Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
IT Security Incident Management
Caricato da
BrianEarl0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
137 visualizzazioni3 pagineThis document outlines standard operating procedures for handling IT security incidents at Queen Mary college. It details responsibilities for incident reporting and management. Key steps include maintaining registers of computer systems and data sets, logging all incidents, investigating potential breaches, notifying relevant parties, reviewing incident logs annually and escalating any serious incidents to senior management. The goal is to ensure incidents are addressed according to best practices and that confidential data is protected.
Descrizione originale:
By definition, information security exists to protect your organization's valuable information resources. But too often information security efforts are viewed as thwarting business objectives.
Copyright
© © All Rights Reserved
Formati disponibili
PDF, TXT o leggi online da Scribd
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoThis document outlines standard operating procedures for handling IT security incidents at Queen Mary college. It details responsibilities for incident reporting and management. Key steps include maintaining registers of computer systems and data sets, logging all incidents, investigating potential breaches, notifying relevant parties, reviewing incident logs annually and escalating any serious incidents to senior management. The goal is to ensure incidents are addressed according to best practices and that confidential data is protected.
Copyright:
© All Rights Reserved
Formati disponibili
Scarica in formato PDF, TXT o leggi online su Scribd
0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
137 visualizzazioni3 pagineIT Security Incident Management
Caricato da
BrianEarlThis document outlines standard operating procedures for handling IT security incidents at Queen Mary college. It details responsibilities for incident reporting and management. Key steps include maintaining registers of computer systems and data sets, logging all incidents, investigating potential breaches, notifying relevant parties, reviewing incident logs annually and escalating any serious incidents to senior management. The goal is to ensure incidents are addressed according to best practices and that confidential data is protected.
Copyright:
© All Rights Reserved
Formati disponibili
Scarica in formato PDF, TXT o leggi online su Scribd
Sei sulla pagina 1di 3
SOP Number DG27 v1 Page 1 of 3
Standard Operating Procedures (SOP) for:
IT Security Incident Management
SOP Number: DG27 Version Number: 1
Effective Date: 15 July 2014 Review Date: 23/06/2015
Author:
Reviewer:
David Pick, IT Services Security
Paul Smallcombe, Records & Information Compliance Manager
Authorisation:
Name / Position Chris Day, Director of IT Services
Signature C Day
Date 15 July 2014
Accountability:
Position Line Managers
Responsibility:
Position Directors/ Heads of Department
QM IT Security Team
QM Records & Information Compliance Manager
QM Central Network Team
All members of the College
Revision History
Version Description Author Date
1 Initial version. David Pick 16/08/2010
1 Annual Review No Change Ian Douglas 23/06/2014
Purpose and Objective:
To ensure that information technology security incidents are handled in accordance with industry
best practice.
References:
SOP DG05 Information Security Incident Reporting
SOP DG09 Information Classification
SOP DG13 Records Management
SOP Text
Responsibility Activity
1. Directors/ Heads of
Department
Each Director/ Head of Department shall inform the IT Security
Team of the existence of any computer systems within their areas
of responsibility containing Confidential or Restricted information
as defined by SOP DG09 Information Classification.
2. QM IT Security
Team
Queen Mary shall maintain a register of computer systems holding
data sets held that contain Confidential or Restricted information
as defined by SOP DG09 Information Classification. This
register shall identify the computer systems, the person or role
within Queen Mary responsible for the operation of those
SOP Number DG27 v1 Page 2 of 3
computer systems, reference to the entries in the register of data
sets held by the QM Records and Information Compliance
Manager, and information about the software used by those
computer systems. Refer to SOP DG13 Records Management.
3. QM IT Security
Team
Queen Mary shall maintain a log of incidents that may impinge on
any aspect of data security for the computer systems holding
Confidential or Restricted information including, but not limited
to, the confidentiality and integrity of the data. Other incidents, for
example, major incidents affecting the availability of computer
systems, shall also be recorded in the log. Refer to SOP DG13
Records Management.
4. QM IT Security
Team
QM Records &
Information
Compliance Manager
The QM IT Security Team will advise the QM Records &
Information Compliance Manager about any information or
guidance they receive or generate about the degree of logging
required for different types of incident. The QM Records &
Information Compliance Manager shall publish this guidance
periodically to all members of Queen Mary.
5. Incident Manager
Where a breach of physical security is detected an Incident
Manager shall be assigned. The Incident Manager of that physical
breach shall determine if any computer equipment or records of
computer access credentials might have been accessed and, if so,
report it as a possible breach of IT security to the IT Security
Team.
6. Any person aware of
a potential breach of
IT Security
Where a suspicion of any breach of the security of any computer
system registered with the IT Security Team is raised it shall be
reported to the IT Security Team. If there is any doubt about it, it
shall be reported.
7. QM IT Security
Team
When it receives a report of a potential or actual breach of IT
security, the IT Security Team shall determine the scope of the
computer systems that might be placed at risk. The IT Security
Team shall consult its registers and inform both the overall
Incident Manager and the QM Records & Information Compliance
Manager of all data sets that may have potentially been placed at
risk.
8. QM IT Security
Team
The IT Security Team shall consult with the person or team
responsible for each computer system possibly involved and
appoint a technically-competent System Investigator for that
particular breach, either from the IT Security Team or from the
team responsible for the computer system(s) involved.
9. System Investigator
QM Records &
Information
Compliance Manager
The System Investigator shall determine if any breach of the IT
Security of that system actually occurred and report the actual
extent of the breach to the overall Incident Manager and the IT
Security Team. If Confidential or Restricted data has been put at
risk the IT Security Team shall inform the QM Records &
Information Compliance Manager who shall notify the persons
responsible for the data set as per SOP DG05 Information
Security Incident Reporting.
10. All Members of
Queen Mary
Any disclosure of computer account credentials shall be regarded
as a breach of IT security and the standard notifications and
actions taken. In this context all systems to which the
compromised account has access shall be considered as potentially
compromised.
SOP Number DG27 v1 Page 3 of 3
11. QM IT Security
Team
The contents of the IT security incident log shall be reviewed
periodically, and in any case at least annually, and a report made
to the Audit and Compliance Committee.
12. QM IT Security
Team
Any incident deemed to be serious by the QM IT Security Team
shall be escalated to the Queen Mary Senior Executive
immediately, who will provide a report to the Audit and
Compliance Committee.
13. QM IT Security
Team
Any person
responsible for a
computer system
used for handling
Confidential or
Restricted data
The IT Security Team shall monitor the general IT threat
landscape, especially for software used by any computer system
registered with it, and notify the teams responsible for computer
systems handling Confidential or Restricted data of significant
threats.
The team responsible for any computer system shall also monitor
the threat landscape of the software which they use and notify the
IT Security Team of any significant threats.
The IT Security Team shall arrange periodic reviews, at least
annually, of the information security requirements of each
computer system in the register.
14. QM Central Network
Team
The QM Network Team shall maintain a register of all (semi-)
autonomous sub-networks connected to the College network
which will identify the network addresses used on that sub-
network, the department or institute to which that sub-network
belongs, and the person or role responsible for managing that sub-
network.
15. Any person
conducting any part
of an IT Security
Incident investigation
If any computer system is determined to be at risk in any specific
incident, both the person identified in this register and the local
Information Security Manager for the department responsible for
the network connection used by that computer shall be included in
the list of people to whom reports are made about the incident.
16. QM Central Network
Team
If a sub-network is determined to be a source or relay of any
malware or network traffic causing other problems the offending
material or traffic shall be blocked.
Potrebbero piacerti anche
- Operationalizing Information Security: Putting the Top 10 SIEM Best Practices to WorkDa EverandOperationalizing Information Security: Putting the Top 10 SIEM Best Practices to WorkNessuna valutazione finora
- Incident Response Guide PDFDocumento17 pagineIncident Response Guide PDFAguinaldo CristianoNessuna valutazione finora
- Security Incident Response Plan HLDocumento6 pagineSecurity Incident Response Plan HLnicolasv100% (1)
- 10 Steps To Implement A Disaster Recovery Plan - QTS White PaperDocumento14 pagine10 Steps To Implement A Disaster Recovery Plan - QTS White PaperShiva PrasadNessuna valutazione finora
- Disaster Recovery Plan Template 02Documento34 pagineDisaster Recovery Plan Template 02ryandini fadhilah100% (1)
- The It Disaster Recovery PlanDocumento4 pagineThe It Disaster Recovery Planbrynner16100% (1)
- Disaster Recovery PolicyDocumento21 pagineDisaster Recovery PolicyLavhonte Antonio Davis50% (2)
- Disaster RecoveryDocumento6 pagineDisaster Recoverymav2u2Nessuna valutazione finora
- DRP TemplateDocumento13 pagineDRP Templatemiloja99Nessuna valutazione finora
- Firewall Policy: Prepared byDocumento8 pagineFirewall Policy: Prepared byChristine MbinyaNessuna valutazione finora
- Disaster Recovery Plan LastDocumento13 pagineDisaster Recovery Plan LastMary Ařmĥølīc Yøja100% (1)
- Backup and Recovery PolicyDocumento17 pagineBackup and Recovery PolicyJasminBesic100% (2)
- Information Security Policy ChecklistDocumento2 pagineInformation Security Policy ChecklistRead Rule100% (6)
- Operations Security Policy Template v1.0Documento10 pagineOperations Security Policy Template v1.0rsgrthyjhNessuna valutazione finora
- Firewall Policy TemplateDocumento8 pagineFirewall Policy TemplateChristine MbinyaNessuna valutazione finora
- A17 Business Continuity Policy v1Documento5 pagineA17 Business Continuity Policy v1john mNessuna valutazione finora
- 10-Cisa It Audit - BCP and DRPDocumento27 pagine10-Cisa It Audit - BCP and DRPHamza NaeemNessuna valutazione finora
- Information Security Incident ManagementDocumento3 pagineInformation Security Incident ManagementBara Daniel100% (1)
- IT Disaster Recovery PlanDocumento6 pagineIT Disaster Recovery PlanCentaur ArcherNessuna valutazione finora
- Information Security Incident ManagementDocumento8 pagineInformation Security Incident ManagementcaliagarNessuna valutazione finora
- IT Risk Assessment ChecklistDocumento10 pagineIT Risk Assessment Checklistje100% (2)
- ISO 22301 Self Assessment ChecklistDocumento3 pagineISO 22301 Self Assessment ChecklistNicholasFCheongNessuna valutazione finora
- It Security GuidelinesDocumento143 pagineIt Security GuidelinesTeam LeaderNessuna valutazione finora
- Disaster Recovery DrillDocumento12 pagineDisaster Recovery DrillApoorv Bishnoi100% (3)
- Information Security PlanDocumento11 pagineInformation Security PlanJohn J. Macasio100% (1)
- CyberIncidentManagementPlanningGuide en PDFDocumento28 pagineCyberIncidentManagementPlanningGuide en PDFthale24Nessuna valutazione finora
- 9-BCP DRPDocumento67 pagine9-BCP DRPRuppee Edward100% (1)
- Security Incident Management ProcessDocumento8 pagineSecurity Incident Management ProcessHiren DhadukNessuna valutazione finora
- Cyber Security Incident Response Plan2Documento4 pagineCyber Security Incident Response Plan2Anonymous GIf6vnNessuna valutazione finora
- It Security - A Hand BookDocumento72 pagineIt Security - A Hand Bookjkpdbnlbsg100% (4)
- An IT Security Manager's ChecklistDocumento4 pagineAn IT Security Manager's Checklistrajunair0% (1)
- Critical Systems Cyber Security ControlsDocumento36 pagineCritical Systems Cyber Security ControlsHiba Afaneh100% (1)
- Network Security and ManagementDocumento4 pagineNetwork Security and Managementrashid1986Nessuna valutazione finora
- Internal Audit Report - Information Technology Risk AssessmentDocumento8 pagineInternal Audit Report - Information Technology Risk AssessmentFlorence NkosiNessuna valutazione finora
- IT in Disaster RecoveryDocumento20 pagineIT in Disaster RecoverykirarakiNessuna valutazione finora
- Data Centre Disaster Recovery ChecklistDocumento4 pagineData Centre Disaster Recovery ChecklistRadzi Fasha100% (1)
- ISCP Low Impact TemplateDocumento18 pagineISCP Low Impact TemplateChandra RaoNessuna valutazione finora
- Aquisition Assessment PolicyDocumento2 pagineAquisition Assessment PolicyConstantin TomaNessuna valutazione finora
- Disaster Recovery PlanDocumento9 pagineDisaster Recovery PlanRobert MrClayton Ifyournasty100% (1)
- HK - Baseline IT Security Policy PDFDocumento31 pagineHK - Baseline IT Security Policy PDFsivextien100% (1)
- 5 Steps For Disaster Recovery PlanningDocumento17 pagine5 Steps For Disaster Recovery PlanningnoorzeNessuna valutazione finora
- Incident Management PolicyDocumento18 pagineIncident Management Policyasterix01ar100% (1)
- IT Disaster Recovery PlanDocumento2 pagineIT Disaster Recovery Planbiestavel100% (1)
- Disaster Recovery PlanDocumento12 pagineDisaster Recovery PlanUthpala Pahalavithaƞa100% (2)
- NIST Approach To Patch and Vulnerability ManagementDocumento6 pagineNIST Approach To Patch and Vulnerability ManagementBabby BossNessuna valutazione finora
- Risk MGMT For CComputingDocumento24 pagineRisk MGMT For CComputingGeorge ReyesNessuna valutazione finora
- BCP in BANKSDocumento13 pagineBCP in BANKSshawkat zafarNessuna valutazione finora
- Wireless Administrator ChecklistDocumento4 pagineWireless Administrator ChecklistIndrajit Banerjee100% (5)
- Maintenance ChecklistDocumento8 pagineMaintenance ChecklistAngNessuna valutazione finora
- It Security Risk Assessment GuidelinesDocumento23 pagineIt Security Risk Assessment Guidelinessantsj78Nessuna valutazione finora
- Incident ResponseDocumento6 pagineIncident ResponseShu Bham100% (1)
- Business Continuity Management and IT Disaster RecoveryDocumento4 pagineBusiness Continuity Management and IT Disaster RecoveryKeith Parker100% (3)
- Network Incident Response PlanDocumento5 pagineNetwork Incident Response PlanNgaira MandelaNessuna valutazione finora
- BCP ChecklistDocumento2 pagineBCP ChecklistAsim Amitav JenaNessuna valutazione finora
- Data Backup Policy-SIDocumento10 pagineData Backup Policy-SIChetan PatelNessuna valutazione finora
- SAMA BCM Framework - Continuity and ResilienceDocumento36 pagineSAMA BCM Framework - Continuity and ResiliencechanchalNessuna valutazione finora
- IT Disaster RecoveryDocumento7 pagineIT Disaster RecoveryVarun AhujaNessuna valutazione finora
- DR BCP Guidebook PDFDocumento17 pagineDR BCP Guidebook PDFhaji5Nessuna valutazione finora
- Computer Security Incident Handling GuideDocumento79 pagineComputer Security Incident Handling GuideDinu Șișianu100% (1)
- Problems PDFDocumento9 pagineProblems PDFEduarGelvezNessuna valutazione finora
- Gordon NovelDocumento50 pagineGordon NovelNic Hotep100% (2)
- BM 81004 MuvDocumento52 pagineBM 81004 MuvHamza Abbasi AbbasiNessuna valutazione finora
- 4.10) Arch Shaped Self Supporting Trussless Roof SpecificationsDocumento11 pagine4.10) Arch Shaped Self Supporting Trussless Roof Specificationshebh123100% (1)
- Nuevo CvuDocumento1 paginaNuevo CvuJesús GonzálezNessuna valutazione finora
- Biomasse-HKW Sandreuth E NQDocumento8 pagineBiomasse-HKW Sandreuth E NQValeriu StanNessuna valutazione finora
- Islamic Law - WaterDocumento12 pagineIslamic Law - WaterAnum FaheemNessuna valutazione finora
- BIOS 203: Free Energy Methods Tom MarklandDocumento23 pagineBIOS 203: Free Energy Methods Tom MarklandNemanja ĐokovićNessuna valutazione finora
- AI in RobotsDocumento75 pagineAI in RobotsIslam SehsahNessuna valutazione finora
- Cache MemoryDocumento20 pagineCache MemoryKeshav Bharadwaj RNessuna valutazione finora
- EM230 BR BM3 Fitting InstructionsDocumento2 pagineEM230 BR BM3 Fitting InstructionsRoman BabaevNessuna valutazione finora
- Published Document Guidance On The Use of BS EN 13108, Bituminous Mixtures - Material SpecificationsDocumento8 paginePublished Document Guidance On The Use of BS EN 13108, Bituminous Mixtures - Material SpecificationsCristián JiménezNessuna valutazione finora
- An Introduction Into The Feynman Path Integral PDFDocumento94 pagineAn Introduction Into The Feynman Path Integral PDFLivardy WufiantoNessuna valutazione finora
- Dogging Guide 2003 - WorkCover NSWDocumento76 pagineDogging Guide 2003 - WorkCover NSWtadeumatas100% (1)
- Preview ISO+749-1977 PDFDocumento3 paginePreview ISO+749-1977 PDFLiana GaniNessuna valutazione finora
- Compact 40/25Documento58 pagineCompact 40/25znim04Nessuna valutazione finora
- Engine Maintenance PartsDocumento13 pagineEngine Maintenance PartsSerkanAl100% (1)
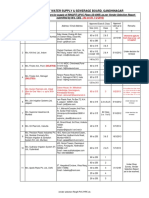
- GWSSB Vendor List 19.11.2013Documento18 pagineGWSSB Vendor List 19.11.2013sivesh_rathiNessuna valutazione finora
- Optimizing Technique-Grenade Explosion MethodDocumento18 pagineOptimizing Technique-Grenade Explosion MethodUday Wankar100% (1)
- Design For Manufacturing Course - by DFRDocumento257 pagineDesign For Manufacturing Course - by DFRhlgc63100% (2)
- Comfort and Performance Your Customers DemandDocumento18 pagineComfort and Performance Your Customers Demandgizex2013Nessuna valutazione finora
- WEISER Locks and HardwareDocumento24 pagineWEISER Locks and HardwareMaritime Door & WindowNessuna valutazione finora
- Delhi Factories Rule 1950 PDFDocumento84 pagineDelhi Factories Rule 1950 PDFAkhilesh Kumar SinghNessuna valutazione finora
- Supplier GPO Q TM 0001 02 SPDCR TemplateDocumento6 pagineSupplier GPO Q TM 0001 02 SPDCR TemplateMahe RonaldoNessuna valutazione finora
- Antikythera MechanismDocumento25 pagineAntikythera MechanismchetansergiurazvanNessuna valutazione finora
- zx350lc 3 InglesDocumento6 paginezx350lc 3 InglesLuis Nahuelhuaique LemusNessuna valutazione finora
- 20 Site SummaryDocumento2 pagine20 Site SummaryMuzammil WepukuluNessuna valutazione finora
- A9K CatalogueDocumento152 pagineA9K CatalogueMohamed SaffiqNessuna valutazione finora
- Manual CRM-91H 93H 9SDocumento2 pagineManual CRM-91H 93H 9SFilip FilipovicNessuna valutazione finora
- Practical Industrial Cybersecurity: ICS, Industry 4.0, and IIoTDa EverandPractical Industrial Cybersecurity: ICS, Industry 4.0, and IIoTNessuna valutazione finora
- The Internet Con: How to Seize the Means of ComputationDa EverandThe Internet Con: How to Seize the Means of ComputationValutazione: 5 su 5 stelle5/5 (6)
- CISM Certified Information Security Manager Study GuideDa EverandCISM Certified Information Security Manager Study GuideNessuna valutazione finora
- Hacking With Kali Linux : A Comprehensive, Step-By-Step Beginner's Guide to Learn Ethical Hacking With Practical Examples to Computer Hacking, Wireless Network, Cybersecurity and Penetration TestingDa EverandHacking With Kali Linux : A Comprehensive, Step-By-Step Beginner's Guide to Learn Ethical Hacking With Practical Examples to Computer Hacking, Wireless Network, Cybersecurity and Penetration TestingValutazione: 4.5 su 5 stelle4.5/5 (9)
- Digital Forensics and Incident Response - Second Edition: Incident response techniques and procedures to respond to modern cyber threats, 2nd EditionDa EverandDigital Forensics and Incident Response - Second Edition: Incident response techniques and procedures to respond to modern cyber threats, 2nd EditionNessuna valutazione finora
- Tor Darknet Bundle (5 in 1): Master the Art of InvisibilityDa EverandTor Darknet Bundle (5 in 1): Master the Art of InvisibilityValutazione: 4.5 su 5 stelle4.5/5 (5)
- How to Disappear and Live Off the Grid: A CIA Insider's GuideDa EverandHow to Disappear and Live Off the Grid: A CIA Insider's GuideNessuna valutazione finora
- Transformational Security Awareness: What Neuroscientists, Storytellers, and Marketers Can Teach Us About Driving Secure BehaviorsDa EverandTransformational Security Awareness: What Neuroscientists, Storytellers, and Marketers Can Teach Us About Driving Secure BehaviorsValutazione: 5 su 5 stelle5/5 (2)
- Facing Cyber Threats Head On: Protecting Yourself and Your BusinessDa EverandFacing Cyber Threats Head On: Protecting Yourself and Your BusinessValutazione: 4.5 su 5 stelle4.5/5 (27)
- 200+ Ways to Protect Your Privacy: Simple Ways to Prevent Hacks and Protect Your Privacy--On and OfflineDa Everand200+ Ways to Protect Your Privacy: Simple Ways to Prevent Hacks and Protect Your Privacy--On and OfflineNessuna valutazione finora
- Cybersecurity for Beginners : Learn the Fundamentals of Cybersecurity in an Easy, Step-by-Step Guide: 1Da EverandCybersecurity for Beginners : Learn the Fundamentals of Cybersecurity in an Easy, Step-by-Step Guide: 1Nessuna valutazione finora
- An Ultimate Guide to Kali Linux for BeginnersDa EverandAn Ultimate Guide to Kali Linux for BeginnersValutazione: 3.5 su 5 stelle3.5/5 (4)
- Set Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNDa EverandSet Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNValutazione: 5 su 5 stelle5/5 (1)
- Anonymize Yourself: The Art of Anonymity to Achieve Your Ambition in the Shadows and Protect Your Identity, Privacy and ReputationDa EverandAnonymize Yourself: The Art of Anonymity to Achieve Your Ambition in the Shadows and Protect Your Identity, Privacy and ReputationValutazione: 4 su 5 stelle4/5 (23)
- Hands-On AWS Penetration Testing with Kali Linux: Set up a virtual lab and pentest major AWS services, including EC2, S3, Lambda, and CloudFormationDa EverandHands-On AWS Penetration Testing with Kali Linux: Set up a virtual lab and pentest major AWS services, including EC2, S3, Lambda, and CloudFormationNessuna valutazione finora
- Surveillance and Surveillance Detection: A CIA Insider's GuideDa EverandSurveillance and Surveillance Detection: A CIA Insider's GuideNessuna valutazione finora
- The Future and Opportunities of Cybersecurity in the WorkforceDa EverandThe Future and Opportunities of Cybersecurity in the WorkforceValutazione: 3 su 5 stelle3/5 (1)
- Law, Privacy and Surveillance in Canada in the Post-Snowden EraDa EverandLaw, Privacy and Surveillance in Canada in the Post-Snowden EraNessuna valutazione finora
- Coding Democracy: How a Growing Hacking Movement is Disrupting Concentrations of Power, Mass Surveillance, and Authoritarianism in the Digital AgeDa EverandCoding Democracy: How a Growing Hacking Movement is Disrupting Concentrations of Power, Mass Surveillance, and Authoritarianism in the Digital AgeValutazione: 4.5 su 5 stelle4.5/5 (3)
- Risk Management and Information Systems ControlDa EverandRisk Management and Information Systems ControlValutazione: 5 su 5 stelle5/5 (1)
- CCSP Certified Cloud Security Professional A Step by Step Study Guide to Ace the ExamDa EverandCCSP Certified Cloud Security Professional A Step by Step Study Guide to Ace the ExamNessuna valutazione finora