Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
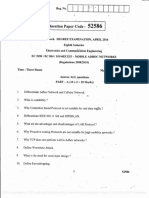
Answer All The Questions Networking: (Subject With Code)
Caricato da
gunaTitolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Answer All The Questions Networking: (Subject With Code)
Caricato da
gunaCopyright:
Formati disponibili
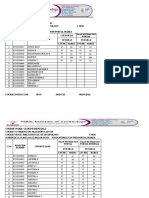
MRK Institute of Technology MRK Institute of Technology
(Approved by AICTE & Affiliated to Anna University) (Approved by AICTE & Affiliated to Anna University)
Kattumannarkoil – 608301. Kattumannarkoil – 608301.
INTERNAL ASSESSMENT EXAMINATION - I INTERNAL ASSESSMENT EXAMINATION – I
(Subject with code) (Subject with code)
Year : Sem : Year : Sem :
Duration : 3 1/2 Hrs Marks : 100 Duration : 3 1/2 Hrs Marks : 100
Department : Date : Department : Date :
PART - A (20x2 =40)
PART - A (20x2 =40) ANSWER ALL THE QUESTIONS
ANSWER ALL THE QUESTIONS 1. List out the differences between Mobile Computing and Wireless
1. List out the differences between Mobile Computing and Wireless Networking
Networking 2. List some random assignment scheme
2. List some random assignment scheme 3. List the advantages of mobile computing
3. List the advantages of mobile computing 4. Explain hidden and exposed terminal problems in infrastructure
4. Explain hidden and exposed terminal problems in infrastructure less network
less network 5. What is random assignment scheme in the MAC protocol
5. What is random assignment scheme in the MAC protocol 6. List the application of mobile computing
6. List the application of mobile computing 7. What is connection less and connection oriented packet switching
7. What is connection less and connection oriented packet switching techniques
techniques 8. Difference between FDMA and TDMA
8. Difference between FDMA and TDMA 9. Prove that Barker code has good auto correlation
9. Prove that Barker code has good auto correlation 10. Describe about MAC layer in DECT architecture
10. Describe about MAC layer in DECT architecture 11. List the modifications proposed in single hop and multi hop
11. List the modifications proposed in single hop and multi hop wireless networks
wireless networks 12. What is the purpose of DHCP? In what way DHCP can be used
12. What is the purpose of DHCP? In what way DHCP can be used for mobility
for mobility 13. Mention the different entities in a mobile IP
13. Mention the different entities in a mobile IP 14. What led to the development of indirect TCP
14. What led to the development of indirect TCP 15. What is the reaction of standard TPC in case of packet loss
15. What is the reaction of standard TPC in case of packet loss 16. How does a MN identify that it has moved
16. How does a MN identify that it has moved 17. State any four features of IPV618 What led to the development
17. State any four features of IPV618 What led to the development of indirect TCP?
of indirect TCP? 18. List the modifications proposed in single hop and multi hop
18. List the modifications proposed in single hop and multi hop wireless networks
wireless networks 19. Illustrate the use of BOOTP protocol
19. Illustrate the use of BOOTP protocol 20. What is COA? How it is assigned
20. What is COA? How it is assigned
PART - B (5X12 = 60) PART - B (5X12 = 60)
ANSWER ALL THE QUESTIONS ANSWER ALL THE QUESTIONS
21. (a) (i)Explain hidden and exposed terminal problem in infrastructure 21. (a) (i)Explain hidden and exposed terminal problem in infrastructure
less network (6) less network (6)
(ii) Describe architecture of mobile computing (6) (ii) Describe architecture of mobile computing (6)
(Or) (Or)
21. (b) (i) Explain the wireless MAC issues in detail (6) 21. (b) (i) Explain the wireless MAC issues in detail (6)
(ii) Explain fixed assignment scheme with a neat diagram (6) (ii) Explain fixed assignment scheme with a neat diagram (6)
22. (a) (i) Differentiate between FDMA, TDMA and CDMA (6) 22. (a) (i) Differentiate between FDMA, TDMA and CDMA (6)
(ii) Explain the characteristics of mobile computing (6) (ii) Explain the characteristics of mobile computing (6)
(Or) (Or)
22. (b) (i) Write short note on ALOHA. Write a short note on slotted 22. (b) (i) Write short note on ALOHA. Write a short note on slotted
ALOHA scheme (6) ALOHA scheme (6)
(ii) Explain the advantages of CDMA explain the Disadvantages (ii) Explain the advantages of CDMA explain the Disadvantages
of CDMA (6) of CDMA (6)
23. (a) (i) Explain in detail about Multiple Access Collision Avoidance 23. (a) (i) Explain in detail about Multiple Access Collision Avoidance
(MACA) (6) (MACA) (6)
(ii) Briefly explain about code division multiple accesses with (ii) Briefly explain about code division multiple accesses with
neat sketches (6) neat sketches (6)
(Or) (Or)
23.(b) (i) what are th fixed assignment schemes of MAC Protocol? 23.(b) (i) what are th fixed assignment schemes of MAC Protocol?
Explain their mechanism in detail. (6) Explain their mechanism in detail. (6)
(ii) Explain the various taxonomy of Mac protocols in Detail (ii) Explain the various taxonomy of Mac protocols in Detail
24. (a) (i) Explain about the key mechanism in mobile IP (6) 24. (a) (i) Explain about the key mechanism in mobile IP (6)
(ii) With a neat diagram explain how packet delivery to and (ii) With a neat diagram explain how packet delivery to and
from a mobile node is transferred in Mobile IP (6) from a mobile node is transferred in Mobile IP (6)
(Or) (Or)
24. (b) (i) Give the comparison of various TCP advantages and 24. (b) (i) Give the comparison of various TCP advantages and
disadvantages in wireless networking (6) disadvantages in wireless networking (6)
(ii) Explain in detail about virtualization structure (6) (ii) Explain in detail about virtualization structure (6)
25. (a) (i) Discuss the UDP datagram communication (6) 25. (a) (i) Discuss the UDP datagram communication (6)
(ii) What is encapsulation? Explain in detail the various (ii) What is encapsulation? Explain in detail the various
encapsulation techniques in mobile IP (6) encapsulation techniques in mobile IP (6)
(Or) (Or)
25. (b) (i) Explain IP in IP, minimal IP and GRE encapsulation Methods 25. (b) (i) Explain IP in IP, minimal IP and GRE encapsulation Methods
(12) (12)
Potrebbero piacerti anche
- SOP-20-CP Smart Operation Panel User GuideDocumento2 pagineSOP-20-CP Smart Operation Panel User GuideTrinnatee ChotimongkolNessuna valutazione finora
- SWT FOH - SchlumbergerDocumento519 pagineSWT FOH - SchlumbergerMarwenNessuna valutazione finora
- Digital Forensics and Artificial Intelligence A StudyDocumento4 pagineDigital Forensics and Artificial Intelligence A StudyInternational Journal of Innovative Science and Research TechnologyNessuna valutazione finora
- WSN Question Bank 2017-2018Documento6 pagineWSN Question Bank 2017-2018Kommisetty Murthyraju100% (1)
- Question Bank For Mobile Computing Regulation 2013Documento9 pagineQuestion Bank For Mobile Computing Regulation 2013PRIYA RAJI100% (1)
- Annapoorana Engineering College, SalemDocumento1 paginaAnnapoorana Engineering College, SalemdeepaNessuna valutazione finora
- Assessment 2 Ques PaperDocumento4 pagineAssessment 2 Ques PaperKaviya TamilNessuna valutazione finora
- IT6601-Mobile Computing Question Bank: Unit I Part ADocumento7 pagineIT6601-Mobile Computing Question Bank: Unit I Part ANaveenTummidiNessuna valutazione finora
- Mobile Adhoc Networks QPDocumento2 pagineMobile Adhoc Networks QPDr.chitra ECENessuna valutazione finora
- Stucor Qp-Ec8702Documento5 pagineStucor Qp-Ec8702diamond puppyNessuna valutazione finora
- Now and Get: Best VTU Student Companion App You Can GetDocumento16 pagineNow and Get: Best VTU Student Companion App You Can GetMOHAMMED IYANUDDINNessuna valutazione finora
- AWN Viva Question BankDocumento3 pagineAWN Viva Question BankPiyushPurohitNessuna valutazione finora
- UNIT-1 SNO Questions Levels 1 L1Documento7 pagineUNIT-1 SNO Questions Levels 1 L1ijklmnopNessuna valutazione finora
- Internal Assesment Test I WsanDocumento1 paginaInternal Assesment Test I WsanDR.SENTHILKUMAR MNessuna valutazione finora
- IT6601 MC AU QP Reg 2013Documento11 pagineIT6601 MC AU QP Reg 2013bhuvangatesNessuna valutazione finora
- Anna University QP Iot 2022 mc4302Documento2 pagineAnna University QP Iot 2022 mc4302Kanimozhi LNessuna valutazione finora
- Ad Hoc QuestionsDocumento13 pagineAd Hoc QuestionsMadhavan SamNessuna valutazione finora
- Question Paper Code:: (10×2 20 Marks)Documento2 pagineQuestion Paper Code:: (10×2 20 Marks)Csc MalliakaraiNessuna valutazione finora
- Mobile ComputingDocumento5 pagineMobile Computingmichael.ferraris100% (1)
- Switching Theory and Logic Design - June-2015Documento55 pagineSwitching Theory and Logic Design - June-2015Rama HarithaNessuna valutazione finora
- Question Paper Code:: Reg. No.Documento2 pagineQuestion Paper Code:: Reg. No.Vijayarasu ThirunavukkarasuNessuna valutazione finora
- Question BankDocumento12 pagineQuestion BankMahu DNessuna valutazione finora
- Computer Network Technology Prelim ExaminationDocumento2 pagineComputer Network Technology Prelim ExaminationOmar MehrajNessuna valutazione finora
- @vtucode - in - CN QUESTION BANK 2021 SCHEMEDocumento7 pagine@vtucode - in - CN QUESTION BANK 2021 SCHEMEvinaykumarms343Nessuna valutazione finora
- 4507 CPLD and FPGA ArchitecturesDocumento1 pagina4507 CPLD and FPGA ArchitecturesshobiNessuna valutazione finora
- Mobile Computing Model Exam Question PapersDocumento3 pagineMobile Computing Model Exam Question PapersSamy KmNessuna valutazione finora
- Question Paper of Computer NetworkDocumento1 paginaQuestion Paper of Computer NetworkBhesh Chaudhary100% (1)
- Computer NetworksDocumento2 pagineComputer NetworksManoj BalaNessuna valutazione finora
- 15A04704 Data Communications & NetworkingDocumento2 pagine15A04704 Data Communications & NetworkingKumar ChandrasekharNessuna valutazione finora
- Erts - Model 1Documento3 pagineErts - Model 1Ece DeptNessuna valutazione finora
- Question BankDocumento9 pagineQuestion BankK R OFFSET PRINTERSNessuna valutazione finora
- Name: Sabia Tasleem ENROLLMENT NO: 166756687 Programme Code: Mca 3 SEM Course Code: Mcs042 Data Communication and Computer NetworkDocumento51 pagineName: Sabia Tasleem ENROLLMENT NO: 166756687 Programme Code: Mca 3 SEM Course Code: Mcs042 Data Communication and Computer NetworkSunil SharmaNessuna valutazione finora
- EC6802-wn - QB - With Out BloomsDocumento12 pagineEC6802-wn - QB - With Out BloomsBabiyola AntonyNessuna valutazione finora
- 5 Years Anna University Question PaperDocumento13 pagine5 Years Anna University Question PaperG. SIVARANJANI Associate ProfessorNessuna valutazione finora
- WSN June 2019 QPDocumento1 paginaWSN June 2019 QPtempNessuna valutazione finora
- Ec7001 Adhoc and Wireless Sensor NetworksDocumento2 pagineEc7001 Adhoc and Wireless Sensor NetworksninbrocknitinNessuna valutazione finora
- 2022 Summer Question Paper (Msbte Study Resources)Documento3 pagine2022 Summer Question Paper (Msbte Study Resources)sonavanepraniteeNessuna valutazione finora
- VU C7 T P Networking 2020Documento2 pagineVU C7 T P Networking 2020enabarunmondal2004Nessuna valutazione finora
- WIRELESS+AND+MOBILE+NETWORKING Seme2 2006Documento2 pagineWIRELESS+AND+MOBILE+NETWORKING Seme2 2006api-26171521Nessuna valutazione finora
- Model Questionpaper - Paper2Documento3 pagineModel Questionpaper - Paper2Shubhra DixitNessuna valutazione finora
- III b.tech-II Sem Question BankDocumento35 pagineIII b.tech-II Sem Question BankMukesh BathreNessuna valutazione finora
- Computer Networks ModelDocumento2 pagineComputer Networks ModelMahendran MaheNessuna valutazione finora
- Electronics and Communication Engineering: Question Paper Code: X10366Documento4 pagineElectronics and Communication Engineering: Question Paper Code: X10366krithikgokul selvam100% (1)
- IoT IMP QUESTIONSDocumento2 pagineIoT IMP QUESTIONSSyed AhmedNessuna valutazione finora
- Es Model ExamDocumento3 pagineEs Model ExamAarun ArasanNessuna valutazione finora
- Compu Net2Documento3 pagineCompu Net2XXXNessuna valutazione finora
- Vlsi QP 21,22Documento11 pagineVlsi QP 21,22Arunitha ArulnathanNessuna valutazione finora
- CS1302 - Computer NetworksDocumento5 pagineCS1302 - Computer Networkslm_zakaria4420Nessuna valutazione finora
- Adhoc Wireless and Sensor Networks: M. Tech II Semester Supplementary Examinations, February - 2014Documento26 pagineAdhoc Wireless and Sensor Networks: M. Tech II Semester Supplementary Examinations, February - 2014Sreekanth PagadapalliNessuna valutazione finora
- Answer All Questions PART A - (5 2 10)Documento2 pagineAnswer All Questions PART A - (5 2 10)Peer MohamedNessuna valutazione finora
- CS8601 Mobile ComputigDocumento3 pagineCS8601 Mobile ComputigAparna durairajNessuna valutazione finora
- Integrated Dual Degree (B.Tech.+M.Tech.) Examination Electronics & Communication EngineeringDocumento2 pagineIntegrated Dual Degree (B.Tech.+M.Tech.) Examination Electronics & Communication Engineeringnaveen dandemNessuna valutazione finora
- 19ECSC302 851 19ECSC302 881 23KlE504Documento2 pagine19ECSC302 851 19ECSC302 881 23KlE504hammad choudharyNessuna valutazione finora
- V.M.K.V Engineering College Vinayaka Missions University Department of Information Technology IV YEAR (BATCH - 2006-2010) Mobile ComputingDocumento5 pagineV.M.K.V Engineering College Vinayaka Missions University Department of Information Technology IV YEAR (BATCH - 2006-2010) Mobile ComputingpocketoxyNessuna valutazione finora
- Ec6601 QB RejinpaulDocumento5 pagineEc6601 QB RejinpauljohnarulrajNessuna valutazione finora
- Cn-Question BankDocumento3 pagineCn-Question BankA Raghava Chowdary maddipatiNessuna valutazione finora
- Computer Networks (BEG374CO)Documento1 paginaComputer Networks (BEG374CO)Subas ShresthaNessuna valutazione finora
- MPCDocumento5 pagineMPCStella SarkunamNessuna valutazione finora
- Vlsi DesignDocumento2 pagineVlsi DesignXXXNessuna valutazione finora
- Allama Iqbal Open University, Islamabad Warning: (Department of Computer Science)Documento3 pagineAllama Iqbal Open University, Islamabad Warning: (Department of Computer Science)Fawad Ahmad JattNessuna valutazione finora
- CN Chapterwise Question Bank SH-2022Documento3 pagineCN Chapterwise Question Bank SH-2022Pushpa RazNessuna valutazione finora
- Fundamentals of IoT SET 1Documento1 paginaFundamentals of IoT SET 1Manjot KaurNessuna valutazione finora
- CloudDocumento5 pagineCloudgunaNessuna valutazione finora
- The Mechatronics Design Lab Course at The University Of: CalgaryDocumento24 pagineThe Mechatronics Design Lab Course at The University Of: CalgarygunaNessuna valutazione finora
- DE P Art M EN T of Computer Science and Engineering: Cs8711 Cloud Computing LaboratoryDocumento9 pagineDE P Art M EN T of Computer Science and Engineering: Cs8711 Cloud Computing LaboratorygunaNessuna valutazione finora
- CS3362 DSDocumento2 pagineCS3362 DSgunaNessuna valutazione finora
- Department of Computer Science Engineering: Internal Assessment - IDocumento2 pagineDepartment of Computer Science Engineering: Internal Assessment - IgunaNessuna valutazione finora
- MRK Institute of Technology MRKDocumento2 pagineMRK Institute of Technology MRKgunaNessuna valutazione finora
- 01.B.E. CSE Final PDFDocumento125 pagine01.B.E. CSE Final PDFANNessuna valutazione finora
- MRK Institute of Technology MRKDocumento2 pagineMRK Institute of Technology MRKgunaNessuna valutazione finora
- OOAD Lab - 1,3Documento21 pagineOOAD Lab - 1,3gunaNessuna valutazione finora
- Lab Manual: Department of Computer EngineeringDocumento66 pagineLab Manual: Department of Computer EngineeringgunaNessuna valutazione finora
- HCI IA QuesDocumento4 pagineHCI IA QuesgunaNessuna valutazione finora
- WWW - Manaresults.Co - In: Set No. 1Documento5 pagineWWW - Manaresults.Co - In: Set No. 1gunaNessuna valutazione finora
- MRK Institute of Technology: Kattumannarkoil - 608301. Kattumannarkoil - 608301Documento2 pagineMRK Institute of Technology: Kattumannarkoil - 608301. Kattumannarkoil - 608301gunaNessuna valutazione finora
- CS 6008 HciDocumento7 pagineCS 6008 HcigunaNessuna valutazione finora
- QuestionsDocumento4 pagineQuestionsgunaNessuna valutazione finora
- CS6008 Human Computer InteractionDocumento42 pagineCS6008 Human Computer InteractiongunaNessuna valutazione finora
- Final Os LabDocumento103 pagineFinal Os LabgunaNessuna valutazione finora
- Os LabDocumento26 pagineOs LabgunaNessuna valutazione finora
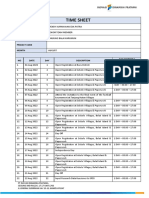
- Timesheet - August 2022 - An Wendy KurniawanDocumento2 pagineTimesheet - August 2022 - An Wendy KurniawanWendy KurniawanNessuna valutazione finora
- D Murli - Creating Multilingual Website (English - Hindi - Punjabi) Using ASPDocumento6 pagineD Murli - Creating Multilingual Website (English - Hindi - Punjabi) Using ASPmrpraveenmNessuna valutazione finora
- GI A1PLUS U5 Test StandardDocumento5 pagineGI A1PLUS U5 Test Standardguzal.zakhidova811Nessuna valutazione finora
- COCU 4 Electroni 1711214Documento6 pagineCOCU 4 Electroni 1711214Atie ZakariaNessuna valutazione finora
- A Secure and Managed Cloud Storage System Using Encryption With Machine Learning ApproachDocumento15 pagineA Secure and Managed Cloud Storage System Using Encryption With Machine Learning ApproachGlobal Research and Development ServicesNessuna valutazione finora
- GNT Series-Product BrochureDocumento36 pagineGNT Series-Product BrochureOo Kenx OoNessuna valutazione finora
- Iwc DumpDocumento612 pagineIwc Dumpstefan ungureanNessuna valutazione finora
- Assignment PDFDocumento7 pagineAssignment PDFhemacrcNessuna valutazione finora
- Representing Knowledge UsingDocumento22 pagineRepresenting Knowledge UsingAdityaNessuna valutazione finora
- Information Sheet No. 1.1 Occupational Health & Safety Policies and ProceduresDocumento3 pagineInformation Sheet No. 1.1 Occupational Health & Safety Policies and ProceduresjezreelcsNessuna valutazione finora
- PLSQL ResumeDocumento4 paginePLSQL ResumeBindu BhargaviNessuna valutazione finora
- Rudrabhisheka-Stotram Telugu PDF File2009Documento3 pagineRudrabhisheka-Stotram Telugu PDF File2009Sreenivas GNessuna valutazione finora
- Lab #3Documento13 pagineLab #3Trần Mỹ LinhNessuna valutazione finora
- Create A Variety of Assessments Using Pathways 2E Examview ContentDocumento3 pagineCreate A Variety of Assessments Using Pathways 2E Examview ContentMaha Al AmadNessuna valutazione finora
- My Python CodesDocumento4 pagineMy Python CodesEsmael UtaNessuna valutazione finora
- .5 Computer Teaching StrategiesDocumento40 pagine.5 Computer Teaching StrategiesELIZABETH GRACE AMADORNessuna valutazione finora
- G8 Final Term 2 Revision Sheet (21-22)Documento10 pagineG8 Final Term 2 Revision Sheet (21-22)Hala HassanNessuna valutazione finora
- RSM QuadraticsDocumento11 pagineRSM QuadraticsCatherine RozeNessuna valutazione finora
- (Lecture Notes in Applied and Computational Mechanics 19) Paul B. MacCready (Auth.), Rose McCallen PH.D., Fred Browand PH.D., Dr. James Ross Ph.D. (Eds.) - The Aerodynamics of Heavy Vehicles - TrucksDocumento534 pagine(Lecture Notes in Applied and Computational Mechanics 19) Paul B. MacCready (Auth.), Rose McCallen PH.D., Fred Browand PH.D., Dr. James Ross Ph.D. (Eds.) - The Aerodynamics of Heavy Vehicles - TrucksVương HoàngNessuna valutazione finora
- Chinas HisenseDocumento2 pagineChinas HisenseNhi ThanhNessuna valutazione finora
- Introduction To Programming TutorialsDocumento152 pagineIntroduction To Programming TutorialsWangechiNessuna valutazione finora
- TECHNOSHOCKERSDocumento5 pagineTECHNOSHOCKERScarlosNessuna valutazione finora
- Kelas 7 SMP 7402 Inggris Bab 2 IntroducingDocumento4 pagineKelas 7 SMP 7402 Inggris Bab 2 IntroducingCorry IntanNessuna valutazione finora
- Barnagay Inventory Form 1Documento2 pagineBarnagay Inventory Form 1Barangay San Jose Csfp100% (2)
- Condair Se Technical ManualDocumento129 pagineCondair Se Technical ManualLOZADA SALINAS CARLOS ALBERTONessuna valutazione finora
- UiPath String ManipulationDocumento3 pagineUiPath String ManipulationGovindan M SundaramNessuna valutazione finora
- Guide Lacls Colombia Electronic InvoiceDocumento61 pagineGuide Lacls Colombia Electronic InvoiceGuillermo José Jiménez EscamillaNessuna valutazione finora