Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Multi-Master Replication of OpenLDAP Server On CentOS 6.4
Caricato da
Sharizan SumuuiTitolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Multi-Master Replication of OpenLDAP Server On CentOS 6.4
Caricato da
Sharizan SumuuiCopyright:
Formati disponibili
Multi-Master Replication Of OpenLDAP Server on CentOS
6.4
In this post I will try to explain how to configure multi-master replication of OpenLDAP
Server on CentOS 6.4
In my previous post, I have shown you how to configure OpenLDAP Server with SASL/TLS.
If you dont know how to configure, please visit this link
http://easylinuxtutorials.blogspot.in/2013/11/installing-configuring-openldap-
server.html
Some important point about multi-master replication:
In previous releases of OpenLDAP, replication was discussed in terms of a master server
and some slave servers.
In OpenLDAP version 2.4.x, it support multi-master replication model.
The LDAP Sync Replication engine, syncrepl for short, is a consumer-side replication
engine that enables the consumer LDAP server to maintain a shadow copy of a DIT.
A provider replicates directory updates to consumers.
Consumers receive replication updates from providers.
In simple, layman terms, Provider means Master, Consumer means Slave.
In multi-master all providers acts as consumers.
In multi-master replication, syncrepl supports two synchronization operations, i.e.
refreshOnly and refreshAndPersist.
In refreshOnly mode synchronization, the provider uses a pull-based synchronization
where the consumer servers need not be tracked and no history information is
maintained.
In refreshAndPersist mode of synchronization, the provider uses a push-based
synchronization. The provider keeps track of the consumer servers that have
requested the persistent search and sends them necessary updates as the provider
replication content gets modified.
1) Copy the LDAP1 server public key file to the LDAP2 server and LDAP2 server public key
file to LDAP1 server in this location /etc/openldap/certs
[root@ldap1 ~]# scp
ldap2:/etc/pki/tls/certs/ldap2pub.pem /etc/openldap/certs/
[root@ldap1 ~]# scp /etc/pki/tls/certs/ldap1pub.pem
ldap2:/etc/openldap/certs/
2) Set the permissions on the copied public key files to ldap on LDAP1 and LDAP2 Servers
[root@ldap1 ~]# chown ldap. /etc/openldap/certs/ldap2pub.pem
[root@ldap2 ~]# chown ldap. /etc/openldap/certs/ldap1pub.pem
3) Configure /etc/openldap.slapd.conf as below on both LDAP1 and LDAP2 Servers
[root@ldap1 ~]# vim /etc/openldap/slapd.conf
#
# See slapd.conf(5) for details on configuration options.
# This file should NOT be world readable.
#
include /etc/openldap/schema/corba.schema
include /etc/openldap/schema/core.schema
include /etc/openldap/schema/cosine.schema
include /etc/openldap/schema/duaconf.schema
include /etc/openldap/schema/dyngroup.schema
include /etc/openldap/schema/inetorgperson.schema
include /etc/openldap/schema/java.schema
include /etc/openldap/schema/misc.schema
include /etc/openldap/schema/nis.schema
include /etc/openldap/schema/openldap.schema
include /etc/openldap/schema/ppolicy.schema
include /etc/openldap/schema/collective.schema
# Allow LDAPv2 client connections. This is NOT the default.
allow bind_v2
# Do not enable referrals until AFTER you have a working directory
# service AND an understanding of referrals.
#referral ldap://root.openldap.org
pidfile /var/run/openldap/slapd.pid
argsfile /var/run/openldap/slapd.args
# Load dynamic backend modules
# - modulepath is architecture dependent value (32/64-bit system)
# - back_sql.la overlay requires openldap-server-sql package
# - dyngroup.la and dynlist.la cannot be used at the same time
# modulepath /usr/lib/openldap
# modulepath /usr/lib64/openldap
# moduleload accesslog.la
# moduleload auditlog.la
# moduleload back_sql.la
# moduleload chain.la
# moduleload collect.la
# moduleload constraint.la
# moduleload dds.la
# moduleload deref.la
# moduleload dyngroup.la
# moduleload dynlist.la
# moduleload memberof.la
# moduleload pbind.la
# moduleload pcache.la
# moduleload ppolicy.la
# moduleload refint.la
# moduleload retcode.la
# moduleload rwm.la
# moduleload seqmod.la
# moduleload smbk5pwd.la
# moduleload sssvlv.la
moduleload syncprov.la
# moduleload translucent.la
# moduleload unique.la
# moduleload valsort.la
# The next three lines allow use of TLS for encrypting connections
using a
# dummy test certificate which you can generate by running
# /usr/libexec/openldap/generate-server-cert.sh. Your client software
may balk
# at self-signed certificates, however.
#TLSCACertificatePath /etc/openldap/certs
#TLSCertificateFile "\"OpenLDAP Server\""
#TLSCertificateKeyFile /etc/openldap/certs/password
TLSCertificateFile "/etc/pki/tls/certs/ldap1pub.pem"
TLSCertificateKeyFile "/etc/pki/tls/certs/ldap1key.pem"
# Sample security restrictions
# Require integrity protection (prevent hijacking)
# Require 112-bit (3DES or better) encryption for updates
# Require 63-bit encryption for simple bind
# security ssf=1 update_ssf=112 simple_bind=64
# Sample access control policy:
# Root DSE: allow anyone to read it
# Subschema (sub)entry DSE: allow anyone to read it
# Other DSEs:
# Allow self write access
# Allow authenticated users read access
# Allow anonymous users to authenticate
# Directives needed to implement policy:
# access to dn.base="" by * read
# access to dn.base="cn=Subschema" by * read
# access to *
# by self write
# by users read
# by anonymous auth
#
# if no access controls are present, the default policy
# allows anyone and everyone to read anything but restricts
# updates to rootdn. (e.g., "access to * by * read")
#
# rootdn can always read and write EVERYTHING!
# enable on-the-fly configuration (cn=config)
database config
access to *
by
dn.exact="gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth"
manage
by * none
# enable server status monitoring (cn=monitor)
database monitor
access to *
by
dn.exact="gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth"
read
by dn.exact="cn=Manager,dc=example,dc=com" read
by * none
#####################################################################
##
# database definitions
#####################################################################
##
database bdb
suffix "dc=example,dc=com"
checkpoint 1024 15
rootdn "cn=Manager,dc=example,dc=com"
rootpw {SSHA}5h1vaYgy7fOLash39ZFKLQ3TOzqNYk/g
loglevel 256
sizelimit unlimited
# Cleartext passwords, especially for the rootdn, should
# be avoided. See slappasswd(8) and slapd.conf(5) for details.
# Use of strong authentication encouraged.
# rootpw secret
# rootpw {crypt}ijFYNcSNctBYg
# The database directory MUST exist prior to running slapd AND
# should only be accessible by the slapd and slap tools.
# Mode 700 recommended.
directory /var/lib/ldap
# Indices to maintain for this database
index objectClass eq,pres
index ou,cn,mail,surname,givenname eq,pres,sub
index uidNumber,gidNumber,loginShell eq,pres
index uid,memberUid eq,pres,sub
index nisMapName,nisMapEntry eq,pres,sub
# Replicas of this database
#replogfile /var/lib/ldap/openldap-master-replog
#replica host=ldap-1.example.com:389 starttls=critical
# bindmethod=sasl saslmech=GSSAPI
# authcId=host/ldap-master.example.com@EXAMPLE.COM
# Multi master replication
ServerID 1 "ldaps://ldap1.example.com"
ServerID 2 "ldaps://ldap2.example.com"
overlay syncprov
syncprov-checkpoint 10 1
syncprov-sessionlog 100
syncrepl rid=1
provider="ldaps://ldap1.example.com"
type=refreshAndPersist
interval=00:00:00:10
retry="5 10 60 +"
timeout=1
schemachecking=off
searchbase="dc=example,dc=com"
scope=sub
bindmethod=simple
tls_cacert=/etc/pki/tls/certs/ldap1pub.pem
binddn="cn=Manager,dc=example,dc=com"
credentials="redhat"
syncrepl rid=2
provider="ldaps://ldap2.example.com"
type=refreshAndPersist
interval=00:00:00:10
retry="5 10 60 +"
timeout=1
schemachecking=off
scope=sub
searchbase="dc=example,dc=com"
bindmethod=simple
tls_cacert=/etc/openldap/certs/ldap2pub.pem
binddn="cn=Manager,dc=example,dc=com"
credentials="redhat"
MirrorMode on
4) Convert the slapd.conf to cn=config format and re-initialize the slapd.d folder
on LDAP1 and LDAP2 Servers
[root@ldap1 ~]# rm -rf /etc/openldap/slapd.d/*
[root@ldap1 ~]# slaptest -u
[root@ldap1 ~]# slaptest -f /etc/openldap/slapd.conf -F
/etc/openldap/slapd.d/
5) Change the permissions on the /etc/openldap/slapd.d/ to ldap on LDAP1 and LDAP2
Servers
[root@ldap1 ~]# chown -R ldap. /etc/openldap/slapd.d/
6) Restart the slapd service on LDAP1 and LDAP2 Servers
[root@ldap1 ~]# service slapd restart
7) Check whether replication is working or not by adding an entry into DIT on both servers,
the entry should be visible by ldapsearch on both server if it is added on anyone of them.
8) If there is any problem in replication check the log file /var/log/ldap for more
information and troubleshooting.
Configuration terms used in /etc/openldap/slapd.conf for replication
rid -> replica ID for servers, which should be numeric and unique for each server
provider -> URI of ldap server which will be the master server
type -> type of synchronization between LDAP servers for replication
interval -> time interval for initial synchronization process i.e. 10 secs here
retry -> retry the synchronization process if incase consumer is not available i.e. retry 10
times every 5 seconds, if it fails and then every 60 sec it will continue
timeout -> timeout incase of failure in retry i.e. 1 sec
schemachecking -> off means will not check for schema during schema
searchbase -> search base that will be replicated to the other server
scope -> sub means all the sub DNs will be replicated
bindmethod -> connection type for replication process
binddn -> the user authorized for replication process
credentials -> user password for the user initiating the replication process
Potrebbero piacerti anche
- Quick Configuration of Openldap and Kerberos In Linux and Authenicating Linux to Active DirectoryDa EverandQuick Configuration of Openldap and Kerberos In Linux and Authenicating Linux to Active DirectoryNessuna valutazione finora
- Fisiere Modificate Ldap ClientDocumento8 pagineFisiere Modificate Ldap ClientBogdan MarghescuNessuna valutazione finora
- Configuration of a Simple Samba File Server, Quota and Schedule BackupDa EverandConfiguration of a Simple Samba File Server, Quota and Schedule BackupNessuna valutazione finora
- Sz. Melléklet: Az Önálló PDC-ként Működő Samba Szerver Konfigurációs ÁllományaDocumento13 pagineSz. Melléklet: Az Önálló PDC-ként Működő Samba Szerver Konfigurációs ÁllományaÁkos KeresztesNessuna valutazione finora
- Configuration of a Simple Samba File Server, Quota and Schedule BackupDa EverandConfiguration of a Simple Samba File Server, Quota and Schedule BackupNessuna valutazione finora
- Hướng dẫn cấu hình Primary Domain Controller with SambaDocumento17 pagineHướng dẫn cấu hình Primary Domain Controller with Sambaptit2004Nessuna valutazione finora
- DRBD-Cookbook: How to create your own cluster solution, without SAN or NAS!Da EverandDRBD-Cookbook: How to create your own cluster solution, without SAN or NAS!Nessuna valutazione finora
- Openldap SuccessDocumento8 pagineOpenldap SuccessrsaravanaveluNessuna valutazione finora
- Quick and Dirty Openldap Replication: A. Install Os and LdapDocumento5 pagineQuick and Dirty Openldap Replication: A. Install Os and LdapmohitadmnNessuna valutazione finora
- openLDAP Mirror Mode ReplicationDocumento5 pagineopenLDAP Mirror Mode ReplicationAdzmely MansorNessuna valutazione finora
- Configure LDAP Client To Authenticate With LDAP ServerDocumento6 pagineConfigure LDAP Client To Authenticate With LDAP Serverlatifa guesmiNessuna valutazione finora
- Authenticating Windows To OpenLDAP Server On Ubuntu 9Documento17 pagineAuthenticating Windows To OpenLDAP Server On Ubuntu 9vno2000Nessuna valutazione finora
- LDAPDocumento5 pagineLDAPVineeth NandanamNessuna valutazione finora
- Ldap Configuration With TlsDocumento5 pagineLdap Configuration With Tlsmohitmathur9Nessuna valutazione finora
- Ldap With ReplicationDocumento12 pagineLdap With ReplicationShrini VasanNessuna valutazione finora
- Eduroam Installation in ZambiaDocumento11 pagineEduroam Installation in ZambiaThomas YobeNessuna valutazione finora
- Step by Step OpenLDAP Server Configuration On CentOS 7Documento5 pagineStep by Step OpenLDAP Server Configuration On CentOS 7kamakom78Nessuna valutazione finora
- Step-By-Step Openldap: On This PageDocumento5 pagineStep-By-Step Openldap: On This PageNagarajuRbNessuna valutazione finora
- Samba+Postfix With Ldap ServerDocumento11 pagineSamba+Postfix With Ldap ServermanojgodiyalNessuna valutazione finora
- BSD Guides: Doing Stuff With FreeBSD, NetBSD, OpenBSD, & Mac OS XDocumento9 pagineBSD Guides: Doing Stuff With FreeBSD, NetBSD, OpenBSD, & Mac OS XaalejosdNessuna valutazione finora
- TP LdapDocumento3 pagineTP Ldapسعيد الطنجاويNessuna valutazione finora
- Directory ServerDocumento47 pagineDirectory Serversanju_81Nessuna valutazione finora
- OpenLDAP Server Configuration On RHEL7Documento6 pagineOpenLDAP Server Configuration On RHEL7amit_iihtdhn280Nessuna valutazione finora
- LDAP CommandsDocumento4 pagineLDAP CommandsptrscribdNessuna valutazione finora
- TP5.-CentOS OpenLDAPDocumento7 pagineTP5.-CentOS OpenLDAPEmma maNessuna valutazione finora
- Freeradius For Windows: Server EditionDocumento13 pagineFreeradius For Windows: Server EditionHaris SpringNessuna valutazione finora
- Ldap Authentication ConfigDocumento10 pagineLdap Authentication ConfigJohn DoeNessuna valutazione finora
- Linux SAN Related CommandsDocumento7 pagineLinux SAN Related CommandsShashi KanthNessuna valutazione finora
- LDAP TutorialDocumento28 pagineLDAP Tutorialzorrito26Nessuna valutazione finora
- 389 Directory ServerDocumento24 pagine389 Directory ServerRajMohenNessuna valutazione finora
- Manual de Freradius - Radius - Dalo 2020Documento10 pagineManual de Freradius - Radius - Dalo 2020Jonathan DominguezNessuna valutazione finora
- HTB1Documento7 pagineHTB1Nonight gamsNessuna valutazione finora
- Creds: 1. DatabaseDocumento7 pagineCreds: 1. DatabaseNonight gamsNessuna valutazione finora
- iRedMail SOGo v4 PDFDocumento6 pagineiRedMail SOGo v4 PDFmamat_doNessuna valutazione finora
- Configuring LDAP Client: Solaris 9Documento6 pagineConfiguring LDAP Client: Solaris 9ccokerNessuna valutazione finora
- Free Radius ConfigurationDocumento14 pagineFree Radius ConfigurationAgus Setiawan100% (2)
- OpenLdap Documentation1Documento14 pagineOpenLdap Documentation1kourosh nosrati heraviNessuna valutazione finora
- Ldap Server ConfigurationDocumento20 pagineLdap Server ConfigurationSaminadane ThiyagarajanNessuna valutazione finora
- Accel PPPDocumento46 pagineAccel PPPraphaelrrlNessuna valutazione finora
- Practical LDAP and LinuxDocumento28 paginePractical LDAP and LinuxPablinchox100% (1)
- RHCSA Solved PaperDocumento5 pagineRHCSA Solved PaperdSolarian0% (1)
- Do280 20191230Documento10 pagineDo280 20191230Mousam BhagatNessuna valutazione finora
- LDAPKeyserver - GnuPG WikiDocumento10 pagineLDAPKeyserver - GnuPG Wikijuan perezNessuna valutazione finora
- RHCSASolved PDFDocumento5 pagineRHCSASolved PDFDuluth MarketsNessuna valutazione finora
- ABD00 Notebooks Combined - DatabricksDocumento109 pagineABD00 Notebooks Combined - DatabricksBruno TelesNessuna valutazione finora
- Mastering Postgresql Administration: B M, E DB April, 2009Documento111 pagineMastering Postgresql Administration: B M, E DB April, 2009mehul3685Nessuna valutazione finora
- Create A Global Addressbook With OpenLDAP 2Documento12 pagineCreate A Global Addressbook With OpenLDAP 2info infoNessuna valutazione finora
- Qmail With Ldap: Download DirectoryDocumento12 pagineQmail With Ldap: Download DirectoryramngngNessuna valutazione finora
- How To Install Linux, Apache, Mysql, PHP (Lamp) Stack On Debian 9 StretchDocumento24 pagineHow To Install Linux, Apache, Mysql, PHP (Lamp) Stack On Debian 9 StretchHenry CahyoNessuna valutazione finora
- Directory Server Centos55Documento11 pagineDirectory Server Centos55Yiannis PanteleakisNessuna valutazione finora
- ManagerDocumento11 pagineManagerAbdennacer AyebNessuna valutazione finora
- Windows Red Team Cheat SheatDocumento13 pagineWindows Red Team Cheat SheatReniere SantosNessuna valutazione finora
- Freeradius3 0 3onubuntu14 04ltsDocumento21 pagineFreeradius3 0 3onubuntu14 04ltsClia AnickNessuna valutazione finora
- Redhat Linux EnterpriseDocumento13 pagineRedhat Linux EnterpriseFaisal Saeed SaeedNessuna valutazione finora
- LDAP Configuration For RHEL 6 Server and Ubuntu 12.04 ClientDocumento4 pagineLDAP Configuration For RHEL 6 Server and Ubuntu 12.04 ClientSanjay SangwanNessuna valutazione finora
- LDAPDocumento6 pagineLDAPanitajayantNessuna valutazione finora
- Readme PDFDocumento13 pagineReadme PDFFreddy ManullangNessuna valutazione finora
- Configure AIX To Authenticate To ADDocumento5 pagineConfigure AIX To Authenticate To ADthanhlv2Nessuna valutazione finora
- AirPort Extreme and Bluetooth Regulatory CertificationDocumento1 paginaAirPort Extreme and Bluetooth Regulatory CertificationkeelparNessuna valutazione finora
- Xcode 3.1.1 Developer Tools For Mac OS X v10.5Documento6 pagineXcode 3.1.1 Developer Tools For Mac OS X v10.5Sharizan SumuuiNessuna valutazione finora
- About Xcode ToolsDocumento6 pagineAbout Xcode ToolsElise BurchNessuna valutazione finora
- About Xcode ToolsDocumento6 pagineAbout Xcode ToolsElise BurchNessuna valutazione finora
- Master Biz Administartion 4.8.17 FA - CompressedDocumento2 pagineMaster Biz Administartion 4.8.17 FA - CompressedSharizan SumuuiNessuna valutazione finora
- RHB Report Reg - Plantation - Thematic - 20200721 - RHB 55105792099995565f16d9296e1e7 Lwd3ral6pt20200722Documento17 pagineRHB Report Reg - Plantation - Thematic - 20200721 - RHB 55105792099995565f16d9296e1e7 Lwd3ral6pt20200722Sharizan SumuuiNessuna valutazione finora
- How To Forward Traffic Logs To Syslog Server - Live CommunityDocumento3 pagineHow To Forward Traffic Logs To Syslog Server - Live CommunitySharizan SumuuiNessuna valutazione finora
- The 20 Minute Business Plan: Business Model Canvas Made EasyDocumento19 pagineThe 20 Minute Business Plan: Business Model Canvas Made EasySharizan SumuuiNessuna valutazione finora
- Capacity Planning For DNS - UoB UnixDocumento6 pagineCapacity Planning For DNS - UoB UnixSharizan SumuuiNessuna valutazione finora
- Handouts - Part 1 (Oct10)Documento7 pagineHandouts - Part 1 (Oct10)Sharizan SumuuiNessuna valutazione finora
- 01 Implementing BGP RoutingDocumento42 pagine01 Implementing BGP RoutingSharizan SumuuiNessuna valutazione finora
- INtroduction To Nagios by Ethan GalstadDocumento49 pagineINtroduction To Nagios by Ethan GalstadSharizan SumuuiNessuna valutazione finora
- Sky Is The Limit 1Documento6 pagineSky Is The Limit 1Sharizan SumuuiNessuna valutazione finora
- How To Forward Traffic Logs To Syslog Server - Live CommunityDocumento3 pagineHow To Forward Traffic Logs To Syslog Server - Live CommunitySharizan SumuuiNessuna valutazione finora
- How To Build Weathermap in CACTiDocumento1 paginaHow To Build Weathermap in CACTiSharizan SumuuiNessuna valutazione finora
- EDU080626 TLIM Process Timeline (v1.1.4)Documento2 pagineEDU080626 TLIM Process Timeline (v1.1.4)Sharizan SumuuiNessuna valutazione finora
- 7HabFam Virt Cert SLPSHT EDU (v1.0.2)Documento1 pagina7HabFam Virt Cert SLPSHT EDU (v1.0.2)Sharizan SumuuiNessuna valutazione finora
- Ds Zoneflex r500 PDFDocumento4 pagineDs Zoneflex r500 PDFSharizan SumuuiNessuna valutazione finora
- BGP Concepts and TheoryDocumento3 pagineBGP Concepts and TheorySharizan SumuuiNessuna valutazione finora
- BGP CommunityDocumento4 pagineBGP CommunitySharizan SumuuiNessuna valutazione finora
- BGP AttributeDocumento63 pagineBGP AttributeAniket RasalNessuna valutazione finora
- Cisco TE With 12000 Router SeriesDocumento306 pagineCisco TE With 12000 Router SeriesSharizan SumuuiNessuna valutazione finora
- Mincom: Release NotesDocumento44 pagineMincom: Release NotesLodyNessuna valutazione finora
- AkamaiDocumento78 pagineAkamaiBala SubramanyamNessuna valutazione finora
- Use of Wrapper Classes in JavaDocumento5 pagineUse of Wrapper Classes in Javafunny mania worldNessuna valutazione finora
- Computer System OrganizationDocumento133 pagineComputer System OrganizationdexterdubeyNessuna valutazione finora
- LDPC Tutorial Mod1Documento55 pagineLDPC Tutorial Mod1JerryNessuna valutazione finora
- Oracle Apps Gurus - Imp Sales Order QueriesDocumento3 pagineOracle Apps Gurus - Imp Sales Order QueriesAravind AllamNessuna valutazione finora
- Visual Basic 6 VariablesDocumento44 pagineVisual Basic 6 Variablesz0r00zh100% (1)
- UC-3500 Host Communication Specifications (Except North America)Documento47 pagineUC-3500 Host Communication Specifications (Except North America)Олександр100% (1)
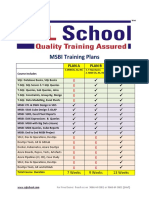
- MSBI Training Plans: Plan A Plan B Plan CDocumento14 pagineMSBI Training Plans: Plan A Plan B Plan CVeerendra ReddyNessuna valutazione finora
- Page 196Documento1 paginaPage 196Hasantha PathiranaNessuna valutazione finora
- progISP Manual PDFDocumento4 pagineprogISP Manual PDFNur AntoNessuna valutazione finora
- RS-449 Serial Interface StandardsDocumento9 pagineRS-449 Serial Interface StandardsGlenda GragedaNessuna valutazione finora
- Webcopy OriginDocumento18 pagineWebcopy Originfelipe appleNessuna valutazione finora
- Td2058 PDFDocumento1 paginaTd2058 PDFOney Enrique Mendez MercadoNessuna valutazione finora
- HW Task 1Documento8 pagineHW Task 1Royale FairyNessuna valutazione finora
- Basic IT EnglishDocumento2 pagineBasic IT EnglishVarga NaomiNessuna valutazione finora
- 嵌入式系統 Introduction to Embedded System Design: Part 5: Serial Communication (UART)Documento26 pagine嵌入式系統 Introduction to Embedded System Design: Part 5: Serial Communication (UART)N26094354鐘筠凱Nessuna valutazione finora
- GCBASIC Command GuideDocumento9 pagineGCBASIC Command GuideJoao Joaquim100% (1)
- DVB Digital Video BroadcastingDocumento53 pagineDVB Digital Video BroadcastingBeky GuellautineNessuna valutazione finora
- CSE 1002: (Problem Solving and Object Oriented Programming)Documento3 pagineCSE 1002: (Problem Solving and Object Oriented Programming)JskNessuna valutazione finora
- PDI2000 LabsDocumento281 paginePDI2000 LabsBhaskar ReddyNessuna valutazione finora
- Hadoop Exercise MapreduceDocumento5 pagineHadoop Exercise MapreduceSureshAnand CSENessuna valutazione finora
- 0478 - 11 Computer Science - Question Paper June 2018Documento12 pagine0478 - 11 Computer Science - Question Paper June 2018laiba munirNessuna valutazione finora
- Unicel Host Interface Specifications - DXC AllDocumento170 pagineUnicel Host Interface Specifications - DXC AllRuny RunyNessuna valutazione finora
- Assignment: Advance Marketing Research & Data AnalyticsDocumento4 pagineAssignment: Advance Marketing Research & Data AnalyticsAnwar khanNessuna valutazione finora
- Ananth Manaseh NadarDocumento5 pagineAnanth Manaseh NadarSourabh SharmaNessuna valutazione finora
- Computer Literacy MCQ Quiz - Objective Question With Answer For Computer Literacy - Download Free PDFDocumento34 pagineComputer Literacy MCQ Quiz - Objective Question With Answer For Computer Literacy - Download Free PDFTiotsop Lambou DuclairNessuna valutazione finora
- Conducting Cambridge IGCSE ICT (0417) Practical Tests June 2022Documento5 pagineConducting Cambridge IGCSE ICT (0417) Practical Tests June 2022Aurpa RahmanNessuna valutazione finora
- Penentuan Jurusan Siswa Sekolah Menengah Atas Disesuaikan Dengan Minat Siswa Menggunakan Algoritma Fuzzy C-MeansDocumento12 paginePenentuan Jurusan Siswa Sekolah Menengah Atas Disesuaikan Dengan Minat Siswa Menggunakan Algoritma Fuzzy C-Meansnovi dewi angelinaNessuna valutazione finora
- Brij Kishor SinghDocumento4 pagineBrij Kishor SinghPhani PNessuna valutazione finora
- Dark Data: Why What You Don’t Know MattersDa EverandDark Data: Why What You Don’t Know MattersValutazione: 4.5 su 5 stelle4.5/5 (3)
- Grokking Algorithms: An illustrated guide for programmers and other curious peopleDa EverandGrokking Algorithms: An illustrated guide for programmers and other curious peopleValutazione: 4 su 5 stelle4/5 (16)
- Starting Database Administration: Oracle DBADa EverandStarting Database Administration: Oracle DBAValutazione: 3 su 5 stelle3/5 (2)
- SQL QuickStart Guide: The Simplified Beginner's Guide to Managing, Analyzing, and Manipulating Data With SQLDa EverandSQL QuickStart Guide: The Simplified Beginner's Guide to Managing, Analyzing, and Manipulating Data With SQLValutazione: 4.5 su 5 stelle4.5/5 (46)
- Blockchain Basics: A Non-Technical Introduction in 25 StepsDa EverandBlockchain Basics: A Non-Technical Introduction in 25 StepsValutazione: 4.5 su 5 stelle4.5/5 (24)
- Fusion Strategy: How Real-Time Data and AI Will Power the Industrial FutureDa EverandFusion Strategy: How Real-Time Data and AI Will Power the Industrial FutureNessuna valutazione finora
- THE STEP BY STEP GUIDE FOR SUCCESSFUL IMPLEMENTATION OF DATA LAKE-LAKEHOUSE-DATA WAREHOUSE: "THE STEP BY STEP GUIDE FOR SUCCESSFUL IMPLEMENTATION OF DATA LAKE-LAKEHOUSE-DATA WAREHOUSE"Da EverandTHE STEP BY STEP GUIDE FOR SUCCESSFUL IMPLEMENTATION OF DATA LAKE-LAKEHOUSE-DATA WAREHOUSE: "THE STEP BY STEP GUIDE FOR SUCCESSFUL IMPLEMENTATION OF DATA LAKE-LAKEHOUSE-DATA WAREHOUSE"Valutazione: 3 su 5 stelle3/5 (1)
- Business Intelligence Strategy and Big Data Analytics: A General Management PerspectiveDa EverandBusiness Intelligence Strategy and Big Data Analytics: A General Management PerspectiveValutazione: 5 su 5 stelle5/5 (5)
- Cloud Computing Playbook: 10 In 1 Practical Cloud Design With Azure, Aws And TerraformDa EverandCloud Computing Playbook: 10 In 1 Practical Cloud Design With Azure, Aws And TerraformNessuna valutazione finora
- IBM DB2 Administration Guide: Installation, Upgrade and Configuration of IBM DB2 on RHEL 8, Windows 10 and IBM Cloud (English Edition)Da EverandIBM DB2 Administration Guide: Installation, Upgrade and Configuration of IBM DB2 on RHEL 8, Windows 10 and IBM Cloud (English Edition)Nessuna valutazione finora
- ITIL 4: Digital and IT strategy: Reference and study guideDa EverandITIL 4: Digital and IT strategy: Reference and study guideValutazione: 5 su 5 stelle5/5 (1)
- ITIL 4: Direct, plan and improve: Reference and study guideDa EverandITIL 4: Direct, plan and improve: Reference and study guideNessuna valutazione finora
- Modelling Business Information: Entity relationship and class modelling for Business AnalystsDa EverandModelling Business Information: Entity relationship and class modelling for Business AnalystsNessuna valutazione finora
- Mastering Amazon Relational Database Service for MySQL: Building and configuring MySQL instances (English Edition)Da EverandMastering Amazon Relational Database Service for MySQL: Building and configuring MySQL instances (English Edition)Nessuna valutazione finora
- Joe Celko's SQL for Smarties: Advanced SQL ProgrammingDa EverandJoe Celko's SQL for Smarties: Advanced SQL ProgrammingValutazione: 3 su 5 stelle3/5 (1)
- DB2 9 System Administration for z/OS: Certification Study Guide: Exam 737Da EverandDB2 9 System Administration for z/OS: Certification Study Guide: Exam 737Valutazione: 3 su 5 stelle3/5 (2)
- Web Dragons: Inside the Myths of Search Engine TechnologyDa EverandWeb Dragons: Inside the Myths of Search Engine TechnologyValutazione: 4.5 su 5 stelle4.5/5 (2)
- Big Data and Analytics: The key concepts and practical applications of big data analytics (English Edition)Da EverandBig Data and Analytics: The key concepts and practical applications of big data analytics (English Edition)Nessuna valutazione finora