Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
SOT Model Towards Peer To Peer System: Sjohnbee, B.Ranjith
Caricato da
ijcertDescrizione originale:
Titolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
SOT Model Towards Peer To Peer System: Sjohnbee, B.Ranjith
Caricato da
ijcertCopyright:
Formati disponibili
ISSN (Online): 2349-7084
GLOBAL IMPACT FACTOR 0.238
ISRA JIF 0.351
INTERNATIONAL JOURNAL OF COMPUTER ENGINEERING IN RESEARCH TRENDS
VOLUME 1, ISSUE 6, DECEMBER 2014, PP 409-413
SOT Model towards Peer to Peer System
1
1
S JOHN BEE , 2 B.RANJITH
M.Tech Research Scholar, Priyadarshini Institute of Technology and Science for Women
2
HOD-CSE, Priyadarshini Institute of Technology and Science for Women
Abstract:
In a peer-to-peer (P2P) network, each device assumes the part of Client and server in the meantime. In P2p framework, a
standout amongst the most essential issues is trust administration. P2P frameworks depend on different companions to
finish the undertakings. Companions need to trust one another for fruitful operation of the framework. While imparting in the
middle of companions trust development is paramount to take administration from the obscure asset. In this paper we think
over for four trust models focused around different methodologies, for example, by approaches, by notoriety and so forth.
Presently a large portion of models for trust administration are focused around notoriety. There are numerous models which
meets expectations under aforementioned methodologies out of these we have examined Eigen trust, SORT, Worldwide
Trust model and NICE. We have likewise analyzed four trust models in P2P frameworks. The examination is focused around
the profits and their properties.
Keywords: Peer-to-peer systems, trust management, reputation, and security
1. INTRODUCTION
Peer systems accomplish tasks by relying on
collaboration. P2P systems are exposed to security
threats, due to lack of central authority and dynamic in
nature. In case of secure environment, building up of
trust relationship can reduce the risk and reliable in
future interactions. The fundamental challenges for
peer-to-peer (P2P) systems is to manage the risks
involved in interaction and collaboration with priory
unknown and potentially malignant agents. In case of
malignant environment, establishing trust is a most
difficult task. Moreover, trust is a social phenomenon
i.e. firm belief in the reliability and difficult to measure
with numeric values. Benchmarks are needed to
symbolize trust. Ranking of peers is necessary so that
trustworthiness can be displayed based on metrics
defined.
The measurement of trust depends on interactions and
feedbacks of peers. Interactions with a peer provide
specific information but feedbacks might contain
illusive information. Peer to peer is a decentralized
network architecture in which each peer can act as a
server for sharing of resources. P2P systems can be
classified into two groups: unstructured and
structured. In unstructured P2P, a limited number of
connections are maintained by each peer to other
neighboring peers in the network. Searching in an
unstructured P2P environment leads to flooding
queries in the network. In structured P2P systems, a
hash function is used in order to couple keys with
objects. To hold the relevant objects, distributed hash
table (DHT) is used to route key-based queries
efficiently to peers.
Peer to Peer System
A peer-to-peer network is a type of decentralized and
distributed network architecture in which individual
nodes in the network act as both suppliers and
consumers of resources, in contrast to the centralized
clientserver model where client nodes request access
to resources provided by central servers. In this
network, tasks are shared amongst multiple
interconnected peers who make a portion of their
resources directly available to other network
participants, without the need for centralized
coordination by servers.
Below figure provides a conceptual representation of
the P2P overlay topology. In this, every machine plays
IJCERT2014
www.ijcert.org
409
ISSN (Online): 2349-7084
GLOBAL IMPACT FACTOR 0.238
ISRA JIF 0.351
INTERNATIONAL JOURNAL OF COMPUTER ENGINEERING IN RESEARCH TRENDS
VOLUME 1, ISSUE 6, DECEMBER 2014, PP 409-413
the role of client and server at the same time. Although
a P2P network has a number of advantages over the
traditional client-server model in terms of efficiency
and fault tolerance, additional security threats can be
introduced. Users and IT administrators need to be
aware of the risks from propagation of malicious code,
the legality of downloaded content, and vulnerabilities
within peer-to-peer software. Security and preventative
measures should be implemented to protect from any
potential leakage of sensitive information and possible
security breaches.
Fig. 1 P2P overlay topology
In this paper structured p2p is implemented, because
all the peers are organized into a clear logical overlay.
A novel trust model is proposed that intent to decrease
malignant activity in a P2P system by establishing trust
relations among peers in their contiguity. Local view of
trust is developed by its own based on the past
interaction. Thus, good peers form dynamic trust
groups in their contiguity and can isolate malignant
peers. In novel trust, at the beginning of the process the
peers are assumed to be strangers. Only after providing
a service, a peer becomes an acquaintance of another
peer e.g., file uploading. The peer chooses to trust
strangers if it has no acquaintance. Each peer has a set
of acquaintances, a subset of which is identified as its
neighbors. Using a service of a peer is an interaction,
which is evaluated based on priority, and recentness of
the interaction, and contentment of the requester. An
acquaintances
observation
about
a
peer,
recommendation,
is
calculated
based
on
recommenders
honesties.
It
contains
the
recommenders own experience about the peer, data
collected from the recommenders acquaintances, and
the recommenders confidence level in the suggestion.
If the confidence level is low, the recommendation has
a low value in evaluation. Novel defines three trust
metrics. Reputation metric represents the belief in the
system and allows parties to build trust, or the degree
to which one party has confidence in another within
the context of a given purpose or decision and is
calculated based on recommendations. The service
trust metric is used for selection of service providers.
The recommendation trust metric is needed when
requesting recommendations. When calculating
reputation metric, recommendations are evaluated
based on recommendation trust metric.
2. RELATED WORK
Trust model creation based on following trust
principles such as,
a) Trust is content-dependent.
b) Negative and positive belief is supported.
c) Trust is based on past experience.
d) Information exchange through recommendation.
e) Different opinions of all the agents are considered.
f) Recommendations may increase or decrease the trust
level [2].
Reputation is the opinion of the public towards a
person or organization or resources. In p2p, reputation
represents the opinions nodes and expectation about an
agents behavior based on data or observations of its
past behavior. In this, the users rate he reliability of
parties they deal with, and share this data with their
peers. Reputation trust identifies the malicious
responses from benign ones by using reputation of
peers provided by them.Peer s past transaction are
stored in trust vectors, which are of constant-length,
binary vector of l bit i.e. (8, 16, 32). A 1 bit represents an
honest transaction; 0 represents a dishonest one.
Reputation-based trust management properties:
a) No central coordination. No central database.
b) No peer has a global view of the system.
c) Global behavior emerges from local interactions.
d) Peers are autonomous.
e) Peers and connections are unreliable.
Two types of ratings are performed;
1. Trust rating
2. Distrust rating
Peer to peer information sharing environments are
increasingly gaining acceptance on the internet as they
provide an infrastructure in which the desired
information can be located and downloaded while
IJCERT2014
www.ijcert.org
410
ISSN (Online): 2349-7084
GLOBAL IMPACT FACTOR 0.238
ISRA JIF 0.351
INTERNATIONAL JOURNAL OF COMPUTER ENGINEERING IN RESEARCH TRENDS
VOLUME 1, ISSUE 6, DECEMBER 2014, PP 409-413
preserving the anonymity of both requestors and
providers. Reputation sharing is done based on a
distributed polling algorithm by which resource
requestors can assess the reliability of perspective
providers before initiating the download; also it keeps
the current level of anonymity of requestors and
providers, as well as that of the parties sharing their
view on others reputation *7+. In absence of central
database, manage trust in a peer-to-peer network is
tedious, which is based on binary trust values, i.e., a
peer is either trustworthy or not. In case a dishonest
transaction occurs, the peers can forward their
complaints to other peers. To store the complaints in a
peer-to-peer network, special data structures namely
the P-Grid are needed to be designed [8]. An agent uses
own experiences when building trust and does not
consider information of other agents [9]. Each peer
stores its own reputation using signed certificates. This
approach eliminates the need for reputation queries,
but it requires a public-key infrastructure [10].
An algorithm is introduced to classify users and assign
them roles based on trust relationships [11]. Reputation
systems are vulnerable to incorrect and false feedback
attacks. Thus feedback ratings must be based on goal
criteria [12].Trust and distrust metrics are defined. A
nonzero distrust value lets an agent to distinguish an
untreated user from a new user [13]. Reputation is been
used as a currency. A central agent issues money to
peers in return for their services to others. This money
can be used to get better quality of service [14]. A
history of interactions is stored and considers ratings
and recentness of interactions when evaluating trust.
Number of interactions with a peer is a measure of
confidence about the peer [15].
3. EXISTING TRUST MODELS IN PEER TO
PEER SYSTEM
There are many trust models, some are noted as
follows like,Global Trust, NICE, EIGENTRUST, SORT.
(Chen Ding,Jussi Kangasharju 2010, Hai Ren 2012)
Global Trust Model
This model is based on binary trust. In other words, an
agent could be either trustworthy or not. The
transactions are performed by the agents, and each of
them t (p, q) can be performed correctly or not. If there
is one agent p cheating within a transaction, the agent
will
become
from
the
global
perspective
untrustworthy. For distributing the information about
transactions agent, these information is forwarded by
agents to other agents. In this model, it is assumed that
the trust exists and malicious behavior is just
exceptions. If there is a malicious behavior of q, an
agent is able to file a complaint c(p,q). Firstly, lets
consider a simple situation. If there are two agents p
and q, they interact with each other very well. After for
a while, another agent r, which wants to get the
trustworthiness of p and q. As p, it is cheating, but q is
honest. After their interaction, the complaint about p
will be filed by q that is pretty fair. On the other side, p
will also do the similar thing as q does, so that to hide
its misbehavior. To an outside observer r, it cannot
distinguish whether p is honest or q is honest, it is very
hard for r to tell the truth. There is another new trouble
for P continues to cheat. p is a cheater which can be
distinguished in the following way.
Assume that, p is cheating in another interaction with
s. Then, agent r will detect that p complaint about q
and s. In contract, both q and s all complaint about p.
So we can get a conclusion, p is the cheater.
Generalizing the above idea by the below equation:
T(p) = ,|c(p,q)|q P}| |,c(q,p)|q 2 P}
The higher values of T(p), the trustworthy of p is lower.
4. NICE MODEL
In order to determine good peers in P2P system, and
establish steady cooperation with other peers, NICE
model is inspired in this background. This model is
used to guard against malicious peers. Each peer at the
ends of an interaction, creating a cookie with feedback
about the other peer assigns it. The signed cookies are
exchange among them. If the transaction is successful,
the value of the cookie is positive, otherwise, the value
is negative.
NICE model differs other models lively. For other
models, it is required for them to be in charge of the
requestor is trusted. For NICE model, if one peer wants
to request a certain data or other things. The peer can
just show the provider with a cookie signed by the
provider itself. The validity of the cookies provided
will be justified by the provider. If the cookie is right,
then, it is regarded as a evidence of the requestor peers
IJCERT2014
www.ijcert.org
411
ISSN (Online): 2349-7084
GLOBAL IMPACT FACTOR 0.238
ISRA JIF 0.351
INTERNATIONAL JOURNAL OF COMPUTER ENGINEERING IN RESEARCH TRENDS
VOLUME 1, ISSUE 6, DECEMBER 2014, PP 409-413
trustworthiness. Positive cookies will be exchanged by
interacting peers; negative cookies are retained by the
peer that creates it. To guarantee the negative cookies
are unhampered and available to other peers in the
system. To
Avoid any other attacks perpetrated by colluding
peers; the peers will create robust cooperative groups
with other good peers. In this way, every peer has a
preference list of good peers, and maintaining it based
on the past interaction history. At last peers are
removed which are having negative feedback cookies.
trustworthiness in providing services and giving
recommendations. Service trust is calculated on the
basis of the reputation, satisfaction and the
recommendation given by the other peers. SelfOrganizing Trust model that aims to decrease
malicious activity in a P2P system by establishing trust
relations among peers in their proximity. (Ahmet
Burak Can 2013)
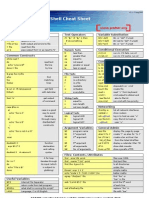
Fig 2 Directed graph with trust paths between peers.
Eigentrust
1 Recommendation request about Pj
This is distributed algorithm to decrease the number of
downloads of inauthentic files in a peer-to-peer file
sharing network that assigns each peer a unique global
trust value, based on the peers history of uploads.
Eigen Trust model is designed for the reputation
management of P2P system. The global reputation of
each peer i is marked by the local trust values assigned
to peer i by other peers, and it is weighted by the global
reputation of the assigned peers. For normalizing local
trust value Cij, the definition is as follow: Sij is meant
for each peer enable to store the number satisfactory
transactions it has had with peer j, and it is also meant
for the number of unsatisfactory transactions it has had
with peer
5. SOT
Self-Organizing Trust model that enables distribute
algorithms that allows a peer to reason about
trustworthiness of other peers based on past
interactions and recommendations. Peers create their
own trust network in their proximity by using local
information available and do not try to learn global
trust information. Two contexts of trust, service and
recommendation contexts are defined to measure
2 Recommendation of Pj
3 Service Request
4 Service
No a priori information or a trusted peer is used to
leverage trust establishment. Peers do not try to collect
trust information from all peers. Each peer develops its
own local view of trust about the peers interacted in
the past. In this way, good peers form dynamic trust
groups in their proximity and can isolate malicious
peers. Since peers generally tend to interact with a
small set of peers forming trust relations in proximity
of peers helps to mitigate attacks in a P2P system. SOT
models considerably behaves well by considering all
the parameters like efficient trust calculation but this
model has high computation cost due lot of calculation
of metrics. (Ahmet Burak Can 2013)
6. CONCLUSION
In P2P systems, it is important to detect the malicious
peers and harmful resources before a peer starts
downloading. Reputation-based trust management is
IJCERT2014
www.ijcert.org
412
ISSN (Online): 2349-7084
GLOBAL IMPACT FACTOR 0.238
ISRA JIF 0.351
INTERNATIONAL JOURNAL OF COMPUTER ENGINEERING IN RESEARCH TRENDS
VOLUME 1, ISSUE 6, DECEMBER 2014, PP 409-413
used to promote honest and cooperative behaviors, and
thus the overall credibility of the P2P network can be
maintained at an expected level. A trust model for P2P
networks is presented, in which a peer can develop a
trust network in its proximity. A peer can isolate
malicious peers around itself as it develops trust
relationships with good peers. Two context of trust,
service and recommendation contexts are defined to
measure capabilities of peers in providing services and
giving
recommendations.
Interactions
and
recommendations are considered with satisfaction,
weight,
and
fading
effect
parameters.
A
recommendation contains the recommenders own
experience, information from its acquaintances, and
level of confidence in the recommendation. These
parameters provided us a better assessment of
trustworthiness. We have studied various approaches
and models for trust management out of which SORT
model is quite better as compared to other models with
respect to performance and accuracy but only 1
drawback is that it has high computational and
communicational cost.
[6].Hai Ren(2006), Comparison of Trust Model in Peer
to Peer System, Helsinki University of Technology,
TKK T-110.5290 Seminar on Network Security.
REFERENCES
[11] E. Terzi, Y. Zhong, B. Bhargava, Pankaj, and S.
Madria,An Algorithm for Building User-Role Profiles
in a Trust Environment, Proc. Fourth Int l Conf. Data
Warehousing and Knowledge Discovery (DaWaK), vol.
2454, 2002.
[1]Ahmet
Burak Can, and Bharat Bhargava, (2013)
SORT: A SelfORganizing Trust Model for Peer-to-Peer
Systems,IEEE Transactions On Dependable And Secure
Computing, Vol. 10, No. 1.
[2]Chen Ding, Chen Yueguo, Cheng Weiwei(2012), EBook Of Trust Management in P2P Systems.Jussi
Kangasharju(2011), E-Book OfIntroduction Peer-toPeer
Networks.
[3] Gupta(2011). Peer-To-Peer Networks And
Computation:Current
Trends
And
Future
Perspectives,Computing And Informatics, Vol. 30, 559
594
[4]Stefan Saroiu, P. Krishna Gummadi, Steven
D.Gribble(2013) A Measurement Study of Peer-to-Peer
File Sharing Systems Dept. of Computer Science and
Engineering, Univ. of Washington, Seattle, WA, 981952350
[5]Loubna Mekouar(2005) Reputation-based Trust
Management
in
Peer-to-Peer
File
Sharing
Systems,University of Waterlo IEEE Consumer
Communications and Networking Conference (CCNC)
[7] F. Cornelli, E. Damiani, S.D.C. di Vimercati, S.
Paraboschi,and P. Samarati, Choosing Reputable
Servents in a P2P Network, Proc. 11th World Wide
Web Conf. (WWW), 2002.
*8+ K. Aberer and Z. Despotovic, Managing Trust in a
Peer-2-Peer Information System, Proc. 10th Int l Conf.
Information and Knowledge Management (CIKM),
2001.
[9] S. Marsh, Formalising Trust as a Computational
Concept.PhD thesis, Department of Mathematics and
Computer Science,University of Stirling, 1994.
[10] B. Ooi, C. Liau, and K. Tan, Managing trust in
peer-topeer
systems
using
reputation-based
techniques, in Proceedings of the 4th International
Conference on Web Age Information Management,
2003.
*12+ A. Jsang, R. Ismail, and C. Boyd, A Survey of
Trust and Reputation Systems for Online Service
Provision, Decision Support Systems, vol. 43, no. 2,
pp. 618-644, 2007.
[13] P. Victor, C. Cornelis, M. De Cock, and P. Pinheiro
da Silva, Gradual Trust and Distrust in Recommender
Systems, Fuzzy Sets Systems, vol. 160, no. 10, pp.
1367-1382, 2009.
*14+ M. Gupta, P. Judge, and M. Ammar, A Reputation
System for Peer-to-Peer Networks, Proc. 13th Int l
Workshop Network and Operating Systems Support
for Digital Audio and Video (NOSSDAV), 2003.
*15+ B. Yu, M.P. Singh, and K. Sycara, Developing
Trust in Large- Scale Peer-to-Peer Systems, Proc. IEEE
First Symp.Multi-Agent Security and Survivability,
2004.
IJCERT2014
www.ijcert.org
413
Potrebbero piacerti anche
- Mobile Agents in Networking and Distributed ComputingDa EverandMobile Agents in Networking and Distributed ComputingNessuna valutazione finora
- SOT Model Towards Peer To Peer SystemDocumento5 pagineSOT Model Towards Peer To Peer SystemIJCERT PUBLICATIONSNessuna valutazione finora
- An Efficient Trust Model For Peer-to-Peer NetworkDocumento4 pagineAn Efficient Trust Model For Peer-to-Peer NetworkInternational Journal of Application or Innovation in Engineering & ManagementNessuna valutazione finora
- A Self-Organizing Trust Model With Peer AcquaintanceDocumento5 pagineA Self-Organizing Trust Model With Peer AcquaintanceInternational Journal of Application or Innovation in Engineering & ManagementNessuna valutazione finora
- (IJCST-V4I3P64) :suyog Ashokrao Nagare, Prof. D.B. KshirsagarDocumento4 pagine(IJCST-V4I3P64) :suyog Ashokrao Nagare, Prof. D.B. KshirsagarEighthSenseGroupNessuna valutazione finora
- An Exaustive Survey of Trust Models in p2p NetworkDocumento12 pagineAn Exaustive Survey of Trust Models in p2p NetworkijwscNessuna valutazione finora
- A Reputation System Model Based On Indication To Combat Pollution in P2P NetworksDocumento6 pagineA Reputation System Model Based On Indication To Combat Pollution in P2P NetworksFabíola SoaresNessuna valutazione finora
- Trust Based Content Distribution For Peer-To-Peer Overlay NetworksDocumento12 pagineTrust Based Content Distribution For Peer-To-Peer Overlay NetworksAIRCC - IJNSANessuna valutazione finora
- SORT A Self ORganizing Trust Model For Peer To Peer SystemsDocumento4 pagineSORT A Self ORganizing Trust Model For Peer To Peer Systemsvikas11031992Nessuna valutazione finora
- P2P Reputation ManagementDocumento5 pagineP2P Reputation ManagementMuhammadMazidNessuna valutazione finora
- Paper-5 Analysis of Integrating External Trustworthiness Software & Study On Information Retrieval SystemsDocumento8 paginePaper-5 Analysis of Integrating External Trustworthiness Software & Study On Information Retrieval SystemsRachel WheelerNessuna valutazione finora
- Purging of Untrustworthy Recommendations From A GridDocumento9 paginePurging of Untrustworthy Recommendations From A GridijngnNessuna valutazione finora
- Powertrust: A Robust and Scalable Reputation System For Trusted Peer-To-Peer ComputingDocumento14 paginePowertrust: A Robust and Scalable Reputation System For Trusted Peer-To-Peer ComputingjasonwNessuna valutazione finora
- Vol2no8 1Documento11 pagineVol2no8 1Managing Editor Journal of ComputingNessuna valutazione finora
- Ensuring Security in Peer To Peer NetworksDocumento14 pagineEnsuring Security in Peer To Peer NetworksIsaac NabilNessuna valutazione finora
- A Reputation-Based Trust Model - 2003Documento12 pagineA Reputation-Based Trust Model - 2003Moh SaadNessuna valutazione finora
- T M R: A: Rust Etrics in Ecommender Systems SurveyDocumento12 pagineT M R: A: Rust Etrics in Ecommender Systems Surveyacii journalNessuna valutazione finora
- Financial Risk Governance RiskDocumento5 pagineFinancial Risk Governance RiskShidrokh GoudarziNessuna valutazione finora
- A Reputation-Based Trust Model For Peer-To-Peer Ecommerce CommunitiesDocumento13 pagineA Reputation-Based Trust Model For Peer-To-Peer Ecommerce CommunitiesNthambi MiriamNessuna valutazione finora
- Security in Distributed Systems: First Shipra Varshney, Second Jaya Kumari VermaDocumento6 pagineSecurity in Distributed Systems: First Shipra Varshney, Second Jaya Kumari VermaShipra Kumar VarshneyNessuna valutazione finora
- Gain Factor Trust A Trust Evaluation Framework in Online Social Networks PDFDocumento3 pagineGain Factor Trust A Trust Evaluation Framework in Online Social Networks PDFeditorinchiefijcsNessuna valutazione finora
- Golbeck2006 Chapter CombiningProvenanceWithTrustIn PDFDocumento8 pagineGolbeck2006 Chapter CombiningProvenanceWithTrustIn PDFLakshit ChughNessuna valutazione finora
- Spamex Report PlasuryanuragDocumento63 pagineSpamex Report PlasuryanuragSudipto Kumar DasNessuna valutazione finora
- Gupta2021 Article TrustEstimationInPeer-to-peerNDocumento10 pagineGupta2021 Article TrustEstimationInPeer-to-peerNNikhil SharmaNessuna valutazione finora
- Dynamic, Privacy-Preserving Decentralized Reputation SystemsDocumento12 pagineDynamic, Privacy-Preserving Decentralized Reputation SystemsjasonwNessuna valutazione finora
- Filmtrust: Movie Recommendations Using Trust in Web-Based Social NetworksDocumento5 pagineFilmtrust: Movie Recommendations Using Trust in Web-Based Social NetworkszeeshanNessuna valutazione finora
- PID1349855Documento7 paginePID1349855kieraNessuna valutazione finora
- A Quantifiable Trust Model For Blockchain-Based Identity ManagementDocumento8 pagineA Quantifiable Trust Model For Blockchain-Based Identity ManagementKiran Kumar ReddyNessuna valutazione finora
- Al Oufi2012Documento9 pagineAl Oufi2012Ishita GuptaNessuna valutazione finora
- Neighbor Node Discovery and Verification Using Trust Prediction in Mobile Ad Hoc NetworksDocumento31 pagineNeighbor Node Discovery and Verification Using Trust Prediction in Mobile Ad Hoc NetworksSuganyadevi SubramaniamNessuna valutazione finora
- Managing Trust in A Peer-2-Peer Information System : Karl Aberer, Zoran DespotovicDocumento8 pagineManaging Trust in A Peer-2-Peer Information System : Karl Aberer, Zoran DespotovicfrancisleunggieNessuna valutazione finora
- Dokumen - Tips Cs6703 Grid and Cloud Computing Unit 5Documento69 pagineDokumen - Tips Cs6703 Grid and Cloud Computing Unit 5Suban RavichandranNessuna valutazione finora
- A Deep Learning Based TrustDocumento22 pagineA Deep Learning Based TrustfaniNessuna valutazione finora
- Hybrid Trust Model For Internet RoutingDocumento12 pagineHybrid Trust Model For Internet RoutingAIRCC - IJCNCNessuna valutazione finora
- A Trust Based and Time Influenced Similarity Computation Method For Collaborative FilteringDocumento10 pagineA Trust Based and Time Influenced Similarity Computation Method For Collaborative FilteringDocukitsNessuna valutazione finora
- 1 s2.0 S0925231221017410 MainDocumento15 pagine1 s2.0 S0925231221017410 MainAbdelkarim GhanemNessuna valutazione finora
- Oghma - Peer 2 Peer Secure MediaDocumento8 pagineOghma - Peer 2 Peer Secure MediaJournal of Computer Science and EngineeringNessuna valutazione finora
- A Hybrid Trust Evaluation Framework For E-Commerce in Online Social Network: A Factor Enrichment PerspectiveDocumento17 pagineA Hybrid Trust Evaluation Framework For E-Commerce in Online Social Network: A Factor Enrichment PerspectiveajithNessuna valutazione finora
- Module 3 - Building Peer Networks and Essentials of CommunicationDocumento16 pagineModule 3 - Building Peer Networks and Essentials of Communication9743081454Nessuna valutazione finora
- CORE: A Collaborative Reputation Mechanism To Enforce Node Cooperation in Mobile Ad Hoc NetworksDocumento18 pagineCORE: A Collaborative Reputation Mechanism To Enforce Node Cooperation in Mobile Ad Hoc Networksjasmina2468Nessuna valutazione finora
- CARTADocumento16 pagineCARTAtnhphuongNessuna valutazione finora
- Develop A Computational Trust Prototype For The Semantic WebDocumento7 pagineDevelop A Computational Trust Prototype For The Semantic WebMarco Antonio Mendoza RodriguezNessuna valutazione finora
- P2P and Grid ComputingDocumento6 pagineP2P and Grid ComputingMumit Shawlin UchchhwasNessuna valutazione finora
- Trusted Based NW ProtocolDocumento6 pagineTrusted Based NW Protocolnkr1Nessuna valutazione finora
- A Friend Recommendation Algorithm Based On Social Network TrustDocumento5 pagineA Friend Recommendation Algorithm Based On Social Network Trustanil kasotNessuna valutazione finora
- International Journal of Engineering Research and Development (IJERD)Documento6 pagineInternational Journal of Engineering Research and Development (IJERD)IJERDNessuna valutazione finora
- Secure Information Sharing in Digital Supply Chains: Bharat Bhargava and Rohit RanchalDocumento16 pagineSecure Information Sharing in Digital Supply Chains: Bharat Bhargava and Rohit RanchalHadi UtomoNessuna valutazione finora
- Trustworthiness Inference Framework in The Social Internet of Things A Context-Aware ApproachDocumento9 pagineTrustworthiness Inference Framework in The Social Internet of Things A Context-Aware ApproachMeriem Chiraz ZouzouNessuna valutazione finora
- Trust-Based Recommendation: An Empirical Analysis: Daire O'Doherty Salim Jouili Peter Van RoyDocumento9 pagineTrust-Based Recommendation: An Empirical Analysis: Daire O'Doherty Salim Jouili Peter Van RoyDocukitsNessuna valutazione finora
- Searching Social NetworksDocumento8 pagineSearching Social NetworksoreskeNessuna valutazione finora
- Calculating Trust Value in Information Propagation For Online Social Network SitesDocumento5 pagineCalculating Trust Value in Information Propagation For Online Social Network SiteserpublicationNessuna valutazione finora
- DocDocumento68 pagineDocSushma GajjalaNessuna valutazione finora
- Trust Management System For Semantic Web: Rp5g09@ecs - Soton.ac - UkDocumento4 pagineTrust Management System For Semantic Web: Rp5g09@ecs - Soton.ac - UkRaman PalNessuna valutazione finora
- In Uencing Factors On The Lending Intention of Online Peer-to-Peer LendingDocumento33 pagineIn Uencing Factors On The Lending Intention of Online Peer-to-Peer LendinggitaNessuna valutazione finora
- Cloud Computing KeyDocumento9 pagineCloud Computing KeyDu Lịch Việt Nam Npops Viet NamTravelNessuna valutazione finora
- Constellation Network: PRO Consensus OverviewDocumento3 pagineConstellation Network: PRO Consensus OverviewSethVNessuna valutazione finora
- The Impact of Trustworthiness in The Dating App Experience: A Trust-Inducing Model ProposalDocumento14 pagineThe Impact of Trustworthiness in The Dating App Experience: A Trust-Inducing Model ProposalHoai Thao Van PhamNessuna valutazione finora
- SSRN Id3769854Documento8 pagineSSRN Id3769854whitneykarundeng08Nessuna valutazione finora
- Deep Matrix Factorization For Trust-Aware Recommendation in Social NetworksDocumento18 pagineDeep Matrix Factorization For Trust-Aware Recommendation in Social NetworksAbdelkarim GhanemNessuna valutazione finora
- Weighted Coefficient Firefly Optimization Algorithm and Support Vector Machine For Trust Model and Link ReliabilityDocumento16 pagineWeighted Coefficient Firefly Optimization Algorithm and Support Vector Machine For Trust Model and Link ReliabilityAIRCC - IJCNCNessuna valutazione finora
- Revolution of Storms From Vendor Lock-In To The Data StorageDocumento6 pagineRevolution of Storms From Vendor Lock-In To The Data StorageijcertNessuna valutazione finora
- Exigent Life From Wireless Ad-Hoc Signal NetworksDocumento8 pagineExigent Life From Wireless Ad-Hoc Signal NetworksijcertNessuna valutazione finora
- New Design and Achievement of IPTV Service Delivery Through VirtualizationDocumento7 pagineNew Design and Achievement of IPTV Service Delivery Through VirtualizationijcertNessuna valutazione finora
- Entrustment of Access Control in Public Clouds: A.Naga Bala, D.RavikiranDocumento7 pagineEntrustment of Access Control in Public Clouds: A.Naga Bala, D.RavikiranijcertNessuna valutazione finora
- EAACK: Secure IDS For Wireless Sensor Networks: AbstractDocumento9 pagineEAACK: Secure IDS For Wireless Sensor Networks: AbstractijcertNessuna valutazione finora
- Design of Low Power TPG With LP-LFSR: AbstractDocumento5 pagineDesign of Low Power TPG With LP-LFSR: AbstractijcertNessuna valutazione finora
- PandasDocumento1.349 paginePandasMichael GemminkNessuna valutazione finora
- DFL-Series, Configuración VPNDocumento102 pagineDFL-Series, Configuración VPNLuis Diego Salas QuesadaNessuna valutazione finora
- Online QuizDocumento25 pagineOnline QuizJyotiiBubnaRungta100% (1)
- New Integration New RBSDocumento12 pagineNew Integration New RBSabhinav100% (1)
- Simotion New Features V531 ENDocumento13 pagineSimotion New Features V531 ENGener TzabNessuna valutazione finora
- Data PreprocessingDocumento22 pagineData PreprocessingDinh Duy HiepNessuna valutazione finora
- It1304 2013Documento12 pagineIt1304 2013Har JayasingheNessuna valutazione finora
- Hierarchical Model The Hierarchical Data Model Organizes Data in A Tree StructureDocumento6 pagineHierarchical Model The Hierarchical Data Model Organizes Data in A Tree Structureshail_pariNessuna valutazione finora
- Sabertooth 990FX R20 Memory QVLDocumento3 pagineSabertooth 990FX R20 Memory QVLCarlos Gabriel Sierra JeldresNessuna valutazione finora
- Barcode Recognition System (Second Seminar)Documento13 pagineBarcode Recognition System (Second Seminar)Alex WunnaNessuna valutazione finora
- Reverse A Linked List - GeeksforGeeksDocumento14 pagineReverse A Linked List - GeeksforGeekscaiosilvaazeredo_443Nessuna valutazione finora
- Computer Science TestDocumento13 pagineComputer Science TestmvanwetteringNessuna valutazione finora
- Elau SX-1 Servo DriveDocumento170 pagineElau SX-1 Servo Driveanon_6032832230% (1)
- Ansi Iso 9075 1 1999 PDFDocumento85 pagineAnsi Iso 9075 1 1999 PDFMark Joseph BalaresNessuna valutazione finora
- Fortisiem 4.10.0 User GuideDocumento555 pagineFortisiem 4.10.0 User GuideLuca Andreoli50% (2)
- Web Services Security: SOAP Message Security 1.1 (WS-Security 2004)Documento76 pagineWeb Services Security: SOAP Message Security 1.1 (WS-Security 2004)Uday KumarNessuna valutazione finora
- Chapter 4 Memory ElementDocumento87 pagineChapter 4 Memory ElementWann FarieraNessuna valutazione finora
- Bash Script Cheat SheetDocumento1 paginaBash Script Cheat SheetHardeep Singh100% (1)
- Certified Ethical Hacker Exam PDFDocumento253 pagineCertified Ethical Hacker Exam PDFsdbvjasbNessuna valutazione finora
- C++ Project On Banking Management System BEL320,319,322,323Documento7 pagineC++ Project On Banking Management System BEL320,319,322,323KRST100% (4)
- RANAP Location Reporting Control MessageDocumento1 paginaRANAP Location Reporting Control MessageTAOUACHINessuna valutazione finora
- Designing Reusable Frameworks For Test AutomationDocumento35 pagineDesigning Reusable Frameworks For Test Automationmunna102Nessuna valutazione finora
- Python QuestionaireDocumento4 paginePython QuestionaireRaghuvaran100% (1)
- Photoshop MCQ Questions and AnswersDocumento9 paginePhotoshop MCQ Questions and AnswersRajeev Vadakkedath77% (13)
- Compuware APM Almanac 2012Documento401 pagineCompuware APM Almanac 2012vikrms1978Nessuna valutazione finora
- Mutillidae Test ScriptsDocumento27 pagineMutillidae Test ScriptsÁlvaro Riobóo de LarrivaNessuna valutazione finora
- Microprocessors LAB MANUALDocumento55 pagineMicroprocessors LAB MANUALsujathaNessuna valutazione finora
- 5 Working With DB2 ObjectsDocumento21 pagine5 Working With DB2 ObjectsrupikavalikiNessuna valutazione finora
- Windows 7 Ultimate Product Key Free For You - Apps For WindowsDocumento5 pagineWindows 7 Ultimate Product Key Free For You - Apps For WindowsmustafaNessuna valutazione finora
- AWS NotesDocumento32 pagineAWS Notespavankalluri100% (6)