Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Rr410504 Network Security and Cryptography
Caricato da
andhracollegesDescrizione originale:
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Rr410504 Network Security and Cryptography
Caricato da
andhracollegesCopyright:
Formati disponibili
www.andhracolleges.
com The Complete Information About Colleges in Andhra Pradesh
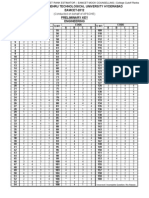
Code No: RR410504 Set No. 1
IV B.Tech I Semester Regular Examinations, November 2007
NETWORK SECURITY AND CRYPTOGRAPHY
(Computer Science & Engineering)
Time: 3 hours Max Marks: 80
Answer any FIVE Questions
All Questions carry equal marks
⋆⋆⋆⋆⋆
www.andhracolleges.com
1. (a) What is it importance to study the Feistel cipher?
(b) Which parameters and design choices determine the actual algorithm of a
Feistel cipher?
2. Explain the process of encryption and decryption in IDEA algorithm.
3. List four general categories of schemes for distribution of public keys.
4. (a) Explain Chinese Remainder Theorem.
(b) State and prove Euler’s theorem?
[8]
[8]
[16]
[16]
(c) Using Fermat’s theorem, find 201 mod 11. [5+5+6]
5. (a) List requirements for a Hash Function.
(b) What basic arithmetical and logical functions are used in SHA-1? [6+10]
6. (a) What is R64 conversion?
(b) Why is R64 conversion useful for an e-mail application?
www.andhracolleges.com
(c) Why is the segmentation and reassembly function in PGP needed? [4+6+6]
7. (a) Give examples of applications of IPSec.
(b) What services does IPSec provide? [8+8]
8. Write notes on
(a) Viruses
(b) Worms
(c) Bacteria [6+6+4]
⋆⋆⋆⋆⋆
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
1 ofUSA-UK-Australia-Germany-France-NewZealand
1 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR410504 Set No. 2
IV B.Tech I Semester Regular Examinations, November 2007
NETWORK SECURITY AND CRYPTOGRAPHY
(Computer Science & Engineering)
Time: 3 hours Max Marks: 80
Answer any FIVE Questions
All Questions carry equal marks
⋆⋆⋆⋆⋆
www.andhracolleges.com
1. (a) What are differences between a block cipher and a stream cipher?
(b) Explain various modes of operations of block ciphers.
2. Explain the process of encryption and decryption in IDEA algorithm.
3. (a) Explain public key Crypto Systems.
(b) Explain in detail about Euclid’s Algorithm.
(c) Give a brief account on Random number Generation.
[8]
[8]
[16]
[6]
[5]
[5]
4. (a) Explain in detail about Euclid’s Algorithm.
(b) Determine gcd(1970,1066). [8+8]
5. (a) What is a difference between little-endian and big-endian format?
(b) What basic arithmetical and logical functions are used in MD5? [6+10]
6. (a) What is R64 conversion?
(b) Why is R64 conversion useful for an e-mail application?
www.andhracolleges.com
(c) Why is the segmentation and reassembly function in PGP needed? [4+6+6]
7. Write note on Encapsulating security payload. [16]
8. (a) what information used by a typical packet-filtering router?
(b) What are some weaknesses of a packet-filtering router?
(c) What is the difference between a packet-filtering router and a stateful inspec-
tion firewall? [8+4+4]
⋆⋆⋆⋆⋆
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
1 ofUSA-UK-Australia-Germany-France-NewZealand
1 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR410504 Set No. 3
IV B.Tech I Semester Regular Examinations, November 2007
NETWORK SECURITY AND CRYPTOGRAPHY
(Computer Science & Engineering)
Time: 3 hours Max Marks: 80
Answer any FIVE Questions
All Questions carry equal marks
⋆⋆⋆⋆⋆
www.andhracolleges.com
1. (a) What is it importance to study the Feistel cipher?
(b) What is the purpose of the S-boxes in DES?
2. (a) List the characteristics of advanced block ciphers.
(b) What are the differences between RC5 and RC2?
3. (a) Explain Diffie-Hellman Key Exchange in Elliptic curve cryptography?
(b) Explain the process encryption and decryption in Elliptic curve cryptography?
[8+8]
[10]
[6]
[8]
[8]
4. (a) Explain Miller-Robin test algorithm.
(b) Explain Chinese Remainder Theorem . [8+8]
5. (a) What is the difference between weak and strong collision resistance?
(b) What is the role of a compression function in a hash function? [6+10]
6. (a) What is R64 conversion?
www.andhracolleges.com
(b) Why is R64 conversion useful for an e-mail application?
(c) Why is the segmentation and reassembly function in PGP needed? [4+6+6]
7. Write note on Encapsulating security payload. [16]
8. Write notes on
(a) Trapdoors
(b) Logic bomb
(c) Trojan horses [5+5+6]
⋆⋆⋆⋆⋆
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
1 ofUSA-UK-Australia-Germany-France-NewZealand
1 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR410504 Set No. 4
IV B.Tech I Semester Regular Examinations, November 2007
NETWORK SECURITY AND CRYPTOGRAPHY
(Computer Science & Engineering)
Time: 3 hours Max Marks: 80
Answer any FIVE Questions
All Questions carry equal marks
⋆⋆⋆⋆⋆
www.andhracolleges.com
1. This problem provides a numerical example of encryption using a one-round version
of DES. We start with the same bit pattern for the key and plain text, namely,
In hexadecimal notation 0 1 2 3 4 5 6 7 8 9 A B C D E F
Inbinary notation: 0000 0001 0010 0011 0100 0101 0110 0111
1000 1001 1010 1011 1100 1101 1110 1111
(a) Derive K1 , the first - round subkey.
(b) Derive L0 , R0
(c) Expand R0 to get E[R0 ]
(d) Calculate A=E[R0 ] ⊕ K1 .
(e) Group the 48-bit result of (d) into sets of 6 bits and evaluate the corresponding
S-box substitutions.
(f) Cancatenate the results of (e) to get a 32-bit result,B.
(g) Apply the permutation to get P(B).
(h) Calculate R1=P(B) ⊕ L0
www.andhracolleges.com
(i) write down the cipher text. [16]
2. (a) List the characteristics of advanced block ciphers. [8]
(b) What are the differences between RC5 and RC2? [8]
3. (a) What is an Elliptic Curve? [4]
(b) What is the Zero point of an elliptic curve? [2]
(c) Explain the process encryption and decryption in Elliptic curve Cryptography?
[10]
4. (a) Define a Groups, a Rings and a Fields?
(b) Construct Additive table and Multiplicative table for GF(7)? [6+10]
5. Define digital Signature. Explain its role in network security. [16]
6. (a) What is R64 conversion?
(b) Why is R64 conversion useful for an e-mail application?
(c) Why is the segmentation and reassembly function in PGP needed? [4+6+6]
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
1 ofUSA-UK-Australia-Germany-France-NewZealand
2 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR410504 Set No. 4
7. (a) List and briefly define the business requirements for secure payment processing
with credit cards over the Internet.
(b) List and briefly define the principal categories of SET participants. [8+8]
8. Write notes on
(a) Viruses
www.andhracolleges.com
(b) Worms
(c) Bacteria [6+6+4]
⋆⋆⋆⋆⋆
www.andhracolleges.com
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
2 ofUSA-UK-Australia-Germany-France-NewZealand
2 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
Potrebbero piacerti anche
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- Eamcet 2014 Medical Question Paper With Key Solutions AndhracollegesDocumento62 pagineEamcet 2014 Medical Question Paper With Key Solutions Andhracollegesandhracolleges100% (1)
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- EAMCET 2014 Agriculture & Medical Preliminary Answer KeysDocumento1 paginaEAMCET 2014 Agriculture & Medical Preliminary Answer KeysLohith_EnggNessuna valutazione finora
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- Eamcet Agriculture Last Ranks Cutoffs Andhracolleges Eamcet 2013 CutoffsDocumento3 pagineEamcet Agriculture Last Ranks Cutoffs Andhracolleges Eamcet 2013 Cutoffsandhracolleges33% (3)
- Polycet 2014 Question PaperDocumento24 paginePolycet 2014 Question PaperandhracollegesNessuna valutazione finora
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (400)
- Andhracollege Eamcet 2014 Engineering Question Paper With Key SolutionsDocumento62 pagineAndhracollege Eamcet 2014 Engineering Question Paper With Key Solutionsandhracolleges50% (4)
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (588)
- Eamcet 2014 Engineering Key Solutions AndhracollegesDocumento42 pagineEamcet 2014 Engineering Key Solutions Andhracollegesandhracolleges75% (8)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- Eamcet 2014 Engineering Key SolutionsDocumento42 pagineEamcet 2014 Engineering Key Solutionsandhracolleges100% (1)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- Eamcet 2004 Engineering PaperDocumento12 pagineEamcet 2004 Engineering PaperandhracollegesNessuna valutazione finora
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (895)
- Eamcet 2012 Engineering Paper KeyDocumento1 paginaEamcet 2012 Engineering Paper KeyandhracollegesNessuna valutazione finora
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- Eamcet 2006 Engineering PaperDocumento14 pagineEamcet 2006 Engineering PaperandhracollegesNessuna valutazione finora
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- Eamcet 2003 Engineering PaperDocumento12 pagineEamcet 2003 Engineering Paperandhracolleges100% (1)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- Eamcet 2007 Engineering PaperDocumento13 pagineEamcet 2007 Engineering Paperandhracolleges100% (1)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (266)
- Eamcet 2010 Medical PaperDocumento63 pagineEamcet 2010 Medical PaperandhracollegesNessuna valutazione finora
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (74)
- Eamcet 2002 Engineering PaperDocumento14 pagineEamcet 2002 Engineering Paperandhracolleges0% (1)
- Icet-2014-Important Instructions BookletDocumento3 pagineIcet-2014-Important Instructions BookletandhracollegesNessuna valutazione finora
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- Eamcet 2009 Engineering Physics PaperDocumento19 pagineEamcet 2009 Engineering Physics PaperandhracollegesNessuna valutazione finora
- EAMCET Engineering Entrance Solved Paper 2000Documento13 pagineEAMCET Engineering Entrance Solved Paper 2000Giri NathNessuna valutazione finora
- Eamcet 2001 Engineering PaperDocumento14 pagineEamcet 2001 Engineering PaperandhracollegesNessuna valutazione finora
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (345)
- Eamcet Pharmacy College Fee DetailsDocumento14 pagineEamcet Pharmacy College Fee DetailsandhracollegesNessuna valutazione finora
- TS ICET Syllabus and Exam PatternDocumento5 pagineTS ICET Syllabus and Exam PatterngayathriNessuna valutazione finora
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2259)
- FeeDocumento34 pagineFeeThanniru VenkateshNessuna valutazione finora
- EAMCET NotificationDocumento3 pagineEAMCET NotificationKeerthiPratheek ReddyNessuna valutazione finora
- Andrew ResumeDocumento4 pagineAndrew ResumeAnonymous blqN8zpfNessuna valutazione finora
- 1.3.1.3 SkillsIntegrationChallenge SGDocumento4 pagine1.3.1.3 SkillsIntegrationChallenge SGStefanny GavilemaNessuna valutazione finora
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- Chapter 6 Tools of Structured AnalysisDocumento47 pagineChapter 6 Tools of Structured AnalysisHarpreet RaiNessuna valutazione finora
- OpenBIM Focus Issue1Documento9 pagineOpenBIM Focus Issue1moderntalking87Nessuna valutazione finora
- Interview Questions For QA TesterDocumento27 pagineInterview Questions For QA TesterSadan KumarNessuna valutazione finora
- Vinay Karthik B S - ResumeDocumento3 pagineVinay Karthik B S - ResumeVinayKarthikBSNessuna valutazione finora
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (121)
- Chapter 8 - StudDocumento49 pagineChapter 8 - StudAshrafD.ZulkeflyNessuna valutazione finora
- Daily Time Record Daily Time RecordDocumento2 pagineDaily Time Record Daily Time RecordJasmine Rose Cole CamosNessuna valutazione finora
- DSS Clearing and Sanitization MatrixDocumento4 pagineDSS Clearing and Sanitization MatrixHomerKhanNessuna valutazione finora
- Game Server Development in Node - JS: Charlie Crane @xieccDocumento44 pagineGame Server Development in Node - JS: Charlie Crane @xieccVu NguyenNessuna valutazione finora
- UT Dallas Syllabus For cs7301.002.07s Taught by Kevin Hamlen (kxh060100)Documento11 pagineUT Dallas Syllabus For cs7301.002.07s Taught by Kevin Hamlen (kxh060100)UT Dallas Provost's Technology GroupNessuna valutazione finora
- Dnsreport Idat - Edu.peDocumento5 pagineDnsreport Idat - Edu.pejuan992276377Nessuna valutazione finora
- Kongsberg K-Pos Auto Track Mode Operator ManualDocumento122 pagineKongsberg K-Pos Auto Track Mode Operator ManualZhiyong Shan100% (1)
- Intro To Arduino: Zero To Prototyping in A Flash!Documento93 pagineIntro To Arduino: Zero To Prototyping in A Flash!Najem IslamNessuna valutazione finora
- Introduction To 8086 MicroprocessorDocumento13 pagineIntroduction To 8086 MicroprocessorVijay Arunagiri ANessuna valutazione finora
- All Cs Midterm Important TopicDocumento15 pagineAll Cs Midterm Important TopicAtif MubasharNessuna valutazione finora
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- Design of Experiments: A 360 Development ApproachDocumento24 pagineDesign of Experiments: A 360 Development ApproachAbhijit More100% (1)
- Department of Computer Science: Notes On Interprocess Communication in UnixDocumento11 pagineDepartment of Computer Science: Notes On Interprocess Communication in UnixkartikNessuna valutazione finora
- BA IntroDocumento23 pagineBA Introudayraj_vNessuna valutazione finora
- Microprocessors Piplining SlidesDocumento38 pagineMicroprocessors Piplining SlidesHamza HassanNessuna valutazione finora
- Major Project Report FormatDocumento4 pagineMajor Project Report FormatarunkaranNessuna valutazione finora
- Managing Supply Chain Risks: Emerging Trends & TechnologiesDocumento30 pagineManaging Supply Chain Risks: Emerging Trends & Technologiespradeep100% (1)
- 08 - Memory ManagementDocumento36 pagine08 - Memory ManagementShunyi LiuNessuna valutazione finora
- Parallelized RSA On Multicore CPUs and GPUDocumento21 pagineParallelized RSA On Multicore CPUs and GPUkennedy beyanNessuna valutazione finora
- 151 Implicit Differentiation Second DerivativesDocumento7 pagine151 Implicit Differentiation Second DerivativesEsa KhanNessuna valutazione finora
- 6.10-Tutorial For Week6Documento17 pagine6.10-Tutorial For Week6Sikappi SubbuNessuna valutazione finora
- Class IX Final TermDocumento4 pagineClass IX Final TermSonam BaghaNessuna valutazione finora
- CFD Modeling of A Gas Cyclone D T: Technical University Sofia, BulgariaDocumento2 pagineCFD Modeling of A Gas Cyclone D T: Technical University Sofia, BulgariaBarny GomesNessuna valutazione finora
- C Bodi 20Documento41 pagineC Bodi 20Azfar RazaNessuna valutazione finora
- Excel Essentials: A Step-by-Step Guide with Pictures for Absolute Beginners to Master the Basics and Start Using Excel with ConfidenceDa EverandExcel Essentials: A Step-by-Step Guide with Pictures for Absolute Beginners to Master the Basics and Start Using Excel with ConfidenceNessuna valutazione finora
- Clean Code: A Handbook of Agile Software CraftsmanshipDa EverandClean Code: A Handbook of Agile Software CraftsmanshipValutazione: 5 su 5 stelle5/5 (13)