Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Computer Audit
Caricato da
Jubert Padilla0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
143 visualizzazioni9 pagineaudit
Copyright
© © All Rights Reserved
Formati disponibili
DOCX, PDF, TXT o leggi online da Scribd
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoaudit
Copyright:
© All Rights Reserved
Formati disponibili
Scarica in formato DOCX, PDF, TXT o leggi online su Scribd
0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
143 visualizzazioni9 pagineComputer Audit
Caricato da
Jubert Padillaaudit
Copyright:
© All Rights Reserved
Formati disponibili
Scarica in formato DOCX, PDF, TXT o leggi online su Scribd
Sei sulla pagina 1di 9
Computer-aided audit tools
From Wikipedia, the free encyclopedia
This article is written like a personal reflection or opinion essay rather than an
encyclopedic description of the subject. Pleasehelp improve it by rewriting it in
an encyclopedic style. (August 2009)
'Computer-assisted audit techniques (CAATs) or computer-assisted audit tools and techniques (CAATTs) is a
growing field within the audit profession. CAATs is the practice of using computers to automate the audit
process. CAATs normally includes using basic office productivity software such as spreadsheet, word
processors and text editing programs and more advanced software packages involving use statistical
analysis and business intelligence tools. But also more dedicated specialized software are available (see
below).
CAATs have become synonymous with data analytics in the audit process.
Contents
[hide]
1 Traditional auditing vs CAATs
o 1.1 Traditional audit example
o 1.2 CAATTs alternative
o 1.3 Traditional audit vs CAATTs on specific risks
2 Specialized software
3 Other uses of CAATs
o 3.1 Creation of electronic work papers
o 3.2 Fraud detection
o 3.3 Analytical tests
o 3.4 Data analysis reports
o 3.5 Continuous monitoring
o 3.6 Curb stoning in surveys
o 3.7 Note on the acronyms CAATTs vs CAATs
4 See also
5 External links
6 References
Traditional auditing vs CAATs[edit]
Traditional audit example[edit]
The traditional method of auditing allows auditors to build conclusions based upon a limited sample of a
population, rather than an examination of all available or a large sample of data. The use of small samples may
diminish the validity of audit conclusions. Management realizes that they conduct thousands or perhaps
millions of transactions a year and the auditor only sampled a handful. The auditor will then state that they
conducted the sample based upon generally accepted audit standards (GAAS) and that their sample was
statistically valid.
Another common criticism of the audit profession occurs after a problem emerges. Whenever a problem
emerges within a department, management might ask, "Where were the auditors?" This is a futile question,
because nobody can see beyond the present.
CAATTs alternative[edit]
CAATTs, not CAATs, addresses these problems. CAATTs, as it is commonly used, is the practice of analyzing
large volumes of data looking for anomalies. A well designed CAATTs audit will not be a sample, but rather a
complete review of all transactions. Using CAATTs the auditor will extract every transaction the business unit
performed during the period reviewed. The auditor will then test that data to determine if there are any
problems in the data. For example, using CAATTs the auditor can find invalid Social Security Numbers (SSN)
by comparing the SSN to the issuing criteria of the social security administration. The CAATTs auditor could
also easily look for duplicate vendors or transactions. When such a duplicate is identified, they can approach
management with the knowledge that they tested 100% of the transactions and that they identified 100% of the
exceptions.
Traditional audit vs CAATTs on specific risks[edit]
Another advantage of CAATs is that it allows auditors to test for specific risks. For example, an insurance
company may want to ensure that it doesn't pay any claims after a policy is terminated. Using traditional audit
techniques this risk would be very difficult to test. The auditor would "randomly select" a "statistically valid"
sample of claims (usually 3050.) They would then check to see if any of those claims were processed after a
policy was terminated. Since the insurance company might process millions of claims the odds that any of
those 3050 "randomly selected" claims occurred after the policy was terminated is extremely unlikely.
Using CAATTs the auditor can select every claim that had a date of service after the policy termination date.
The auditor then can determine if any claims were inappropriately paid. If they were, the auditor can then figure
out why the controls to prevent this failed. In a real life audit, the CAATTs auditor noted that a number of claims
had been paid after policies were terminated. Using CAATTs the auditor was able to identify every claim that
was paid and the exact dollar amount incorrectly paid by the insurance company. Furthermore, the auditor was
able to identify the reason why these claims were paid. The reason why they were paid was because the
participant paid their premium. The insurance company, having received a payment, paid the claims. Then after
paying the claim the participant's check bounced. When the check bounced, the participant's policy was
retrospectively terminated, but the claim was still paid costing the company hundreds of thousands of dollars
per year.
Which looks better in an audit report:
"Audit reviewed 50 transactions and noted one transaction that was processed incorrectly"
or
"Audit used CAATTs and tested every transaction over the past year. We noted XXX exceptions wherein the
company paid YYY dollars on terminated policies."
However, the CAATTs driven review is limited only to the data saved on files in accordance with a systematic
pattern. Much data is never documented this way. In addition saved data often contains deficiencies, is poorly
classified, is not easy to get, and it might be hard to become convinced about its integrity. So, for the present
CAATTs is complement to an auditor's tools and techniques. In certain audits CAATTs can't be used at all. But
there are also audits which simply can't be made with due care and efficiently without CAATTs.
Specialized software[edit]
In the most general terms, CAATTs can refer to any computer program utilized to improve the audit process.
Generally, however, it is used to refer to any data extraction and analysis software. This would include
programs such as spreadsheets (e.g. Excel), databases (e.g. Access), statistical analysis (e.g. SAS), business
intelligence (e.g. Crystal Reports and Business Objects), etc.
Benefits of audit software include:
They are independent of the system being audited and will use a read-only copy of the file to avoid any
corruption of an organizations data.
Many audit-specific routines are used such as sampling.
Provides documentation of each test performed in the software that can be used as documentation in the
auditors work papers.
Audit specialized software may perform the following functions:
Data queries.
Data stratification.
Sample extractions.
Missing sequence identification.
Statistical analysis.
Calculations.
Duplicated transactions.
Pivot tables.
Cross tabulation.
Other uses of CAATs[edit]
In addition to using data analysis software, the auditor uses CAATs throughout the audit for the following
activities while performing data analysis:
Creation of electronic work papers[edit]
Keeping electronic work papers on a centralized audit file or database will allow the auditor to navigate through
current and archived working papers with ease. The database will make it easier for auditors to coordinate
current audits and ensure they consider findings from prior or related projects. Additionally, the auditor will be
able to electronically standardize audit forms and formats, which can improve both the quality and consistency
of the audit working papers.
Fraud detection[edit]
CAATs provides auditors with tools that can identify unexpected or unexplained patterns in data that may
indicate fraud. Whether the CAATs is simple or complex, data analysis provides many benefits in the
prevention and detection of fraud.
CAATs can assist the auditor in detecting fraud by performing and creating the following,
Analytical tests[edit]
Evaluations of financial information made by studying plausible relationships among both financial and non-
financial data to assess whether account balances appear reasonable (AU 329). Examples include ratio, trend,
and Benford's Law tests.
Data analysis reports[edit]
Reports produced using specific audit commands such as filtering records and joining data files.
Continuous monitoring[edit]
Continuous monitoring is an ongoing process for acquiring, analyzing, and reporting on business data to
identify and respond to operational business risks. For auditors to ensure a comprehensive approach to
acquire, analyze, and report on business data, they must make certain the organization continuously monitors
user activity on all computer systems, business transactions and processes, and application controls.
Curb stoning in surveys[edit]
Curb stoning is the term for instances where a surveyor completes a survey form by making up data. Because
some of the data should conform with Benford's law, this practice can be detected using CAATTs which
provide the capability of performing such tests.
Note on the acronyms CAATTs vs CAATs[edit]
CAATTs and CAATs are used interchangeably. While CAATs has emerged as the more common spelling,
CAATTs is the more precise acronym. The acronym CAATTs solves one of the two problems with defining the
acronym. CAATs means:
Computer Aided (or Assisted) Audit Techniques (or Tools and Techniques)
The first "A" and the "T" can have two different meanings depending on who uses the term. By using the term
CAATTs, one is clearly incorporating both "Tools" AND "Techniques."
See also[edit]
Comparison of specialized computer-aided audit tools
Generalized audit software
Information technology audit
Separation of duties
Information Systems Audit and Security
()
Instructor: LihChyun Shu (shulc@mail.ncku.edu.tw)
Course objective
In recent years, information technology (IT) has inspired the reengineering of
traditional business operations. As global networks expand the interconnection
of the world, the smooth operation of communication and computing systems
becomes vital. The immediate need for organizations to protect critical
information continues to increase. IT advances have introduced new risks* that
require unique internal controls and also have had great influences on auditing.
In this course, we will first present an overview of information systems audit (or
information technology autid). We then discuss alternative audit approaches
and review the internal control concerns.
We will give a basic introduction to the broader field of information security,
defining key terms and explaining essential concepts. Will then examine the
business drivers behind the security analysis design process. We will look into
key laws that shape the field of information security, as well as computer ethics
necessary to better educate those implementing security. We then study key
areas of potential computer risk. An overview of relevant technology and
systems issues will also be provided. Finally, students will learn to use computer
assisted audit tools in order to have a hands-on experience.
*Risk: danger; possibility that something harmful or undesirable may happen.
(Longman dictionary of contemporary English)
Course content
1. Auditing, Assurance, and Internal Control
2. Computer Assisted Audit Tools and Technologies (CAATT)
3. CAATTs for Data Extraction and Analysis
4. Introduction to Information Security
5. The Need for Security
6. Legal, Ethical and Professional Issues in Information Security
7. Risk Management: Identifying and Assessing Risk
8. Risk Management: Assessing and Controlling Risk
9. Blueprint for Security
Texts:
James A. Hall. Information Systems Auditing and Assurance, South Western
College Publishing, 1999.
Michael E. Whitman and Herbert J. Mattord. Principles of Information
Security, Thomson Course Technology, 3rd Ed., 2008.
Course slides:
Auditing, assurance, internal control (Chap1 of Hall 99) Relevant links
Computer assisted audit tools and techniques (Chap 6 of Hall
99) 1 2 Relevant links
CAATTs for Data Extraction and Analysis (Chap 7 of Hall 99) Relevant links
Introduction to information security (Chap 1 of Whitman & Mattord
'03) Relevant links Info security related news
The need for security (Chap 2 of Whitman & Mattord '03) Relevant links
Risk management: identifying and assessing risk (Chap 4 of Whitman &
Mattord '03) Relevant links
Risk management: assessing and controlling risk (Chap 5 of Whitman &
Mattord '03)
Supplemental slides:
(slides talk by )
In-class presentation by students
Exercises
Evaluation (subject to change):
Class participation (5%)
Exercises (37%)
Exam (20%)
Case discussion (8%)
Book chapter/paper oral and written presentation (30%)
Links:
Illustrative Risks to the Public in the Use of Computer Systems and Related
Technology (Risks-illustrative.pdf)
Risks-List: Risk-Forum Digest
Software Engineering Notes
Sarbanes-Oxley Act on Computerworld Financial law may force IT
systems overhaul Sarbanes-Oxley Act (Wiki)
The University of Waterloo Centre for Information Systems Assurance
Hawaii International Conference on System Sciences
Journal of Information Systems (accessible via NCKU-Journal)
International Journal of Accounting Information Systems (accessible
via NCKU-Journal)
CNS 17799 CNS 17800
Why Information Security is Hard -- An Economic Perspective (Ross Anderson) Orange Book
Summary
Potrebbero piacerti anche
- Computer Aided Audit ToolsDocumento8 pagineComputer Aided Audit ToolsRahul GargNessuna valutazione finora
- A 6.4 Audit Unit 6Documento8 pagineA 6.4 Audit Unit 6Gaurav MahajanNessuna valutazione finora
- Computer Assisted Audit ToolsDocumento41 pagineComputer Assisted Audit ToolsLaiza Mechelle Roxas MacaraigNessuna valutazione finora
- CaatDocumento2 pagineCaatkarannathaniNessuna valutazione finora
- Computer Assisted Audit TechniquesDocumento5 pagineComputer Assisted Audit TechniquesMuhammad JawadNessuna valutazione finora
- IT AuditDocumento4 pagineIT AuditBryanNessuna valutazione finora
- Bit006 Accounting Information Systemcontrol&Substantive TestingDocumento4 pagineBit006 Accounting Information Systemcontrol&Substantive TestingGabriel PatronNessuna valutazione finora
- Using CAATs To Support IS AuditDocumento3 pagineUsing CAATs To Support IS AuditJerome B. AgliamNessuna valutazione finora
- Audit Command LanguageDocumento12 pagineAudit Command LanguageFrensarah RabinoNessuna valutazione finora
- Computer-Assisted Audit Techniques (CAATs)Documento5 pagineComputer-Assisted Audit Techniques (CAATs)Esther WanjukiNessuna valutazione finora
- Data Analysis Software: I S C J, V 1, 2 0 0 3Documento6 pagineData Analysis Software: I S C J, V 1, 2 0 0 3Rina Agustina ManikNessuna valutazione finora
- Using CAATs To Support Is AuditDocumento3 pagineUsing CAATs To Support Is AuditrasmaheeNessuna valutazione finora
- Using Caats To Support Is Audit: PolivirtualDocumento2 pagineUsing Caats To Support Is Audit: PolivirtualMauricio Argel Ruíz CabañasNessuna valutazione finora
- 4 - Computer Assisted Auditing Techniques (CAAT)Documento3 pagine4 - Computer Assisted Auditing Techniques (CAAT)gimata kochomataNessuna valutazione finora
- Write Up On Audit TrailDocumento14 pagineWrite Up On Audit Trailcrown oked100% (1)
- System Audit: Foundations of Information System AuditingDocumento4 pagineSystem Audit: Foundations of Information System AuditingmercatuzNessuna valutazione finora
- Computer Assisted Audit Tools Chap-04Documento30 pagineComputer Assisted Audit Tools Chap-04I-am KumNessuna valutazione finora
- Financial Audit Report 1Documento2 pagineFinancial Audit Report 1Honourable FunloveNessuna valutazione finora
- CPA Journal-Continuous AuditingDocumento3 pagineCPA Journal-Continuous AuditingPaul Ryan BalonNessuna valutazione finora
- Impact of SAS No. 94 On Computer Audit TechniquesDocumento5 pagineImpact of SAS No. 94 On Computer Audit TechniquesJerome B. AgliamNessuna valutazione finora
- Chapter 8 "RICK HAYES" "Analytical Procedures"Documento15 pagineChapter 8 "RICK HAYES" "Analytical Procedures"Joan AnindaNessuna valutazione finora
- Preliminary ReviewDocumento6 paginePreliminary ReviewLet it beNessuna valutazione finora
- Internal Auditing ProjectDocumento8 pagineInternal Auditing ProjectvafratisNessuna valutazione finora
- Internal Auditing ProjectDocumento8 pagineInternal Auditing ProjectvafratisNessuna valutazione finora
- Awareness Session On: Computer-Assisted Audit Tools and Techniques"Documento22 pagineAwareness Session On: Computer-Assisted Audit Tools and Techniques"Sunil Kumar PatroNessuna valutazione finora
- The Importance of Continuous Audit and Real Time DisclosureDocumento8 pagineThe Importance of Continuous Audit and Real Time DisclosurePrateik RyukiNessuna valutazione finora
- Auditing: Submitted By:-Kajol Setia (H) IV-B A7004618039Documento7 pagineAuditing: Submitted By:-Kajol Setia (H) IV-B A7004618039Kajol SethiNessuna valutazione finora
- Continuous AuditingDocumento2 pagineContinuous AuditingHasan Barlaas0% (1)
- IAASB-FAQ-Automated-Tools-Techniques Sept 2020Documento7 pagineIAASB-FAQ-Automated-Tools-Techniques Sept 2020Daniel GarciaNessuna valutazione finora
- GTAG 04 - Management of IT Auditing 2nd Edition PDFDocumento20 pagineGTAG 04 - Management of IT Auditing 2nd Edition PDFton rNessuna valutazione finora
- Data AnalyticsDocumento25 pagineData AnalyticsElla GraceNessuna valutazione finora
- CAAT Commonwealth of Massachusetts Department of RevenueDocumento9 pagineCAAT Commonwealth of Massachusetts Department of Revenueoseng2mercon2010Nessuna valutazione finora
- Thesis Audit TrailDocumento4 pagineThesis Audit TrailBuyingCollegePapersSingapore100% (2)
- Continuous IT Compliance:: A Stepwise Approach To Effective AssuranceDocumento6 pagineContinuous IT Compliance:: A Stepwise Approach To Effective AssurancePadmavijayanNessuna valutazione finora
- Information Systems Auditing: The IS Audit Testing ProcessDa EverandInformation Systems Auditing: The IS Audit Testing ProcessValutazione: 1 su 5 stelle1/5 (1)
- Philippine Auditing Practices Statements (PAPS) 1009 Computer Assisted Audit TechniquesDocumento9 paginePhilippine Auditing Practices Statements (PAPS) 1009 Computer Assisted Audit Techniqueserjan nina bombayNessuna valutazione finora
- Cse 4502 Computer Auditing: Group Assignment Group 7 "Computer Auditing in A Glance" Name Matric NoDocumento11 pagineCse 4502 Computer Auditing: Group Assignment Group 7 "Computer Auditing in A Glance" Name Matric NoJaja TihaNessuna valutazione finora
- Chapter 4Documento51 pagineChapter 4Ralph AvakianNessuna valutazione finora
- Auditing Information Systems: Enhancing Performance of the EnterpriseDa EverandAuditing Information Systems: Enhancing Performance of the EnterpriseNessuna valutazione finora
- Ch17 James HallDocumento8 pagineCh17 James HallThessaloe B. FernandezNessuna valutazione finora
- IS Auditor - Process of Auditing: Information Systems Auditor, #1Da EverandIS Auditor - Process of Auditing: Information Systems Auditor, #1Nessuna valutazione finora
- Details: Test DataDocumento3 pagineDetails: Test DataNisrina NSNessuna valutazione finora
- Accounting Information Systems The Processes Controls 2nd Edition Turner Solutions ManualDocumento13 pagineAccounting Information Systems The Processes Controls 2nd Edition Turner Solutions Manualmrsamandareynoldsiktzboqwad100% (26)
- Chapter 5 - Auditing Information Technology-Based ProcessesDocumento4 pagineChapter 5 - Auditing Information Technology-Based ProcessesMichael AnibanNessuna valutazione finora
- Data AnalyticsDocumento5 pagineData AnalyticsMayal AhmedNessuna valutazione finora
- AUDITINGDocumento4 pagineAUDITINGArj Sulit Centino DaquiNessuna valutazione finora
- Data Analytics For External Auditors: What Data Analytics Can Do and How It Contributes To Audit QualityDocumento6 pagineData Analytics For External Auditors: What Data Analytics Can Do and How It Contributes To Audit QualityGeorgia VasanthaNessuna valutazione finora
- CH 07Documento11 pagineCH 07Hussein AlkhafagiNessuna valutazione finora
- 123 AuditDocumento5 pagine123 AuditFelicia RedondoNessuna valutazione finora
- CP 6Documento32 pagineCP 6prem kumar reddyNessuna valutazione finora
- How It's Changing AuditingDocumento2 pagineHow It's Changing Auditingkhushboosingh25junNessuna valutazione finora
- INFORMATIONS SYSTEMS AUDIT NOTES MucheluleDocumento59 pagineINFORMATIONS SYSTEMS AUDIT NOTES MuchelulevortebognuNessuna valutazione finora
- ACL and ComplianceDocumento5 pagineACL and ComplianceJhonatan EleraNessuna valutazione finora
- Audit SapDocumento15 pagineAudit SapYLEF25Nessuna valutazione finora
- Icai 4Documento55 pagineIcai 4Harun Raaj GuptaNessuna valutazione finora
- Computer Based Information System AuditDocumento4 pagineComputer Based Information System AuditAdin IhtiNessuna valutazione finora
- Audit SapDocumento15 pagineAudit SapThun An Freitas ChiuNessuna valutazione finora
- GTAG 4 2nd EditionDocumento20 pagineGTAG 4 2nd EditionaluqueroNessuna valutazione finora
- Management of IT Auditing: 2nd EditionDocumento20 pagineManagement of IT Auditing: 2nd EditionJohn Wilben Sibayan ÜNessuna valutazione finora
- JUBERT L. PADILLA - Application LetterDocumento1 paginaJUBERT L. PADILLA - Application LetterJubert PadillaNessuna valutazione finora
- Welcom E: Computer Systems Servicing (NC Ii)Documento33 pagineWelcom E: Computer Systems Servicing (NC Ii)Jubert PadillaNessuna valutazione finora
- Dalit PoemDocumento1 paginaDalit PoemJubert PadillaNessuna valutazione finora
- Anecdotal Record: Calumbaya, Bauang, La UnionDocumento3 pagineAnecdotal Record: Calumbaya, Bauang, La UnionJubert PadillaNessuna valutazione finora
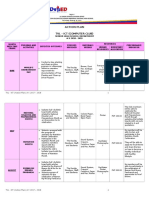
- LESSON EXEMPLAR On COMPUTER NETWORKINGDocumento3 pagineLESSON EXEMPLAR On COMPUTER NETWORKINGJubert Padilla50% (2)
- PE 1 Weekly-Home-Learning-PlanDocumento3 paginePE 1 Weekly-Home-Learning-PlanJubert Padilla100% (1)
- WHLP Week 2 INTRO TO PHILO ELMER PATACSILDocumento2 pagineWHLP Week 2 INTRO TO PHILO ELMER PATACSILJubert PadillaNessuna valutazione finora
- EARTH LIFE SCIENCE October-12-16Documento8 pagineEARTH LIFE SCIENCE October-12-16Jubert PadillaNessuna valutazione finora
- Senior High School DepartmentDocumento4 pagineSenior High School DepartmentJubert PadillaNessuna valutazione finora
- Lesson Exemplar in Computer Systems Servicing (NC Ii) : Region I Schools Division of La UnionDocumento4 pagineLesson Exemplar in Computer Systems Servicing (NC Ii) : Region I Schools Division of La UnionJubert PadillaNessuna valutazione finora
- The Parent / Guardian Submits The Student's Activity Sheets / Outputs Personally in Their Respective Barangay HallDocumento3 pagineThe Parent / Guardian Submits The Student's Activity Sheets / Outputs Personally in Their Respective Barangay HallJubert PadillaNessuna valutazione finora
- Senior High School DepartmentDocumento8 pagineSenior High School DepartmentJubert PadillaNessuna valutazione finora
- Don Eulogio de Guzman Memorial National High SchoolDocumento1 paginaDon Eulogio de Guzman Memorial National High SchoolJubert PadillaNessuna valutazione finora
- 1ST Quarter CSS 12 Week 5-6Documento6 pagine1ST Quarter CSS 12 Week 5-6Jubert PadillaNessuna valutazione finora
- 3RD Quarter CSS 12 Week 1-2Documento4 pagine3RD Quarter CSS 12 Week 1-2Jubert PadillaNessuna valutazione finora
- All Weeks Whlp-Per - Dev.Documento6 pagineAll Weeks Whlp-Per - Dev.Jubert PadillaNessuna valutazione finora
- 2ND Quarter CSS 12 Week 7-8Documento6 pagine2ND Quarter CSS 12 Week 7-8Jubert PadillaNessuna valutazione finora
- 2ND Quarter CSS 12 Week 3-4Documento6 pagine2ND Quarter CSS 12 Week 3-4Jubert PadillaNessuna valutazione finora
- 2ND Quarter CSS 12 Week 5-6Documento6 pagine2ND Quarter CSS 12 Week 5-6Jubert PadillaNessuna valutazione finora
- 2ND Quarter CSS 12 Week 1-2Documento6 pagine2ND Quarter CSS 12 Week 1-2Jubert PadillaNessuna valutazione finora
- Senior High School DepartmentDocumento6 pagineSenior High School DepartmentJubert PadillaNessuna valutazione finora
- CSS 12 Week 3-4Documento6 pagineCSS 12 Week 3-4Jubert PadillaNessuna valutazione finora
- Senior High School DepartmentDocumento6 pagineSenior High School DepartmentJubert PadillaNessuna valutazione finora
- Action Plan: TVL - Ict (Computer Club)Documento7 pagineAction Plan: TVL - Ict (Computer Club)Jubert PadillaNessuna valutazione finora
- Special Project and DonationsDocumento1 paginaSpecial Project and DonationsJubert PadillaNessuna valutazione finora
- Daily Lesson Plan Computer Systems Servicing 11 First Semester, S.Y. 2019-2020Documento4 pagineDaily Lesson Plan Computer Systems Servicing 11 First Semester, S.Y. 2019-2020Jubert PadillaNessuna valutazione finora
- Senior High School Department Researches: Don Eulogio de Guzman Memorial National High SchoolDocumento2 pagineSenior High School Department Researches: Don Eulogio de Guzman Memorial National High SchoolJubert PadillaNessuna valutazione finora
- CrosswordDocumento1 paginaCrosswordJubert PadillaNessuna valutazione finora
- Action Plan: TVL - Ict (Computer Club)Documento7 pagineAction Plan: TVL - Ict (Computer Club)Jubert PadillaNessuna valutazione finora
- Scoring Rubric Computer Systems Servicing 11 First Semester, S.Y. 2019-2020Documento10 pagineScoring Rubric Computer Systems Servicing 11 First Semester, S.Y. 2019-2020Jubert PadillaNessuna valutazione finora
- RetailersDocumento11 pagineRetailersrakshit1230% (1)
- Project Change ManagementDocumento15 pagineProject Change ManagementTaskia FiraNessuna valutazione finora
- Diamonds+in+the+Sky PDFDocumento70 pagineDiamonds+in+the+Sky PDFRaffi Delic100% (5)
- Stock TradingDocumento7 pagineStock TradingJared RobisonNessuna valutazione finora
- Research Paper - Sample SimpleDocumento15 pagineResearch Paper - Sample Simplewarblade_02Nessuna valutazione finora
- Jetro Restaurant Depot AgreementDocumento28 pagineJetro Restaurant Depot AgreementUFCW770Nessuna valutazione finora
- Macroeconomics SlidesDocumento20 pagineMacroeconomics SlidesSantiya SubramaniamNessuna valutazione finora
- Questionnaire Consumer Perception On Online ShoppingDocumento5 pagineQuestionnaire Consumer Perception On Online Shoppingrkpreethi75% (8)
- Three Rivers DC Data Quality StrategyDocumento11 pagineThree Rivers DC Data Quality StrategyJazzd Sy GregorioNessuna valutazione finora
- Tally FeaturesDocumento69 pagineTally FeaturesSudhakar Ganjikunta0% (1)
- 1 - 20.09.2018 - Corriogendum 1aDocumento1 pagina1 - 20.09.2018 - Corriogendum 1achtrpNessuna valutazione finora
- Airline Reservations SystemDocumento6 pagineAirline Reservations SystemShanie Rosero BriongosNessuna valutazione finora
- MANACCDocumento22 pagineMANACCNadine KyrahNessuna valutazione finora
- Venture Capital & Ventre Capitalist: Made By: Gagan Vats Priyanka Tuteja Achal Jain Akshat DhallDocumento24 pagineVenture Capital & Ventre Capitalist: Made By: Gagan Vats Priyanka Tuteja Achal Jain Akshat DhalltarunshridharNessuna valutazione finora
- LTE World Summit 2014 Brochure PDFDocumento16 pagineLTE World Summit 2014 Brochure PDFMoussa Karim AlioNessuna valutazione finora
- Hizon Notes - Transportation Laws (Jarodelyn Mabalot - S Conflicted Copy)Documento120 pagineHizon Notes - Transportation Laws (Jarodelyn Mabalot - S Conflicted Copy)Jimcris Posadas Hermosado100% (1)
- Sarah Kuhn ResumeDocumento2 pagineSarah Kuhn Resumeapi-433846859Nessuna valutazione finora
- 1930 Hobart DirectoryDocumento82 pagine1930 Hobart DirectoryAnonymous X9qOpCYfiBNessuna valutazione finora
- Subhiksha Case StudyDocumento9 pagineSubhiksha Case StudyRavi Keshava Reddy100% (1)
- Nothing Phone (1) (Black, 128 GB) : Grand Total 27009.00Documento1 paginaNothing Phone (1) (Black, 128 GB) : Grand Total 27009.00Rehan KahnNessuna valutazione finora
- Railways PresentationDocumento33 pagineRailways PresentationshambhoiNessuna valutazione finora
- OSHA 3000 - Employer Rights and ResponsibilitiesDocumento28 pagineOSHA 3000 - Employer Rights and ResponsibilitiesWahed Mn ElnasNessuna valutazione finora
- Chung Ka Bio Vs Intermediate Appelate CourtDocumento1 paginaChung Ka Bio Vs Intermediate Appelate CourtJosiah BalgosNessuna valutazione finora
- High Dividend Yield StocksDocumento3 pagineHigh Dividend Yield StockskaizenlifeNessuna valutazione finora
- Association of Differently Abled Person in The Province of AntiqueDocumento2 pagineAssociation of Differently Abled Person in The Province of AntiqueLucifer MorningstarNessuna valutazione finora
- Major Issues Relating To Infrastructure of Indian RailwaysDocumento80 pagineMajor Issues Relating To Infrastructure of Indian Railwayssri103120% (5)
- IND AS 103 - Bhavik Chokshi - FR ShieldDocumento26 pagineIND AS 103 - Bhavik Chokshi - FR ShieldSoham Upadhyay100% (1)
- Introduction For UPSDocumento19 pagineIntroduction For UPSteju_690% (1)
- Grade 8 EMS Classic Ed GuideDocumento41 pagineGrade 8 EMS Classic Ed GuideMartyn Van ZylNessuna valutazione finora
- Joy Film - Guided Viewing Questions & AnalysisDocumento6 pagineJoy Film - Guided Viewing Questions & AnalysisMichael MarquisNessuna valutazione finora