Part B QASanthosh kannaNessuna valutazione finora
- Cryptography and Its TypesDocumento10 pagineCryptography and Its TypesFaizan AhmadNessuna valutazione finora
- CAP361: Security and Privacy of Information Lecture Number 05-08 Bhagat AvinashDocumento73 pagineCAP361: Security and Privacy of Information Lecture Number 05-08 Bhagat AvinashShri Prashant JhaNessuna valutazione finora
- PU Is Security - 5. Net Security Cryptography RDocumento40 paginePU Is Security - 5. Net Security Cryptography RByu PALEMBANGNessuna valutazione finora
- 06 Chapter1Documento27 pagine06 Chapter1Sravya ReddyNessuna valutazione finora
- Cryptography Course WorkDocumento27 pagineCryptography Course WorkSovan PalNessuna valutazione finora
- Classical Encryption Techniques: Lecture-2Documento54 pagineClassical Encryption Techniques: Lecture-2nibar dyllanNessuna valutazione finora
- Encryption StandardsDocumento76 pagineEncryption Standardsbhasker7100% (1)
- Cryptographic AlgorithmsDocumento4 pagineCryptographic AlgorithmstedsgamerNessuna valutazione finora
- New Security Lectures FinallyDocumento87 pagineNew Security Lectures Finallyطيبه محمد احمد حمد هندسة تقنيات الحاسوبNessuna valutazione finora
- Securing Network Transactions - Pptx/vijetha BhatDocumento27 pagineSecuring Network Transactions - Pptx/vijetha BhatVijetha bhatNessuna valutazione finora
- Cryptography and Public Key Infrastructure on the InternetDa EverandCryptography and Public Key Infrastructure on the InternetValutazione: 5 su 5 stelle5/5 (1)
- 05 SlideDocumento42 pagine05 SlideAtheerNessuna valutazione finora
- (Clifford) Advances in Engineering Software PDFDocumento796 pagine(Clifford) Advances in Engineering Software PDFNguyễn Tấn LậpNessuna valutazione finora
- TIMO Selection Primary 5Documento2 pagineTIMO Selection Primary 5Qurniawan Agung Putra100% (5)
- Calibration of SensorsDocumento5 pagineCalibration of SensorsSubhrajit MoharanaNessuna valutazione finora
- Rakesh Mandal 180120031Documento7 pagineRakesh Mandal 180120031Rakesh RajputNessuna valutazione finora
- Math 139-1 Lesson 6 and 7Documento52 pagineMath 139-1 Lesson 6 and 7jenny teresa50% (2)
- Rish em 3490 Ss Manual Rev-C 1phDocumento7 pagineRish em 3490 Ss Manual Rev-C 1phpitambervermaNessuna valutazione finora
- Programme Number: 1 InputDocumento18 pagineProgramme Number: 1 InputroshanNessuna valutazione finora
- Ds and AlgoDocumento2 pagineDs and AlgoUbi BhattNessuna valutazione finora
- Bayesian Analysis of Working Capital Management On Corporate Profitability: Evidence From IndiaDocumento19 pagineBayesian Analysis of Working Capital Management On Corporate Profitability: Evidence From IndiaHargobind CoachNessuna valutazione finora
- Liquid Holdup in PackedDocumento11 pagineLiquid Holdup in PackedVictor VazquezNessuna valutazione finora
- RoboticsDocumento579 pagineRoboticsDaniel Milosevski83% (6)
- Gomory's CutsDocumento7 pagineGomory's Cutsgladiator001Nessuna valutazione finora
- St501-Ln1kv 04fs EnglishDocumento12 pagineSt501-Ln1kv 04fs Englishsanthoshs241s0% (1)
- Emf Questions For AssignmentDocumento7 pagineEmf Questions For AssignmentDrGopikrishna PasamNessuna valutazione finora
- VCE Technical Drawing SpecsDocumento36 pagineVCE Technical Drawing SpecsLucas GauciNessuna valutazione finora
- Robot Toolbox MatlabDocumento166 pagineRobot Toolbox Matlabbboby14100% (1)
- Climate WorkbookDocumento119 pagineClimate WorkbookreaderdarkeyeNessuna valutazione finora
- REF615 Standard ConfigurationDocumento11 pagineREF615 Standard Configurationmaruf048Nessuna valutazione finora
- Fluid Mechanics and Machinery - Lecture Notes, Study Material and Important Questions, AnswersDocumento3 pagineFluid Mechanics and Machinery - Lecture Notes, Study Material and Important Questions, AnswersM.V. TVNessuna valutazione finora
- Variables Answers ReasonsDocumento4 pagineVariables Answers ReasonsEDEN FE D. QUIAPONessuna valutazione finora
- A Revised Double Sampling Control ChartDocumento9 pagineA Revised Double Sampling Control Chartspitraberg100% (2)
- Solving Cubic Equations Roots Trough Cardano TartagliaDocumento2 pagineSolving Cubic Equations Roots Trough Cardano TartagliaClóvis Guerim VieiraNessuna valutazione finora
- Guided Revision: Target: JEE (Main + Advanced) - 2019Documento3 pagineGuided Revision: Target: JEE (Main + Advanced) - 2019Mridul ChhipaNessuna valutazione finora
- Placing DatumsDocumento29 paginePlacing Datumssaravind120% (1)
- 6 Prosiding ICM2E 2017Documento434 pagine6 Prosiding ICM2E 2017Andinuralfia syahrirNessuna valutazione finora
- Basis Path TestingDocumento4 pagineBasis Path TestingKaushik MukherjeeNessuna valutazione finora
- Carreon WS06Documento4 pagineCarreon WS06Keneth CarreonNessuna valutazione finora
- Machine Design - Spur GearsDocumento5 pagineMachine Design - Spur GearsKleeanne Nicole UmpadNessuna valutazione finora
- Prospeccion Geoelec Trica en Corrien Te Continua. Ernest0 Orellana. ParaninfoDocumento2 pagineProspeccion Geoelec Trica en Corrien Te Continua. Ernest0 Orellana. ParaninfoGustavo MiguelNessuna valutazione finora