Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Flow Based Detectingddos Attack in Large Scale Network
Caricato da
pramodCopyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Flow Based Detectingddos Attack in Large Scale Network
Caricato da
pramodCopyright:
Formati disponibili
International Journal on Applications in Information and Communication Engineering
Volume 2: Issue 1: January 2016, pp 43-48. www.aetsjournal.com
ISSN (Online) : 2394-6237
----------------------------------------------------------------------------------------------------------------------------- ------------------------------
Flow Based DetectingDDoS Attack in Large
Scale Network by Using Entropy Variation
Technique
V.Deepa ,V.Nandhini
A. IP trace back
Abstract A distributed denial-of-service (DDoS) attack is
an attempt to make a computer resource unavailable to its
intended users. A number of IP traceback approaches have
been suggested to identify attackers and there are two major
methods for IP trace back, the probabilistic packet marking
(PPM) and the deterministic packet marking (DPM) Both of
these strategies require routers to inject marks into individual
packets. The memory less feature occur in the Internet routing
mechanisms makes it extremely hard for old mechanisms. So
newly introduced effective and efficient IP trace back scheme
against DDoS attacks based on entropy variations. In trace
back mechanisms identifying the number of zombies in large
scale network and all so give the authentication for blocked
users. It works as an independent software module with
current routing software. This makes it a feasible and easy to
be implemented solution for the current Internet.
IP trace back means the capability of identifying the actual
source of any packet sent across the Internet. Because of the
vulnerability of the original design of the Internet, we may not
be able to find the actual hackers at present. In fact, IP
traceback schemes are considered successful if they can
identify the zombies from which the DDoS attack packets
entered the Internet. Research on DDoS detection mitigation
and filtering has been conducted pervasively.
B. Packet pollution
However, the efforts on IP traceback are limited. A
number of IP traceback approaches have been suggested to
identify attackers and there are two major methods for IP
traceback, the probabilistic packet marking (PPM) and the
deterministic packet marking (DPM). Both of these strategies
require routers to inject marks into individual packets.
Moreover, the PPM strategy can only operate in a local range
of the Internet (ISP network), where the defender has the
authority to manage. However, this kind of ISP networks is
generally quite small, and we cannot traceback to the attack
sources located out of the ISP network. The DPM strategy
requires all the Internet routers to be updated for packet
marking. However, with only 25 spare bits available in as IP
packet, the scalability of DPM is a huge problem. Moreover,
the DPM mechanism poses an extraordinary challenge on
storage for packet logging for routers. Therefore, it is
infeasible in practice at present. Further, both PPM and DPM
are vulnerable to hacking, which is referred to as packet
pollution.
IndexTermsDistributed
Denial-of-Service
(DDoS),
Probabilistic Packet Marketing (PPM), Deterministic Packet
Marketing (DPM), Routers, Internet Routing Mechanisms.
I. INTRODUCTION
DoS attacks, attackers generate a huge amount of
requests to victims through compromised computers
(zombies), with the aim of denying normal service or
degrading of the quality of services. It has been a major threat
to the Internet since year 2000, and a recent survey on the
largest 70 Internet operators in the world demonstrated that
DDoS attacks are increasing dramatically, and individual
attacks are more strong and sophisticated. Furthermore, the
survey also found that the peak of 40 gigabit DDoS attacks
nearly doubled in 2008 compared with the previous year. The
key reason behind these phenomena is that the network
security community does not have effective and efficient
traceback methods to locate attackers as it is easy for attackers
to disguise themselves by taking advantages of the
vulnerabilities of the World Wide Web, such as the dynamic,
stateless, and anonymous nature of the Internet.
C. Entropy Variations
IP trace back methods should be independent of packet
pollution and various attack patterns. In previous work on
DDoS attack detection, compared the packet number
distributions of packet flows, which are out of the control of
attackers once the attack is launched, and found that the
similarity of attack flows is much higher than the similarity
among legitimate flows, e.g., flash crowds. Entropy rate, the
entropy growth rate as the length of a stochastic sequence
increases , was employed to find the similarity between two
flows on the entropy growth pattern, and relative entropy, an
abstract distance between two probabilistic mass distributions,
was taken to measure the instant difference between two
V.Deepa , Department of Computer Science&Engg,Mahendra college of
engineering ,Salem (Email: erdeepasri22@gmail.com)
V.Nandhini , Vivekanantha college of Technology for women, Namakkal.
(Email :nandhinigenuine@gmail.com)
43
International Journal on Applications in Information and Communication Engineering
Volume 2: Issue 1: January 2016, pp 43-48. www.aetsjournal.com
ISSN (Online) : 2394-6237
----------------------------------------------------------------------------------------------------------------------------- -----------------------------flows. A novel mechanism for IP traceback using information and the victim notices that it is under attack, it will start the
theoretical parameters, and there is no packet marking in the traceback procedure. The workload of traceback is distributed,
proposed strategy; therefore, can avoid the inherited and the overall traceback time mainly depends on the network
shortcomings of the packet marking mechanisms. Categorize delays between the victim and the attackers.
packets that are passing through a router into flows, which are
II. RELATED WORK
defined by the upstream router where a packet came from, and
Denials of Service (DOS) [5] attacks are intended to shut
the destination address of the packet. During non-attack
periods, routers are required to observe and record entropy down the servers for a period of time. To make site nonfunctional for a time the main part of attack is DOS attack.
variations of local flows.
DOS attacks are usually doing by following methods: Send
D. Pushback Process
unlimited amount of packets to the server; executing
Flow entropy variation or entropy variation malwares; teardrop attack; Application level flood Sending
interchangeably. Once a DDoS attack has been identified, the unlimited packets by ping command is also known as ICMP
victim initiates the following pushback process to identify the flood. This method can be done in the following way. A
locations of zombies: the victim first identifies which of its simple DOS attack code would be: Ping {ip} -t -l 20000 on
upstream routers are in the attack tree based on the flow command prompt window. This command sends 20000 bytes
entropy variations it has accumulated, and then submits of data to the ip, in a single packet. The -t is to ping the
requests to the related immediate upstream routers. The specified host until stopped and -l is to specify the buffer size.
upstream routers identify where the attack flows came from A Teardrop attack involves sending mangled Internet Packet
based on their local entropy variations that they have fragments with overlapping, over-sized, payloads to the target
monitored. Once the immediate upstream routers have machine. In peer to peer attack thousands of computers will
identified the attack flows, they will forward the requests to try to access a single computer at the same time. It will break
their immediate upstream routers, respectively, to identify the down all the connection from the server at last the target
attacker sources further; this procedure is repeated in a parallel machine will fail. Application level flood is by the m isand distributed fashion until it reaches the attack source(s) or programming of an application installed on the server. So it
the discrimination limit between attack flows and legitimate will consume a major portion of server computing power and
flows is satisfied.
memory.
Distributed denial of service (DDoS) [9] attacks present a
E. PPM and DPM
significant security threat to corporations, and the threat
Our analysis, experiments, and simulations demonstrate that appears to be growing In one study, covering a three-week
the proposed traceback mechanism is effective and efficient period in 2001, investigators observed more than 12,000
compared with the existing methods. The current strategy is attacks against more than 5000 distinct targets, ranging from
fundamentally different from the existing PPM or DPM well-known ecommerce companies such as Amazon and
traceback mechanisms, and it outperforms the available PPM Hotmail to small foreign ISPs and dial-up connections. DDoS
and DPM methods. Because of this essential change, the attacks make computer systems inaccessible by flooding
proposed strategy overcomes the inherited drawbacks of servers, networks, or even end user systems with useless
packet marking methods, such as limited scalability, huge traffic so that legitimate users can no longer gain access to
demands on storage space, and vulnerability to packet those resources. In a typical DDoS attack, a large number of
pollutions. The proposed method brings no modifications on compromised hosts are amassed to send useless packets. In
current routing software. Both PPM and DPM require update recent years, the attack methods and tools have become more
on the existing routing software, which is extremely hard to sophisticated, effective, and more difficult to trace to the real
achieve on the Internet. On the other hand, our proposed attackers, while defense technologies have been unable to
method can work independently as an additional module on withstand large-scale attacks.
routers for monitoring and recording flow information, and
A denial of service (DoS) attack is an attempt to prevent
communicating with its upstream and downstream routers legitimate users of a service from using that service. When this
when the pushback procedure is carried out. The current attack comes from a single host or network node, then it is
method will be effective for future packet flooding DDoS simply referred to as a DoS attack. A more serious threat is
attacks because it is independent of traffic patterns. Some posed by a DDoS attack. In a DDoS attack, an attacker is able
previous works depend heavily on traffic patterns to conduct to recruit a number of hosts throughout the Internet to
their traceback. For example, they expected that traffic simultaneously or in a coordinated fashion launch an attack
patterns obey Poisson distribution or Normal distribution. upon the target. This section is concerned with DDoS attacks.
However, traffic patterns have no impact on the proposed First, we look at the nature and types of attacks. Next, we
scheme; therefore, deal with any complicated attack patterns, examine means by which an attacker is able to recruit a
even legitimate traffic pattern mimicking attacks. The network of hosts for attack launch. Finally, this section looks
proposed method can archive real-time traceback to attackers. at countermeasures.
Once the short-term flow information is in place at routers,
44
International Journal on Applications in Information and Communication Engineering
Volume 2: Issue 1: January 2016, pp 43-48. www.aetsjournal.com
ISSN (Online) : 2394-6237
----------------------------------------------------------------------------------------------------------------------------- -----------------------------To handle a novel framework to detect and identify DDoS that the attackers address can be localized to within 25
attacks. Our proposed approach is able to detect any type of equally likely sites which render PPM effective against single
DDoS attacks such as TCP SYN flood, TCP RST flood, UDP source attacks. Next, to concentrate the consequences of the
flood, ICMP flood, and DNS flood, as long as they use attacker mounting distributed DoS attacks where each
spoofed source IP addresses. The key idea of our framework is partaking attack host transmits a minimal traffic volume to
to exploit spatial and temporal correlation of DDoS attack maximize anonymity, and attack volume amplification is
traffic. In this framework, we design a perimeter-based anti- achieved by engaging a large number of sources. Thus PPM,
DDoS system, in which traffic is analyzed only at the edge while effective against single-source attacks, is potentially
routers of an Internet service provider (ISP) network. The anti- vulnerable when subject to distributed DoS attacks.
DDoS system consists of two major components: (1) feature
The Source Path Isolation Engine (SPIE) to enable IP trace
extraction (2) detection. Our feature extraction scheme back, the ability to identify the source of a particular IP packet
exploits temporal correlation between the outgoing traffic and given a copy of the packet to be traced, its destination, and an
the incoming traffic on a link, which makes distinct features approximate time of receipt. Historically, tracing individual
between normal and attack traffic; the 2D matching features packets has required prohibitive amounts of memory; one of
are used by the detection module. In detection, our machine SPIEs key innovations is to reduce the memory requirement
learning algorithm is able to utilize the spatial correlation of (down to 0.5% of link bandwidth per unit time) through the
DDoS attack traffic at different routers.
use of Bloom filters [3]. By storing only packet digests, and
Trace back mechanisms are a critical part of the defense not the packets themselves, SPIE also does not increase a
against IP spoofing and DoS attacks, as well as being of networks vulnerability to eavesdropping. SPIE therefore
forensic value to law enforcement. Currently proposed IP trace allows routers to efficiently determine if they forwarded a
back mechanisms are inadequate to address the trace back particular packet within a specified time interval while
problem for the following reasons: they require DDoS victims maintaining the privacy of unrelated traffic.
to gather thousands of packets to reconstruct a single attack
In other words, such attacks may reduce the quality of
path; they do not scale to large scale Distributed DoS attacks; services unnoticeably. Our defense method calls for
and they do not support incremental deployment. We propose collaborative detection and filtering (CDF) of shrew DDoS
Fast Internet Trace back (FIT), a new packet marking attacks. We detect shrew attack flows hidden in legitimate
approach that significantly improves IP trace back in several TCP/UDP streams by spectral analysis against pre-stored
dimensions: (1) victims can identify attack paths with high template of average attack spectral characteristics. This novel
probability after receiving only tens of packets, a reduction of scheme is suitable for either software or hardware
13 orders of magnitude compared to previous packet marking implementation. The CDF scheme is implemented with the
schemes; (2) FIT performs well even in the presence of legacy NS-2 network simulator using real-life Internet background
routers, allowing every FIT-enabled router in path to be traffic mixed with attack datasets used by established research
identified; and (3) FIT scales to large distributed attacks with groups. Our simulated results show high detection accuracy by
thousands of attackers. Compared with previous packet merging alerts from cooperative routers. Both theoretical
marking schemes, FIT represents a step forward in modeling and simulation experimental results are reported
performance and deploys ability
here. The experiments achieved up to 95% successful
The source identification problem in the framework of detection of network anomalies along with a low 10% false
probabilistic packet marking (PPM) and present a positive alarms. The scheme cuts off malicious flows
comprehensive analysis of its properties. We show that PPM containing shrew attacks using a newly developed packetis vulnerable to spoofing of the marking field in the IP header filtering scheme. Our filtering scheme retained 99% of
by the attacker which can impede trace back by the victim. legitimate TCP flows, compared with only 20% TCP flows
The optimal decision problem the victim can choose the retained by using the Drop Tail algorithm. The paper also
marking probability and the attacker chooses the spoofed considers DSP, FPGA, and network processor implementation
marking value, source address, and attack volume can be issues and discusses limitations and further research
expressed as a constrained minimax optimization problem: the challenges.
victim selects the marking probability such that the number of
III. PROPOSED APPROACH
forgeable attack paths is minimized and the attacker chooses
A novel traceback method for DDoS attacks that is based on
the traffic volume and marking value to maximize uncertainty.
We show that the attackers ability to hide his location is entropy variations between normal and DDoS attack traffic,
curtailed by increasing the marking probability; however, the which is fundamentally different from commonly used packet
degree to which the victim can delimit the attackers injection marking techniques The results of extensive experimental and
of uncertainty is bounded by sampling constraints. In simulation studies are presented to demonstrate the
particular, the attacker, by choosing a minimal attack traffic effectiveness and efficiency of the proposed method. This
volume, can amplify the number of equally likely forged experiments show that accurate traceback is possible within 20
attack paths to, independent of the victims choice of marking seconds (approximately) in a large-scale attack network with
probability, resources must be nontrivially taxed. We show thousands of zombies.
45
International Journal on Applications in Information and Communication Engineering
Volume 2: Issue 1: January 2016, pp 43-48. www.aetsjournal.com
ISSN (Online) : 2394-6237
----------------------------------------------------------------------------------------------------------------------------- -----------------------------that are passing through the local router Ri. If v is the victim
router, then v D. Therefore, a flow at a local router can be
Advantages
It is memory non-intensive
defined as follows:
Efficiently scalable
Fij(ui,dj) = {<ui,dj,t>|uiU,dj D,i,j I} . (3.1)
Robust against packet pollution
We denote |fij(ui,dj,t)| as the count number of packets of the
Independent of attack traffic patterns.
flow fij at time t. For a given time interval T, we define the
variation of the number of packets for a given flow as follows:
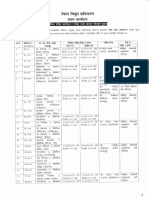
We categorize the packets that are passing through a router
Nij(ui,dj,t+ T) = |fij(ui,dj,t+ T )| - |fij(ui,dj, t)|
into flows. A flow is defined by a pair the upstream router (3.2)
where the packet came from, and the destination address of the
If we set |fij(ui,dj, t)| = 0, then Nij(ui,dj,t+ T) is the
packet. Entropy is an information theoretic concept, which is a number of packets of flow fij, which went through the local
measure of randomness. We employ entropy variation in this router during the time interval T. In order to make the
paper to measure changes of randomness of flows at a router presentation tidy, we use Nij(ui,dj ) to represent Nij(ui,dj,t+
for a given time interval. We notice that entropy variation is T) in the rest of this paper. Based on the large number
only one of the possible metrics change point of flows, to theorem, we have the probability of each flow at a local router
identify the abnormality of DDoS attacks; however, attackers as follows:
could cheat this feature by increasing attack strength slowly.
We can also employ other statistic metrics to measure the
randomness, such as standard variation or high-order moments
(3.3)
of flows. We choose entropy variation rather than others in
this paper because of the low computing workload for entropy Where pij(ui,dj) gives the probability of the flow fij
variations. First, let us have a close investigation on the flows over all the flows on the local router, and
of a router, as shown in system modeling diagram generally, a
. Let F be the
router knows its local topology.
random variable of the number of flows during the
time interval T on a local router, therefore, we
define the entropy of flows for the local router as
follows:
LAN
Rou
terK
Rou
terJ
(3.4)
In order to differentiate from the original definition
of entropy, we call H(F) as entropy variation in this
paper, which measures the variations of randomness
of flows on a given local router.
Rou
terI
Destina
tion M
Vic
tim
Flows
Destina
tion N
Fig.1 System Modeling
We name the router that we are investigating now as a local
router. In the rest of the paper, we use I as the set of positive
integers, and R as the set of real numbers. We denote a flow
on a local router by <ui; dj; t>; i; j I; t R, where ui is an
upstream router of a local router Ri, dj is the destination
address of a group of packets that are passing through the local
router Ri, and t is the current time stamp. For example, the
local router Ri in Fig. 2 has two different incoming flowsthe
ones from the upstream routers Rj and Rk, respectively. We
name this kind of flows as transit flows. Another type of
incoming flows of the local router Ri is generated at the local
area network; we call these local flows, and we use L to
represent the local flows. We name all the incoming flows as
input flows, and all the flows leaving router Ri are named as
output flows. We denote ui; i I as the immediate upstream
routers of the local router Ri, and set U as the set of incoming
flows of router Ri. Therefore, U ={ui, i I} + {L}. We use a
set D = {di, i I }to represent the destinations of the packets
Fig.2 System Architecture
46
International Journal on Applications in Information and Communication Engineering
Volume 2: Issue 1: January 2016, pp 43-48. www.aetsjournal.com
ISSN (Online) : 2394-6237
----------------------------------------------------------------------------------------------------------------------------- -----------------------------The flows with destination as the victim include legitimate theoretic concept, which is a measure of randomness. We
flows, such as f2, and a combination of attack flows and employ entropy variation to measure changes of randomness
legitimate flows, such as f1 and f3. Compared with non-attack of flows at a router for a given time interval. We notice that
cases, the volumes of some flows increase significantly in a entropy variation is only one of the possible metrics. Change
very short time period in DDoS attack cases. Observers at point of flows, to identify the abnormality of DDoS attacks.
routers R1, R3, R4, and V will notice the dramatic changes
The volumes of some flows increase significantly in a very
however, the routers who are not in the attack paths, such as short time period in DDoS attack cases at the time measure
R2, will not be able to sense the variations. Therefore, once flow variation using entropy. It is true that the network traffic
the victim realizes an ongoing attack, it can push-back to the for a router may dynamically change a lot from peak to offLANs, which caused the changes based on the information of peak service times. However, this kind of change lasts for a
flow entropy variations, and therefore, we can identify the relatively long time interval, e.g., at least at the level of
locations of attackers. The traceback can be done in a parallel minutes. If we break down these changes into seconds, the
and distributed fashion in our proposed scheme. In Fig, based change of traffic is quite smooth in our context. The number
on its knowledge of entropy variations, the victim knows that of flows for a given router is stable at both the attack cases and
attackers are somewhere behind router R1, and no attackers non attack cases. For a local router, suppose that the number
are behind router R3. Then the traceback request is delivered of flows is N, and the probability distribution is P (p1,
to router R1. Similar to the victim, router R1 knows that there p2pN).
are two groups of attackers, one group is behind the link to
C. Workload Distribution(IP Pushback Tracing)
LAN1 and another group is behind the link to LAN2. Then the
IP TraceBack algorithm used to tracing the actual source of
traceback requests are further delivered to the edge routers of
LAN1, respectively. Based on entropy variation information attacker The effectiveness and efficiency of the proposed
of router R3, the edge router of LAN1 can infer that the entropy variation based on IP traceback mechanism. Our first
attackers are located in the local area network, LAN1. task is to show that the flow entropy variation is stable for non
Similarly, the edge router of LAN2 finds that there are attack cases, and find out the fluctuations for normal
attackers in LAN1; furthermore, there are attackers behind situations; the second task is to demonstrate the relationship
router R4. The traceback request is then further passed to the between the drop of flow entropy variation and the increase of
attack strength, so that we can identify the threshold for
upstream routers, until we locate the attackers in LAN4.
identifying attack sources; we further simulate the whole
IV. METHODOLOGY
attack tree for traceback, and evaluate the total traceback time.
Following are the most frequently used project Once a DDoS attack has been confirmed by any of the existing
management methodologies in the project management DDoS detection algorithms, then the victim starts the IP
practice:
traceback algorithm the IP traceback algorithm is installed at
1. Local Flow Monitoring and Recording
routers. It is initiated by the victim, and at the upstream
2. Analyzing the Flow Variation(Using Entropy Variation)
routers, it is triggered by the IP traceback requests from the
3. Workload Distribution(IP Pushback Tracing)
victim or the downstream routers which are on the attack path.
4. Identifying and Blocking the Attack Source
The proposed algorithms are independent from the current
5. Evaluate the Total Trace Back Time
routing software; they can work as independent modules at
6. Authentication for Blocked User
routers. As a result, we do not need to change the current
routing software.
A. Local Flow Monitoring and Recording
D. Identifying and Blocking the Attack Source
The main objectives of this module is monitoring and
recording the flow of packet information. The packets that are
This module is used to identifying the attack sources and
passing through a router into flows. A flow is defined by pair also blocking source of an attack. It employs the features that
information for the upstream router where the packet came are out of the control of hackers to conduct IP traceback. We
from and the destination address of the packet. In this module,
observe and store short-term information of flow entropy
they used to monitoring the incoming packet flow and variations at routers. Once a DDoS attack has been identified
outgoing packet flow information. Recording the flow of by the victim via detection algorithms, the victim then initiates
packet information to the temporary routing table in non attack the pushback tracing procedure. The traceback algorithm first
duration time.
identifies its upstream routers where the attack flows came
from, and then submits the traceback requests to the related
B. Analyzing the Flow Variation(Using Entropy Variation)
upstream routers.
The main objectives of these modules are analyzing
This procedure continues until the most far away zombies
the flow variation for each and every packet from the are identified or when it reaches the discrimination limitation
temporary routing table. A flow is defined by a pair the of DDoS attack flows. Extensive experiments and simulations
upstream router where the packet came from and the have been conducted, and the results demonstrate that the
destination address of the packet. Entropy is an information proposed mechanism works very well in terms of
47
International Journal on Applications in Information and Communication Engineering
Volume 2: Issue 1: January 2016, pp 43-48. www.aetsjournal.com
ISSN (Online) : 2394-6237
----------------------------------------------------------------------------------------------------------------------------- -----------------------------effectiveness and efficiency. Finally identified a source require routers to inject marks into individual packets.
attacker and blocking the source attacker from the current Moreover, the PPM strategy can only operate in a local range
network access.
of the Internet (ISP network), where the defender has the
authority to manage. However, this kind of ISP networks is
E. Evaluate the Total Trace Back Time
generally quite small, and we cannot traceback to the attack
The total trace back time of identifying source of an sources located out of the ISP network. The DPM strategy
attacker. The effectiveness and efficiency of the proposed requires all the Internet routers to be updated for packet
entropy variation based on IP traceback mechanism. Our first marking. However, with only 25 spare bits available in as IP
task is to show that the flow entropy variation is stable for non packet, the scalability of DPM is a huge problem. Moreover,
attack cases, and find out the fluctuations for normal the DPM mechanism poses an extraordinary challenge on
situations; the second task is to demonstrate the relationship storage for packet logging for routers. Therefore, it is
between the drop of flow entropy variation and the increase of infeasible in practice at present. Further, both PPM and DPM
attack strength, so that we can identify the threshold for are vulnerable to hacking, which is referred to as packet
identifying attack sources; we further simulate the whole pollution.
attack tree for traceback, and evaluate the total traceback time
VI. FUTURE WORK
Consequently, in order to evaluate our scheme, we have
carefully conducted extensive simulations and real case
The proposed method deals with the packet flooding type of
observations. The simulation settings are arranged according. attacks perfectly. However, for the attacks with small number
We set the attack tree as a binary tree or three-branch tree, attack packet rates, e.g., if the attack strength is less than seven
respectively, and zombies are distributed in the attack tree times of the strength of non-attack flows, then the current
uniformly. We note that, our entropy variation traceback metric cannot discriminate it. Therefore, a metric of finer
mechanism is independent from the topology of attack granularity is required to deal with such situations. Second one
network and it is also independent from the network topology is Location estimation of attackers with partial information.
of victims, such as, 5-10 minutes attack duration, 10,000 When the attack strength is less than seven times of the normal
packets per second of attack flows.
flow packet rate, the proposed method cannot succeed at the
The performance evaluation included two parts the first one moment. However, we can detect the attack with the
focused on the entropy variation monitoring at a local router; information that we have accumulated so far using traditional
and the second part was to demonstrate the effectiveness of methods, e.g., the hidden Markov chain model, or recently
DDoS attacker traceback and the overall traceback time. developed tools, e.g., the network tomography.
Conducted two simulations for this purpose: we make the
REFERENCES
mean of flows as 100 packets per time unit, and the standard
variations (std) of the flows are 25 and 50, respectively. We [1] Al-Duwairi and Govindarasu(May 2006), Novel Hybrid Schemes
Employing Packet Marking and Logging for IP Traceback, IEEE Trans.
observe the changes of the entropy variation against the
Parallel and Distributed Systems, vol. 17, no. 5, pp. 403-418.
number of flows. The results are shown in Fig. 10. It indicates [2] Aljifri (May/June2003) IP Traceback: A New Denial-of-Service
Deterrent? IEEE Security & Privacy, vol. 1, no. 3, pp. 24-31.
that the standard variation of the entropy variation is quite
and Ansari (Apr 2003) IP Traceback with Deterministic
stable (the fluctuation is around 1-3 percent), even when the [3] Belenky
Packet Marking, IEEE Comm. Letters, vol. 7, no. 4, pp. 162-164.
fluctuations of the flows are quite big, 25% and 50%, [4] Gao and Ansari (May 2005), Tracing Cyber Attacks from the Practical
Perspective, IEEE Comm. Letters, vol. 43, no. 5, pp. 123-131.
respectively. Moreover, the standard variation of entropy
[5] Moore et al(May 2006) Inferring Internet Denial-of-Service
variation decreases when the number of flows increases.
[6]
F. Authentication for Blocked User
In this module the user is blocked for some reason by
Administrator. So the user sends request to authenticate the
network like earlier periods and user request to know the
blocked reason from admin at the same time. Administrator
need to identify whether the authenticate user with the help of
starting time key. If the user gave that key to administrator.
Then Administrator identify that key if the is correct user get
the authentication from administrator. Here after the user
thought access his system with the help of that key only.
[7]
[8]
V. CONCLUSION
A number of IP traceback approaches have been suggested
to identify attackers and there are two major methods for IP
traceback, the probabilistic packet marking (PPM) and the
deterministic packet marking (DPM) Both of these strategies
48
Activity,.ACM Trans. Computer Systems, vol. 24, no. 2, pp. 115-139.
Mirkovic et al., (June 2009) Accurately Measuring Denial of Service in
Simulation and Testbed Experiments, IEEE Trans. Dependable and
Secure Computing, vol. 6, no. 2, pp. 81-95, Apr.
Mirkovic et al., (Aug. 2008)Testing a CollaborativeDDoS Defense in a
Red/Blue Team Exercise, IEEE Trans. Computers, vol. 57, no. 8, pp.
1098-1112
Park and Lee (2001), On the Effectiveness of Probabilistic Packet
Marking for IP Traceback under Denial of Service Attack, Proc IEEE
INFOCOMM
Potrebbero piacerti anche
- Prolog 10 MQuestions R1Documento7 pagineProlog 10 MQuestions R1pramodNessuna valutazione finora
- The Google File SystemDocumento15 pagineThe Google File SystemEddie Awad100% (18)
- Discriminating Ddos Attacks From Flash Crowds Using Flow Correlation CoefficientDocumento8 pagineDiscriminating Ddos Attacks From Flash Crowds Using Flow Correlation CoefficientpramodNessuna valutazione finora
- G) KFN LJB"T/ K - FLWS/) F: K - Ydkq / Låtlokqsf) Kf&/Oqmd LJJ/) FDocumento3 pagineG) KFN LJB"T/ K - FLWS/) F: K - Ydkq / Låtlokqsf) Kf&/Oqmd LJJ/) FpramodNessuna valutazione finora
- Iqrf, Flqfoq: FDQD VQNDocumento4 pagineIqrf, Flqfoq: FDQD VQNpramodNessuna valutazione finora
- Reliable Determination of Zombies Based On Entropy VariationDocumento4 pagineReliable Determination of Zombies Based On Entropy VariationJournal of Computer ApplicationsNessuna valutazione finora
- Discriminating Ddos Attacks From Flash Crowds Using Flow Correlation CoefficientDocumento8 pagineDiscriminating Ddos Attacks From Flash Crowds Using Flow Correlation CoefficientpramodNessuna valutazione finora
- Communication Systems Ii - LabmanualDocumento12 pagineCommunication Systems Ii - LabmanualpramodNessuna valutazione finora
- Filter Design: Lab ManualDocumento9 pagineFilter Design: Lab ManualpramodNessuna valutazione finora
- Filter Design: Lab ManualDocumento9 pagineFilter Design: Lab ManualpramodNessuna valutazione finora
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (400)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (266)
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (588)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (121)
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- Earthing Transformer and Its Application To The Power SystemDocumento34 pagineEarthing Transformer and Its Application To The Power SystemRathinaKumar100% (1)
- Drawing Free-Body DiagramsDocumento5 pagineDrawing Free-Body DiagramsMahamadali DesaiNessuna valutazione finora
- Introduction To PSpice PDFDocumento7 pagineIntroduction To PSpice PDFEduardo FernándezNessuna valutazione finora
- Absorption of Gamma RaysDocumento9 pagineAbsorption of Gamma RaysRachit KanchanNessuna valutazione finora
- Q4 - WEEK 2 - MEASURES OF POSITION For GROUPED DATADocumento16 pagineQ4 - WEEK 2 - MEASURES OF POSITION For GROUPED DATAEllaineeeeNessuna valutazione finora
- Communication Engineering 2 MarksDocumento38 pagineCommunication Engineering 2 MarksNandhini100% (2)
- Module01 - AHPDocumento18 pagineModule01 - AHPmia100% (1)
- Physics Lab ReportDocumento3 paginePhysics Lab ReportReysa Gabrielle PileNessuna valutazione finora
- Mongo DB Basic CommandsDocumento15 pagineMongo DB Basic CommandsgauriNessuna valutazione finora
- AC 23-8B Flight Test Guide App 1Documento22 pagineAC 23-8B Flight Test Guide App 1Ladislao PazmanyNessuna valutazione finora
- Chapter 1-Thermodynamic-Merged-CompressedDocumento60 pagineChapter 1-Thermodynamic-Merged-CompressedAina SyafiqahNessuna valutazione finora
- Liquid Solutions: Physical Chemistry by Prince SirDocumento14 pagineLiquid Solutions: Physical Chemistry by Prince SirSunnyNessuna valutazione finora
- Tutorial Summary: 3D Example: Magneto Thermal ApplicationDocumento3 pagineTutorial Summary: 3D Example: Magneto Thermal ApplicationAndrewNessuna valutazione finora
- Choking vs. Clutch Performance: A Study of Sport Performance Under PressureDocumento19 pagineChoking vs. Clutch Performance: A Study of Sport Performance Under Pressuremensrea0Nessuna valutazione finora
- Paper Test For General PhysicsDocumento2 paginePaper Test For General PhysicsJerrySemuelNessuna valutazione finora
- Roll Forging.Documento36 pagineRoll Forging.jaydee420Nessuna valutazione finora
- Schuetz Et Al., 2013Documento6 pagineSchuetz Et Al., 2013IrisCoraymaGuevaraSilvaNessuna valutazione finora
- Neural-Network-Based Maximum Power Point Tracking Methods For Photovoltaic Systems Operating Under Fast Changing EnvironmentsDocumento12 pagineNeural-Network-Based Maximum Power Point Tracking Methods For Photovoltaic Systems Operating Under Fast Changing EnvironmentsAbderrezak BadjiNessuna valutazione finora
- Advantage of Oil CoolingDocumento2 pagineAdvantage of Oil CoolingYin ThoNessuna valutazione finora
- Tutorial 4 JawapanDocumento6 pagineTutorial 4 JawapanlimNessuna valutazione finora
- Principle of StatisticsDocumento6 paginePrinciple of StatisticsMd Tarekul IslamNessuna valutazione finora
- Introduction To Fission and FusionDocumento19 pagineIntroduction To Fission and FusionZubair Hassan100% (1)
- The Best Itext Questions On StackoverflowDocumento361 pagineThe Best Itext Questions On Stackoverflowadaf8850% (2)
- The Chemistry Maths Book: Erich SteinerDocumento16 pagineThe Chemistry Maths Book: Erich SteinerDewi MariyamNessuna valutazione finora
- 9.coordination CompoundsDocumento46 pagine9.coordination CompoundsSeenu MNessuna valutazione finora
- Lab Report Welding (SMAW) - FizaDocumento13 pagineLab Report Welding (SMAW) - FizaCheng Yee71% (7)
- UMTS TutorialDocumento84 pagineUMTS Tutorialnale_2100% (1)
- The Chemistry of Copper: Number 83 WWW - Curriculum-Press - Co.ukDocumento5 pagineThe Chemistry of Copper: Number 83 WWW - Curriculum-Press - Co.uks7076728g100% (1)
- AI CalculatorDocumento41 pagineAI CalculatorAneeza zafarNessuna valutazione finora
- Surgical Sutures: Suture SizeDocumento7 pagineSurgical Sutures: Suture SizeMei PayumoNessuna valutazione finora