Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
19i8 Ijaet0805874 Designing of A Smart Car
Caricato da
Anil Kumar BTitolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
19i8 Ijaet0805874 Designing of A Smart Car
Caricato da
Anil Kumar BCopyright:
Formati disponibili
International Journal of Advances in Engineering & Technology, May 2012.
©IJAET ISSN: 2231-1963
DESIGNING OF A SMART CAR USING ARM7
Narasimhulu. M, Naresh Kumar Reddy. B, Subrahmanya Sharma .G
Department of Electronics Engineering, KL University, Vijayawada, India
ABSTRACT
Security system nowadays become a need for vehicles and available with many modern features. This car
security system comes with extra secure access and message on GSM net. The system only can be accessed and
configured by owner using GSM module communication via mobile phone. In this project, when the car is theft,
an intruder alert message will be sent to the user’s phone through GSM communication and GPS positioning.
After the certain time, by using the GSM net and the GPS positioning techniques the probability of finding car
where accident occurs or the car parked location will done easily . And in this project the wireless camera is
used to capture the video in digital form. The digital video can be transferred into an image by using dot net and
image processing technologies. With ARM7 as the core, the new intelligent mobile vehicle checking system
integrated a lot of hardware modules such as video capture, GPS positioning and wireless transmission, the
design of the system software used the embedded software developing platform based on ADS integrated
development environment. By the hardware/software co-design, the new intelligent mobile vehicle checking
system implemented the functions of video capturing, intelligent plate distinguishing, GPS positioning and
wireless transmission, met the traffic auditing department’s needs about Mobile Vehicle Checking.
KEYWORDS: Mobile Vehicle checking, video capture, GPS, GPRS, embedded system
I. INTRODUCTION
In the past decades, the issue of security has become more significant and the need for effective
security systems has intensified [1]. Many areas were marked as restricted, since illegal access can
have serious consequences for homeland security and can even result in the loss of lives in the case of
an explosive armed vehicle. To increase security in access control applications for a vehicle that
enters a restricted area, this work proposes the architecture and installation of a vehicle inspection
system. Three different computer vision applications are integrated in the system, namely license plate
recognition, vehicle manufacturer/model detection and under-vehicle inspection. The systems use
several vehicle features to identify the vehicle from different aspects and their combination could
improve the overall system effectiveness and identify attempts of fraudulence, such as the use of
stolen plates. Typical applications would include high-security areas such as airports, embassies,
power plants and military camps. In these areas, registered vehicles are allowed to enter, where other
vehicles are prohibited. In the literature, License Plate Recognition (LPR) remains the principal
vehicle identifier. Systems of this type, detect the vehicle license plate, segment its characters and
proceed to character recognition. Such systems are still widely researched and used, despite the fact
that license plates can be easily altered in case of fraud. Fitting a piece of glass in front of the plate to
cause light deflection and replacing the plates with stolen or counterfeit ones, are just a few examples.
System effectiveness can be drastically improved if license plate recognition is combined with
simultaneous vehicle manufacturer and model recognition. In the latter, recognition is conducted
through the vehicle mask and the manufacturer logo and is based on machine learning techniques and
artificial intelligence. These features can help to identify a vehicle with a tampered or stolen plate.
With the development of technology, people have higher expectation of living, country has invested
a huge amount of money to the capital construction, especially to roads infrastructure. In this
situation, the roads infrastructure is developing fast, the highway mileage has enormous increase and
185 Vol. 3, Issue 2, pp. 185-191
International Journal of Advances in Engineering & Technology, May 2012.
©IJAET ISSN: 2231-1963
there is an increasing number of vehicles on the roads. However, the huge number of cars raises
problems of its own; there are more and more car thefts, lost and violations of rules which are given
serious attentions. The time which is spent on checking on the roads by the department of traffic
charge, check and police has been taken too much. Meanwhile, vehicles overload problem is getting
worse around the country. Because of the merits of high capacity, large services and economy, public
buses have become the main means of urban traffic. If the bus which took lots of people had a traffic
accident, the result would be serious. The main cause of those serious accidents is overload; therefore,
it is time to find some way to resolve this problem. However, most departments take care of this
problem in traditional way, such as manual judgment and road checking. This traditional vehicle
checking way has some faults such as leak checking, false checking, and is a heavy work for vehicle
checking people, so it needs to find a intelligent mobile vehicle checking system to replace the
traditional one. The new intelligent mobile vehicle checking system is designed to meet this need.
This paper is giving the main idea of designing of an intelligent mobile vehicle checking system
using ARM 7 and the GSM and GPS positioning techniques .In this paper the section 1describes the
introduction ,section 2 describes the system design and composition techniques and the processes of
video capture, vehicle licence recognition system and ARM7 peripheral interface. Section 3 describes
hardware design and section 4 describes the software design
1.1. RELATED WORK
In this paper we are using the ARM7 as the core and the GPS and GSM techniques for the position
and for sending the msg to mobile. We will also use the Bluetooth and 8051 controller in the place of
ARM 7 in order to perform the controlling of the system. The following section represents the system
function and composition of the system by using the ARM7.
II. SYSTEM FUNCTION AND COMPOSITION
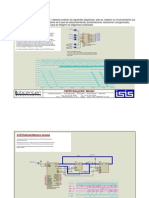
As shown in the figure 1, this system builds a new intelligent vehicle checking system based on
ARM7, embedded processing technology, processing technology of digital videos, vehicle
identification technology, GSM wireless mobile telecommunication technology, GPS positioning
technique, implements the checking to vehicles which break the rules or owe the charge. This system
has the following features.
2.1. Video Capture
When the system works, the camera in the front of the car collects the data automatically and saves it
in the video buffer,
2.2. Vehicle Recognition
The system recognizes the vehicle license by digital video data. The digital video is captured by the
digital camera. The dot net and image processing technologies are used to convert the digital data into
the image which contains the information of licence of the car. By collecting the data it will store the
licence number and information of the car.
Figure 1. System Composition
186 Vol. 3, Issue 2, pp. 185-191
International Journal of Advances in Engineering & Technology, May 2012.
©IJAET ISSN: 2231-1963
2.3. Communication Function
The vehicle checking terminal communicates with the server center by the SMS message on the GSM
net;
2.4. Gps Positioning
The system can correctly send the position and time of the checking vehicle to the server center by
GPS positioning, therefore, the terminals can be coordinated properly.
III. HARDWARE DESIGN
Intelligent mobile vehicle checking system is composed of ARM7 microprocessor, peripheral
equipment, and video capture, GPS positioning module GS-216 m, wireless telecommunication
module Q24PL002 and remote control receiver. The detailed hardware composition is shown in figure
2.
3.1. ARM7 microprocessor and peripheral equipment
The circuit of ARM7 microprocessor and peripheral equipment includes a ARM7 chip, a clock
circuit, a reset 115 circuit, a 32MB flash memory, a LCD. All of these make up the control and
process core of the system.
Figure 2. Hardware Composition
3.2. Video capture
The video capture module includes: video decoder and output, data buffering and data transmission.
The implementation-principle of video capture is shown in figure 3. The analog video signal captured
from the camera is changed to digital signal by SAAA7111A signal-chip video decoder. The
SAAA7111A signal-chip is initialized and controlled by ARM7. The SAAA7111A output data is
written into FIFO buffer. The ARM7 generates interrupt when the data reaches a certain amount. The
DMA is started after ARM7 interrupt and sends the video data into buffer.
Figure 3. Principles of video Capture
187 Vol. 3, Issue 2, pp. 185-191
International Journal of Advances in Engineering & Technology, May 2012.
©IJAET ISSN: 2231-1963
3.3. ARM7 architecture
Figure 4. ARM7 architecture
3.4. Equation output and input of GPS data
The GPS module in this system is GS-216m made by Gstar, Korea. The GPS module can receive the
data by connected to ARM7 development-board URAT0 through RS232 port. When the ARM7 chip
sends the instruction AT to GPS module, the GPS module starts receiving the data and saves it into
memory. This instruction sends the region information with the vehicle license information to the
support-server center through GSM net. Because the system is based on GPS data which is sent
through GPRS net, it must be initialed at first. The initial instructions are following:
Reset
User settings initialized
Press ++++++ to enter the setup mode…Done
Init command List:
AT+ID=X CR
AT+IP=X CR
AT+PORT=X CR
AT+HTH=X CR
AT+BAUD=X CR
AT+APN=X CR
AT+AGREE=X CR
AT+REST=X CR
AT+ID=X: this instruction is used to set the terminal address. Each device must be set the address
which indicates its ID, the default ID is 139XXXXXXXX. The default address is the SIM card mobile
phone number which contains 11 numbers, the address can be changed as required.
AT+ID=? : This instruction is used to inquire the ID of the terminal. The instruction can be used to
check whether the set of the device is correct.
AT+IP=X this instruction is used to set the IP address
of the server in surveillance centre. The format of IP is
X.X.X.X. AT+IP=? this instruction is used to inquire the
IP address.
AT+PORT=X this instruction is used to set the port number of the application software in
surveillance center server. AT+PORT=? this instruction is used to inquire the port number.
188 Vol. 3, Issue 2, pp. 185-191
International Journal of Advances in Engineering & Technology, May 2012.
©IJAET ISSN: 2231-1963
AT+HTH=X AT+HTH=? this instruction is used to set and inquire the time intervals of the GPS
positioning information which the terminals send automatically. The unit of the time interval is
second.
AT+BAUD=X AT+BAUD=? this instruction is used to set and inquire the initial baud rate. The
default is 4800 and does not need changing usually.
AT+APN=X AT+APN=? this instruction is used to set and inquire the connect port of GPRS
telecommunication. The default value is CMNET.
AT+AGREE=X AT+AGREE=? this instruction is used to set and inquire the net communication
protocol. The default value is TCP protocol. The terminal on car supports the UDP and the TCP
protocol. Users can change the protocol as needs.
3.5. GPRS Wireless Communication
The GPRS communication device used in this system consists of Q24PL002 GPRS module made by
Wave COM and the development-board. The GPRS module is installed on the development-board,
the RS232 port on the development-board is connected to URAT1 on the ARM7 experiment &
development board in order to implement that the ARM7 chip has control over the GPRS
communication device. The GPRS device is controlled by the ARM7 through AT instructions. The
GPRS device includes 24 operation instructions in common use, 10 talking operation instructions, 9
message operation instructions, 7 TCP/IP operation instructions. Some simple operations, such as
signal strength checking, module vision checking, serial port baud rate checking, SIM card state
reading, should be done when the GPRS device connects to the support server center. After making
sure that the state which the ARM7 experiment-development board connects to the server center by
the GPRS device is normal, the ARM7 chip outputs the AT instructions in order to send the vehicle-
region information which is acquired by GPS module and vehicle license information which is
acquired by vehicle-checking and distinguishing device to the server center through GSM net. After
receiving the data, the server center compares the data with the black list in database and sends the
result to the ARM7 experiment-development board through GSM net.
IV. SOFTWARE DESIGN
The software of the new intelligent mobile vehicle checking system includes two parts, the remote-
server center software and embedded terminal software. The development of the software is based on
ADS integrated development environment.
4.1. Introduction of ADS integrated development environment
The ADS integrated development environment is a microcontroller for ARM which is developed by
the ARM Company, its full name is ARM Developer Suit and the mature vision is ADS1.2. ADS1.2
supports all the ARM microcontroller before ARM10, supports the software debug and JTAG
simulate, supports the assembly language, C and C++ language. It has the merits of high compile
efficiency and rich system libraries. The environment can run on Windows98 WindowsXP Windows
2000 and Red Hat Linux.
Figure 5. Composition software
189 Vol. 3, Issue 2, pp. 185-191
International Journal of Advances in Engineering & Technology, May 2012.
©IJAET ISSN: 2231-1963
4.2. Functions of the system software and implementation
4.2.1. Composition of software
The server center saves the data library which contains the newest vehicles in the ‘black list’ or the
date from Q24PL002 into SD card. The video capture software collects the video data and changes its
format, and then the video capture software sends the data to the identification buffer. Date is sampled
and sent to the vehicle checking software. The vehicle checking software identifies the vehicle license
and compares it with the data in the SD card. If the car is the one which breaks the rules, the software
displays the information of the car (include the license of the car, the name of the car and its owner).
If the information is not in the SD card, the soft will inquire the server center and send the result to
terminal.
4.2.2. Implementation
The design of this system software can be divided into four modules, they are video capture module,
vehicle license identification module, the graphical user interface module and communication module.
The video capture module is executed in interrupt instruction, the vehicle license identification
module and the graphical user interface module are executed in the main programme and the
communication module is executed in a programme alone. The communication between each module
depends on the message passing.
4.3 Development of interrelated software
4.3.1. Development of Boot Loader
Boot Loader is a boot programme which runs before the operating system nucleus. This programme is
on the entrance of reset, and implements the download and load of programme.
4.3.2. Driver
The abstraction level separates the part which depends on the hardware platform and makes the
amount of work reach least. The driver just needs to design the codes which are relate to hardware,
and provide a unified interface for the operation software. During the development of the embedded
software used in the terminal, the driver of SD card, the driver of serial port and the driver of remote
control are designed.
4.3.3. Identification software
The vehicle license identification module includes the region location of vehicle license, the pre-
processing of the vehicle license image, the cutting up and Identification of the single character on the
vehicle license. The software depends on the date to implement real-time Identification of vehicle
license.
V. CONCLUSIONS AND FURTHER RECOMMENDATIONS
This paper proposes the integration of a vehicle inspection system, which significantly increases
security in vehicle identification by integrating different computer vision modules. Three different
subsystem implementations were presented, namely the license plate recognition system, vehicle
manufacturer/ model detection and under-vehicle inspection. The three distinct modules were
analyzed and discussed. Results show that each method reaches good success rates, which in turn
indicate that these modules can be used to boost the overall performance of an integrated platform for
security inspection and access control. Finally, issues such as installation and operation principles
were briefly discussed. The proposed system could be installed in entrance check points that require
high security standards, such as government buildings, army camps or country borders and it can
considerably facilitate prompt and effective vehicle inspection. Immediate benefits are the ability to
reduce the number of personnel required to operate security gates, as well as to increase their level of
awareness, while ensuring their personal safety. The new intelligent mobile vehicle checking system
uses the detection technique of video capture, the wireless communication technique, meets the traffic
auditing department’s needs about Mobile Vehicle Checking. The system has the advantages of small
size, low costs, full featured and powerful expansibility.
VI. RESULTS
By using this smart car system we will easily find the location of a car .By using the GPS and
GSM technique the longitudinal values will send to the mobile which is connected to the system. By
190 Vol. 3, Issue 2, pp. 185-191
International Journal of Advances in Engineering & Technology, May 2012.
©IJAET ISSN: 2231-1963
calculating these values in Google earth we will find out the location. And by using the Wireless
camera the thief image is also capture so the thief will easily caught. And by using this system the
traffic will be easily controlled. So by using this system the vehicles easily recognised which are not
follows the traffic rules.
ACKNOWLEDGEMENTS
We thank to our principal, Prof. K .Raja shekar Rao, for providing necessary facilities towards
carrying out this work. We acknowledge the diligent efforts of our Head of the Department
Dr.S.Balaji in assisting us towards implementation of this idea.
REFERENCES
[1] Inigo R.M., Application of machine vision to traffic monitoring and control, IEEE Transactions
Vehicular Technology, 1989, 38(3):112 122.
[2] Lotufo R.A., Morgan A.D., Johnson A.S.Automatic number-plate recognition. Proceedings of image
Analysis for transport applications, IEE Colloquium, 1990(6):1-6.
[3] Robert T.Collins, Alan J.Lipton, etal.A System for Video Surveillance and Monitoring. Carnegie Mellon
University, 2000.
[4] K.W.Dickinson, C.L.Wan, Road traffic monitoring using the Trip system.IEEE 2nd int.Conf.Road Traffic
Monitoring, 1989-02:56-60.
[5] A.S.Johnson,B.M.Bird.Number-;pate matching for automatic vehicle identification.Proceedings of electronic
image and image processing in security and forensic science,IEEE Colloquium,1990(4):1-8.
[6] McKenna K, you Brandt A.Moving Object Recognition Using An Adaptive Background
Memory.Cappellini,Time-Varying Image Processing and Moving Object Recongnition.Amsterdam;Elsevier
Science,1990;289-296.
[7] W.Grimson, C.Stauffer,R.Romano,etal.Using adaptive tracking to classify and monitor activities in a site
.IEEE Conf.ON Computer Vision and Pattern Recongnition.1998:22-29.
[8] C.Stauffer,W.E.L.Grimson.Learning Patterns of Activity Using Real- Time Tracking.IEEE
Trans,PAMI,2000,22(8):747-757
[9] D. Robson, “Safe and secure in transit”, Imaging and Machine Vision Europe, Dec. 2007 – Jan. 2008,
online article: http://www.imveurope.com/ /features/feature.php?feature_id=50, last date of access: 27/11/2009.
[10] K.V.S.S.S.S. Salram, N. Gunasekaran, and S. Rama Reddy, “Bluetooth in Wireless Communication”,
IEEE Communications Magazine, June
2002, pp. 90-96.
[11] G. Lamm, G. Falauto, J. Estrada, and J. Gadiyaram, "Bluetooth wireless networks security features", Proc.
IEEE Workshop Information Assurance and Security, 2001, pp.265 -272 .
[12] R. Nüsser and R. Pelz, "Bluetooth-based wireless connectivity in an automotive environment", Proc.
IEEE Vehicular Technology Conf.— Fall, vol. 4, 2000, pp.1935 -1942.
[13] P. D. Garner, “Mobile Bluetooth Networking: Technical considerations and applications”, The IEE,
Michael Faraday House, 2003, pp. 274-276.
[14] Albert S. Huang and Larry Rudolph, Bluetooth Essential for Programmers, Cambridge University press,
New Tork, 2007.
[15] P. Murphy, E. Welsh, and P. Frantz, "Using Bluetooth for short-term ad-hoc connections between moving
vehicles: A feasibility study", Proc. IEEE Vehicular Technology Conf. (VTC), pp.414 -418
Short Biography
M. Narasimhulu received B. Tech. degree from Sri Venkateswara University in 2010. He is
pursuing M Tech in Koneru Lakshamyya University.
B. Naresh Kumar received B. Tech. degree from Sri Venkateswara University. M Tech in
Koneru Lakshamyya University.
191 Vol. 3, Issue 2, pp. 185-191
Potrebbero piacerti anche
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (587)
- Audi - US A7 - 2014-2Documento49 pagineAudi - US A7 - 2014-2Anil Kumar BNessuna valutazione finora
- A Comparative Study of Gender and Age Classification in Speech SignalsDocumento12 pagineA Comparative Study of Gender and Age Classification in Speech SignalsAnil Kumar BNessuna valutazione finora
- Audi - US TDi - 2007Documento11 pagineAudi - US TDi - 2007Anil Kumar BNessuna valutazione finora
- Audi - US Full Line - 2009Documento16 pagineAudi - US Full Line - 2009Anil Kumar BNessuna valutazione finora
- Human Gender and Age Detection Based On Attributes of FaceDocumento16 pagineHuman Gender and Age Detection Based On Attributes of FaceAnil Kumar BNessuna valutazione finora
- Human Age and Gender Estimation Using Facial Image ProcessingDocumento5 pagineHuman Age and Gender Estimation Using Facial Image ProcessingAnil Kumar BNessuna valutazione finora
- Computer vision techniques for road pothole detectionDocumento16 pagineComputer vision techniques for road pothole detectionAnil Kumar BNessuna valutazione finora
- Audi A4-Product-Guide 2020Documento31 pagineAudi A4-Product-Guide 2020Mai PhaNessuna valutazione finora
- SCI PaperDocumento17 pagineSCI PaperAnil Kumar BNessuna valutazione finora
- Fusion of Local Binary Pattern and Local Phase Quantization Features Set For Gender Classification Using FingerprintsDocumento8 pagineFusion of Local Binary Pattern and Local Phase Quantization Features Set For Gender Classification Using FingerprintsAnil Kumar BNessuna valutazione finora
- The All New Mercedes AMG A 35 4MATICDocumento47 pagineThe All New Mercedes AMG A 35 4MATICAnil Kumar BNessuna valutazione finora
- Age Estimation and Gender Recognition Technique Using Deep LearningDocumento8 pagineAge Estimation and Gender Recognition Technique Using Deep LearningIJRASETPublicationsNessuna valutazione finora
- Applsci 12 05320 v2Documento15 pagineApplsci 12 05320 v2Anil Kumar BNessuna valutazione finora
- PN - DFCBU - 2020 - 01 - JAN - TATA MOTORS LIMITED - TIGOR - 11325010 - SIZE 297 (W) X 210 (H) MM - TIGOR MCE LEAFLET - For WebDocumento2 paginePN - DFCBU - 2020 - 01 - JAN - TATA MOTORS LIMITED - TIGOR - 11325010 - SIZE 297 (W) X 210 (H) MM - TIGOR MCE LEAFLET - For WebDevesh BholeNessuna valutazione finora
- A Feasibility Study On Real-Time Gender Recognition: IjarcceDocumento7 pagineA Feasibility Study On Real-Time Gender Recognition: IjarcceAnil Kumar BNessuna valutazione finora
- Age and Gender Identification in Social MediaDocumento8 pagineAge and Gender Identification in Social MediaAnil Kumar BNessuna valutazione finora
- A Study On Face Recognition Techniques With Age and Gender ClassificationDocumento6 pagineA Study On Face Recognition Techniques With Age and Gender ClassificationAnil Kumar BNessuna valutazione finora
- Age and gender classification with machine learningDocumento12 pagineAge and gender classification with machine learningAnil Kumar BNessuna valutazione finora
- Joint Estimation of Age and Gender From Unconstrained Face Images Using Lightweight Multi-Task CNN For Mobile ApplicationsDocumento4 pagineJoint Estimation of Age and Gender From Unconstrained Face Images Using Lightweight Multi-Task CNN For Mobile ApplicationsAnil Kumar BNessuna valutazione finora
- Age and Gender Prediction From Face Images Using Attentional Convolutional NetworkDocumento6 pagineAge and Gender Prediction From Face Images Using Attentional Convolutional NetworkAnil Kumar BNessuna valutazione finora
- Age and Gender Prediction Using Deep Convolutional Neural NetworksDocumento6 pagineAge and Gender Prediction Using Deep Convolutional Neural NetworksAnil Kumar BNessuna valutazione finora
- Age and Gender Recognition Using Multi-Task CNN: Duc-Quang Vu, Thi-Thu-Trang Phung, Chien-Yao Wang and Jia-Ching WangDocumento5 pagineAge and Gender Recognition Using Multi-Task CNN: Duc-Quang Vu, Thi-Thu-Trang Phung, Chien-Yao Wang and Jia-Ching WangAnil Kumar BNessuna valutazione finora
- Age and Gender Estimation Using Deep Residual Learning NetworkDocumento3 pagineAge and Gender Estimation Using Deep Residual Learning NetworkAnil Kumar BNessuna valutazione finora
- Automatic Age and Gender Estimation Using Deep Learning and Extreme Learning MachineDocumento11 pagineAutomatic Age and Gender Estimation Using Deep Learning and Extreme Learning MachineAnil Kumar BNessuna valutazione finora
- Age and Gender Classification Using Multiple Convolutional Neural NetworkDocumento11 pagineAge and Gender Classification Using Multiple Convolutional Neural NetworkAnil Kumar BNessuna valutazione finora
- Age Group and Gender Estimation in The Wild With Deep Ror ArchitectureDocumento11 pagineAge Group and Gender Estimation in The Wild With Deep Ror ArchitectureAnil Kumar BNessuna valutazione finora
- Age Group Classification and Gender Recognition From Speech With Temporal Convolutional Neural NetworksDocumento18 pagineAge Group Classification and Gender Recognition From Speech With Temporal Convolutional Neural NetworksAnil Kumar BNessuna valutazione finora
- A Study On Gender and Age Classification As A Vital Tools in The Identification and Verification SystemDocumento13 pagineA Study On Gender and Age Classification As A Vital Tools in The Identification and Verification SystemAnil Kumar BNessuna valutazione finora
- Sensors: Gender and Age Estimation Methods Based On Speech Using Deep Neural NetworksDocumento18 pagineSensors: Gender and Age Estimation Methods Based On Speech Using Deep Neural NetworksAnil Kumar BNessuna valutazione finora
- Real-Time Embedded Age and Gender Classification in Unconstrained VideoDocumento9 pagineReal-Time Embedded Age and Gender Classification in Unconstrained VideoAnil Kumar BNessuna valutazione finora
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (890)
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (399)
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (73)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2219)
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (344)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (265)
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (119)
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- Rectifier Circuits: Half-Wave Rectifier (HWR)Documento18 pagineRectifier Circuits: Half-Wave Rectifier (HWR)Md ArifNessuna valutazione finora
- DIWH Series: Diko Elektrikli Cihazlar San. Ve Tic. A.ŞDocumento19 pagineDIWH Series: Diko Elektrikli Cihazlar San. Ve Tic. A.ŞEric ToroNessuna valutazione finora
- Bluetooth Low Energy (BLE) 5 Module BT840F: SpecificationsDocumento26 pagineBluetooth Low Energy (BLE) 5 Module BT840F: SpecificationsArthit SomrangNessuna valutazione finora
- Installation and Use Instructions 7 Day Electronic Timer (TE103)Documento2 pagineInstallation and Use Instructions 7 Day Electronic Timer (TE103)eeindustrialNessuna valutazione finora
- HH100-HH120 English PDFDocumento18 pagineHH100-HH120 English PDFsil doroNessuna valutazione finora
- Radar Vs Stealth - Passive Radar & FutureDocumento8 pagineRadar Vs Stealth - Passive Radar & Futurelynx437Nessuna valutazione finora
- Samsung - NP R530 NP R730.Bremen L.ba41 XXXXXA - Rev.1.0.schematicsDocumento59 pagineSamsung - NP R530 NP R730.Bremen L.ba41 XXXXXA - Rev.1.0.schematicsTuput Amadre100% (1)
- Kurzweil MicropianoDocumento24 pagineKurzweil Micropianoestereo8Nessuna valutazione finora
- W810i Service ManualDocumento53 pagineW810i Service Manualamdomalik100% (2)
- A819 PDFDocumento4 pagineA819 PDFjpauloaliancaNessuna valutazione finora
- 3 Operation Instructions, PLC SystemDocumento25 pagine3 Operation Instructions, PLC SystemheemaNessuna valutazione finora
- Genaral Catalog PLC PanasonicDocumento36 pagineGenaral Catalog PLC Panasonicpeter08068350% (2)
- Gseriesr2.0 Printer Spare Parts List en UsDocumento14 pagineGseriesr2.0 Printer Spare Parts List en UsBrahiam ColmenaresNessuna valutazione finora
- Daily DigestDocumento2 pagineDaily DigesttechsmartNessuna valutazione finora
- Switching Power Supply Design Review - 60 Watt Flyback Regulator by Raoji Patel and Glen FRFTZ Slup072Documento17 pagineSwitching Power Supply Design Review - 60 Watt Flyback Regulator by Raoji Patel and Glen FRFTZ Slup072Burlacu AndreiNessuna valutazione finora
- Ch02 Wal MartDocumento1 paginaCh02 Wal MartMuhammad Shafiq GulNessuna valutazione finora
- User Manual: Tracer-AN SeriesDocumento44 pagineUser Manual: Tracer-AN SeriesSarah WoodNessuna valutazione finora
- Actividad 2. Comparativo de Circuitos DigitalesDocumento8 pagineActividad 2. Comparativo de Circuitos DigitalesArmando Guerrero RochaNessuna valutazione finora
- Bose Lifestyle 28 Repair - Schematics PDFDocumento32 pagineBose Lifestyle 28 Repair - Schematics PDFAurelio Machado75% (4)
- Ret620 Ansi BRDocumento4 pagineRet620 Ansi BRFernando TamayoNessuna valutazione finora
- C100 Service Training Manual: 3.2L Engine Mechanical Participant HandbookDocumento54 pagineC100 Service Training Manual: 3.2L Engine Mechanical Participant Handbooksertex_jo83% (6)
- RBS 6000 Technical DataDocumento15 pagineRBS 6000 Technical DataMohammed Makled100% (1)
- Solar Inverter XC Op Manual 990 4612DDocumento76 pagineSolar Inverter XC Op Manual 990 4612DPradeep Kumar SukumaranNessuna valutazione finora
- Metal Oxides Semiconductor CeramicsDocumento14 pagineMetal Oxides Semiconductor Ceramicsumarasad1100% (1)
- Analog Electronics - U. A. Bakshi and A. P. GodseDocumento124 pagineAnalog Electronics - U. A. Bakshi and A. P. GodseIrfan M IrshadNessuna valutazione finora
- Downloads Drivers Ds800 Development Suite Software 4 1 Ds800 en 133388Documento2 pagineDownloads Drivers Ds800 Development Suite Software 4 1 Ds800 en 133388saoNessuna valutazione finora
- 063927Documento4 pagine063927mprice2461Nessuna valutazione finora
- 14Φ Series Metal Oxide Varistor (MOV) Data Sheet: FeaturesDocumento12 pagine14Φ Series Metal Oxide Varistor (MOV) Data Sheet: Featuresirensy vivasNessuna valutazione finora
- User's Manual: STUF-200H Handheld Ultrasonic FlowmeterDocumento76 pagineUser's Manual: STUF-200H Handheld Ultrasonic FlowmeterLupu Vasile0% (1)
- Video Processor Vep-2100fDocumento18 pagineVideo Processor Vep-2100fVictor BlancoNessuna valutazione finora