Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Integration in Access Control Systems: Putting Together The Pieces of An Integrated Access Control System
Caricato da
Minh NhậtTitolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Integration in Access Control Systems: Putting Together The Pieces of An Integrated Access Control System
Caricato da
Minh NhậtCopyright:
Formati disponibili
Integration in
Access Control Systems
Putting Together the Pieces of an Integrated
Access Control System
An RS2 Technologies White Paper
400 Fisher Street, Suite G
Munster, IN 46321
www.rs2tech.com
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
Integration in
Access Control Systems
Putting Together the Pieces of an Integrated
Access Control System
Table of Contents
Executive Summary 3
What is Integration? 3
Perspectives on Access Control Integration 4
How Integration Works 6
Integration with CCTV 6
Integration with Digital & Network Video Recording 7
Integration with Intercom Systems 8
Integration with Intrusion Detection 9
Integration with Wireless/IP and PoE Locksets 10
Completely Integrated Systems 11
Integration with Software and Other Systems 12
The Importance of Partnering in Integration 13
The Role of the Systems Integrator 13
The Future of Integration: Convergence 14
Questions to Ask Vendors and Systems Integrators 15
Conclusions 16
About RS2 Technologies 17
2009, RS2 Technologies, LLC. All rights reserved. RS2, RS2 Technologies, Access It!, and the RS2 logo are all
trademarks of RS2 Technologies, LLC. Microsoft and SQL are trademarks of Microsoft Corporation. All other names
and trademarks are the property of their respective owners. Information contained within this document is intended
for general educational purposes and is subject to change without notice. It is considered to be accurate at the
time of publication, but RS2 Technologies, LLC assumes no liability and makes no warranties, express or implied,
with respect to the accuracy of the information or its use for any purpose.
2 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
Executive Summary
In the first two papers of the RS2 White Paper series1, we examined the
subjects of Total Cost of Ownership (TCO) and Open Architecture as they
relate to access control systems. We concluded that an important element
of TCO was the use of Open Architecture and that, in turn, Open Architec-
ture was the cornerstone of integration. We stated that this integration
allowed end users to build completely integrated security systems incor-
porating access control, badging, CCTV, digital or network video recording
and analytics, intercom, intrusion detection, wireless/IP locksets and other
functions such as visitor management.
This White Paper endeavors to provide a useful definition of integration
(as it pertains to access control systems), provides several examples
(including diagrams) of discrete integrated systems, and discusses what
the next step(s) might be along the road to even higher levels of integration.
It also lists some of the questions that end users should ask the vendors
of access control systems and the systems integrators who install these
systems. Readers are then encouraged to apply these conclusions to their
own evaluations of access control systems.
System integration is also What is Integration?
about value-adding (to the Not too many years ago, when defining a word, writers
system) capabilities that would quote the American Heritage or Merriam-Webster
are possible because of dictionaries. In keeping with the times, we find Wikipedias
interactions between sub- definition of system integration to be very useful for the
systems purposes of this White Paper:
System integration is the bringing together of the component sub-systems
into one system and ensuring that the sub-systems function together as a
system.
A system is an aggregation of sub-systems cooperating so that the system
is able to deliver the over-arching functionality. System integration involves
integrating existing (often disparate) sub-systems.
System integration is also about value-adding (to the system) capabilities
that are possible because of interactions between sub-systems.
A little long, but right on the mark for our purposes. Please note that we
are using the term system integration almost interchangeably with
1
Copies of the RS2 White Papers Total Cost of Ownership of Access Control Systems and Open
Architecture in Access Control Systems can be downloaded by logging on to the RS2 web site
(www.rs2tech.com) or by calling 877.682.3532 and requesting a copy.
3 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
integration. In the world of access control, the distinction between
the two terms tends to blur, as what is being integrated is just that
systems/sub-systems.
Perhaps equally as important as defining what integration is, is defining
what it is not. Integration is occasionally used interchangeably with con-
vergence. In his article Convergence 2.0, Bill Zalud, editor of Security
magazine, says For some, convergence is a fancy-pants term for security
systems integration in which various security subsystems are connected
beyond simple interfacing. In a general way, however, most security lead-
ers see convergence as the bringing together of physical and logical or
computer security in ways that primarily emphasize access controls and
identity management. 2 We will deal with convergence in greater detail
later. See The Future of Integration: Convergence on page 14.
Perspectives on Access Control Integration
Integration between access control and other security systems is so preva-
lent today that its almost hard to remember that, as recently as a few years
ago, that was not the case. However, one need only look at security trade
publications from that period to find stories like this:
A security manager for a large corporation comes in from a long Memorial Day
weekend and reviews the security logs for the time he was away. He sees
a line of type in his access control log saying that someone was attempting
an unauthorized entrance to a highly secure area of the facility on Memo-
rial Day itself, when no regular employees were present.
Today, its difficult to find
He reviews his access control logs to see whose card was
a security sub-system
being used to try to enter. Unfortunately, he has no way of
that doesnt integrate with
confirming whether that person actually was attempting entry
access control.
or someone else was using the persons card because the
corporations video system is not integrated with its access control system. 3
Seems pretty primitive by todays standards, doesnt it? In fact, video was
one of the very first integrations (with access control) to occur. Today, its
difficult to find a security sub-system that doesnt integrate with access
control. While video is still the obvious hot spot, access control also now
routinely integrates with intercom, intrusion detection, wireless locks, visitor
management, and other systems.
2
Convergence 2.0, Security Magazine, February 2009, Bill Zalud. 2009 Security Magazine.
3
Trends in Video Integration: The Need for Open Book Design, SDM Magazine, 4/3/06, Russ Gager.
2006 SDM Magazine.
4 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
Who and what drove the change? And why did it occur so quickly? The who
are, literally, all the stakeholders: suppliers, integrators, and end users. The
why essentially boils down to economics on the part of all three groups.
In a series of articles in 2006, SDM magazine examined integration from
all three perspectives. There were certainly differences between the three
groups. Suppliers were looking for a competitive advantage; integrators were
looking for products that would improve their profitability; end users were look-
ing for single-platform systems that were easy and cost-effective to operate:
Suppliers:
Integration is not a buzz word anymore it is already here. People are trying
to understand it better. As manufacturers are getting to understand the impor-
tance from a market development standpoint, the end users are beginning to
realize the importance of getting as much as possible out of the investment. 4
Integrators:
What integrators also look for is manufacturers that typically enable the
integrating company to make money, and how you do that is limit distribution
so not everybody sells it, and you dont sell directly to end users. . .Manufac-
turers who sell directly to end users are avoided by most integrators. 4
(Note: From its founding in 1998, RS2 Technologies has never sold to end users.)
End Users:
For us here, the bottom line is dollars. 4
Better integration would economize on the biggest expense of installing
security equipment not the equipment itself, but running the wire for it. 4
And, in a more recent (June 2008) article entitled Feature Sets that $ell, the
Big 3 features are identified as integration, open platform, and ease of use:
Integration with video, or any other system, is a boon to customers in todays
economy. The way things have matured, CCTV, access, and alarm man-
agement were traditionally separate systems, says Matt Barnette . . . AMAG
Technology. Today, we are finding more customers trying to do more with
less. They need systems that play into that. 5
4
Integration: The Suppliers Perspective, SDM Magazine, 5/1//06, Russ Gager. 2006 SDM.
Integration: The Integrators Perspective, SDM Magazine, 6/1//06, Russ Gager. 2006 SDM.
Integration: The En d Users Perspective, SDM Magazine, 7/1//06, Russ Gager. 2006 SDM.
5
Feature Sets That Sell, SDM Magazine, June 2008, Karyn Hodgson. 2008 SDM Magazine.
5 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
How Integration Works
I know you. You know me.
- from Come Together, the Beatles, 1969
Its a pretty safe bet that, when John Lennon wrote Come Together in
1969, he wasnt thinking about security system integration. Nevertheless,
those 6 words are a succinct description of what happens in an integrated
security system. Literally, the individual sub-systems recognize and talk
to each other through the access control system, allowing them to come
together as an integrated system. Many integrated systems started out
as one or two sub-systems that were integrated with the access control
system. In the RS2 experience, video and CCTV were among the initial
physical security sub-systems to be integrated with access control, followed
quickly by intercom and intrusion detection. Most recently, wireless/IP lock-
sets are being integrated with access control.
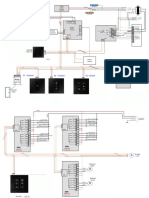
How do all the pieces go together? The following series of diagrams shows
how various sub-systems are integrated with RS2s Access It! access con-
trol systems. As shown in Figures 1-6, each system utilizes the Local Area
Network (TCP/IP) to configure any number of components.
Integration with Closed Circuit Television (CCTV)
In the case of CCTV, the Access It! system connects through the LAN
either directly to IP cameras or through the access control server and a
CCTV matrix switch to an unlimited number of dome cameras. Using inter-
active graphical display maps, users can direct cameras to preset positions
based on alarms or events, control cameras with full PTZ (pan-tilt-zoom)
capability, view live events on demand, and perform other functions.
An Integrated Access Control & CCTV System
Access Access It! workstation with
CCTV Matrix Switch CCTV integration option
Control Server
Dome
Camera Local Area
Network
(TCP/IP)
Access It! workstation with
One or more IP CCTV integration option
cameras connected
to the LAN Access It! workstation with
CCTV integration option
Access It! workstation with
CCTV integration option
Figure 1: This diagram shows the network setup for an RS2 Access Control System that has
been integrated with a CCTV system.
6 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
Integration with Digital and Network Video Recorders
With digital and network video recorder systems (DVRs and NVRs), users
can perform all of the same functions as with the CCTV system (i.e., PTZ
camera control, live camera view on demand, etc.), and have the added
capabilities of video playback on demand (or tied to alarm/event time and
data), hyperlinking to video from access control history reports, simple GUI
(graphical user interface) for faster incident investigations, and many other
functions. Because of the popularity of video analytics, RS2 integrates with
more than a dozen DVR/NVR manufacturers, and incorporates a Univer-
sal DVR/NVR Viewer into its Access It! software.
An Integrated Access Control & DVR/NVR System
Access It! workstation with
Access DVR/NVR integration option
Control
Server
Local Area
Network
(TCP/IP) Access It! workstation
with DVR/NVR
One or more integration option
IP cameras
connected Access It! workstation with
to the LAN DVR/NVR integration option
(for live view)
Access It! workstation with
One or more DVRs or NVRs DVR/NVR integrationoption
connected to the LAN
Figure 2: This diagram shows the network setup for an RS2 Access Control System that has
been integrated with a DVR/NVR system.
Video and the analytics associated with it is certainly the fastest-develop-
ing area that is integrating with access control. New developments allow
users to choose intelligent cameras that have built-in content analytics
that can not only see the scene but can also interpret it using computer al-
gorithms that analyze what the camera is seeing. These analytics-enabled
cameras supplement the analytics software that resides on the application
server. Writing about these cameras in the March 2009 issue of SDM mag-
azine, in an article titled Wheres Everyone Going?, Gadi Piran, president
and chief operating officer of On-Net Surveillance Systems, points out:
Their capabilities include detection of specific movements and behaviors,
such as:
Motion detection (the size/shape, speed, and direction of a moving object)
Non-motion detection, such as stalled vehicles or an abandoned object
Behavior analysis, such as tailgating at entry points or loitering
continued on page 8
7 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
continued from page 7
Accurate optical character recognition (OCR) for applications such as license
plate recognition
In the same article, Piran also discusses the advantages of using PoE (Power-
over-Ethernet) and wireless technology to enable users to extend the reach of their
video-integrated access control systems to areas without a power supply, similar to
what is being done with wireless/IP locksets (see page 10 of this White Paper).
Integration with Intercom Systems
In an integrated access control and intercom system, the Access It! work-
stations connect through the LAN and access control server to an intercom
switch serving multiple intercom stations. Integration between the access
control system and the intercom stations allows automatic connection to
those stations during alarm processing. If an employee presses an emer-
gency call button during an incident, an alarm is generated in the Access
It! system, prompting a security officer to acknowledge the alarm. This
automatically connects the master intercom station to the emergency call
box, giving the security officer full audio of any ongoing incident.
An Integrated Access Control & Intercom System
Intercom Switch Access Access It! workstation with
Control Server Intercom System integration
option
Local Area
Network
(TCP/IP)
Access It! workstation with
Intercom System integration
option
Multiple Intercom Access It! workstation with
Stations connected Intercom System integration
to the Intercom Switch option
Access It! workstation with
Intercom System integration
option
Figure 3: This diagram shows the network setup for an RS2 Access Control System that has been integrated
with an intercom system.
8 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
Integration with Intrusion Detection
The integration of access control systems with intrusion detection is an
excellent example of how systems integration not only provides end users
with greatly increased functionality, but can also reduce overall security
system costs.
In the past, intrusion detection systems and access control systems were
installed using separate cabling, door contacts, etc., which increased
system installation costs. Also, the systems did not share data, making it
difficult to associate intrusion alarms with access control events. By inte-
grating access control with intrusion detection products, end users now
use a single, consistent GUI (graphical user interface) for both the access
control system and the intrusion detection system. This allows them to
monitor intrusion events and alarms, execute access control system tasks
based on those same events/alarms, record alarm event data in the access
control system events database, and even control day-to-day intrusion
detection system operations (arming/disarming zones, etc.) via the access
control system. (See Figure 4.)
An Integrated Access Control & Intrusion Detection System
Access Control Server Access It! workstation with
Intrusion Detection Integration
option
System
Keypad Access It! workstation
with Intrusion Detection
Intrusion Detection Integration option
Panel (TCP/IP)
One or more Intrusion
Detection panels connected
to the LAN
Local Area
Intrusion Detection
Network
Panel (TCP/IP)
(TCP/IP)
System
Keypad
Access It! workstation
with Intrusion Detection
Integration option
Figure 4: This diagram shows the network setup for an RS2 Access Control System that has been integrated
with an intrusion detection system
9 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
Integration with Wireless, IP and PoE Locksets
One of the most recent examples of integrating access control with other
physical security systems is that of wireless, IP, and PoE (Power-over-Eth-
enet) locksets. RS2 Technologies was one of the pioneers in partnering
with the manufacturers of both the IEEE 802.11 and 900 MHz technolo-
gies, which allowed users to extend the reach of their access control
systems through their existing wireless and IP infrastructures. Users can
add openings to their systems in locations that were previously difficult or
cost-prohibitive to incorporate using hard-wired technology. These wireless
locks not only provide centrally managed access control to these types of
locations, but they do so without much of the cost, labor and infrastructure
upgrades associated with traditional hard-wired systems.
As with the example of access control/intrusion detection integration,
wireless locks lower costs by reducing installation labor, simplifying project
management (fewer trade personnel), and leveraging existing infrastruc-
ture. (For example, a typical hard-wired access-controlled opening takes an
average of 8 hours to install and bring to operational status, whereas wire-
less locks take about an hour to install by a single technician.)
An Integrated Access Control & Wireless/IP Lockset System
Wireless Doors Access It! workstation with Wireless/IP
(900 MHz) Panel Interface Lockset Integration option
(Limited to 16 doors Module
per PIM)
PIM
LAN (TCP/IP)
Power-over
Wireless Ethernet
Gateway (PoE) capable
EP 1502
Access It! workstation
or with Wireless/IP Lockset
EP2500 Integration option
PoE Doors
(Unlimited)
Access Control
Server
WAP
Wireless
Access Point
Wireless Doors (802.11) Note: Systems can be set up to include
(Unlimited) any combination of wireless, PoE, and
traditional wired doors.
Figure 5: This diagram shows the network setup for an RS2 Access Control System that has been integrated
with wireless, IP, and PoE lockset systems.
10 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
Completely Integrated Systems
The adage The whole is greater than the sum of the parts is frequently
used to describe conditions or systems in which the synergistic effect of
combining individual parts or sub-systems produces a significantly en-
hanced outcome. Completely integrated security systems (a term which
should be used with considerable caution, as there will always be additional
functions and sub-systems that can be integrated into systems that were
previously considered complete) which combine several or all of the
functions described in Figures 1-5 are a good example of that maxim. Fig-
ure 6 below illustrates how a completely integrated security system might
combine elements of CCTV, video surveillance & analytics, intercom, intru-
sion detection, and wireless/IP and PoE locksets through the same Local
Area Network.
A Completely Integrated Security System
Access
Control
Server Intercom Switch
Multiple Intercom
Stations
Multiple Access It worksta-
CCTV Matrix tions with integration options
Switch for DVR/NVR, CCTV, Intercom,
Intrustion Detection, Wireless/
IP Locksets, etc.
LAN (TCP/IP)
One or more Power-over-Ethernet
Dome Cameras (PoE) capable
PoE Doors
(unlimited)
One or more
IP Cameras
(for live view)
Intrusion Detection
Panel (TCP/IP)
WAP
EP 1502 Wireless
or
EP 2500 Access Point
System
Keypad Wireless
Gateway
One or more Wireless
DVRs or NVRs PIM Doors
(see note)
Figure 6: This diagram shows the network setup for an RS2 Access Control System that has been integrated
with video surveillance, intercom, CCTV, intrusion detection, and wireless/IP and PoE lockset systems.
Note that in the case of wireless/IP locksets, systems operating on 900
MHz are limited to 16 doors per PIM (Panel Interface Module). With
IEEE 802.11 systems, there are no limits. PoE systems can also have an
unlimited number of doors. Systems can be set up to include any combi-
nation of wireless/IP, PoE, and traditional wired doors.
11 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
Integration with Software and Other Systems
Integration between access control systems and other elements of a
security system is not limited to physical sub-systems, but can also include
integration with other software systems. A good example is electronic visi-
tor management. For those not familiar with the subject, electronic visitor
management systems were created more than a decade ago to address
what Mark Eardley, in an article in Hi-Tech Security Solutions, called the big
loophole in access control. His point was that access control
Integration with access
control is not limited to systems did a great job of tracking employees, but not quite
physical sub-systems, as great of a job of tracking visitors.6 Up through the mid-90s,
but can also include visitor management consisted of visitors and contractors sign-
other software systems. ing a paper log with names that were at best, illegible, and at
worst, false. In the event of an emergency such as a fire, it was
impossible to quickly determine who was still in the building. To address these
issues, companies and organizations started to install stand-alone electronic
visitor management systems about 10 years ago and, within the past few
years, began integrating them with access control systems. However, even
as recently as 2008, estimates Howard Marson, CEO of visitor management
supplier EasyLobby, Inc., no more than 15% of visitor management systems
are integrated with access control.7
Comprehensive visitor management systems electronically scan the visitors
ID (business card, drivers license or passport), and automatically capture
name, company, title, contact information, etc. into a database file, with photo
and signature, name of the person being visited, reason for the visit, and
entry and exit times. Multiple stations can share a central database over the
network for monitoring and reporting. And, enterprise-level systems can also
track incoming packages and even visitors vehicles.8
In terms of integrating with access control, while the visitor management
system does, indeed, have physical equipment such as badge printers,
turnstiles, and self-serve kiosks (for un-manned lobbies), these are generally
controlled directly by the visitor management software. Integration between it
and access control software such as RS2s Access It! Universal occurs within
the same SQL server where both the visitor management and access control
databases reside. An example would be the integration between Access It!
and EasyLobbys SVM visitor management system, in which the SVM
software includes a configuration and installation utility that allows users to
6
Visitor Management, Hi-Tech Security Solutions, June 2007, Mark Eardley. 2007 Hi-Tech
Security Solutions.
7
Beyond the Visitor Ledger, SDM Magazine, October 10, 2008, Joan Engebretson; and Visitor ID
Integrates with Access, Security Magazine, October 8, 2008. 2008 SDM Magazine and Security
Magazine.
8
Tracking People, Packages and Vehicles, Security Magazine, February 1, 2009. 2009
Security Magazine.
12 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
install the integration between the two systems and configure a variety of
settings. Once the integration is established, operators use the Access It!
GUI to create access levels equivalent to those assigned by the visitor
management software.
The Importance of Partnering in Integration
Powerfully integrated systems start with powerful integration partners. RS2
has partnered with a number of the leading manufacturers of DVRs, NVRs,
CCTV and intercom systems, and intrusion detection panels, as well as with
companies offering employee and visitor management systems and other
access control products that can add value to our systems. Our integration
partners include such names as ABM Data Systems, Altronix, ASSA ABLOY,
AWID, Bioscrypt, Blackboard, Bosch, Costar Video Systems, Dedicated Mi-
cros, Digiop, Digital Watchdog, DMP (Digital Monitoring Products), EasyLob-
by, Exacq Technologies, Farpointe Data, HID, Integral Technologies, Integrat-
ed Engineering, IR Schlage, March Networks, Mercury Security, Milestone
Systems, On-Net Surveillance Systems, Inc., Panasonic, Pelco, RTS Sentry,
Stentofon (Zenitel), Toshiba, Vicon, Vision Controls, XceedID, and others.
The Role of the Systems Integrator
The importance of the professional systems integrator organization in the
planning, installation, and servicing of a successfully integrated access control
system simply cannot be overstated. And, it seems so obvious
The importance of the
to us that we will not devote more than a few paragraphs to cite
systems integrator to a
the opinions of other observers:
successfully integrated
access control system
cannot be overstated. We try to work with integrators that we have relationships with,
and we feel are qualified and will give us good service and
pricing. As you get a few systems under your belt, that relationship and trust
begins to build. We are achieving seamless integration at this point. Speaking
for myself, low cost isnt always the determining factor. For me, its actually
fairly low on the list in determining who will get a job. 9
Throughout its history, RS2 Technologies has endeavored to work with
top-notch systems integrators who are viewed by end users as security
system experts and security partners, and not as vendors.
Integrators often specialize in high-end systems, but are either familiar with
all others or can easily figure it out. They are at their best in complex projects
that join parts of separate systems to function with core usability. 10
9
Integration: The End Users Perspective, SDM Magazine, 7/1//06, Russ Gager. 2006 SDM.
10
The Integrator Relationship, Security Magazine, April 2009, Bill Zalud. 2009 Security Magazine.
13 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
For a list of integrators in your area that can plan and install an integrated
access control system, end users should contact the RS2 Regional Sales
Manager in their area or RS2 Corporate Headquarters. For that contact
information, see page 17 of this White Paper.
The Future of Integration: Convergence
What is the future of integration in access control? Certainly, we will see
more discrete systems join the current list of those that integrate with ac-
cess control. Beyond that, however, will be a new level of integration that
most observers define as convergence. But, what is
Most security leaders
convergence? In the past few years, perhaps no se-
see convergence as
curity industry buzzword has been defined in articles
the bringing together
of physical and logical and promotional materials more than convergence,
security. writes Honeywell Senior Product Manager Beth
Thomas, in an article in CSO Online. These defini-
tions have most commonly referred to the integration of physical security
and IT systems, with occasional elements of building control. 11
E. John Sutton, security and integration manager of the Port Authority of
NY and NJ, offers that Enterprise level systems combine many security
functions within one system; this is convergence at some defined level. 12
However, as we quoted Bill Zalud of Security on page 4, most security
leaders see convergence as the bringing together of physical and logical
or computer security in ways that primarily emphasize access controls
and identity management. 13 That, it seems to us, is the most useful
definition. How will this be accomplished? Most indications are that, as
was the initial experience with integration, it will again be the joint efforts of
manufacturers, integrators and end users that determines the final shape
of convergence. The difference will be that, at the end user level, IT profes-
sionals will be a bigger part of the mix.
11
Industry View: Checklist for Converged Access Control, CSO Online, June 2008. 2008 CXO
Media, Inc.
12
Convergence 2.0, Security Magazine, February 2009, Bill Zalud. 2009 Security Magazine.
13
Ibid.
14 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
Questions to Ask Access Control Manufacturers and Systems Integrators
As in our first two White Papers, we offer a list of questions that purchasers of
Access Control Systems should ask the manufacturers of those systems in rela-
tion to the integration of the system with other sub-systems. (For copies of previous
lists of Questions to Ask Vendors, please download our White Papers on Total Cost
of Operation and Open Architecture.) Because this White Paper deals with the inte-
gration of access control with other systems, and because of the importance of the
systems integrator in the installation of such an integrated system, we have expand-
ed the list to include questions that should be asked of systems integrators. Like all
such lists, this list is not all-inclusive, but a good basic list of questions would include:
Questions for Access Control Manufacturers:
What other security systems does your system integrate with (e.g., CCTV,
intercom, intrusion detection, visitor management, etc.)?
How long have you been integrating in each of these areas?
Specifically, which manufacturers of each of these types of systems do you
integrate with?
Does your Dealer List include systems integrators who have experience in
installing complex integrated systems?
Can you provide a list of such integrators in our area?
What kind of a relationship do you have with these integrators?
Can you provide a list of projects that have involved integration of your access
control system with other systems?
How familiar are you with our business sector (e.g., education, banking,
hospitals, etc.)?
Do you have integrated installations in our business sector?
Can you provide references at those installations?
Questions for Systems Integrators:
In what types of systems do you specialize?
What manufacturers products do you install?
How many systems have you installed that have involved integration between
access control and at least one other sub-system?
Can you provide a list of these, with names and numbers of references?
How many project managers, installation technicians, service technicians,
and account managers work from the office that would install and service
our system?
What kind of relationship do you have with the manufacturers of each of the
systems that would be part of our project?
If applicable to the project: Do you have personnel who have IT/IP knowledge?
For a more complete list of questions for systems integrators, see The Integrator
Relationship, April 2009 Security Magazine.
15 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
Conclusions
Stand-alone, un-integrated security systems and sub-systems are a thing of the
past. They are neither operationally effective nor cost effective. The security system
of today is a system that efficiently and effectively integrates access control with mul-
tiple sub-systems, both physical and software. The security system of tomorrow will
be a system that accomplishes the convergence of physical and logical (IT) security.
End users who are contemplating the purchase and installation of new access con-
trol systems (or the upgrade/expansion of existing systems) should do their research
on integrated systems with manufacturers and systems integrators by asking them
at a minimum the questions outlined in this White Paper. First and foremost, they
should seek out a systems integration organization that has experience in the instal-
lation of complex integrated systems, and should develop a long-term partnership
with that organization.
16 Integration in Access Control Systems
RS2 TECHNOLOGIES W H I T E PA P E R May 2009
About RS2 Technologies, LLC
RS2 Technologies, headquartered in Munster, Indiana, is a technology-driven
developer and manufacturer of cutting edge access management hardware
and software. The companys hardware line includes a wide range of system
control processors, input/output modules, multiplexers, card readers and prox-
imity and smart cards. RS2 also offers the industrys most advanced, easy-
to-use software with its Access It! line of access control software. RS2 is a
Microsoft Certified Partner with ISV (Independent Software Vendor) software
solutions competency status.
For more information, visit our web site at www.rs2tech.com or contact:
Corporate Headquarters
Gary Staley National Sales Director
877.682.3532
gstaley@rs2tech.com
St. Louis Office
David W. Barnard
Director of Dealer Development
877.682.3532
dbarnard@rs2tech.com
West Coast Sales Office
Ty Caudill
Western Regional Sales Manager
877.682.3532
tcaudill@rs2tech.com
Southeast Sales Office
Ed Sims
Southeast Regional Sales Manager
877.682.3532
esims@rs2tech.com
Northeast Sales Office
David Bensky
Northeast Regional Sales Manager
301.524.2971
dbensky@rs2tech.com
European Sales Offices
UK (London): 0207.993.4737
Italy (Milan): 029.175.4046
Asia Sales Offices
Beijing: 86.10.58630222 ext. 315
Hong Kong: 852.2893.8899 ext. 308
17 Integration in Access Control Systems
Potrebbero piacerti anche
- RCS 8.2 SysAdmin 1.201 ENDocumento119 pagineRCS 8.2 SysAdmin 1.201 ENAndres CelisNessuna valutazione finora
- Sinopoli System Integration Chap 16Documento4 pagineSinopoli System Integration Chap 16ryan angNessuna valutazione finora
- Integration Strategy 1Documento13 pagineIntegration Strategy 1Renchester AmoresNessuna valutazione finora
- Psospg 1701Documento22 paginePsospg 1701neo.sanjeev6666Nessuna valutazione finora
- Comparative Study On Network Monitoring Tools: International Research Journal of Engineering and Technology (Irjet)Documento3 pagineComparative Study On Network Monitoring Tools: International Research Journal of Engineering and Technology (Irjet)Irfaan Khan QasmiNessuna valutazione finora
- LNA08111 eDocumento72 pagineLNA08111 eAdonai BinghimanNessuna valutazione finora
- The Power To Predict and Prevent: Infrastructure Monitoring 101Documento23 pagineThe Power To Predict and Prevent: Infrastructure Monitoring 101whizboyNessuna valutazione finora
- Monitoring and Observability For: Data PlatformDocumento27 pagineMonitoring and Observability For: Data PlatformkholisNessuna valutazione finora
- Platform Architecture ComparitionDocumento6 paginePlatform Architecture Comparitionali aghajaniNessuna valutazione finora
- Oic Presentation en VfinalDocumento27 pagineOic Presentation en Vfinalricky patealNessuna valutazione finora
- Genetec - Optimizing Video and Access Control Integration With A Next-Generation Unified Security Platform PDFDocumento13 pagineGenetec - Optimizing Video and Access Control Integration With A Next-Generation Unified Security Platform PDFKonangi ChandrasekharNessuna valutazione finora
- IET2016 Gvelez Ootaegui PostprintDocumento30 pagineIET2016 Gvelez Ootaegui Postprintelizabarzi73Nessuna valutazione finora
- Iot@Work Automation Middleware System Design and ArchitectureDocumento8 pagineIot@Work Automation Middleware System Design and ArchitectureTeddy IswahyudiNessuna valutazione finora
- Iotivity - Connecting Things in Iot: Ashok SubashDocumento48 pagineIotivity - Connecting Things in Iot: Ashok SubashVishal RathodNessuna valutazione finora
- A Comprehensive Review of Embedded System Design Aspects For Rural Application PlatformDocumento7 pagineA Comprehensive Review of Embedded System Design Aspects For Rural Application PlatformAbdelraheem AhmedNessuna valutazione finora
- IQ R DatasheetDocumento100 pagineIQ R DatasheetWaqas SaeedNessuna valutazione finora
- Scripting Your Network Operations and Security With Ansible and AppViewXDocumento22 pagineScripting Your Network Operations and Security With Ansible and AppViewXSathishkumar JanakiramanNessuna valutazione finora
- Interoperability in The Iot - An Evaluation of The Semantic-Based ApproachDocumento9 pagineInteroperability in The Iot - An Evaluation of The Semantic-Based ApproachMohammed AfnanNessuna valutazione finora
- Standard & The Long TailDocumento25 pagineStandard & The Long Tail21i046 Muizzah Al-qoroniNessuna valutazione finora
- 002 Chapter 2Documento18 pagine002 Chapter 2Indra YantomoNessuna valutazione finora
- Embedded and IOT Systems: (Industrial Training and Viva)Documento25 pagineEmbedded and IOT Systems: (Industrial Training and Viva)Dark VoidNessuna valutazione finora
- Learning Packet 1 ELECTIVE 4Documento17 pagineLearning Packet 1 ELECTIVE 4Kyla DacutNessuna valutazione finora
- Nagios Based Enhanced IT Management System: Ahmed D. KORADocumento9 pagineNagios Based Enhanced IT Management System: Ahmed D. KORAkhadirNessuna valutazione finora
- Sensors: Integrated Design and Implementation of Embedded Control Systems With ScilabDocumento15 pagineSensors: Integrated Design and Implementation of Embedded Control Systems With ScilabCarlos Sulca NeiraNessuna valutazione finora
- Analyzing An OT Network, What To ExpectDocumento6 pagineAnalyzing An OT Network, What To ExpectRodrigo José SouzaNessuna valutazione finora
- Tc-Bac Bms Software Kmc-UsaDocumento16 pagineTc-Bac Bms Software Kmc-UsaHa CongNessuna valutazione finora
- Architectural Design (SD&A)Documento33 pagineArchitectural Design (SD&A)Nareen AsadNessuna valutazione finora
- IIOTManufacturingDocumento17 pagineIIOTManufacturingkedar majethiyaNessuna valutazione finora
- IIoT For Engineers - 2016 12 PDFDocumento24 pagineIIoT For Engineers - 2016 12 PDFjairo73scribdNessuna valutazione finora
- Research On Automation Integration Technology of Application Systems Based On Web ServicesDocumento6 pagineResearch On Automation Integration Technology of Application Systems Based On Web ServicesRitam DasNessuna valutazione finora
- Ma Network Automation Guide EbookDocumento25 pagineMa Network Automation Guide Ebookjalvarez82Nessuna valutazione finora
- Application Telecontrol St7 enDocumento110 pagineApplication Telecontrol St7 enBob RhemNessuna valutazione finora
- Types of Edge Computing Part 2 - Etsi Mec Deployment Models - Deck - 862980Documento38 pagineTypes of Edge Computing Part 2 - Etsi Mec Deployment Models - Deck - 862980KLNessuna valutazione finora
- CSE3001Documento34 pagineCSE3001Majety S LskshmiNessuna valutazione finora
- Testing Network Security Using OPNET: Agustin Zaballos, Guiomar Corral, Isard Serra, Jaume AbellaDocumento5 pagineTesting Network Security Using OPNET: Agustin Zaballos, Guiomar Corral, Isard Serra, Jaume Abellaupindah70Nessuna valutazione finora
- Z Chondamrongkul Et Al. - 2020 - Automated Security Analysis For Microservice ArchiDocumento4 pagineZ Chondamrongkul Et Al. - 2020 - Automated Security Analysis For Microservice ArchiMonica Johana Buitrago RamirezNessuna valutazione finora
- Programmatic Interoperability: B. Craig Meyers James D. SmithDocumento44 pagineProgrammatic Interoperability: B. Craig Meyers James D. SmithSoftware Engineering Institute Publications100% (1)
- Ultimate Guide To ObservabilityDocumento16 pagineUltimate Guide To ObservabilityShruthiNessuna valutazione finora
- An Authentication Model For IoT CloudsDocumento4 pagineAn Authentication Model For IoT CloudsTeddy IswahyudiNessuna valutazione finora
- HikCentral-Professional Version 2 BrochureDocumento19 pagineHikCentral-Professional Version 2 BrochureArioNessuna valutazione finora
- ET - System IntegrationDocumento20 pagineET - System IntegrationYUSNITA BINTI MUHAMAD NOORNessuna valutazione finora
- MELSEC iQ-F Series PDFDocumento192 pagineMELSEC iQ-F Series PDFedu126121Nessuna valutazione finora
- Iot Reference Architecture Guide New PDFDocumento12 pagineIot Reference Architecture Guide New PDFRishi KumarNessuna valutazione finora
- Cyberi 2018 8337550Documento6 pagineCyberi 2018 8337550Nguyễn Văn AnhNessuna valutazione finora
- Mitsubishi IQ F PLCDocumento192 pagineMitsubishi IQ F PLCChi Nguyen NgocNessuna valutazione finora
- Facilio State of Operations and Maintenance SoftwareDocumento25 pagineFacilio State of Operations and Maintenance Softwarearunkumar277041Nessuna valutazione finora
- Journal of Network and Computer ApplicationsDocumento19 pagineJournal of Network and Computer ApplicationsPedrito OrangeNessuna valutazione finora
- Mitsubishi iQ-F-FX Series Selection GuideDocumento82 pagineMitsubishi iQ-F-FX Series Selection GuideNhậtQuangNguyễnNessuna valutazione finora
- Latesttechnomanias Blogspot Com 2011 08 Implementation Evaluation and HTMLDocumento1 paginaLatesttechnomanias Blogspot Com 2011 08 Implementation Evaluation and HTMLManishNessuna valutazione finora
- 19 04 11 Sap Cloud Platform Ipass OverviewDocumento88 pagine19 04 11 Sap Cloud Platform Ipass OverviewFlex TrackNessuna valutazione finora
- Automation Systems and Control Components: Consistent, Intelligent and Future-ProofDocumento168 pagineAutomation Systems and Control Components: Consistent, Intelligent and Future-ProofEljameely JamaleldeenNessuna valutazione finora
- ETL Integrator User GuideDocumento63 pagineETL Integrator User GuideAmit KatkarNessuna valutazione finora
- 05.1 Software ArchtiecutreDocumento33 pagine05.1 Software ArchtiecutrePatricia Aurelia Tekad TuerahNessuna valutazione finora
- Nms 2nd UnitDocumento30 pagineNms 2nd UnitjilikajithendarNessuna valutazione finora
- Gain Cloud Agility With Software-Defined Infrastructure - A Blueprint For Optimizing IT Infrastructure and Operations-A00021159enwDocumento19 pagineGain Cloud Agility With Software-Defined Infrastructure - A Blueprint For Optimizing IT Infrastructure and Operations-A00021159enwSara-QMNessuna valutazione finora
- Use of Open Source TechnologiesDocumento7 pagineUse of Open Source Technologiestest2012Nessuna valutazione finora
- How OPC UA and MQTT Prevent Interoperability - LinkedInDocumento7 pagineHow OPC UA and MQTT Prevent Interoperability - LinkedInajayvgNessuna valutazione finora
- IP-XACT Standardized IP Interfaces For Rapid IP IntegrationDocumento26 pagineIP-XACT Standardized IP Interfaces For Rapid IP IntegrationAbdul ThoufiqNessuna valutazione finora
- PI PROFINET System Description en WebDocumento28 paginePI PROFINET System Description en WebMarcos Paulo Menezes SilvaNessuna valutazione finora
- Export REACH 20230201 05274627Documento2 pagineExport REACH 20230201 05274627Minh NhậtNessuna valutazione finora
- MCCB Selection For 75KW IE3 MotorDocumento1 paginaMCCB Selection For 75KW IE3 MotorMinh NhậtNessuna valutazione finora
- Export REACH 20230201 05280728Documento2 pagineExport REACH 20230201 05280728Minh NhậtNessuna valutazione finora
- Zelio Control Relays - RM22TG20 DatasheetDocumento7 pagineZelio Control Relays - RM22TG20 DatasheetMinh NhậtNessuna valutazione finora
- How To Select Motor Protection Component When Using IE3 MotorDocumento1 paginaHow To Select Motor Protection Component When Using IE3 MotorMinh NhậtNessuna valutazione finora
- Kavacha Bro Eng May2013Documento28 pagineKavacha Bro Eng May2013Minh NhậtNessuna valutazione finora
- Star Delta CircuitDocumento1 paginaStar Delta CircuitMinh NhậtNessuna valutazione finora
- MEP Planning ManualDocumento118 pagineMEP Planning ManualMinh NhậtNessuna valutazione finora
- Atys T Nmo 541995d EN PDFDocumento66 pagineAtys T Nmo 541995d EN PDFMinh NhậtNessuna valutazione finora
- Quick Installation Manual IP GatewayDocumento28 pagineQuick Installation Manual IP GatewayMinh Nhật100% (2)
- Micrologic For ACB MVSDocumento8 pagineMicrologic For ACB MVSMinh NhậtNessuna valutazione finora
- Sample Wiring Diagram-InNCOMDocumento2 pagineSample Wiring Diagram-InNCOMMinh Nhật100% (2)
- Digital Signal Processing: Frequency Response Digital Filter DesignsDocumento23 pagineDigital Signal Processing: Frequency Response Digital Filter DesignsMinh NhậtNessuna valutazione finora
- A Generalized Multilevel Inverter TopologyDocumento8 pagineA Generalized Multilevel Inverter TopologyMinh NhậtNessuna valutazione finora
- Effects of High or Low VoltageDocumento2 pagineEffects of High or Low VoltageMinh NhậtNessuna valutazione finora
- Useful Vocabulary For The Resume and InterviewDocumento10 pagineUseful Vocabulary For The Resume and InterviewMinh NhậtNessuna valutazione finora
- HERICDocumento7 pagineHERICMinh NhậtNessuna valutazione finora
- L01Documento8 pagineL01Minh NhậtNessuna valutazione finora
- SSPre PFIEV Chapter1 2012Documento174 pagineSSPre PFIEV Chapter1 2012Minh NhậtNessuna valutazione finora
- FFT2 AlgorithmDocumento41 pagineFFT2 AlgorithmMinh NhậtNessuna valutazione finora
- FFT2 AlgorithmDocumento41 pagineFFT2 AlgorithmMinh NhậtNessuna valutazione finora
- Sport On The Barcoo: Regional Tidy Towns Awards To Tambo and BlackallDocumento10 pagineSport On The Barcoo: Regional Tidy Towns Awards To Tambo and BlackallbarcooindependentNessuna valutazione finora
- Tico Tico No FubaDocumento3 pagineTico Tico No Fubaoseas oliveira OliveiraNessuna valutazione finora
- Christmas SongsDocumento3 pagineChristmas SongsmelissaringjalljaNessuna valutazione finora
- English File: Grammar, Vocabulary, and PronunciationDocumento3 pagineEnglish File: Grammar, Vocabulary, and PronunciationMirian Apaza100% (1)
- Tugas Penilaian 1, MK B - Ing PGSDDocumento2 pagineTugas Penilaian 1, MK B - Ing PGSDevidewisartika610Nessuna valutazione finora
- AAU5833f Technical Specifications (V100R016C10 - Draft A) (PDF) - ENDocumento35 pagineAAU5833f Technical Specifications (V100R016C10 - Draft A) (PDF) - ENMohammed ShakilNessuna valutazione finora
- Grade 09 Sinhala Language and Literature Textbook Sinhala Medium - New SyllabusDocumento220 pagineGrade 09 Sinhala Language and Literature Textbook Sinhala Medium - New SyllabusMatheesha WijewardanaNessuna valutazione finora
- New American Plays (Anne Commire, Philip Kan Gotanda Etc.)Documento260 pagineNew American Plays (Anne Commire, Philip Kan Gotanda Etc.)RonnieNessuna valutazione finora
- Controller Editor Ableton Live Template Manual EnglishDocumento51 pagineController Editor Ableton Live Template Manual EnglishD CNessuna valutazione finora
- FM Transmitter: General HD Upgrade FM Signal-To-Noise RatioDocumento2 pagineFM Transmitter: General HD Upgrade FM Signal-To-Noise RatioJose Hugo Sosa SalasNessuna valutazione finora
- Lesson Plan Music 9Documento4 pagineLesson Plan Music 9Shamaica SurigaoNessuna valutazione finora
- SidekickQuickGuide enDocumento2 pagineSidekickQuickGuide enalogeno_Nessuna valutazione finora
- Grimshaw, Jeremy - Music of A More Exalted SphereDocumento35 pagineGrimshaw, Jeremy - Music of A More Exalted SphereRicardo AriasNessuna valutazione finora
- Verbos en InglesDocumento17 pagineVerbos en InglesEma Orellana100% (1)
- CNX Nano2 ManualDocumento13 pagineCNX Nano2 Manualbillren1100% (1)
- Lumberjacks in Love (Sheet Music)Documento5 pagineLumberjacks in Love (Sheet Music)Jimmy KaplanNessuna valutazione finora
- Horace Silver - Preacher (Piano Voicings)Documento3 pagineHorace Silver - Preacher (Piano Voicings)Nicola Tontoli83% (6)
- South Scope Oct 2010Documento84 pagineSouth Scope Oct 2010kasam193Nessuna valutazione finora
- 2nd Quarter Exam Music and ArtsDocumento10 pagine2nd Quarter Exam Music and ArtsNiño Joshua Ong BalbinNessuna valutazione finora
- Transformer Isolated Gate DriveDocumento9 pagineTransformer Isolated Gate DriverobertdenchNessuna valutazione finora
- Acoustical and Perceptual Characteristics of Alaryngeal SpeechDocumento59 pagineAcoustical and Perceptual Characteristics of Alaryngeal SpeechKUNNAMPALLIL GEJO JOHN100% (1)
- English DialectsDocumento18 pagineEnglish Dialectsduneden_1985100% (9)
- Pathologie Générale Du BâtimentDocumento226 paginePathologie Générale Du BâtimentGCAlgerie.com100% (2)
- Death of A Salesman SGDocumento7 pagineDeath of A Salesman SGThomas DyeNessuna valutazione finora
- Oe 254 Antenna TM PDFDocumento2 pagineOe 254 Antenna TM PDFMichaelNessuna valutazione finora
- Bright Ideas - 3 - Evaluation Material PDFDocumento48 pagineBright Ideas - 3 - Evaluation Material PDFAnalia Garcia100% (2)
- Eric DollardDocumento30 pagineEric Dollardgeorge100% (1)
- Lesson Plan - Nursery Rhyme - 1st TryDocumento6 pagineLesson Plan - Nursery Rhyme - 1st TryNadyaCazacNessuna valutazione finora
- Aef 1 File Test 4 170107213147 PDFDocumento4 pagineAef 1 File Test 4 170107213147 PDFDHeartNessuna valutazione finora
- Graziela Bortz: Rhythm in The Music of Brian Ferneyhough, Michael Finnissy, and Arthur KampelaDocumento127 pagineGraziela Bortz: Rhythm in The Music of Brian Ferneyhough, Michael Finnissy, and Arthur KampelaAriel Magno da CostaNessuna valutazione finora