Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Pair Based Authentication Using Dynamic Grid
Caricato da
Editor IJRITCCCopyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Pair Based Authentication Using Dynamic Grid
Caricato da
Editor IJRITCCCopyright:
Formati disponibili
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 8
ISSN: 2321-8169
5220 - 5223
__________________________________________________________________________________________
Pair Based Authentication using Dynamic Grid
Janhavi Thakur
M.E.Scholar,
Department of Computer Engineering,
TCET, Mumbai, India
Sheetal Rathi
Assistant Professor
Department of Computer Engineering,
TCET, Mumbai, India
Abstract:- Authentication is an important step in Login to the system. In this paper we are implementing one scheme for Mobile Social Network
which makes the authentication process secure compare to the other schemes. Many schemes were proposed to secure the system. We first
explore some major schemes proposed for the Authentication process. Due to the lots of attacks in the cyber world, high performance and secure
login schemes are becoming important and we are implementing one such scheme in our implementation of mobile social network: Pair based
authentication.
General Terms:
Authentication, Security
Keywords:
Mobile Social Network, Session Passwords, Pair Based Authentication Dynamic Grid.
__________________________________________________*****_______________________________________
1. Introduction:
Social networking has become an important factor in our
life, which allows us to connect with the families and
friends. Now a day mobile are playing an important role in
day to day life. They have come up with the tag line
anywhere; anytime that has given rise to the term Mobile
Social Network.
The use of mobile social networks is increasing day by day.
More and more people are registering to avail the services.
The users personal data is very sensitive information. So
the networking sites should guarantee the users that there
data will be safe. Here comes the question of the security to
the system.
Authentication is the main step to access any social website,
where user have to put username and password i.e. some
credential to the system so that the they will understand
genuine user is accessing the website. Many schemes and
techniques are available to provide the authentication.
In this paper we have first listed out all the authentication
schemes. We have focused on text passwords, graphical
passwords and biometrics. The possible attacks on them
were shortlisted. Then we have implemented Pair Based
Dynamic Grid Authentication scheme and compared its
parameters with the existing schemes.
2.
Related Work:
We have divided the term Security in two processes
Authentication, Authorization. Several techniques are
present in each area.
user is been given the access to the system. There are
various ways of authentication techniques i.e. textual
passwords, Graphical passwords and Biometrics
Graphical
Passwords
Textual
Passwords
Biometrics
Authentication
Schheme
.
Fig.1 Authentication Scheme
Among the various authentication techniques textual
password is popular. It consists of the string of alphabets
and special characters. Generally the users have tendency to
choose simple passwords i.e. Spouses name, maiden name,
building name etc. User can choose any arbitrary or lengthy
password to avoid such attacks. But studies have found that
they are not easy to remember.
There are various attacks possible on the textual passwords
like Brute Force attack, Eavesdropping, Dictionary attack,
Social Engineering, Key Logging and Shoulder Surfing etc
[1, 2, 3].
In Authentication phase, the user has to submit correct
credentials which are already stored in the system. After that
5220
IJRITCC | August 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 8
ISSN: 2321-8169
5220 - 5223
__________________________________________________________________________________________
Graphical passwords were introduced to overcome the
attacks faced by textual passwords mostly shoulder surfing,
key logging etc. Various graphical password schemes were
introduced by many authors [4, 5, 6].
In such a scheme the user have to enter the username. After
that the graphical objects will be displayed on the screen.
Depending on the scheme either user have to place images
from random to correct order which were preselected by
user while registration.
3. Pair Based Authentication using Dynamic Grid:
The scheme Pair Based Dynamic Grid Authentication helps
user to keep the login process secured. It also removes the
disadvantages faced by various schemes invented before.
Following are the steps which have to be followed so as to
enter the password. The user makes the pair of the
password. First user checks for the row and then column.
Now he/she finds the intersecting character and enters it as
password. After successfully entering all the password
logins to the system.
Using mouse, touch pad, touch screen user has to select the
objects. Also signatures can be used for authentication. But
even if the slight change is found the authentication is
stopped.
Though the system is secured compare to the textual
passwords it has lots of disadvantages. User verifies or
authenticate only when proper sketch is drawn. Extra
sensitive key pads are required for such scheme. Also the
time required in authentication process is longer.
The biometric scheme is used for authentication which is
based on the image recognition process. In this scheme first
the image is pre-processed and then matched with the
database. Iris recognition, face recognition, thumbs
recognition are the various types of biometrics.
It is one of the good authentication schemes as its real and
unique. Also it doesnt have the fear to be stolen. But this
scheme is expensive also the process is time consuming [7,
8].
The Pair Based Authentication scheme [9] helps to remove
the drawbacks of the above schemes. It helps to avoid
various attacks on the login system such as dictionary
attack, brute force attack, shoulder surfing attack etc. But
Pair Based Authentication Grid is static, due to which key
logging attack is possible. So we will implement new
authentication scheme Pair Based Dynamic Grid
Authentication in which the display changes after every
session.
The scheme Pair Based Dynamic Grid Authentication
consists of three phases: Registration, Login and
Verification Phase. In the Registration phase User registers
the password. When login is to be performed users have to
enter the credential from the shown grids. The system then
verifies the password with the stored database password. As
the system is designed to work with pair of characters only
even length passwords are allowed.
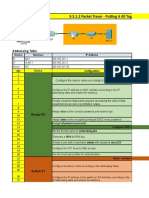
Fig.4 Pair Based Dynamic Grid Authentication Scheme
The below are the steps which are used for the
authentication process.
Registration
Enter Username
Pair Based System with Dynamic
Grid
Verify the Password
Fig.3 Flow diagram of Pair Based Dynamic Grid
Authentication Scheme
This authentication scheme consists of three steps
Step 1) Register Username and Password
Step 2) Login to the system
Step 3) Verify the stored password
5221
IJRITCC | August 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 8
ISSN: 2321-8169
5220 - 5223
__________________________________________________________________________________________
4. Experimental Results:
All the experiments were executed on 2.40 GHz Intel i5
processor with 4GB RAM. The program code is written in
C# and executed using .Net framework.
As we can see in the above screenshots of Pair based
authentication using dynamic grid scheme, the interface
changes after each session, thereby thwarting any key
logging attack on the user.
Table 1 shows textual passwords, graphical passwords,
biometrics and Pair Based Dynamic Grid Authentication are
compared in various parameters. From which it is clear that
Pair Based Dynamic Grid Authentication requires low cost,
it gives high protection level, processing time is also low
and it doesnt require
additional hardware. We can see that it is the best technique.
Table 1. Comparison of Authentication technique
Authenticati
on Schemes
1)Textual
Password
2)Graphical
Password
Cost
Low
High
Prote
ction
Level
Medi
um
Medi
um
Process
ing
Time
Addition
al
Hardwar
e
Required
Low
No
High
Yes
3)Biometric
High
High
High
Yes
4)Pair Based
Dynamic Grid
low
High
Low
No
Based Authentication using Dynamic grid is the best
technique.
Table 2.Attacks on the Authentication technique
Authenti
cation
Schemes
Attacks
1)Textual
Password
Eves Dropping,
Shoulder
Surfing,
Social
Engineering,
Key Logging,
Eves Drooping,
Guessing
2)Graphi
cal
Password
3)Biomet
ric
4)Pair
Based
Dynamic
Grid
Authentication Schemes
--
--
--
Cost
High
Medium
Protection
Level
Low
Processing
Time
Textual
Graphical Biometric Pair Based
Hardware
Required
Fig.5 Comparison of Paired Based Authentication with
other schemes
Table 2 enlists the attacks possible on the above scheme.
We can see from the table that except textual password all
other schemes, too resist various attacks but their
implementation cost is high. Again we can say that Pair
5.
Resistant to
Attacks
Cost
Low
--
Eves Dropping,
Shoulder
Surfing,
Social
Engineering,
Key Logging,
Eves Drooping
Eves Dropping,
Shoulder
Surfing,
Social
Engineering,
Key Logging,
Eves Drooping
Eves Dropping,
Shoulder
Surfing,
Social
Engineering,
Key Logging,
Eves Drooping
High
High
Low
CONCLUSION:
Conventional authentication schemes like Textual Password
and others have experienced limitations while handling the
login process. Though textual passwords are the simplest
way to handle the login process it is more prone to attacks.
Other schemes graphical password requires more processing
time than the textual passwords hence lessen the
performance. Also it provides medium security. Another
traditional scheme, biometrics faces the challenge for
maintaining the high precision equipments required for
scanning iris, thumbprint, etc. Also the processing time is
more compared to the other schemes. It takes significant
amount of time whenever the matching is to be performed
5222
IJRITCC | August 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 8
ISSN: 2321-8169
5220 - 5223
__________________________________________________________________________________________
between the users entered data and database data.
Implemented authentication scheme comes over these three
disadvantages.
Experimental results of Pair Based Dynamic Grid
Authentication show that it is efficient in reducing
processing time by taking texts as the input. Also, shows the
cost for designing the system is very less as no external
hardware is required for the authentication process. It is
resistant to many attacks and provides high protection level.
The implemented authentication scheme is faster and more
secured compared to the other schemes in the market. More
websites should adopt these schemes to avail the advantages
given by it.
6.
ACKNOWLEDMENT:
We are greatly indebted to Dr.R.R.Sedamkar for his
guidance and enlightened comments, which has helped in
completing work successfully.
REFERENCES:
[1]
M. Weir, S. Aggarwal, B. de Medeiros, and B. Glodek,
Password cracking using probabilistic context-free
grammars, in Proc. IEEE Symposium on Security and
Privacy, 2009.
[2]
Fujita, K. and Y. Hirakawa, A study of password
authentication method against observing wrapper approach
for feature subset selection in Attacks, 6th International
Symposium on Intelligent keystroke dynamics identity
verification, Systems and Informatics, SISY 2008.
D. Florencio and C. Herley, A large-scale study of web
password habits, in Proc. WWW07, 2007.
[3]
[4]
Eljetlawi, A.M.; Fac. of Eng., Univ. of Tajoura, Tripoli,
Libya," Graphical password: Existing recognition base
graphical password usability", IEEE, March 2010
[5]
Almulhem, A.; Comput. Eng. Dept., King Fahd Univ. of
Pet. & Miner., Dhahran, Saudi Arabia,"A graphical
password authentication system", IEEE, FEB 2011
[6]
XiaoyuanSuo,; Ying Zhu; Owen, G.S,
passwords: a survey", IEEE, DEC 2005.
"Graphical
Ahmed, A.A.E. and I. Traore, Anomaly Intrusion
Detection Based on Biometrics, IEEE Proceedings, IAW
'05.
[8] Varun Kacholia and Shashank Pandit,Biometric
Authentication Using Random Distribution, Canadian IT
Security Symposium (CITSS), 2003
[9] VAISHNAVI
PANCHAL*,
CHANDAN
P.
PATIL,Authentication Schemes for Session Password,
IJSER 2013
[10] Shakir, M. and Abdul Ayaz Khan,S3TFPAS Scalable
shoulder surfing resistant Textual-Formula base Password
Authentication system IEEE, 2010
[7]
5223
IJRITCC | August 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
Potrebbero piacerti anche
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- Performance Analysis of Image Restoration Techniques at Different NoisesDocumento4 paginePerformance Analysis of Image Restoration Techniques at Different NoisesEditor IJRITCCNessuna valutazione finora
- Regression Based Comparative Study For Continuous BP Measurement Using Pulse Transit TimeDocumento7 pagineRegression Based Comparative Study For Continuous BP Measurement Using Pulse Transit TimeEditor IJRITCCNessuna valutazione finora
- A Review of 2D &3D Image Steganography TechniquesDocumento5 pagineA Review of 2D &3D Image Steganography TechniquesEditor IJRITCCNessuna valutazione finora
- Channel Estimation Techniques Over MIMO-OFDM SystemDocumento4 pagineChannel Estimation Techniques Over MIMO-OFDM SystemEditor IJRITCCNessuna valutazione finora
- IJRITCC Call For Papers (October 2016 Issue) Citation in Google Scholar Impact Factor 5.837 DOI (CrossRef USA) For Each Paper, IC Value 5.075Documento3 pagineIJRITCC Call For Papers (October 2016 Issue) Citation in Google Scholar Impact Factor 5.837 DOI (CrossRef USA) For Each Paper, IC Value 5.075Editor IJRITCCNessuna valutazione finora
- A Review of Wearable Antenna For Body Area Network ApplicationDocumento4 pagineA Review of Wearable Antenna For Body Area Network ApplicationEditor IJRITCCNessuna valutazione finora
- Modeling Heterogeneous Vehicle Routing Problem With Strict Time ScheduleDocumento4 pagineModeling Heterogeneous Vehicle Routing Problem With Strict Time ScheduleEditor IJRITCCNessuna valutazione finora
- Channel Estimation Techniques Over MIMO-OFDM SystemDocumento4 pagineChannel Estimation Techniques Over MIMO-OFDM SystemEditor IJRITCCNessuna valutazione finora
- Comparative Analysis of Hybrid Algorithms in Information HidingDocumento5 pagineComparative Analysis of Hybrid Algorithms in Information HidingEditor IJRITCCNessuna valutazione finora
- A Review of Wearable Antenna For Body Area Network ApplicationDocumento4 pagineA Review of Wearable Antenna For Body Area Network ApplicationEditor IJRITCCNessuna valutazione finora
- A Review of 2D &3D Image Steganography TechniquesDocumento5 pagineA Review of 2D &3D Image Steganography TechniquesEditor IJRITCCNessuna valutazione finora
- Safeguarding Data Privacy by Placing Multi-Level Access RestrictionsDocumento3 pagineSafeguarding Data Privacy by Placing Multi-Level Access Restrictionsrahul sharmaNessuna valutazione finora
- Importance of Similarity Measures in Effective Web Information RetrievalDocumento5 pagineImportance of Similarity Measures in Effective Web Information RetrievalEditor IJRITCCNessuna valutazione finora
- Diagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmDocumento5 pagineDiagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmEditor IJRITCCNessuna valutazione finora
- Itimer: Count On Your TimeDocumento4 pagineItimer: Count On Your Timerahul sharmaNessuna valutazione finora
- Network Approach Based Hindi Numeral RecognitionDocumento4 pagineNetwork Approach Based Hindi Numeral RecognitionEditor IJRITCCNessuna valutazione finora
- Fuzzy Logic A Soft Computing Approach For E-Learning: A Qualitative ReviewDocumento4 pagineFuzzy Logic A Soft Computing Approach For E-Learning: A Qualitative ReviewEditor IJRITCCNessuna valutazione finora
- Predictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth KotianDocumento3 paginePredictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth Kotianrahul sharmaNessuna valutazione finora
- Prediction of Crop Yield Using LS-SVMDocumento3 paginePrediction of Crop Yield Using LS-SVMEditor IJRITCCNessuna valutazione finora
- A Study of Focused Web Crawling TechniquesDocumento4 pagineA Study of Focused Web Crawling TechniquesEditor IJRITCCNessuna valutazione finora
- Hybrid Algorithm For Enhanced Watermark Security With Robust DetectionDocumento5 pagineHybrid Algorithm For Enhanced Watermark Security With Robust Detectionrahul sharmaNessuna valutazione finora
- Vehicular Ad-Hoc Network, Its Security and Issues: A ReviewDocumento4 pagineVehicular Ad-Hoc Network, Its Security and Issues: A Reviewrahul sharmaNessuna valutazione finora
- 44 1530697679 - 04-07-2018 PDFDocumento3 pagine44 1530697679 - 04-07-2018 PDFrahul sharmaNessuna valutazione finora
- Efficient Techniques For Image CompressionDocumento4 pagineEfficient Techniques For Image CompressionEditor IJRITCCNessuna valutazione finora
- 45 1530697786 - 04-07-2018 PDFDocumento5 pagine45 1530697786 - 04-07-2018 PDFrahul sharmaNessuna valutazione finora
- A Clustering and Associativity Analysis Based Probabilistic Method For Web Page PredictionDocumento5 pagineA Clustering and Associativity Analysis Based Probabilistic Method For Web Page Predictionrahul sharmaNessuna valutazione finora
- 41 1530347319 - 30-06-2018 PDFDocumento9 pagine41 1530347319 - 30-06-2018 PDFrahul sharmaNessuna valutazione finora
- A Content Based Region Separation and Analysis Approach For Sar Image ClassificationDocumento7 pagineA Content Based Region Separation and Analysis Approach For Sar Image Classificationrahul sharmaNessuna valutazione finora
- Image Restoration Techniques Using Fusion To Remove Motion BlurDocumento5 pagineImage Restoration Techniques Using Fusion To Remove Motion Blurrahul sharmaNessuna valutazione finora
- Space Complexity Analysis of Rsa and Ecc Based Security Algorithms in Cloud DataDocumento12 pagineSpace Complexity Analysis of Rsa and Ecc Based Security Algorithms in Cloud Datarahul sharmaNessuna valutazione finora
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (895)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (344)
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (399)
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (588)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (73)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2259)
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (120)
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- OWASP Web Security GuideDocumento35 pagineOWASP Web Security Guidekaplumb_aga100% (9)
- Enterasys Nac GuideDocumento19 pagineEnterasys Nac GuideIchwan SetiawanNessuna valutazione finora
- Instructions:: Assignment No. 03 Semester: Fall 2019 Network Security-CS315 Total Marks: 20Documento3 pagineInstructions:: Assignment No. 03 Semester: Fall 2019 Network Security-CS315 Total Marks: 20Digambar S TatkareNessuna valutazione finora
- HwontlogDocumento4 pagineHwontlogNaing linn AungNessuna valutazione finora
- Practical Exercise 1 SMC (Syafiq F2056, Hidayat F2036, Ahmad F2008)Documento8 paginePractical Exercise 1 SMC (Syafiq F2056, Hidayat F2036, Ahmad F2008)F2056 SyafiqNessuna valutazione finora
- Ways To Make Money Online - Earn Money OnlineDocumento6 pagineWays To Make Money Online - Earn Money OnlineMoodroot StudioNessuna valutazione finora
- API Testing With TestProject - KTDocumento14 pagineAPI Testing With TestProject - KTTestNessuna valutazione finora
- End of Life For Windows 7 and Windows Server 2002Documento2 pagineEnd of Life For Windows 7 and Windows Server 2002yes techNessuna valutazione finora
- Starting The Default Launcher Using Adb - Ivucica BlogDocumento3 pagineStarting The Default Launcher Using Adb - Ivucica BlogZoran NonkovicNessuna valutazione finora
- VPN PresentationDocumento31 pagineVPN PresentationŠimon KrámskýNessuna valutazione finora
- CS5460 ChadMaughan Assignment4Documento3 pagineCS5460 ChadMaughan Assignment4the_tigdraNessuna valutazione finora
- Security at The Application Layer:: S/MimeDocumento54 pagineSecurity at The Application Layer:: S/MimeKunal KumarNessuna valutazione finora
- Mookambigai College of Engineering: Srinivasa Nagar, Kalamavur, Pudukkottai - 622502Documento55 pagineMookambigai College of Engineering: Srinivasa Nagar, Kalamavur, Pudukkottai - 622502Seekay Alais Karuppaiah CNessuna valutazione finora
- Unit 1Documento70 pagineUnit 1teja mNessuna valutazione finora
- Torrent SupportDocumento31 pagineTorrent SupportakbisoiNessuna valutazione finora
- Topic 3 - NetworksDocumento76 pagineTopic 3 - NetworksDiandra Satria AdhitamaNessuna valutazione finora
- Implementing A Spam and Virus Scanning Mail Server Using Redhat Linux 8.0 and Amavisd-NewDocumento15 pagineImplementing A Spam and Virus Scanning Mail Server Using Redhat Linux 8.0 and Amavisd-NewArmando SepulvedaNessuna valutazione finora
- Indian Matka Online Tips, Best Satta Matka ResultDocumento8 pagineIndian Matka Online Tips, Best Satta Matka ResultMatka IndianNessuna valutazione finora
- CP R80.10 RemoteAccessVPN AdminGuide PDFDocumento159 pagineCP R80.10 RemoteAccessVPN AdminGuide PDFTruong LanNessuna valutazione finora
- 2.2.2.4 Lab - Using Postman To List RoomsDocumento3 pagine2.2.2.4 Lab - Using Postman To List RoomskalyanNessuna valutazione finora
- ACN MicroprojectDocumento26 pagineACN MicroprojectOmeeNessuna valutazione finora
- Jquery, Ajax, JsonDocumento25 pagineJquery, Ajax, JsonrakhaaditNessuna valutazione finora
- CP R80.40 SecurityManagement AdminGuideDocumento609 pagineCP R80.40 SecurityManagement AdminGuideingwarrNessuna valutazione finora
- Dictionnaire Infernal Ou Recherches EtDocumento603 pagineDictionnaire Infernal Ou Recherches EtNexus Bahar100% (2)
- Cyber and Network Security Framework: Knowledge Paper OnDocumento24 pagineCyber and Network Security Framework: Knowledge Paper Onvaragg24Nessuna valutazione finora
- BS 340 (1979) - 1979 Specification For Precast Concrete Kerbs, ChaDocumento1 paginaBS 340 (1979) - 1979 Specification For Precast Concrete Kerbs, Chamohamed samirNessuna valutazione finora
- 9.5.1.2 Packet Tracer - Putting It All Together: Addressing TableDocumento6 pagine9.5.1.2 Packet Tracer - Putting It All Together: Addressing TableGaz ArtimisNessuna valutazione finora
- Internet and InteranetDocumento6 pagineInternet and InteranetGuruKPO0% (1)
- Filmora CrackDocumento2 pagineFilmora CrackAxelia100% (1)
- Remote Access VPN Design GuideDocumento70 pagineRemote Access VPN Design GuidecapodelcapoNessuna valutazione finora