Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
SQL Injection Prevention in Banking
Caricato da
Chen FeliciaCopyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
SQL Injection Prevention in Banking
Caricato da
Chen FeliciaCopyright:
Formati disponibili
Sampada Gadgil/ (IJCSIT) International Journal of Computer Science and Information Technologies, Vol.
4 (2) , 2013, 345- 349
SQL Injection Prevention in Banking
Sampada Gadgil
Department Of IT,
SIES Graduate School Of Technology
Navi Mumbai, India
Abstract SQL injection attack (SQLIA) is a type of attack
on web applications that exploits the fact that input provided
by web clients is directly included in the dynamically
generated SQL statements. SQLIA is one of the foremost
threats to web applications. In an SQL injection attack, an
attacker might insert a malicious SQL query as input to
perform an unauthorized database operation. The attack
works when a program builds queries based on strings from
the client, and passes them to a database server without
handling characters that have special meaning to the server
using SQL injection attacks, an attacker can retrieve or
modify confidential and sensitive information from the
database. The growing use of web-applications for business
purposes has given motivation to attackers to explore the
possibilities and exploit these types of attacks. In this paper all
type of SQL injection attack are discussed. An application is
developed for online banking application. This application
prevents various types of SQL attacks.
Keywords SQL injection,
Detection, Prevention
Web
application,
WASP,
I. INTRODUCTION
In recent years, most of our daily tasks are depend on
database driven web applications because of increasing
activity, such as banking, booking and shopping [1]. For
performing activities such as ordering the merchandize or
paying the bills, information must be trustable to these web
applications and their underlying databases but
unfortunately there is no any guarantee for confidentiality
and integrity of this information. Web applications are often
vulnerable to attacks, which can give attackers easily access
to the application's underlying database. SQL Injection is a
security exploit method in which the attacker aims at
penetrating a back-end database to manipulate, steal or
modify information in the database. The SQL Injection
attack method exploits the Web application by injecting
malicious queries, causing the manipulation of data. Almost
all SQL databases and programming languages are
potentially vulnerable. SQL Injection is subset of an
unverified user input vulnerability ("buffer overflows" are a
different subset), and the idea is to convince the application
to run SQL code that was not intended. Structured Query
Language (SQL) is the nearly universal language of
databases that allows the storage, manipulation, and
retrieval of data. Databases that use SQL include MS SQL
Server, MySQL, Oracle, Access and File maker Pro and
these databases are equally subject to SQL injection attack.
Not preventing SQL Injection attacks leaves your business
at great risk of :
a. Sensitive information can be altered or accessed.
www.ijcsit.com
b. It may lead to financial losses
c. In some cases like banking application, attacker can
withdraw money.
d. Steal customer information such as credit card numbers
To get a better understanding of SQL injection, we need to
have a good understanding of the kinds of communications
that take place during a typical session between a user and a
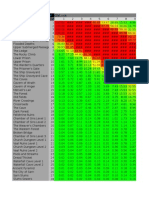
web application. The following figure shows [2] the typical
communication exchange between all the components in a
typical web application system.
Fig 1: SQL Attack Process
SQL vulnerabilities exist where there are applications need
to dynamically constructed SQL statements according to
Web client environment. Because the server-side
applications use SQL statements in the form of patchwork
operation of the database, which allows an attacker to
submit the data they want included in SQL statements. For
all platforms, based SQL standard database software, SQL
language is valid. As long as the client data replaces the
data in SQL statements, may be attacked. The result of
SQLIA can be disastrous because a successful SQL
injection can read sensitive data from database, modify
database data and execute operations on the database. The
main consequences of these vulnerabilities are attacks on [3]
1) Authorization: Critical data may be altered by a
successful SQLIA.
2) Authentication: If there is no any proper control on
username or password, it may be possible to login to a
system as a normal user without knowing a right username
or password.
3) Confidentiality: Usually database contains sensitive
data. So attacker can access that data.
4) Integrity: By a successful SQLIA, not only attacker reads
sensitive information but also it is possible to change or
delete this information.
345
Sampada Gadgil/ (IJCSIT) International Journal of Computer Science and Information Technologies, Vol. 4 (2) , 2013, 345- 349
SQL injection attacks are extremely dangerous types of
attacks. These attacks are very much harmful for the web
based application. This paper focus on various types of
SQL attacks. In this paper, attack types are explained with
an example. An application is developed for preventing
these attacks. This application is developed for banking
system.
II. SQL ATTACK TYPES
There are different methods of attacks that depending on the
goal of attacker are performed together or sequentially. For
a successful SQLIA the attacker should append a
syntactically correct command to the original SQL query.
1. Tautologies: This type of attack injects SQL tokens to the
conditional query statement to be evaluated always true.
Consider this example [1]:
"SELECT * FROM employee WHERE userid = '112' and
password ='aaa' OR '1 '='1
As the tautology statement (1=1) has been added to the
query statement so it is always true.
2. Union Queries: These attacks are related to the
Tautology SQLIAs. The attacker exploits vulnerable
parameters in order to change the result set of a given query.
The trick here is that the attacker injects the SQL code in
such a way that it returns data from a table different from
the one intended by the programmer. The result of Union
Query injection attacks will be a new dataset returned by
the database, containing the union of the first (developerintended) and the second (attacker-intended) query.
Suppose for our examples [1], that the query executed from
the server is the following:
SELECT Name, Phone FROM Users WHERE Id=$id By
injecting the following Id value:
$id= I UNION ALL SELECT credit Card Number, 1 FROM
Credit CarT able
We will have the following query:
SELECT Name, Phone FROM Users WHERE Id= 1 UNION ALL
SELECT creditCardNumber, 1 FROM Credit CarTable, which
will join the result of the original query with all the credit card
users.
3. Piggy Backed Queries: In this attack type, an attacker
tries to inject additional queries into the original query. We
distinguish this type from others because, in this case,
attackers are not trying to modify the original intended
query; instead, they are trying to include new and distinct
queries that piggy-back on the original query. As a result,
the database receives multiple SQL queries [4]. The first is
the intended query which is executed as normal; the
subsequent ones are the injected queries, which are
executed in addition to the first.
If the attacker inputs ; drop table users - - into the pass
field, the application generates the query:
SELECT accounts FROM users WHERE login=doe AND
pass=; drop table users -- AND pin=123
After completing the first query, the database would
recognize the query delimiter (;) and execute the injected
second query. The result of executing the second query
would be to drop table users, which would likely destroy
valuable information. Other types of queries could insert
new users into the database or execute stored procedures.
4. Inference: By this type of attack, intruders change the
behaviour of a database or application [1]. There are two
www.ijcsit.com
well-known attack techniques that are based on inference:
blind injection and timing attacks.
Blind injection - is a well-known type of SQLIA where the
attacker simply injects an SQL statement and observes the
application's behaviour: if the page continues to function
normally, then this would imply that the injected statement
resulted to true, otherwise the attacker will see a non
descriptive error and a page that might differ from the
normal one.
Timing attacks - are similar to blind injection attacks, but
here the attacker formulates the SQL statements in the form
of if-then command and uses SQL commands like
WAITFOR to cause delays in the database statements
execution along one of the branches of the if-then
conditional. [5]
SELECT account FROM users WHERE login='realUser' and
ASCII(SUBSTRING(( SELECT TOP 1 name from sysobjects), 1,
1))
< X WAITFOR 5 -- 'AND pass=' ' AND pin=0, where the
attacker asks if the ASCII value of the first character in the
first name in the table is less than a number (X in our
example) and he will get 5 seconds delay in database
execution of the statement in case that condition evaluates
to true.
5. Illegal/Logically Incorrect Queries: This type of SQLIAs
is used to trigger syntax errors (which would be used to
identify injectable parameters), type conversion errors (to
deduce the data types of certain columns or extract data
from them) or logical errors (which often reveal names of
the tables and columns that caused the error), in order for
the attacker to gather information about the type and
structure of the back-end database of a given Webapplication.
SELECT accounts FROM users WHERE login= AND pass=
AND pin= convert (int,(select top 1 name from sysobjects where
xtype=u))
In the example above [6], we have assumed that the
application is using Microsoft SQL Server and the metadata
table is called sysobjects. The above-query will try extract
the first user table 'xtype=u' and to convert the table name
into an integer.
This will result in a type conversion error and MS SQL Server will
say: \Microsoft OLE DB Provider for SQL Server (0x80040E07)
Error converting varchar value CreditCards to a column of data
type int.".This message will be valuable to the attacker, since now
he will know the type of the database is Microsoft SQL Server,and
secondly, he will now know the name of the first user defined
table in the database (CreditCards).
6. Stored Procedure: SQLIAs of this type try to execute
stored procedures present in the database. Today, most
database vendors ship databases with a standard set of
stored procedures that extend the functionality of the
database and allow for interaction with the operating system
[6]. Therefore, once an attacker determines which backend
database is in use, SQLIAs can be crafted to execute stored
procedures provided by that specific database, including
procedures that interact with the operating system.
CREATE
PROCEDURE
DBO.isAuthenticated
@userName varchar2, @pass varchar2, @pin int AS
EXEC("SELECT accounts FROM users WHERE login= '
+@userName+ and pass= +@password+ and
pin=+@pin);
GO
346
Sampada Gadgil/ (IJCSIT) International Journal of Computer Science and Information Technologies, Vol. 4 (2) , 2013, 345- 349
For authorized/unauthorized user the stored procedure
returns true/false. As an SQLIA, intruder input " , ;
SHUTDOWN; - -" for usemame or password. Then the
stored procedure generates the following query:
SELECT accounts FROM users WHERE login='doe' AND
pass = ' '; SHUTDOWN; -- AND pin=
The first original query is executed and consequently the
second query which is illegitimate is executed and causes
database shut down.
7.Alternate Encodings: This attack type is used in
conjunction with other attacks. In other words, alternate
encodings do not provide any unique way to attack an
application; they are simply an enabling technique that
allows attackers to evade detection and prevention
techniques and exploit vulnerabilities that might not
otherwise be exploitable.
(CIL), or generate any other specific format. Theoretically,
a C# compiler could generate machine code like traditional
compilers of C++ or FORTRAN. However, in practice, all
existing compiler implementations target CIL.
SQL Server 2000 is much more integrated with Windows
NT Server than any of its predecessors. Databases are now
stored directly in Windows NT Server files .SQL Server is
being stretched towards both the high and low end. SQL
Server 2000 creates a database using a set of operating
system files, with a separate file used for each database.
Multiple databases can no longer share the same file. There
are several important benefits to this simplification. Files
can now grow and shrink, and space management is greatly
simplified. All data and objects in the database, such as
tables, stored procedures, triggers, and views, are stored
only within the operating system files. When a database is
In this attack, the following text is injected into the login field:
legalUser; exec(0x73687574646f776e) - - . The resulting created, all the files that comprise the database are zeroed
query generated by the application is:
out (filled with zeros) to overwrite any existing data left on
SELECT accounts FROM users WHERE login=legalUser; the disk by previously deleted files. This improves the
exec(char(0x73687574646f776e)) -- AND pass= AND
performance of day-to-day operations.
pin=
This example makes use of the char() function and of
IV IMPLEMENTATION TECHNIQUE
ASCII hexadecimal encoding. The char() function takes as
a parameter an integer or hexadecimal encoding of a The implementation makes use of WASP [7] tool for online
character and returns an instance of that character. The banking application. WASP stands for Web Application
stream of numbers in the second part of the injection is the SQL Injection Preventer tool. WASP tool consists of two
ASCII hexadecimal encoding of the string SHUTDOWN. approaches. These are positive tainting and syntax aware
Therefore, when the query is interpreted by the database, it evaluation.
would result in the execution, by the database, of the 1) Positive tainting [7]: The effectiveness of this approach,
in that it helps address problems caused by incompleteness
SHUTDOWN command.
in the identification of relevant data to be marked. In the
case of negative tainting, incompleteness leads to trusting
data that should not be trusted and, ultimately, to false
III APPLICATION Development
Here online banking application is developed to prevent negatives. Our basic approach, as explained in the
various types of SQL attacks. Banking application contains following sections, automatically marks as trusted all hardsensitive data like account information, user id or password coded strings in the code and then ensures that all SQL
keywords and operators are built using trusted data. In some
etc.
cases, this basic approach is not enough because developers
This application consists of two modules:
can also use external query fragmentspartial SQL
1. Normal Process: In this module, attacker can make SQL
attack and he can access sensitive information. He can enter commands that come from external input sourcesto build
queries. Because these string fragments are not hard coded
invalid password using SQL keyword or operator. He can
in the application, they would not be part of the initial set of
modify the account or withdraw the money.
2. Prevent Process: In this module WASP prevention trusted data identified by our approach and the approach
technique is used to avoid SQL attacks. So attacker cannot would generate false positives when the string fragments
access the sensitive information. Even if the unauthorized are used in a query. To account for these cases, our
user tries to access account data is not available to him. technique provides developers with a mechanism for
Both the modules contain sub module to perform different specifying sources of external data that should be trusted.
The data sources can be of various types such as files,
types of banking operations.
network connections, and server variables. Our approach
A Deployment Requirement
uses this information to mark data that comes from these
Operating System used is Windows XP Professional. Front additional sources as trusted. In a typical scenario, we
End is Microsoft Visual Studio .Net 2005. Language to expect developers to specify most of the trusted sources
develop this application used is Visual C # .Net. Back End before testing and deployment. However, some of these
is SQL Server 2000. C# is the programming language that sources might be overlooked until after a false positive is
most directly reflects the underlying Common Language reported, in which case, developers would add the omitted
Infrastructure (CLI). Most of its intrinsic types correspond items to the list of trusted sources. In this process, the set of
to value-types implemented by the CLI framework. trusted data sources monotonically grows and eventually
However, the language specification does not state the code converges to a complete set that produces no false positives.
generation requirements of the compiler: that is, it does not It is important to note that false positives that occur after
state that a C# compiler must target a Common Language deployment would be due to the use of external data
Runtime, or generate Common Intermediate Language sources that have never been used during in-house testing.
www.ijcsit.com
347
Sampada Gadgil/ (IJCSIT) International Journal of Computer Science and Information Technologies, Vol. 4 (2) , 2013, 345- 349
In other words, false positives are likely to occur only for
totally untested parts of applications.
Therefore, even when developers fail to completely identify
additional sources of trusted data beforehand, we expect
these sources to be identified during normal testing and the
set of trusted data to quickly converge to the complete set.
It is also worth noting that none of the subjects that we
collected and examined so far required us to specify
additional trusted data sources. All of these subjects used
only hard-coded strings to build query. Strings
Incompleteness may thus leave the application vulnerable
to attacks and can be very difficult to detect, even after
attacks actually occur, because they may go completely
unnoticed. With positive tainting, incompleteness may lead
to false positives, but it would never result in an SQLIA
escaping detection. We track taint information at the
character level rather than at the string level. We do this
because, for building SQL queries, strings are constantly
broken into substrings, manipulated, and combined.
2)Syntax aware evaluation[7]: The key feature of syntax
aware evaluation is that it considers the context in which
trusted and untrusted data is used to make sure that all parts
of a query other than string or numeric literals (for example,
SQL keywords and operators) consist only of trusted
characters. As long as untrusted data is confined to literals,
we are guaranteed that no SQLIA can be performed. The
WASP technique performs syntax-aware evaluation of a
query string immediately before the string is sent to the
database to be executed. To evaluate the query string, the
technique first uses a SQL parser to break the string into a
sequence of tokens that correspond to SQL keywords,
operators, and literals. The technique then iterates through
the tokens and checks whether tokens (that is, substrings)
other than literals contain only trusted data. If all such
tokens pass this check, the query is considered safe and is
allowed to execute.
V EXPERIMENTAL RESULTS
In this application, SQL injection affects the data in the
normal process module. It is shown in the figure 2. Here
SQL operator is used for attack purpose. Attacker can get
sensitive data by applying SQL keywords or operators
which is shown in figure 3.
Fig 3: Result of SQL attack
Figure 4 shows one more attack on web application. This is
an example of tautological attack. In the user name field,
attacker will insert the name and SQL symbols. But when
the attacker clicks the submit button, access to the data is
not given to the attacker.
Fig 4: An example of SQL attack
This attack is prevented, which is shown in the following
figure.
Fig 2: An example of SQL attack
Figure 2 shows example of SQL attack. In this attack, an
unauthorized user is accessing the information. He is using SQL
operator for this purpose and he is getting the details.
www.ijcsit.com
Fig 5: Prevention of SQL attack
348
Sampada Gadgil/ (IJCSIT) International Journal of Computer Science and Information Technologies, Vol. 4 (2) , 2013, 345- 349
VI CONCLUSION AND FUTURE WORK
SQL injection attacks are serious for web application.
These attacks can access, alter or destroy the sensitive data.
In this paper, concept of SQL attack is explained. Different
types of attacks are explained with example.
The application is developed for online banking. For this
WASP tools is used. Two modules are developed. One of
the modules shows how attacker can access the data. The
other one shows prevention of these attacks. It is found that
the attacks can be prevented. Future scope is to actually
deploy this application on web.
REFERENCES
[1]
[2]
[3]
[4]
[5]
[6]
[7]
Atefeh Tajpour, Maslin Masrom, Mohammad Zaman Heydari,
Suhaimi Ibrahim, SQL Injection Detection and Prevention Tools
Assessment,2010 IEEE
Yi Yan, Su Zhengyuan, Dai Zucheng,The Database Protection
System Against SQL Attacks, 2011 IEEE
Atefeh Tajpour, Suhaimi Ibrahim, Maslin Masrom, SQL Injection
Detection and Prevention Techniques, International Journal of
Advancements in Computing Technology Volume 3, Number 7,
August 2011
William G.J. Halfond, Jeremy Viegas, and Alessandro Orso, A
Classification of SQL Injection Attacks and Countermeasures,2006
IEEE
Fatbardh Veseli, SQL Injection Attacks - Detection and
Prevention Techniques
William G.J. Halfond, Jeremy Viegas, and Alessandro Orso, A
Classification of SQL Injection Attacks and Countermeasures,2006
IEEE
William G.J. Halfond, Alessandro Orso, WASP: Protecting Web
Applications Using Positive Tainting and Syntax Aware
Evaluation, IEEE Transaction on Software Engineering, VOL 34,
NO 1, January/February 2008
www.ijcsit.com
349
Potrebbero piacerti anche
- IMail Student User GuideDocumento36 pagineIMail Student User GuideChen Felicia100% (1)
- JDBC Checker A Static Analysis Tool For SQL-JDBC ApplicationsDocumento2 pagineJDBC Checker A Static Analysis Tool For SQL-JDBC ApplicationsChen FeliciaNessuna valutazione finora
- SQL Injection Prevention in BankingDocumento5 pagineSQL Injection Prevention in BankingChen FeliciaNessuna valutazione finora
- 10 1 1 95Documento11 pagine10 1 1 95Akanksha HaritNessuna valutazione finora
- 10 1 1 95Documento11 pagine10 1 1 95Akanksha HaritNessuna valutazione finora
- PoE Exp ChartsDocumento85 paginePoE Exp ChartsChen FeliciaNessuna valutazione finora
- Rapid Application DevelopmentDocumento34 pagineRapid Application DevelopmentChen FeliciaNessuna valutazione finora
- Alien Book ListDocumento1 paginaAlien Book ListChen FeliciaNessuna valutazione finora
- Games 2011Documento1 paginaGames 2011Chen FeliciaNessuna valutazione finora
- PoE PowerlevelingDocumento1 paginaPoE PowerlevelingChen FeliciaNessuna valutazione finora
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (895)
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (400)
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (588)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (74)
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (344)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (121)
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- CV TemplateDocumento4 pagineCV TemplateIri PopescuNessuna valutazione finora
- Frederick Douglass EssayDocumento4 pagineFrederick Douglass Essayapi-452857710Nessuna valutazione finora
- Unemployment InsuranceDocumento8 pagineUnemployment InsuranceBhumani TyagiNessuna valutazione finora
- Bell Atlantic Corp v. TwomblyDocumento4 pagineBell Atlantic Corp v. Twomblylfei1216Nessuna valutazione finora
- Building Planning & DrawingDocumento5 pagineBuilding Planning & Drawingshreeprashant849160% (5)
- Suarez-Eden v. Dickson Et Al - Document No. 3Documento9 pagineSuarez-Eden v. Dickson Et Al - Document No. 3Justia.comNessuna valutazione finora
- Police Law EnforcementDocumento4 paginePolice Law EnforcementSevilla JoenardNessuna valutazione finora
- Wavelets and Signal ProcessingDocumento193 pagineWavelets and Signal ProcessingAlbeno Saleh AhmadNessuna valutazione finora
- Cold SandwichesDocumento7 pagineCold SandwichesLea Galano ManarpaacNessuna valutazione finora
- Cesc Modules 8Documento6 pagineCesc Modules 8kiethly juanitezNessuna valutazione finora
- Inside The Mind of A Master ProcrastinatorDocumento5 pagineInside The Mind of A Master ProcrastinatorDianaNessuna valutazione finora
- 2016 May Virginia Medical Law ReportDocumento20 pagine2016 May Virginia Medical Law ReportMichael DuntzNessuna valutazione finora
- Science Revision Sheet Year 7 Periodic 2Documento5 pagineScience Revision Sheet Year 7 Periodic 2malknabih699Nessuna valutazione finora
- Cristoforo BuondelmontiDocumento15 pagineCristoforo BuondelmontiAnna AchiolaNessuna valutazione finora
- Lesson 4 Prepare and Interpret Technical Drawing: Alphabet of LinesDocumento26 pagineLesson 4 Prepare and Interpret Technical Drawing: Alphabet of LinesREYNALDO BAJADONessuna valutazione finora
- Nosocomial InfectionDocumento31 pagineNosocomial InfectionDr. Ashish Jawarkar0% (1)
- Elec Final OutputDocumento3 pagineElec Final Outputluebert kunNessuna valutazione finora
- Wed 0945-Avionics Modernization For LegacyDocumento38 pagineWed 0945-Avionics Modernization For LegacygasparferrerNessuna valutazione finora
- Factors Affecting The Success or Failure of Project Management Methodologies (PMM) Usage in The UK and Nigerian Construction IndustryDocumento12 pagineFactors Affecting The Success or Failure of Project Management Methodologies (PMM) Usage in The UK and Nigerian Construction IndustryGeorge PereiraNessuna valutazione finora
- 2001OxfEnc - Oxford Encyclopaedia of Ancient EgyptDocumento13 pagine2001OxfEnc - Oxford Encyclopaedia of Ancient EgyptDorrcolacNessuna valutazione finora
- PizzaOrder Assignment Working CodingDocumento3 paginePizzaOrder Assignment Working CodinginpreetkNessuna valutazione finora
- FM TransmitterDocumento15 pagineFM TransmitterMuhammad Aiman AmranNessuna valutazione finora
- IdentifyDocumento40 pagineIdentifyLeonard Kenshin LianzaNessuna valutazione finora
- SS 102 S5 - Final ExamDocumento3 pagineSS 102 S5 - Final ExamTabish HamidNessuna valutazione finora
- Using APpropriate LanguageDocumento25 pagineUsing APpropriate LanguageVerna Dell CorpuzNessuna valutazione finora
- LMC - Boundary Dispute CasesDocumento12 pagineLMC - Boundary Dispute CasesLR FNessuna valutazione finora
- Samsung Galaxy Beam GT I8530 User ManualDocumento172 pagineSamsung Galaxy Beam GT I8530 User ManualFirdaus AhmadNessuna valutazione finora
- Npcih IDocumento2 pagineNpcih IRoYaL RaJpOoTNessuna valutazione finora
- Guidelines: VSBK Design OptionDocumento60 pagineGuidelines: VSBK Design OptionChrisNessuna valutazione finora
- Cee 213 - Transport Principles in Environmental and Water Resources EngineeringDocumento3 pagineCee 213 - Transport Principles in Environmental and Water Resources EngineeringenjpetNessuna valutazione finora