Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
I Bps Bank It Officer
Caricato da
Vikas Garg0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
30 visualizzazioni11 pagineThis document contains information about bank exam paper.
Titolo originale
i Bps Bank It Officer
Copyright
© © All Rights Reserved
Formati disponibili
PDF, TXT o leggi online da Scribd
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoThis document contains information about bank exam paper.
Copyright:
© All Rights Reserved
Formati disponibili
Scarica in formato PDF, TXT o leggi online su Scribd
0 valutazioniIl 0% ha trovato utile questo documento (0 voti)
30 visualizzazioni11 pagineI Bps Bank It Officer
Caricato da
Vikas GargThis document contains information about bank exam paper.
Copyright:
© All Rights Reserved
Formati disponibili
Scarica in formato PDF, TXT o leggi online su Scribd
Sei sulla pagina 1di 11
1.
Bank IT officer Quizzes
1. Which is Computer Memory that does not forget ?
Ans: ROM
2. The computer memory holds data and ?
Ans: program
3. What is means by term RAM ?
Ans: Memory which can be both read and written to
4. Which computer memory is esentially empty ?
Ans: RAM
5. The bubbles in a bubble memory pack are created with the help of ?
Ans: magnetic field
6. Virtual memory is -
Ans: an illusion of an extremely large memory
7. Special locality refers to the problem that once a location is referenced
Ans: a nearby location will be referenced soon
8. An example of a SPOOLED device
Ans: A line printer used to print the output of a number of jobs
9. Page faults occurs when
Ans: one tries to divide a number by 0
10. Overlay is
Ans: a single contiguous memory that was used in the olden days for running large
programs by swapping
Operating System Question Answer
11. Concurrent processes are processes that -
Ans: Overlap in time
12. The page replacement policy that sometimes leads to more page faults when the
size of the memory is increased is -
Ans: FIFO
13. The only state transition that is initiated by the user process itself is -
Ans: Block
14. Fragmentation is -
Ans: fragments of memory words unused in a page
15. Give Example of real time systems
Ans: Aircraft control system, A process control system
PSU Papers for Computer Science
16. Dijkstras banking algorithm in an operating system solves the problem of -
Ans: Deadlock Avoidance
17. In a paged memory system, if the page size is increased, then the internal
fragmentation generally -
Ans: Becomes more
18. An operating system contains 3 user processes each requiring 2 units of resources
R. The minimum number of units of R such that no deadlock will ever occur is -
Ans: 4
19. Critical region is -
Ans: A set of instructions that access common shared resources which exclude one
another in time
20. Kernel is -
Ans: The set of primitive functions upon which the rest of operating system functions
are built up
21. Necessary conditions for deadlock are -
Ans: Non-preemption and circular wait, Mutual exclusion and partial allocation
22. In a time sharing operating system, when the time slot given to a process is
completed, the process goes from the RUNNING state to the -
Ans: READY state
23. Supervisor call -
Ans: Are privileged calls that are used to perform resource management functions,
which are controlled by the operating system
24. Semaphores are used to solve the problem of -
Ans: Mutual exclusion, Process synchronization
25. If the property of locality of reference is well pronounced in a program-
Ans: The number of page faults will be less
Operating System Question Answer for Competitive Exams
26. Pre-emptive scheduling, is the strategy of temporarily suspending a running
process-
Ans: before the CPU time slice expires
27. Mutual exclusion problem occurs -
Ans: among processes that share resources
27. Sector interleaving in disks is done by -
Ans: the operating system
28. Disk scheduling involves deciding-
Ans: the order in which disk access requests must be serviced
29. Dirty bit is used to show the -
Ans: page that is modified after being loaded into cache memory
30. Fence register is used for-
Ans: memory protection.
31. The first-fit, best-fit and worst-fit algorithm can be used for-
Ans: contiguous allocation of memory
32. Give example of single-user operating systems-
Ans: MS-DOS, XENIX
33. In Round Robin CPU Scheduling, as the time quantum is increased, the average
turn around time-
Ans: varies irregulary
34. In a multiprogramming environment-
Ans: more than one process resides in the memory
35. The size of the virtual memory depends on the size of the -
Ans: Address Bus
36. Give example of Scheduling Policies in which context switching never take place-
Ans: Shortest Job First, First-cum-first-served
37. Suppose that a process is in BLOCKED state waiting for some I/O service.
When the service is completed, it goes to the-
Ans: READY State.
Q1. What is Client-server Computing?
Ans: The short answer: Client/server is a computational architecture that involves
client processes
requesting service from server processes.
The long answer: Client/server computing is the logical extension of modular
programming. Modular programming has as its fundamental assumption that
separation of a large piece of software into its constituent parts (modules) creates
the possibility for easier development and better maintainability. Client/server
computing takes this a step farther by recognizing that those modules need not all be
executed within the same memory space.
With this architecture, the calling module becomes the client (that which requests
a service), and the called module becomes the server (that which provides the
service). The logical extension of this is to have clients and servers running on
the appropriate hardware and software platforms for their functions. For example,
database management system servers running on platforms specially designed and
configured to perform queries, or file servers running on platforms with special
elements for managing files. It is this latter perspective that has created the widely-
believed myth that client/server has something to do with PCs or Unix machines.
Q2 What is a Client process?
Ans: The client is a process (program) that sends a message to a server process
(program), requesting that the server perform a task (service). Client programs usually
manage the user-interface portion of the application, validate data entered by the
user, dispatch requests to server programs, and sometimes execute business logic.
The client-basedprocess is the front- end of the application that the user sees and
interacts with. The client process contains solution-specific logic and provides the
interface between the user and the rest of the application system. The client process
also manages the local resources that the user interacts with such as the monitor,
keyboard, workstation CPU and peripherals. One of the key elements of a client
workstation is the graphical user interface (GUI). Normally a part of operating system
i.e. the window manager detects user actions, manages the windows on the display
and displays the data in the windows.
Q3 What is a Server process?
Ans : A server process (program) fulfills the client request by performing the task
requested. Server programs generally receive requests from client programs, execute
database retrieval and updates, manage data integrity and dispatch responses to client
requests. Sometimes server programs execute common or complex business logic.
The server-based process may run on another machine on the network. This server
could be the host operating system or network file server; the server is then provided
both file system services and application services. Or in some cases, another desktop
machine provides the application services. The server process acts as a software
engine that manages shared resources such as databases, printers, communication
links, or high powered-processors. The server process performs the back-end tasks
that are common to similar applications.
Q4 What is a Two-Tier Architecture?
Ans : A two-tier architecture is where a client talks directly to a server, with no
intervening server. It is typically used in small environments (less than 50 users). A
common error in client/server development is to prototype an application in a small,
two-tier environment, and then scale up by simply adding more users to the server.
This approach will usually result in an ineffective system, as the server becomes
overwhelmed. To properly scale to hundreds or thousands of users, it is usually
necessary to move to a three-tier architecture.
Q5 What is a Three-Tier Architecture?
A three-tier architecture introduces a server (or an agent) between the client and the
server. The role of the agent is manyfold. It can provide translation services (as in
adapting a legacy application on a mainframe to a client/server environment),
metering services (as in acting as a transaction monitor to limit the number of
simultaneous requests to a given server), or intellegent agent services (as in mapping
a request to a number of different servers, collating the results, and returning a single
response to the client.
IT Officer Questions for Professional knowledge section
1. The ________ states that a foreign key must either match a primary key value in
another relation or it must be null.
(a) entity integrity rule
(b) referential integrity constraint
(c) action assertion
(d) composite attribute
(e) None of these
2. An applet ________
(a) is an interpreted program that runs on the client
(b) tracks the number of visitors to a Website
(c) is a compiled program that usually runs on the client
(d) collects data from visitors to a Website
(e) None of these
3. A ________ sometimes called a boot sector virus, executes when a computer boots
up because it resides in the boot sector of a floppy disk or the master boot record of a
hard disk.
(a) system virus
(b) Trojan horse virus
(c) file virus
(d) macro virus
(e) None of these
4. Which error detection method uses one's complement arithmetic?
(a) Simply parity check
(b) Checksum
(c) Two-dimensional parity check
(d) CRC
(e) None of these
5. A result of a computer virus can NOT lead to ________ .
(a) Disk Crash
(b) Mother Board Crash
(c) Corruption of program
(d) Deletion of files
(e) None of these
6. The network interface card of LAN is related to following layer of OSI Model
(a) Transport
(b) Network
(c) Data Link
(d) Physical
(e) All of these
7. Which of the following does NOT describe a data warehouse?
(a) Subject-oriented
(b) Integrated
(c) Time-variant
(d) Updateable
(e) None of these
8. Which of the following is TRUE ?
(a) Logical design is software-dependent
(b) In a distributed database, database is stored in one physical location
(c) Conceptual design translates the logical design into internal model
(d) Logical design is software independent
(e) None of these
9. A range check ________
(a) ensures that only the correct data type is entered into a field
(b) verifies that all required data is present
(c) determines whether a number is within a specified limit
(d) tests if the data in two or more associated fields is logical
(e) None of these
10. The total set of interlinked hypertext documents worldwide is-
(a) HTTP
(b) Browser
(c) WWW
(d) B2B
(e) None of these
11. With the object-oriented (OO) approach, an object encapsulates, or ________ .a
programmer.
(a) carries out, the details of an object for
(b) hides, the details of an object from
(c) reveals, the details of an object to
(d) extends, the details of an object beyond
(e) None of these
12. Every computer connected to an intranet or extranet must have a distinct
________
(a) firewall
(b) proxy server
(c) IP address
(d) domain name
(e) None of these
13. A table of bits in which each row represents the distinct values of a key?
(a) Join index
(b) Bitmap index
(c) B + Tree
(d) Hierarchical index
(e) None of these
14. The degree of detail that should be incorporated into a database depends on what?
(a) Data integrity
(b) The type of database
(c) The user's perspective
(d) The business practices and policies
(e) None of these
15. The ________ converts digital signals to analog signals for the purpose of
transmitting data over telephone lines.
(a) Modem
(b) Router
(c) Gateway
(d) Bridge
(e) All of these
16. Before a package can be used in a java program it must be ________ .
(a) executed
(b) referenced
(c) imported
(d) declared
(e) None of these
17. Choose the correct way to indicate that a line in a C++ program is a comment line,
that is, a line the will not be executed as an instruction ________ .
(a) begin the line with a # sign
(b) begin the line with double slashes (/ /)
(c) begin and end the line with double hyphens (- _ -)
(d) indent the line
(e) None of these
18. Programming language built into user programs such as Word and Excel are
known as ________
(a) 4GLs
(b) macro languages
(c) object-oriented languages
(d) visual programming languages
(e) None of these
19. Firewalls are used to protect against ________ .
(a) Unauthorized Attacks
(b) Virus Attacks
(c) Data Driven Attacks
(d) Fire Attacks
(e) All of these
20. This is a standard way for a Web server to pass a Web user's request to an
application program and to receive data back to forward to the user-
(a) Interrupt request
(b) Forward DNS lookup
(c) Data-Link layer
(d) File Transfer Protocol
(e) Common gateway interface
21. Three SQL, DDL, CREATE commands are ________ .
(a) Schema, Base and Table
(b) Base, Table and Schema
(c) Key, Base and Table
(d) Schema, Table and View
(e) None of these
22. Data are ________ in client/server computing.
(a) never sent to the client machine
(b) sent in very large sections to save processing time
(c) sent only upon the client's request
(d) sent in complete copies for the client to filter and sort
(e) sent from the client to the server for processing
23. Which of the following will NOT eliminates the ambiguities of a null value?
(a) Define the attribute as required
(b) Define subtypes
(c) Define each attribute as having an initial value that is recognized as blank
(d) Define supertypes
(e) None of these
24. The ________ directory is mandatory for every disk.
(a) Root
(b) Base
(c) Sub
(d) Case
(e) None of these
25. This is a group of servers that share work and may be able to back each other up if
one server fails.
(a) Channel bank
(b) Cluster
(c) Tiger team
(d) Serverless backup
(e) Logical unit
ANSWERS
1(a), 2. (c), 3. (e), 4. (b), 5. (b) 6. (e), 7. (d), 8. (a), 9. (c), 10. (a) 11. (b), 12. (c), 13.
(b), 14. (b), 15. (a) 16. (c), 17. (b), 18. (d), 19. (a), 20. (e) 21. (d), 22. (c), 23. (d), 24.
(c), 25. (b).
Potrebbero piacerti anche
- AIIMS - Structure of AtomDocumento3 pagineAIIMS - Structure of AtomVikas GargNessuna valutazione finora
- Isothermal ExpansionDocumento8 pagineIsothermal Expansionsoumalya481Nessuna valutazione finora
- AIIMS ElectrochemistryDocumento2 pagineAIIMS ElectrochemistryVikas GargNessuna valutazione finora
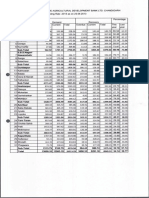
- The Punjab State Cooperative Bank Limited, SCO NO. 175-187, SECTOR 34-A, CHANDIGARHDocumento16 pagineThe Punjab State Cooperative Bank Limited, SCO NO. 175-187, SECTOR 34-A, CHANDIGARHGurjeetNessuna valutazione finora
- Answer KeyDocumento1 paginaAnswer KeyVikas GargNessuna valutazione finora
- Alpha Chemistry Classes: Alkaline Earth MetalsDocumento14 pagineAlpha Chemistry Classes: Alkaline Earth MetalsVikas GargNessuna valutazione finora
- Office of The Registering and Licensing Authority, U.T, Chandigarh Press NoteDocumento1 paginaOffice of The Registering and Licensing Authority, U.T, Chandigarh Press NoteVikas GargNessuna valutazione finora
- Windows Firewall: If You Are Not Using A Network Environment (I.e. USB Connection Only)Documento0 pagineWindows Firewall: If You Are Not Using A Network Environment (I.e. USB Connection Only)Milan KrcmarNessuna valutazione finora
- Cannon LPB3010Documento0 pagineCannon LPB3010lenceNessuna valutazione finora
- WWW - Ppsc.gov - in PDF Pscscce2013 PresylDocumento3 pagineWWW - Ppsc.gov - in PDF Pscscce2013 PresylVikas GargNessuna valutazione finora
- Apps On NT Best PracticesDocumento11 pagineApps On NT Best PracticesVikas GargNessuna valutazione finora
- Detailed Advst. & Information of 1192 Posts of ClerksDocumento9 pagineDetailed Advst. & Information of 1192 Posts of ClerksVikas GargNessuna valutazione finora
- Amc GuideDocumento2 pagineAmc GuideVikas GargNessuna valutazione finora
- The Punjab Cooperative Agricultural Development Banks Rules, 1959Documento14 pagineThe Punjab Cooperative Agricultural Development Banks Rules, 1959Vikas GargNessuna valutazione finora
- History of Modern IndiaDocumento12 pagineHistory of Modern IndiaTanmay JagetiaNessuna valutazione finora
- Defrag TutorialDocumento20 pagineDefrag TutorialVikas GargNessuna valutazione finora
- Benefits of DefragmentationDocumento4 pagineBenefits of DefragmentationVikas GargNessuna valutazione finora
- General Knowledge Know EverythingDocumento141 pagineGeneral Knowledge Know EverythingMudassir ShahNessuna valutazione finora
- Invoice HP Deskjet 2645Documento1 paginaInvoice HP Deskjet 2645Vikas GargNessuna valutazione finora
- CET (PG) - 2013: Panjab University, Chandigarh Answers / KeyDocumento35 pagineCET (PG) - 2013: Panjab University, Chandigarh Answers / KeyVikas GargNessuna valutazione finora
- Panjab University, Chandigarh UGLAW-2013 Answers Key: D A B C A D C B C CDocumento1 paginaPanjab University, Chandigarh UGLAW-2013 Answers Key: D A B C A D C B C CVikas GargNessuna valutazione finora
- Fast Color Scan To A PDF File - 3Documento1 paginaFast Color Scan To A PDF File - 3Vikas GargNessuna valutazione finora
- Panjab University, Chandigarh UGLAW-2013 Answers Key: D A B C A D C B C CDocumento1 paginaPanjab University, Chandigarh UGLAW-2013 Answers Key: D A B C A D C B C CVikas GargNessuna valutazione finora
- CompscDocumento11 pagineCompscVikas GargNessuna valutazione finora
- 104 GK FactsDocumento5 pagine104 GK FactsankitbhargavakietNessuna valutazione finora
- Panjab University, Chandigarh PUTHAT-2013 Answers Key: B A D A C C C C D BDocumento1 paginaPanjab University, Chandigarh PUTHAT-2013 Answers Key: B A D A C C C C D BVikas GargNessuna valutazione finora
- IBPS Computer Awareness Sample Questions 4Documento6 pagineIBPS Computer Awareness Sample Questions 4Brundaban MohapatraNessuna valutazione finora
- It Specialist Officers General Awarness Solved PaperDocumento15 pagineIt Specialist Officers General Awarness Solved PaperVikas GargNessuna valutazione finora
- It Officer Central Bank of IndiaDocumento6 pagineIt Officer Central Bank of IndiaMondar DebNessuna valutazione finora
- It Specialist Officers General Awarness Solved PaperDocumento15 pagineIt Specialist Officers General Awarness Solved PaperVikas GargNessuna valutazione finora
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (895)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (266)
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (400)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (588)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (74)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2259)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (121)
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- AT05 Configuration User Guide Ver1.11Documento11 pagineAT05 Configuration User Guide Ver1.11arcent30Nessuna valutazione finora
- DatapumpDocumento6 pagineDatapumpsam08077Nessuna valutazione finora
- It352 QPDocumento5 pagineIt352 QPRekha V RNessuna valutazione finora
- Silkworm 4100: Quickstart GuideDocumento12 pagineSilkworm 4100: Quickstart Guidevju000Nessuna valutazione finora
- Why Is My PDF Document Appearing As A Blank Page in Print PreviewDocumento1 paginaWhy Is My PDF Document Appearing As A Blank Page in Print PreviewVik BadNessuna valutazione finora
- setPartTrackAndTrace (V2.0) - v11-20230130 - 144759 PDFDocumento11 paginesetPartTrackAndTrace (V2.0) - v11-20230130 - 144759 PDFLucienNessuna valutazione finora
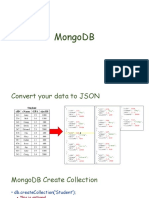
- Mongo DBDocumento35 pagineMongo DBSaurabh Srivastava100% (1)
- Clyde Tuitt ResumeDocumento2 pagineClyde Tuitt ResumeClyde J TuittNessuna valutazione finora
- P20e en 02+CP1L PDFDocumento16 pagineP20e en 02+CP1L PDFvasquezbencomoNessuna valutazione finora
- ELEE28706D AlgorithmAnalysis S3Documento34 pagineELEE28706D AlgorithmAnalysis S3Ehtisham MalikNessuna valutazione finora
- Express Scribe User ManualDocumento62 pagineExpress Scribe User ManualEden Sansão MucacheNessuna valutazione finora
- Coding Systems For Text-Based Data: Ascii and EbcdicDocumento3 pagineCoding Systems For Text-Based Data: Ascii and EbcdicRicHArdNessuna valutazione finora
- (SPFMX-1850) CUS - Material S Data Transmition GTM - SOP IT APD JIRADocumento2 pagine(SPFMX-1850) CUS - Material S Data Transmition GTM - SOP IT APD JIRAsergio escamillaNessuna valutazione finora
- PoemDocumento147 paginePoemAvipsita Das100% (1)
- Origin of ComputerDocumento106 pagineOrigin of ComputerMenesKhidaAngelicaNessuna valutazione finora
- AdsbScope Release 2.7 User GuideDocumento80 pagineAdsbScope Release 2.7 User GuideMandu Ceriano100% (1)
- 9-2 Pointers For Inter-Function Communication: Passing Addresses Functions Returning PointersDocumento42 pagine9-2 Pointers For Inter-Function Communication: Passing Addresses Functions Returning PointersRavi TejaNessuna valutazione finora
- Deploying TCS Usng GPODocumento5 pagineDeploying TCS Usng GPOAgaje O. KelvinNessuna valutazione finora
- Siemens DP/PA Coupler, Active Field Distributors, DP/PA Link and Y Link Operating InstructionsDocumento266 pagineSiemens DP/PA Coupler, Active Field Distributors, DP/PA Link and Y Link Operating InstructionsmaseloNessuna valutazione finora
- Jntu C Lab ProgramsDocumento66 pagineJntu C Lab Programssureshgoud2Nessuna valutazione finora
- Model Question PaperDocumento2 pagineModel Question PaperLalithkumarNessuna valutazione finora
- KM2021XSTUDDocumento222 pagineKM2021XSTUDBeata SzwichtenbergNessuna valutazione finora
- Grok System Design InterviewDocumento163 pagineGrok System Design InterviewCarlos Rojas100% (3)
- 3 - Course PlanDocumento2 pagine3 - Course PlanRajeshwari R PNessuna valutazione finora
- Pps Using C r20 - Unit-3Documento20 paginePps Using C r20 - Unit-3Raj AryanNessuna valutazione finora
- Dell Emc Vxrail: Solution BriefDocumento2 pagineDell Emc Vxrail: Solution BriefArkhanaNessuna valutazione finora
- Prishtina Insight 95 ArticleDocumento1 paginaPrishtina Insight 95 Articlesabedin_mNessuna valutazione finora
- American Megatrends StorTrends User's GuideDocumento133 pagineAmerican Megatrends StorTrends User's GuideAtul MahajanNessuna valutazione finora
- Install Wekan Kanban Board System On Ubuntu 20.04 - 18.04 - ComputingForGeeksDocumento19 pagineInstall Wekan Kanban Board System On Ubuntu 20.04 - 18.04 - ComputingForGeeksCarlos Andrey MontoyaNessuna valutazione finora
- M365 Modern Desktop Administrator Learning Path (Oct 2019)Documento1 paginaM365 Modern Desktop Administrator Learning Path (Oct 2019)m00anj00Nessuna valutazione finora