Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Scalable and Secure Sharing of Personal Health Records in Cloud Computing Using Attribute-Based Encryption
Caricato da
Editor IJRITCCTitolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Scalable and Secure Sharing of Personal Health Records in Cloud Computing Using Attribute-Based Encryption
Caricato da
Editor IJRITCCCopyright:
Formati disponibili
International Journal on Recent and Innovation Trends in Computing and Communication
ISSN 2321 8169
679 681
Volume: 1 Issue: 8
________________________________________________________________________________
Scalable and Secure Sharing of Personal Health Records in Cloud Computing using
Attribute-based Encryption
Ch.Padmini 1, Sk.Salamuddin 2, S.Suresh Babu3
Asst.Professor1, 2, 3, Vignan University
ABSTRACT:
Personal health record (PHR) is an emerging patient-centric model of health information exchange, which is often outsourced to be stored at
a third party, such as cloud providers. However, there have been wide privacy concerns as personal health information could be exposed to
those third party servers and to unauthorized parties. To assure the patients control over access to their own PHRs, it is a promising
method to encrypt the PHRs before outsourcing. Yet, issues such as risks of privacy exposure, scalability in key management, flexible access
and efficient user revocation, have remained the most important challenges toward achieving fine-grained, cryptographically enforced data
access control. In this paper, we propose a novel patient-centric framework and a suite of mechanisms for data access control to PHRs
stored in semi-trusted servers. To achieve fine-grained and scalable data access control for PHRs, we leverage attribute based encryption
(ABE) techniques to encrypt each patients PHR file. Different from previous works in secure data outsourcing, we focus on the multiple
data owner scenario, and divide the users in the PHR system into multiple security domains that greatly reduces the key management
complexity for owners and users. A high degree of patient privacy is guaranteed simultaneously by exploiting multi-authority ABE. Our
scheme also enables dynamic modification of access policies or file attributes, supports efficient on-demand user/attribute revocation and
break-glass access under emergency scenarios. Extensive analytical and experimental results are presented which show the security,
scalability and efficiency of our proposed scheme.
_______________________________________________________*****____________________________________________________________
Health Vault. While it is exciting to have convenient PHR
ARCHITECTURE:
services for everyone, there are many security and privacy
risks. Which could impede its wide adoption. The main
concern is about whether the patients could actually control
the sharing of their sensitive personal health information
(PHI), especially when they are stored on a third-party server
which people may not fully trust.
DISADVANTAGES OF EXISTING SYSTEM:
There have been wide privacy concerns as personal health
information could be exposed to those third party servers and
to unauthorized parties.
Department of Veterans Affairs database containing sensitive
EXISTING SYSTEM:
PHI of 26.5 million military veterans, including their social
Due to the high cost of building and maintaining specialized
security numbers and health problems was stolen by an
data centers, many PHR services are outsourced to or provided
employee who took the data home without authorization.
by third-party service providers, for example, Microsoft
679
IJRITCC | AUG 2013, Available @ http://www.ijritcc.org
________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
ISSN 2321 8169
679 681
Volume: 1 Issue: 8
________________________________________________________________________________
They usually assume the use of a single trusted authority (TA)
multi-domain, multi-authority PHR system with many users.
in the system. This not only may create a load bottleneck, but
The framework captures application level requirements of
also suffers from the key escrow problem since the TA can
both public and personal use of a patients PHRs, and
access all the encrypted files, opening the door for potential
distributes users trust to multiple authorities that better
privacy exposure. In addition, it is not practical to delegate all
reflects reality.
attribute management tasks to one TA, including certifying all
users attributes or roles and generating secret keys.
PHR Owner Module:
The main goal of our framework is to provide secure patient-
PROPOSED SYSTEM:
centric PHR access and efficient key management at the same
To assure the patients control over access to their own PHRs,
time. The key idea is to divide the system into multiple
it is a promising method to encrypt the PHRs before
security domains (namely, public domains (PUDs) and
outsourcing. In this paper, we propose a novel patient-centric
personal domains (PSDs)) according to the different users
framework and a suite of mechanisms for data access control
data access requirements. The PUDs consist of users who
to PHRs stored in semi-trusted servers. To achieve fine-
make access based on their professional roles, such as doctors,
grained and scalable data access control for PHRs, we
nurses and medical researchers. In practice, a PUD can be
leverage attribute based encryption (ABE) techniques to
mapped to an independent sector in the society, such as the
encrypt each patients PHR file.
health care, government or insurance sector. For each PSD, its
users are personally associated with a data owner (such as
family members or close friends), and they make accesses to
To ensure patient-centric privacy control over their own
PHRs based on access rights assigned by the owner.
PHRs, it is essential to have fine-grained data access control
mechanisms that work with semi-trusted servers.
Each data owner (e.g., patient) is a trusted authority of her
In order to protect the personal health data stored on a semi-
own PSD, who uses a KP-ABE system to manage the secret
trusted server, we adopt attribute-based encryption (ABE) as
keys and access rights of users in her PSD. Since the users are
the main encryption primitive. Using ABE, access policies are
personally known by the PHR owner, to realize patient-centric
expressed based on the attributes of users or data, which
access, the owner is at the best position to grant user access
enables a patient to selectively share her PHR among a set of
privileges on a case-by-case basis. For PSD, data attributes
users by encrypting the file under a set of attributes, without
are defined which refer to the intrinsic properties of the PHR
the need to know a complete list of users.
data, such as the category of a PHR file. For the purpose of
PSD access, each PHR file is labeled with its data attributes,
ADVANTAGES OF PROPOSED SYSTEM:
while the key size is only linear with the number of file
We focus on the multiple data owner scenario, and divide the
categories a user can access. Since the number of users in a
users in the PHR system into multiple security domains that
PSD is often small, it reduces the burden for the owner. When
greatly reduces the key management complexity for owners
encrypting the data for PSD, all that the owner needs to know
and users.
is the intrinsic data properties.
In this paper, we bridge the above gaps by proposing a unified
security framework for patient-centric sharing of PHRs in a
680
IJRITCC | AUG 2013, Available @ http://www.ijritcc.org
________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
ISSN 2321 8169
679 681
Volume: 1 Issue: 8
________________________________________________________________________________
Cloud Server Module:
In this paper, we consider the server to be semi-trusted, i.e.,
REFERENCE:
honest but curious as those in [28] and [15]. That means the
Ming Li, Shucheng Yu, Yao Zheng, Kui Ren, and Wenjing
server will try to find out as much secret information in the
Lou, Scalable and Secure Sharing of Personal Health Records
stored PHR files as possible, but they will honestly follow the
in Cloud Computing using Attribute-based Encryption IEEE
protocol in general. On the other hand, some users will also try
TRANSACTIONS ON PARALLEL AND DISTRIBUTED
to access the files beyond their privileges. For example, a
SYSTEMS.
pharmacy may want to obtain the prescriptions of patients for
marketing and boosting its profits. To do so, they may collude
with other users, or even with the server. In addition, we
assume each party in our system is preloaded with a
public/private key pair, and entity authentication can be done
by traditional challenge-response protocols.
ABOUT THE AUTHORS:
Ch. Padmini working as Asst.Professor,
Dept of Information Technology in Vignan
University, Guntur. She has vast
experience in research work.
Attribute based Access Policy Module:
In our framework, there are multiple SDs, multiple owners,
multiple AAs, and multiple users. In addition, two ABE
systems are involved. We term the users having read and write
access as data readers and contributors, respectively.
Sk.Salamuddin working as Asst.Professor,
Dept of Information Technology in Vignan
University, Guntur. He has vast experience
in research work.
S. Suresh Babu working as Asst.Professor,
Dept of Information Technology in Vignan
University, Guntur. He has vast experience
in research work.
Data confidentiality Module
The owners upload ABE-encrypted PHR files to the server.
Each owners PHR file is encrypted both under a certain fine
grained and role-based access policy for users from the PUD
to access, and under a selected set of data attributes that allows
access from users in the PSD. Only authorized users can
decrypt the PHR files, excluding the server.
681
IJRITCC | AUG 2013, Available @ http://www.ijritcc.org
________________________________________________________________________________
Potrebbero piacerti anche
- Channel Estimation Techniques Over MIMO-OFDM SystemDocumento4 pagineChannel Estimation Techniques Over MIMO-OFDM SystemEditor IJRITCCNessuna valutazione finora
- Importance of Similarity Measures in Effective Web Information RetrievalDocumento5 pagineImportance of Similarity Measures in Effective Web Information RetrievalEditor IJRITCCNessuna valutazione finora
- A Review of 2D &3D Image Steganography TechniquesDocumento5 pagineA Review of 2D &3D Image Steganography TechniquesEditor IJRITCCNessuna valutazione finora
- Prediction of Crop Yield Using LS-SVMDocumento3 paginePrediction of Crop Yield Using LS-SVMEditor IJRITCCNessuna valutazione finora
- A Study of Focused Web Crawling TechniquesDocumento4 pagineA Study of Focused Web Crawling TechniquesEditor IJRITCCNessuna valutazione finora
- Diagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmDocumento5 pagineDiagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmEditor IJRITCCNessuna valutazione finora
- Predictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth KotianDocumento3 paginePredictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth Kotianrahul sharmaNessuna valutazione finora
- 44 1530697679 - 04-07-2018 PDFDocumento3 pagine44 1530697679 - 04-07-2018 PDFrahul sharmaNessuna valutazione finora
- 45 1530697786 - 04-07-2018 PDFDocumento5 pagine45 1530697786 - 04-07-2018 PDFrahul sharmaNessuna valutazione finora
- Hybrid Algorithm For Enhanced Watermark Security With Robust DetectionDocumento5 pagineHybrid Algorithm For Enhanced Watermark Security With Robust Detectionrahul sharmaNessuna valutazione finora
- Safeguarding Data Privacy by Placing Multi-Level Access RestrictionsDocumento3 pagineSafeguarding Data Privacy by Placing Multi-Level Access Restrictionsrahul sharmaNessuna valutazione finora
- Itimer: Count On Your TimeDocumento4 pagineItimer: Count On Your Timerahul sharmaNessuna valutazione finora
- 41 1530347319 - 30-06-2018 PDFDocumento9 pagine41 1530347319 - 30-06-2018 PDFrahul sharmaNessuna valutazione finora
- 49 1530872658 - 06-07-2018 PDFDocumento6 pagine49 1530872658 - 06-07-2018 PDFrahul sharmaNessuna valutazione finora
- Paper On Design and Analysis of Wheel Set Assembly & Disassembly Hydraulic Press MachineDocumento4 paginePaper On Design and Analysis of Wheel Set Assembly & Disassembly Hydraulic Press MachineEditor IJRITCCNessuna valutazione finora
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (400)
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (588)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
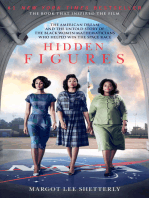
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (895)
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (266)
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (74)
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (121)
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- Group2 FreshippoDocumento13 pagineGroup2 FreshippoSHREEGURO SHRESHTINessuna valutazione finora
- Android SDK 4.x For Experience Cloud SolutionsDocumento127 pagineAndroid SDK 4.x For Experience Cloud SolutionsPrimrose HoangNessuna valutazione finora
- Modernize Your SaaS Enterprise With AWSDocumento33 pagineModernize Your SaaS Enterprise With AWSBragadish ANessuna valutazione finora
- Vmware ConceptsDocumento3 pagineVmware Conceptsrajeshk8Nessuna valutazione finora
- Digital Banking and Alternative SystemsDocumento31 pagineDigital Banking and Alternative SystemsRameen ZafarNessuna valutazione finora
- GCC-2 Marks PDFDocumento14 pagineGCC-2 Marks PDFSuman PawarNessuna valutazione finora
- Gartner Magic Quadrant For Analytics and Business IntelligenceDocumento50 pagineGartner Magic Quadrant For Analytics and Business IntelligencePaulo CesarNessuna valutazione finora
- Web Application Proxy and ADFS On The AWS CloudDocumento31 pagineWeb Application Proxy and ADFS On The AWS Cloudnearurheart1Nessuna valutazione finora
- List of Accepted Papers Iceeccot-2018: Session 1: Image Processing Date: 14th Dec 2018Documento32 pagineList of Accepted Papers Iceeccot-2018: Session 1: Image Processing Date: 14th Dec 2018Suhas ShirolNessuna valutazione finora
- App ServiceDocumento13 pagineApp ServiceParminder Singh KaileyNessuna valutazione finora
- CUCM 11.5 To 12.5 Upgrade Guide (FLEX)Documento10 pagineCUCM 11.5 To 12.5 Upgrade Guide (FLEX)Sid Ali Oulad SmaneNessuna valutazione finora
- #1 Kindle Technology Book Available in Paperback To Expand Market ReachDocumento2 pagine#1 Kindle Technology Book Available in Paperback To Expand Market ReachPR.comNessuna valutazione finora
- ERM Final Paper Prashant Singh PDFDocumento20 pagineERM Final Paper Prashant Singh PDFravan snghNessuna valutazione finora
- Microsoft Endpoint Manager OverviewDocumento4 pagineMicrosoft Endpoint Manager OverviewionNessuna valutazione finora
- Cloud Pricing Models: Taxonomy, Survey, and Interdisciplinary ChallengesDocumento51 pagineCloud Pricing Models: Taxonomy, Survey, and Interdisciplinary Challengesmcclaink06Nessuna valutazione finora
- Security Threat and AWS Modeling Project LectureDocumento11 pagineSecurity Threat and AWS Modeling Project LectureNopeNessuna valutazione finora
- Aneweraof Paas: Ericsson White PaperDocumento11 pagineAneweraof Paas: Ericsson White PapermickygpNessuna valutazione finora
- The Basics of Cloud Computing Economics - VEXXHOSTDocumento8 pagineThe Basics of Cloud Computing Economics - VEXXHOSTVipin TiwariNessuna valutazione finora
- Kamala DevOps - ResumeDocumento4 pagineKamala DevOps - ResumeSatishKumarSinhaNessuna valutazione finora
- Analytic Applications - Part 1Documento66 pagineAnalytic Applications - Part 1Koppala ObulreddyNessuna valutazione finora
- Using MIS 5e Ch. 6-10 & 12 ReviewDocumento242 pagineUsing MIS 5e Ch. 6-10 & 12 ReviewTjhofkes100% (1)
- Oracle Financial Cloud ResumeDocumento39 pagineOracle Financial Cloud ResumebaluanneNessuna valutazione finora
- Cloud Paks Foundational Services Level 1 Quiz Attempt Review PDFDocumento9 pagineCloud Paks Foundational Services Level 1 Quiz Attempt Review PDFameltonayn100% (1)
- Salesforce Marketing CloudDocumento4 pagineSalesforce Marketing CloudAmitNessuna valutazione finora
- The Seven Essential Capabilities of Analytics Driven SiemDocumento5 pagineThe Seven Essential Capabilities of Analytics Driven SiemDika Verdiana SariNessuna valutazione finora
- TCS Digital InterviewDocumento7 pagineTCS Digital InterviewBasanth YajmanNessuna valutazione finora
- Advanced Backup: For Acronis Cyber Protect CloudDocumento2 pagineAdvanced Backup: For Acronis Cyber Protect Cloudintime supportNessuna valutazione finora
- 7 Cloud Terms Infographic EditedDocumento1 pagina7 Cloud Terms Infographic EditedvkandulaNessuna valutazione finora
- Tripwire Enterprise 87 Datasheet PDFDocumento4 pagineTripwire Enterprise 87 Datasheet PDFFrancisco Hernandez MontañezNessuna valutazione finora
- FOOD CLASSIFICATION USING KERAS FinalDocumento21 pagineFOOD CLASSIFICATION USING KERAS FinalSAHITHI NALLANessuna valutazione finora