Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
How To Prepare Fortinet NSE4 - FGT-5.6 Exam ?
Caricato da
waren kobeTitolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
How To Prepare Fortinet NSE4 - FGT-5.6 Exam ?
Caricato da
waren kobeCopyright:
Formati disponibili
How To Pass Fortinet NSE4_FGT-5.6Exam?
https://www.testschamp.com/NSE4_FGT-5.6.html
[2018] Fortinet NSE4_FGT-5.6 Dumps with Valid
NSE4_FGT-5.6 Exam Questions PDF
The Fortinet NSE4_FGT-5.6 Fortinet NSE 4 – FortiOS 5.6 Exam exam is an ultimate source for
professionals to retain their credentials dynamic. And to make your work easier, TestsChamp offers you
the valid dumps, designed and verified by the Fortinet experts. Click here for more info:
https://www.testschamp.com/NSE4_FGT-5.6.html
Fortinet NSE4_FGT-5.6 Exam Questions and Answers (PDF)
Fortinet NSE4_FGT-5.6 Exam Questions | NSE4_FGT-5.6 BrainDumps
How To Pass Fortinet NSE4_FGT-5.6Exam?
https://www.testschamp.com/NSE4_FGT-5.6.html
Version: 6.0
Question: 1
View the routing table, then identify which route will be selected when trying to reach 10.20.30.254?
Response:
A. 10.20.30.0/26 [10/0] via 172.20.168.254, port2
B. 0.0.0.0/0 [10/0] via 172.20.121.2, port1
C. 10.30.20.0/24 [10/0] via 172.20.121.2, port1
D. 10.20.30.0/24 [10/0] via 172.20.167.254, port3
Answer: D
Question: 2
Which of the following statements are true when using Web Proxy Auto-discovery Protocol (WPAD) with
the DHCP discovery method?
(Choose two.)
Response:
A. The browser sends a DHCPINFORM request to the DHCP server.
B. The browser will need to be preconfigured with the DHCP server’s IP address.
C. The DHCP server provides the PAC file for download.
D. If the DHCP method fails, browsers will try the DNS method.
Answer: AD
Question: 3
Fortinet NSE4_FGT-5.6 Exam Questions | NSE4_FGT-5.6 BrainDumps
How To Pass Fortinet NSE4_FGT-5.6Exam?
https://www.testschamp.com/NSE4_FGT-5.6.html
Which of the following statements about the FSSO collector agent timers is true?
Response:
A. The dead entry timeout interval is used to age out entries with an unverified status.
B. The workstation verify interval is used to periodically check if a workstation is still a domain member.
C. The user group cache expiry is used to age out the monitored groups.
D. The IP address change verify interval monitors the server IP address where the collector agent is
installed, and updates the collector agent configuration if it changes.
Answer: A
Question: 4
Which of the following statements about NTLM authentication are correct?
(Choose two.)
Response:
A. It is useful when users log in to DCs that are not monitored by a collector agent.
B. It takes over as the primary authentication method when configured alongside FSSO.
C. Multi-domain environments require DC agents on every domain controller.
D. NTLM-enabled web browsers are required.
Answer: AD
Question: 5
How can you configure the explicit web proxy to block HTTP packets that request a specific HTTP
method?
Response:
A. Create an explicit proxy address that matches the HTTP method and apply it to an explicit proxy policy
with the action Deny.
B. Apply a web filter profile to an explicit proxy policy that blocks the HTTP method.
C. Create a firewall service that matches the HTTP method and apply it to an explicit proxy policy with
the action Deny.
D. Create a DNS filter that matches the HTTP method and apply it to an explicit proxy policy with the
action Deny.
Answer: A
Question: 6
Firewall policies dictate whether a user or device can (or cannot) authenticate to a network. Which
statements are true regarding firewall authentication?
(Choose two.)
Fortinet NSE4_FGT-5.6 Exam Questions | NSE4_FGT-5.6 BrainDumps
How To Pass Fortinet NSE4_FGT-5.6Exam?
https://www.testschamp.com/NSE4_FGT-5.6.html
Response:
A. In order to authenticate a specific user, the firewall policy must include .., both the IP address and the
user as the source.
B. Firewall policies can be configured to authenticate certificate users.
C. Users are forced to actively authenticate when the following protocols are disabled in the firewall
policy: HTTP, HTTPS, FTP, Telnet.
D. The order of the firewall policies always determine whether a user's credentials are determined
actively or passively.
Answer: AB
Question: 7
View the exhibit. You are trying to go to http://www.clailymotion.com (Dailymotion) from the computer
behind the FortiGate. Which statement is correct regarding this application control profile?
Response:
A. Dailymotion will be blocked, as the Video/Audio category is blocked.
B. Dailymotion will be allowed, based on application overrides.
C. Dailymotion will be blocked, based on filter overrides.
D. Dailymotion will be allowed only if the action for Dailymotion is set to authenticate in application
overrides.
Fortinet NSE4_FGT-5.6 Exam Questions | NSE4_FGT-5.6 BrainDumps
How To Pass Fortinet NSE4_FGT-5.6Exam?
https://www.testschamp.com/NSE4_FGT-5.6.html
Answer: B
Question: 8
What statement describes what DNS64 does?
Response:
A. Converts DNS A record lookups to AAAA record lookups.
B. Translates the destination IPv6 address of the DNS traffic to an IPv4 address.
C. Synthesizes DNS AAAA records from A records.
D. Translates the destination IPv4 address of the DNS traffic to an IPv6 address.
Answer:
Question: 9
What information is flushed when the chunk-size value is changed in the config dlp settings?
Response:
A. The database for DLP document fingerprinting
B. The supported file types in the DLP filters
C. The archived files and messages
D. The file name patterns in the DLP filters
Answer: A
Question: 10
What step is required to configure an SSL VPN to access to an internal server using port forward mode?
Response:
A. Configure the virtual IP addresses to be assigned to the SSL VPN users.
B. Install FortiClient SSL VPN client
C. Create a SSL VPN realm reserved for clients using port forward mode.
D. Configure the client application to forward IP traffic to a Java applet proxy.
Answer: D
Question: 11
Examine the partial output from the diagnose sys session list CLI command. What does this output state?
Response:
A. proto_state=05 is the TCP state.
B. proto_state=05 is the U DP state.
Fortinet NSE4_FGT-5.6 Exam Questions | NSE4_FGT-5.6 BrainDumps
How To Pass Fortinet NSE4_FGT-5.6Exam?
https://www.testschamp.com/NSE4_FGT-5.6.html
C. proto_state=05 is the ICMP state.
D. timeout=3600 reflects the maximum length of time a session can be opened.
Answer: A
Question: 12
Which statement about firewall policy NAT is true?
Response:
A. DNAT is not supported.
B. DNAT can automatically apply to multiple firewall policies, based on DNAT rules.
C. You must configure SNAT for each firewall policy.
D. SNAT can automatically apply to multiple firewall policies, based on SNAT rules.
Answer: C
Question: 13
Which statements are true regarding firewall policy NAT using the Outgoing Interface Address with Fixed
Port disabled?
(Choose two.)
Response:
A. Source IP is translated to outgoing interface IP
B. Port address translation is not used
C. This is known as many-to-one NAT.
D. Connections are tracked using source port and source MAC address.
Answer: AC
Question: 14
Which statements are true regarding blocking botnet command and control traffic?
(Choose two.)
Response:
A. DNS lookups are checked against the Botnet Command and Control database.
B. The botnet command and control domains can be enabled on the web filter profile
C. This service requires a FortiGuard web filtering license.
D. The Botnet Command and Control database cannot be downloaded -it's only available on FortiGuard
servers.
Answer: AC
Fortinet NSE4_FGT-5.6 Exam Questions | NSE4_FGT-5.6 BrainDumps
How To Pass Fortinet NSE4_FGT-5.6Exam?
https://www.testschamp.com/NSE4_FGT-5.6.html
Question: 15
What methods can be used to deliver the token code to a user who is configured to use two-factor
authentication?
(Choose three.)
Response:
A. SMS text message
B. Instant message app
C. Voicemail message
D. Email
E. FortiToken
Answer: ADE
Fortinet NSE4_FGT-5.6 Exam Questions | NSE4_FGT-5.6 BrainDumps
How To Pass Fortinet NSE4_FGT-5.6Exam?
https://www.testschamp.com/NSE4_FGT-5.6.html
Thank You For Trying NSE4_FGT-5.6 PDF Demo
To try our NSE4_FGT-5.6 practice exam software visit link below
http://www.testschamp.com/NSE4_FGT-5.6.html
Start Your NSE4_FGT-5.6
Preparation
Use Coupon “20OFF” for extra 20% discount on the purchase of
Practice Test Software. Test your NSE4_FGT-5.6 preparation with
actual exam questions.
Fortinet NSE4_FGT-5.6 Exam Questions | NSE4_FGT-5.6 BrainDumps
Potrebbero piacerti anche
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (587)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (890)
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (399)
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (73)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2219)
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (344)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (265)
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (119)
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- Movement and Position: Question Paper 4Documento14 pagineMovement and Position: Question Paper 4SlaheddineNessuna valutazione finora
- Rubber Chemical Resistance Chart V001MAR17Documento27 pagineRubber Chemical Resistance Chart V001MAR17Deepak patilNessuna valutazione finora
- FS2004 - The Aircraft - CFG FileDocumento5 pagineFS2004 - The Aircraft - CFG FiletumbNessuna valutazione finora
- HCW22 PDFDocumento4 pagineHCW22 PDFJerryPNessuna valutazione finora
- Google Dorks For PentestingDocumento11 pagineGoogle Dorks For PentestingClara Elizabeth Ochoa VicenteNessuna valutazione finora
- Katie Tiller ResumeDocumento4 pagineKatie Tiller Resumeapi-439032471Nessuna valutazione finora
- Lecture Ready 01 With Keys and TapescriptsDocumento157 pagineLecture Ready 01 With Keys and TapescriptsBảo Châu VươngNessuna valutazione finora
- GMWIN SoftwareDocumento1 paginaGMWIN SoftwareĐào Đình NamNessuna valutazione finora
- Sentinel 2 Products Specification DocumentDocumento510 pagineSentinel 2 Products Specification DocumentSherly BhengeNessuna valutazione finora
- 50 Years of Teaching PianoDocumento122 pagine50 Years of Teaching PianoMyklan100% (35)
- John Hay People's Alternative Coalition Vs Lim - 119775 - October 24, 2003 - JDocumento12 pagineJohn Hay People's Alternative Coalition Vs Lim - 119775 - October 24, 2003 - JFrances Ann TevesNessuna valutazione finora
- Catalogoclevite PDFDocumento6 pagineCatalogoclevite PDFDomingo YañezNessuna valutazione finora
- RACI Matrix: Phase 1 - Initiaton/Set UpDocumento3 pagineRACI Matrix: Phase 1 - Initiaton/Set UpHarshpreet BhatiaNessuna valutazione finora
- Intro To Gas DynamicsDocumento8 pagineIntro To Gas DynamicsMSK65Nessuna valutazione finora
- Archlinux 之 之 之 之 Lmap 攻 略 ( 攻 略 ( 攻 略 ( 攻 略 ( 1 、 环 境 准 备 ) 、 环 境 准 备 ) 、 环 境 准 备 ) 、 环 境 准 备 )Documento16 pagineArchlinux 之 之 之 之 Lmap 攻 略 ( 攻 略 ( 攻 略 ( 攻 略 ( 1 、 环 境 准 备 ) 、 环 境 准 备 ) 、 环 境 准 备 ) 、 环 境 准 备 )Goh Ka WeeNessuna valutazione finora
- Reflection Homophone 2Documento3 pagineReflection Homophone 2api-356065858Nessuna valutazione finora
- ABP - IO Implementing - Domain - Driven - DesignDocumento109 pagineABP - IO Implementing - Domain - Driven - DesignddoruNessuna valutazione finora
- Panel Data Econometrics: Manuel ArellanoDocumento5 paginePanel Data Econometrics: Manuel Arellanoeliasem2014Nessuna valutazione finora
- "Behind The Times: A Look at America's Favorite Crossword," by Helene HovanecDocumento5 pagine"Behind The Times: A Look at America's Favorite Crossword," by Helene HovanecpspuzzlesNessuna valutazione finora
- GROSS DOMESTIC PRODUCT STATISTICS (Report) - Powerpoint PresentationDocumento37 pagineGROSS DOMESTIC PRODUCT STATISTICS (Report) - Powerpoint PresentationCyryhl GutlayNessuna valutazione finora
- Acne Treatment Strategies and TherapiesDocumento32 pagineAcne Treatment Strategies and TherapiesdokterasadNessuna valutazione finora
- Math5 Q4 Mod10 DescribingAndComparingPropertiesOfRegularAndIrregularPolygons v1Documento19 pagineMath5 Q4 Mod10 DescribingAndComparingPropertiesOfRegularAndIrregularPolygons v1ronaldNessuna valutazione finora
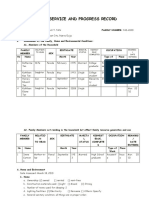
- Family Service and Progress Record: Daughter SeptemberDocumento29 pagineFamily Service and Progress Record: Daughter SeptemberKathleen Kae Carmona TanNessuna valutazione finora
- Mazda Fn4A-El 4 Speed Ford 4F27E 4 Speed Fnr5 5 SpeedDocumento5 pagineMazda Fn4A-El 4 Speed Ford 4F27E 4 Speed Fnr5 5 SpeedAnderson LodiNessuna valutazione finora
- Oracle Learning ManagementDocumento168 pagineOracle Learning ManagementAbhishek Singh TomarNessuna valutazione finora
- 5511Documento29 pagine5511Ckaal74Nessuna valutazione finora
- Malware Reverse Engineering Part 1 Static AnalysisDocumento27 pagineMalware Reverse Engineering Part 1 Static AnalysisBik AshNessuna valutazione finora
- Unit 1 TQM NotesDocumento26 pagineUnit 1 TQM NotesHarishNessuna valutazione finora
- Axe Case Study - Call Me NowDocumento6 pagineAxe Case Study - Call Me NowvirgoashishNessuna valutazione finora
- DECA IMP GuidelinesDocumento6 pagineDECA IMP GuidelinesVuNguyen313Nessuna valutazione finora