Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Coding and Classification
Caricato da
saisenth0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
23 visualizzazioni6 paginedrsenthiil
Copyright
© © All Rights Reserved
Formati disponibili
DOC, PDF, TXT o leggi online da Scribd
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentodrsenthiil
Copyright:
© All Rights Reserved
Formati disponibili
Scarica in formato DOC, PDF, TXT o leggi online su Scribd
0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
23 visualizzazioni6 pagineCoding and Classification
Caricato da
saisenthdrsenthiil
Copyright:
© All Rights Reserved
Formati disponibili
Scarica in formato DOC, PDF, TXT o leggi online su Scribd
Sei sulla pagina 1di 6
Coding and Classification:
Coding: assignment of a symbol (or a set of symbols) to represent information.
Classification: a protocol that is used to separate a large group of objects into separate
sub-groups.
Therefore, we first estimate (or survey) all possible different shapes we may be
dealing with. Next, we identify some features that define something distinguishing
about the shape of a part.
Examples:
This process is largely intuitive (it would be nice to have mathematical representations
of such !ualifiers).
Then, for a given application where we wish to apply "T, we select a small set of
representative features. #ach of these are given one (or a few) code digits.
$or any given feature, we can further classify the variations -- and therefore assign
different values to the code digit (say %, &, ', ..., () depending on the si)e of the actual
feature.
*ased upon this idea, several schemes of coding and classification have been
developed+
(a) Hierarchical Structures (Monocodes):
,ere, each digit (or position) in the code represents a feature-sub-group. The first digit
represents an entire group. The next digit represents sub-groups of the feature, and so
on.
.n this sense, each subse!uent digit is !ualified by the preceding digits (or, in an
object-oriented sense, each subse!uent digit inherits the properties of the previous
digits).
#xample+
/onsider all parts to be classified in terms of a feature+ rotational symmetry.
% 00 Non-rotational (prismatic) parts
& 00 1otational parts.
2ithin these groups, we can further classify by feature+ presence of hole(s).
3 00 No holes
% 00 ,as holes
4dvantages of monocodes+
1. With just a few digits, a very large amount of information can be
stored
2. The hierarchical structure allows parts of the code to be used for
information at different levels of abstraction.
5isadvantages+
1. Impossible to get a good hierarchical structure for most
features/groups
2. ifferent sub!groups may have different levels of sub!sub!groups,
thereby leading to blan" codes in some positions.
(b) Chain codes (Polycodes):
.n this method, the code digit represents one feature. Thus, the value of any given
digit (or position) within the code has no relation to the other digits.
#xample+ 4 feature to be represented may be the longest linear dimension6
The value of this digit may be represented by an integer that is obtained by rounding
off the length (longest dimension) 7in inches8 of the part being coded.
2hat if we are dealing with parts longer than (.9 inches :
2e may need to reserve two (or more) digits for this feature in that case.
4dvantages+
1. #asy to formulate
5isadvantages+
1. $ess information is stored per digit% therefore to get a meaningful
comparison of, say, shape, very long codes will be re&uired.
2. 'omparison of coded parts (to chec" for similarity) re&uires more
wor".
(c) Hybrid Structure:
.n this case, the code for a part is a mixture of polycodes and monocodes. ;uch coding
methods use monocodes where they can, and use polycodes for the other digits -- in
such a way as to obtain a code structure that captures the essential information about a
part shape. This is the most commonly used method of coding and classification.
2e shall study two popular coding methods to gain better understanding of coding
and classification+ Opitz and KK3
<roperties+
1. *ybrid codes
2. +seful in shape classification for design and machining
applications
Opitz Code:
The original =pit) code was a 9-digit code.
5igit-<osition Type $eature-"roup
% .nteger part class (rotational-non-rotational)
& .nteger external shape
' .nteger internal shape
> .nteger plane surface features and machining
9 .nteger auxiliary features (off-axis holes, gear teeth etc.)
?ater, > more digits were added to the coding scheme, in order to increase the
manufacturing information. These last four digits are also called supplementary digits.
4ll four are integers, and respectively represent+
5imensions, @aterial, =riginal shape of raw stocA, and 4ccuracy.
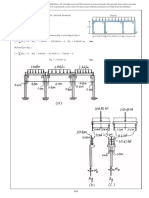
!"a#ple:
*evel "ear, ?ength 0 %.B9, 5iameter 0 '.9
$igure &. *evel gears
7source+ $rench and CiercA, #ngineering drawing D "raphic Technology, pub.+ @c"raw-,ill8
The KK-3 code:
.t was originally developed by the Eapan ;ociety for <romotion of @achining
.ndustry. The domain is machining and grinding parts. The code is &%-digits, each of
which is an integer.
;tructure of the FF-' coding system
7source+ /hang, 2ang, 2ysA, /4@, pub.+ <rentice-,all8
7=riginal source+ Eapan ;ociety for the <romotion of @achine .ndustry8
GT Applications: $esign:
The common process of design involves a designer maAing many decisions that are
non-critical to the ultimate functionality.
7#xample+ "ear si)es for idling gears in a gear-box8
The process of product manufacturing involves+
%. maAing such high level design decision,
&. calculation of the exact dimensions of the components (usually from the
sAetch),
'. /reating the detailed drafting-/45 model of the part,
>. "enerating the process plan for the part, including+
o 5etermination of machine tool, tools, fixtures, machining conditions etc.
@uch time is spent, in this process, in the last two steps. .n this se!uence of tasAs, we
introduce another one+
(&a) <erform coding and classification for the part.
Then, by comparing the code of the new part with those already existing, if the
designer can discover a part very similar to the one we need, then+
%. ,e may use the existing part in the design. 72hat are the benefits :8
&. ,e may be able to perform tasAs (') and (>) by minor modifications to the design
and process plan of the existing part.
Applications: Machine Selection
This is a big issue in job-shops and small batch si)e factories.
/haracteristics of such factories+
many different part shapes and specifications6
shop floor has many general purpose machine tools (m-c centers etc.)
Problems:
%. 4 large percent of the total in-process time of a part (0 average difference between
the time when a raw stocA enters the shop floor and when the final part leaves the
factory) is setup time 7 up to G9H of total machining time8.
5uring much of the setup time, the machine tool is idle.
&. @any parts that are assigned to a machine may under-utili)e its capabilities.
Potrebbero piacerti anche
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (895)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- 5.2 Notes On Production CycleDocumento2 pagine5.2 Notes On Production CyclesaisenthNessuna valutazione finora
- Application of Low Cost Inhibitors To Reduce Rate of Corrosion in Rail Passenger CoachesDocumento9 pagineApplication of Low Cost Inhibitors To Reduce Rate of Corrosion in Rail Passenger CoachessaisenthNessuna valutazione finora
- 5.6 Notes On Material Requirements PlanningDocumento2 pagine5.6 Notes On Material Requirements PlanningsaisenthNessuna valutazione finora
- Fms 1Documento32 pagineFms 1saisenthNessuna valutazione finora
- PhilosophyDocumento1 paginaPhilosophysaisenthNessuna valutazione finora
- 5,5 Notes On Routing in ManufacturingDocumento2 pagine5,5 Notes On Routing in ManufacturingsaisenthNessuna valutazione finora
- Application of Low Cost Inhibitors To Reduce Rate of Corrosion in Rail Passenger CoachesDocumento9 pagineApplication of Low Cost Inhibitors To Reduce Rate of Corrosion in Rail Passenger CoachessaisenthNessuna valutazione finora
- Request To Send PapersDocumento1 paginaRequest To Send PaperssaisenthNessuna valutazione finora
- Vision Mission UniversityDocumento2 pagineVision Mission UniversitysaisenthNessuna valutazione finora
- CH 1 and 2 Product Design and Development (#1)Documento12 pagineCH 1 and 2 Product Design and Development (#1)VinodVermaNessuna valutazione finora
- Intercom Numbers PDFDocumento1 paginaIntercom Numbers PDFsaisenthNessuna valutazione finora
- Me2252 MT1 Unit1Documento23 pagineMe2252 MT1 Unit1saisenthNessuna valutazione finora
- 12 WorkstationdesignDocumento31 pagine12 WorkstationdesignsaisenthNessuna valutazione finora
- 12 WorkstationdesignDocumento31 pagine12 WorkstationdesignsaisenthNessuna valutazione finora
- Lean SylDocumento2 pagineLean SylsaisenthNessuna valutazione finora
- 8 Assignment QP Key Sample ScriptDocumento10 pagine8 Assignment QP Key Sample ScriptsaisenthNessuna valutazione finora
- Academic Calender 2018-19-To Hods (6484)Documento10 pagineAcademic Calender 2018-19-To Hods (6484)saisenthNessuna valutazione finora
- Asper School of Business 9.613 Using Information Technology Part-Time MBA, December 2001 Instructor: Bob TravicaDocumento13 pagineAsper School of Business 9.613 Using Information Technology Part-Time MBA, December 2001 Instructor: Bob TravicasaisenthNessuna valutazione finora
- 2010 Reg Automobile SylDocumento112 pagine2010 Reg Automobile SylsaisenthNessuna valutazione finora
- Electrical Notes - PvsDocumento84 pagineElectrical Notes - PvssaisenthNessuna valutazione finora
- Electrical Notes - PvsDocumento84 pagineElectrical Notes - PvssaisenthNessuna valutazione finora
- 2 Casting FormingDocumento56 pagine2 Casting FormingMohana KrishnanNessuna valutazione finora
- Cellular Manufacturing Systems - Lecture Series 8: Ie 3265 Pom R. R. Lindeke, PHD Spring 2005Documento42 pagineCellular Manufacturing Systems - Lecture Series 8: Ie 3265 Pom R. R. Lindeke, PHD Spring 2005saisenthNessuna valutazione finora
- Group Technology in MFG SystemsDocumento14 pagineGroup Technology in MFG SystemssanoojsiddikhNessuna valutazione finora
- Cellular Manufacturing Systems - Lecture Series 8: Ie 3265 Pom R. R. Lindeke, PHD Spring 2005Documento42 pagineCellular Manufacturing Systems - Lecture Series 8: Ie 3265 Pom R. R. Lindeke, PHD Spring 2005saisenthNessuna valutazione finora
- Cim Syl SpuDocumento2 pagineCim Syl SpusaisenthNessuna valutazione finora
- 7 Production Planning ControlDocumento20 pagine7 Production Planning Controlmaanish000Nessuna valutazione finora
- Cim Two Mark Que With AnsDocumento7 pagineCim Two Mark Que With AnssaisenthNessuna valutazione finora
- Ppcunit1 1Documento1 paginaPpcunit1 1saisenthNessuna valutazione finora
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (266)
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (400)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (588)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (74)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2259)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (121)
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- C28x WorkshopDocumento400 pagineC28x WorkshopMarcio De Andrade VogtNessuna valutazione finora
- Important Dates (PG Students View) Semester 1, 2022-2023 - All Campus (As of 2 October 2022)Documento4 pagineImportant Dates (PG Students View) Semester 1, 2022-2023 - All Campus (As of 2 October 2022)AFHAM JAUHARI BIN ALDI (MITI)Nessuna valutazione finora
- Sfa 5.22 PDFDocumento36 pagineSfa 5.22 PDFLuis Evangelista Moura PachecoNessuna valutazione finora
- Labor LawDocumento6 pagineLabor LawElden Cunanan BonillaNessuna valutazione finora
- 20091216-153551-APC Smart-UPS 1500VA USB SUA1500IDocumento4 pagine20091216-153551-APC Smart-UPS 1500VA USB SUA1500Ifietola1Nessuna valutazione finora
- Misca 367 of 2008Documento5 pagineMisca 367 of 2008Kabelo TsehareNessuna valutazione finora
- Notes in Train Law PDFDocumento11 pagineNotes in Train Law PDFJanica Lobas100% (1)
- Archer AX53 (EU) 1.0 - DatasheetDocumento7 pagineArcher AX53 (EU) 1.0 - DatasheetLucNessuna valutazione finora
- Resistor 1k - Vishay - 0.6wDocumento3 pagineResistor 1k - Vishay - 0.6wLEDNessuna valutazione finora
- By Daphne Greaves Illustrated by Michela GalassiDocumento15 pagineBy Daphne Greaves Illustrated by Michela GalassiLucian DilgociNessuna valutazione finora
- Common Metallurgical Defects in Grey Cast IronDocumento9 pagineCommon Metallurgical Defects in Grey Cast IronRolando Nuñez Monrroy100% (1)
- Unix Training ContentDocumento5 pagineUnix Training ContentsathishkumarNessuna valutazione finora
- GET IELTS BAND 9 SpeakingDocumento54 pagineGET IELTS BAND 9 Speakingm.alizadehsaraNessuna valutazione finora
- Which Among The Following Statement Is INCORRECTDocumento7 pagineWhich Among The Following Statement Is INCORRECTJyoti SinghNessuna valutazione finora
- Impact of Dust& Dirt Accumulation On The Performance of PV PanelsDocumento4 pagineImpact of Dust& Dirt Accumulation On The Performance of PV PanelserpublicationNessuna valutazione finora
- Problemas Del Capitulo 7Documento26 pagineProblemas Del Capitulo 7dic vilNessuna valutazione finora
- 6.T24 Common Variables-R14Documento29 pagine6.T24 Common Variables-R14Med Mehdi LaazizNessuna valutazione finora
- 1.SITXWHS003 Student Assessment Tasks 1Documento58 pagine1.SITXWHS003 Student Assessment Tasks 1Yashaswi GhimireNessuna valutazione finora
- 8 e Daft Chapter 01Documento29 pagine8 e Daft Chapter 01GabNessuna valutazione finora
- Power Off Reset ReasonDocumento4 paginePower Off Reset Reasonmaiacalefato72Nessuna valutazione finora
- Fuel Supply Agreement - First DraftDocumento104 pagineFuel Supply Agreement - First DraftMuhammad Asif ShabbirNessuna valutazione finora
- Aircraft Materials and Hardware: (Nuts, Studs, Screws)Documento25 pagineAircraft Materials and Hardware: (Nuts, Studs, Screws)PakistaniTalent cover songsNessuna valutazione finora
- Software Requirement SpecificationDocumento10 pagineSoftware Requirement SpecificationSushil SarrafNessuna valutazione finora
- Choosing Your PHD TopicDocumento9 pagineChoosing Your PHD TopicvilaiwanNessuna valutazione finora
- Accredited Architecture QualificationsDocumento3 pagineAccredited Architecture QualificationsAnamika BhandariNessuna valutazione finora
- 02 Adaptive Tracking Control of A Nonholonomic Mobile RobotDocumento7 pagine02 Adaptive Tracking Control of A Nonholonomic Mobile Robotchoc_ngoayNessuna valutazione finora
- The Green Wall - Story and Photos by Stephen James Independent Investigative Journalism & Photography - VC Reporter - Ventura County Weekly - California Department of Corrections whistleblower D.J. Vodicka and his litigation against the CDC.Documento8 pagineThe Green Wall - Story and Photos by Stephen James Independent Investigative Journalism & Photography - VC Reporter - Ventura County Weekly - California Department of Corrections whistleblower D.J. Vodicka and his litigation against the CDC.Stephen James - Independent Investigative Journalism & PhotographyNessuna valutazione finora
- BloodDocumento22 pagineBloodGodd LlikeNessuna valutazione finora
- Application For New Ration Card - Telangana & AP StatesDocumento1 paginaApplication For New Ration Card - Telangana & AP Statesping2gopiNessuna valutazione finora
- Lets Talk About Food Fun Activities Games Oneonone Activities Pronuncia - 1995Documento1 paginaLets Talk About Food Fun Activities Games Oneonone Activities Pronuncia - 1995IAmDanaNessuna valutazione finora