Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Heartbleed, A Long-Undiscovered Bug in Cryptographic Software Called OpenSSL
Caricato da
BobapatatasTitolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Heartbleed, A Long-Undiscovered Bug in Cryptographic Software Called OpenSSL
Caricato da
BobapatatasCopyright:
Formati disponibili
re adwrit e .co m http://readwrite.
co m/2014/04/08/heartbleed-o penssl-bug-crypto graphy-web-security#awesm=~o AT9h0eIRIxI4Y
What You Need To Know About Heartbleed, A Really Major Bug That Short-Circuits Web Security ReadWrite
Lauren Orsini
Heartbleed, a long-undiscovered bug in cryptographic sof tware called OpenSSL that secures Web communications, may have lef t roughly two-thirds of the Web vulnerable to eavesdropping for the past two years. Heartbleed isn't your garden-variety vulnerability, so here's a quick guide to what it is, why it's so serious, and what you can do to keep your data saf e.
What's Heartbleed?
T he short version is that it's a vulnerability in the way your browser talks to a website over an encrypted channel. An attacker could theoretically take advantage of the bug to unravel the secure channels used by banks, e-commerce sites and other sensitive locations to steal passwords and other sensitive inf ormation. T he slightly longer version is that Heartbleed is a f law in the OpenSSL implementation of the basic cryptographic protocol that secures Web communications, known as SSL.
What's SSL?
It stands f or Secure Socket Layer, a cryptographic protocol that puts the S in "https"the pref ix you see on Web addresses when they're using a secure, encrypted connection. SSL basically ensures that no one can eavesdrop while you're banking, shopping or doing anything else rth reading your email at Gmail and similar services, or connecting to other sensitive sites.
What's OpenSSL?
OpenSSL is an open-source implementation of SSL and its successor protocol, T LS (which stands f or Transport Security Layer). It's the def ault cryptographic library in the Apache and nginx Web servers, which together powered almost exactly two-thirds of all active websites as of April, according to Netcraf t data (h/t Ars Technica). T hat means OpenSSL is used to protect sensitive Web communications across a vast swathe of the Internet.
Let's Go Back To Heartbleed. What Exactly Does It Do?
Of f icially known as CVE-2014-0160, Heartbleed is a recently discovered bug in OpenSSL that could allow an attack to read inf ormation of f a Web server even though it's supposed to be secured against intrusion. T he bug af f ects an OpenSSL extension known as heartbeat, which makes it possible to keep a secure communication channel open without re-negotiating security protocols over and over again. In ef f ect, the bug allows a malicious users to request data f rom a Web server's memorydata that could include the site's SSL encryption keys, user passwords and other sensitive inf ormation. According to Heartbleed, a website established by researchers at Codenomicon who identif ied the bug (as did a Google engineer):
The Heartbleed bug allows anyone on the Internet to read the memory of the systems protected by the vulnerable versions of the OpenSSL software. This compromises the secret keys used to identify the service providers and to encrypt the traffic, the names and passwords of the users and the actual content. This allows attackers to eavesdrop on communications, steal data
directly from the services and users and to impersonate services and users.
Why Is HeartBleed So Serious?
T here are several reasons. T he f irst, and most obvious, is that Web servers may leak sensitive data as a result of the vulnerability. T he Heartbleed bug lets an attack f orce a server to cough up the contents of its active memory (albeit in 64KB chunks). Depending on what the server happens to be doing, its memory may contain usernames, passwords or credit card numbers. Heartbleed also lets attackers obtain the servers secret keyscryptographic measures that are supposed to ensure only an owner can access sensitive datain order to impersonate servers and decrypt their communications. Whats more, the site explains, is that its disturbing dif f icult to tell if somebody exploits it. T hat means victims may have no way to tell if they've been, well, victimized. Finally, the Heartbleed bug has been in the wild f or roughly two years. T hat's a lot of potential exploitation, should any bad guys have stumbled across it in that time. Even worse, if anyone recorded encrypted traf f ic over that time and extracted a server's encryption keys, they can go back and decrypt past communications at their leisure. Sites that use perf ect f orward secrecy, like Gmail, should be protected f rom retrospective decryption. Unf ortunately, perf ect f orward secrecy isn't widely used across the Web. Can I Tell If My Site Has Been Exploited Via Heartbleed? No. However, you can test your site to see if it's vulnerable.
What Can I Do To Protect My Site?
If your site turns out to be vulnerable, OpenSSL recommends that you upgrade to OpenSSL version 1.0.1g, which patches the Heartbleed vulnerability. If you can't upgrade f or some reason, you can disable OpenSSL heartbeat support f or a quick f ix. Even if you patch the bug, however, its impossible to tell if an attack took place in the past.
What Can I Do To Protect Myself As An Internet User?
Now is a very good time to change all your passwords. Even if you dont think you were af f ected, it's possible that sites you regularly use like Yahoomight have been. Ronald Prins of security f irm Fox-IT tweeted that he used the Heartbleed vulnerability to f ind a Yahoo username and password, and provided proof on his blog. However, Yahoo has apparently patched its servers, as a Heartbleed vulnerability test f or Yahoo.com has shown up clean since 4 PM Eastern.
Has Anyone Exploited The Heartbleed Vulnerability Yet?
We dont know. Security researchers who study the bug have noted that when they exploit it, nothing unusual shows up on the logs. So if bad actors have used it f or attacks, we cant tell. Logo via Codenomicon
Potrebbero piacerti anche
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- Setting Up Raspbian (And DOOM!)Documento23 pagineSetting Up Raspbian (And DOOM!)BobapatatasNessuna valutazione finora
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- BITS Pilani BSC Computer Science BrochureDocumento20 pagineBITS Pilani BSC Computer Science BrochureSuraj MadhavNessuna valutazione finora
- Byte Magazine Vol 14-04Documento400 pagineByte Magazine Vol 14-04BobapatatasNessuna valutazione finora
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- Byte Magazine Vol 10-04Documento510 pagineByte Magazine Vol 10-04BobapatatasNessuna valutazione finora
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (895)
- How To Convert Windows 10 From Legacy BIOS To UEFDocumento3 pagineHow To Convert Windows 10 From Legacy BIOS To UEFBobapatatasNessuna valutazione finora
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (344)
- Byte Magazine Vol 14-04Documento400 pagineByte Magazine Vol 14-04BobapatatasNessuna valutazione finora
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (399)
- EU Elections - DINOsaurs Duck First MeteoriteDocumento3 pagineEU Elections - DINOsaurs Duck First MeteoriteBobapatatasNessuna valutazione finora
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (588)
- Italy To Add Drug Trafficking, Prostitution To GDP FiguresDocumento2 pagineItaly To Add Drug Trafficking, Prostitution To GDP FiguresBobapatatas100% (1)
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- Linux Vs Windows (Folder Explanation)Documento4 pagineLinux Vs Windows (Folder Explanation)BobapatatasNessuna valutazione finora
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (266)
- Gaza Freedom FlotillaDocumento7 pagineGaza Freedom FlotillaBobapatatasNessuna valutazione finora
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- Bitcoin Startup Runs Your Miner For LessDocumento4 pagineBitcoin Startup Runs Your Miner For LessBobapatatasNessuna valutazione finora
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- Colin McRae RallyDocumento6 pagineColin McRae RallyBobapatatasNessuna valutazione finora
- Basic Linux CommandsDocumento5 pagineBasic Linux CommandsBobapatatasNessuna valutazione finora
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (73)
- Apollo ProgramDocumento30 pagineApollo ProgramBobapatatasNessuna valutazione finora
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- WikiLeaks Threatens To Name NSA-targeted Country Despite Warnings It May Lead To DeathsDocumento3 pagineWikiLeaks Threatens To Name NSA-targeted Country Despite Warnings It May Lead To DeathsBobapatatasNessuna valutazione finora
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- Geoffrey Marcy - Finder of New Worlds (Astronomy)Documento11 pagineGeoffrey Marcy - Finder of New Worlds (Astronomy)BobapatatasNessuna valutazione finora
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2259)
- Turkey Coal Mine Explosion - Death Toll RisesDocumento3 pagineTurkey Coal Mine Explosion - Death Toll RisesBobapatatasNessuna valutazione finora
- Scientists Find Way To Turn Light Into MatterDocumento2 pagineScientists Find Way To Turn Light Into MatterBobapatatasNessuna valutazione finora
- Death Toll Rises To 44 in Worst Ever Balkan Flooding (PHOTOS)Documento8 pagineDeath Toll Rises To 44 in Worst Ever Balkan Flooding (PHOTOS)BobapatatasNessuna valutazione finora
- Bilderberg's Silent Takeover of Britain's $60bn Defense BudgetDocumento5 pagineBilderberg's Silent Takeover of Britain's $60bn Defense BudgetBobapatatasNessuna valutazione finora
- Baby We Were Born To RUN - Celebrating 50 Years of BasicDocumento2 pagineBaby We Were Born To RUN - Celebrating 50 Years of BasicBobapatatasNessuna valutazione finora
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- Energy Tower System TS5 2.1 Bluetooth: Ref: 395019 EAN: 8432426395019Documento4 pagineEnergy Tower System TS5 2.1 Bluetooth: Ref: 395019 EAN: 8432426395019BobapatatasNessuna valutazione finora
- Fpbibpmjndmd TS5 Manual enDocumento12 pagineFpbibpmjndmd TS5 Manual enBobapatatasNessuna valutazione finora
- Best CPU For Gamers - April 2014Documento110 pagineBest CPU For Gamers - April 2014BobapatatasNessuna valutazione finora
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- CIA Barred From Using Vaccinations As Cover After Dozens of Doctors KilledDocumento3 pagineCIA Barred From Using Vaccinations As Cover After Dozens of Doctors KilledBobapatatasNessuna valutazione finora
- Alpha CentauriDocumento39 pagineAlpha CentauriBobapatatasNessuna valutazione finora
- Brightest StarsDocumento64 pagineBrightest StarsBobapatatasNessuna valutazione finora
- Gallium Arsenide (GaAs) - EU Singlemarket StalinismDocumento2 pagineGallium Arsenide (GaAs) - EU Singlemarket StalinismBobapatatasNessuna valutazione finora
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (120)
- A Long Way From Chicago (Wiki)Documento3 pagineA Long Way From Chicago (Wiki)BobapatatasNessuna valutazione finora
- Forgotten Advanced CivilizationsDocumento9 pagineForgotten Advanced CivilizationsBobapatatas100% (1)
- Cisco Start Catalog ConnectDocumento109 pagineCisco Start Catalog ConnectRemNessuna valutazione finora
- TCP - IP Internetworking With 'Gawk'Documento61 pagineTCP - IP Internetworking With 'Gawk'serge_viardotNessuna valutazione finora
- Network and System Expert MCQ - QuestionsDocumento12 pagineNetwork and System Expert MCQ - QuestionsElysium AcademyNessuna valutazione finora
- Femto-Femto HO Chalk TalkDocumento37 pagineFemto-Femto HO Chalk TalkPrasoon PuthuvattilNessuna valutazione finora
- Neighbor 10.2.2.2 Route-Reflector-ClientDocumento18 pagineNeighbor 10.2.2.2 Route-Reflector-ClientOstilio SystemsNessuna valutazione finora
- Datasheet Forcepoint NGFW Appliances Specs enDocumento5 pagineDatasheet Forcepoint NGFW Appliances Specs enCharlesNessuna valutazione finora
- 9.1.3 Packet Tracer Identify Mac and Ip AddressesDocumento3 pagine9.1.3 Packet Tracer Identify Mac and Ip AddressesasshonNessuna valutazione finora
- 01-01 AAA ConfigurationDocumento174 pagine01-01 AAA ConfigurationImplantação RadiusNetNessuna valutazione finora
- KISTERS License Server Admin Guide 3Documento12 pagineKISTERS License Server Admin Guide 3Çağatay AbayNessuna valutazione finora
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)
- AP-Enbd Manual v0Documento6 pagineAP-Enbd Manual v0Kauê ViniciusNessuna valutazione finora
- 5.1 Secure Internal Communication SIC PDFDocumento12 pagine5.1 Secure Internal Communication SIC PDFTrupti SansareNessuna valutazione finora
- 3EC419190001 V1 System DescriptionDocumento185 pagine3EC419190001 V1 System Descriptiondragutu danNessuna valutazione finora
- Microsoft Official Course: Implementing AD CSDocumento57 pagineMicrosoft Official Course: Implementing AD CShieuNessuna valutazione finora
- Bajaj Capital Technology Solutions PVT LTDDocumento2 pagineBajaj Capital Technology Solutions PVT LTDChristopher NguyenNessuna valutazione finora
- h16346 Dell Emc Powerscale Ethernet Back End Network OverviewDocumento26 pagineh16346 Dell Emc Powerscale Ethernet Back End Network OverviewNan Win AungNessuna valutazione finora
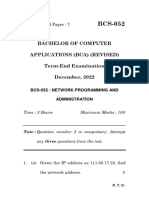
- DEC22Documento7 pagineDEC22Jai Kumar PandeyNessuna valutazione finora
- Building HP FlexFabric DCs-LabDocumento414 pagineBuilding HP FlexFabric DCs-LabRubenOrtegaNessuna valutazione finora
- OSI ModelDocumento10 pagineOSI ModelChandraSekharNessuna valutazione finora
- A Survey of Network-Based Intrusion Detection Data SetsDocumento17 pagineA Survey of Network-Based Intrusion Detection Data SetsKeerthana SudarshanNessuna valutazione finora
- Overview of TETRA FunctionalityDocumento15 pagineOverview of TETRA FunctionalityhrfmoxNessuna valutazione finora
- FiddlerDocumento54 pagineFiddlerSarvesh SinghNessuna valutazione finora
- 5G Core 21.1 SA Working Principles and Data Configuration ISSUE 1.0Documento76 pagine5G Core 21.1 SA Working Principles and Data Configuration ISSUE 1.0Mohamed EldessoukyNessuna valutazione finora
- Apuntes CCNA SecurityDocumento7 pagineApuntes CCNA SecuritySantiago Balaguer GarcíaNessuna valutazione finora
- Data Sheet - Item Number: 750-8212/025-002 Controller PFC200 2nd Generation 2 X ETHERNET, RS-232/-485 Telecontrol Technology Ext. Temperature ECODocumento4 pagineData Sheet - Item Number: 750-8212/025-002 Controller PFC200 2nd Generation 2 X ETHERNET, RS-232/-485 Telecontrol Technology Ext. Temperature ECOarun_daraNessuna valutazione finora
- Airlap 1142 Nak 9Documento36 pagineAirlap 1142 Nak 9Victor PizarroNessuna valutazione finora
- Toc PDFDocumento11 pagineToc PDFSpipparisNessuna valutazione finora
- BGP Weight AttributeDocumento8 pagineBGP Weight AttributexploreNessuna valutazione finora
- Cheat Sheet - Cisco Network Live Issues - 16 Feb, 2015Documento30 pagineCheat Sheet - Cisco Network Live Issues - 16 Feb, 2015Bilal KhanNessuna valutazione finora
- Nginx and Let's Encrypt With Docker in Less Than 5 Minutes - by Philipp - MediumDocumento13 pagineNginx and Let's Encrypt With Docker in Less Than 5 Minutes - by Philipp - MediumProf SilvaNessuna valutazione finora
- HW 1 of Chapter 1Documento1 paginaHW 1 of Chapter 1No oneNessuna valutazione finora
- The Dark Net: Inside the Digital UnderworldDa EverandThe Dark Net: Inside the Digital UnderworldValutazione: 3.5 su 5 stelle3.5/5 (104)
- Defensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityDa EverandDefensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityValutazione: 5 su 5 stelle5/5 (1)
- The Digital Marketing Handbook: A Step-By-Step Guide to Creating Websites That SellDa EverandThe Digital Marketing Handbook: A Step-By-Step Guide to Creating Websites That SellValutazione: 5 su 5 stelle5/5 (6)
- The Internet Con: How to Seize the Means of ComputationDa EverandThe Internet Con: How to Seize the Means of ComputationValutazione: 5 su 5 stelle5/5 (6)
- Python for Beginners: The 1 Day Crash Course For Python Programming In The Real WorldDa EverandPython for Beginners: The 1 Day Crash Course For Python Programming In The Real WorldNessuna valutazione finora