Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
Health Body Wellness Center: Information Security Management System (ISMS)
Caricato da
gtlnxTitolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
Health Body Wellness Center: Information Security Management System (ISMS)
Caricato da
gtlnxCopyright:
Formati disponibili
Health Body Wellness Center
Information Security Management System (ISMS)
Health Body Wellness Center (HBWC) promotes medical research, evaluation, and sharing of information between health care professionals. The HBWCs Office of Grants Giveaway (OGG) provides for the distribution of federally supported medical grants. OGG uses a Microsoft Access database program called Small Hospital Tracking System (SHGTS) to manage the medical grant distribution process. A risk assessment of SHGTS was conducted to evaluate vulnerabilities and establish a baseline of potential threats. This document will outline an ISMS plan for HBWC and provide recommendation of additional steps needed to implement and maintain this plan. Use of the ISO 27000 series certification process will provide a framework for the ISMS. The Plan-Do-Check-Act (PDCA) model provides a stepby-step process for planning, implementing, and management of the ISMS plan. The ISMS outline, network drawing, and additional recommended steps will be discussed below. A1. Business Objectives The first step of any ISMS is the identification of the business objects that need to be included in the planning and maintenance of an organization. Listed below are HBWCs major objects to be considered when developing ISMS. (Arnason, S, & Willett, K.D, 2008) Staff: Basic users, RAS users, Administrators, Executives, and Database Administrators roles, access levels, and responsibility should be defined. Facilities: HBWC headquarters in room 1234 & OGG offices in room 5678 (Location of servers and network devices) physical security must be examined. Technology: Microsoft Windows 95/NT Server environment, Access 97 database, and network devices and configuration of said equipment (Patches & Updates). Discussion of vulnerabilities associated with unsupported Operating Systems (OS) and Applications (Access) should be covered. Key players: Management, Human Resources (HR), Information Technology (IT) staff all should provide players to make up the ISMS committee. The key to success is having management drive the process and establish the framework for the company to follow. Motivations: HBWCs goal is to provide an effective method to promote medical research and the exchange of information of heath care professionals. Institutions rely on grants from OGG to meet this goal. The establishment of a secure environment for SHGTS to operate is paramount to success. Snapshot of security posture: No current ISMS policy is in place at this time. With the aid of the SHGTS risk assessment a review of the overall security posture and development of a comprehensive ISMS plan for HBWC and its customers. Objectives: Evaluate all systems and data on the HBWCs Local Area Network (LAN) to implement an affective ISMS to meet the ISO 27000 series standard. The Confidentiality, Integrity, and Availability (CIA) triad are key considerations of all systems/data that should be evaluated and covered during the PDCA process. A2. Guiding Security Principles Three key principles of security are the CIA triad; they provide a basis for identifying and applying industrial security standards for the protection and prevention of IT systems. Confidentiality policies are designed to prevent unauthorized access to data, databases, including paper data, electronic media, telephone, and data networks (bits and bits). Integrity policies to prevent the modification of data in transit, transaction integrity, and data at rest. The use of encryption technologies insures data integrity. Availability policies include equipment maintenance, monitoring degraded services, and response to loss of asset. These security principles are the basis of a good ISMS program and provide a guideline for its development. (Tipton, H, & Henry, K. 2007)
File:FYT2_Task2 By Thomas A. Groshong Sr Page 1 of 5
Health Body Wellness Center
Information Security Management System (ISMS)
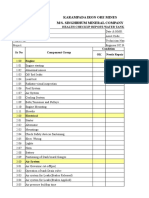
A3. Processes The processes that will be included in the ISMS are the PDCA process, and a transition plan to move HBWC from the current As-is-state to the To-be-state. The PDCA process provides guidance on four steps; develop a plan, implement the plan, verify the plan is in use, and improvement of the plan. Management must first establish guidance for the ISMS team to build a security plan that is current by todays standards. Next a full risk and vulnerability assessment has to be completed that identifies the current threats so an action plan can be developed that addresses them. The plan will provide guidance on the migration of the companys network and how to migrate from the As-is-state to the To-be-state. The ISMS plan will be consistent with ISO 27000 series certification processes. A timeline for implementation, verification/validation, and improvement will be defined as part on the ISMS process. (Arnason, S, & Willett, K.D, 2008) A4. Information Systems (IS) Systems included in the scope of the ISMS are all network devices to include workstations, servers, routers, firewalls, switches and modems. Shown below is the As-is Network Drawing that shows the current state of the HBWC network before implementation of the ISMS policies and procedures. The ISMS team will identify upgrades to the systems that will include OS upgraded, patches/bug fixes, and implementation of system processes such as Active Directory (AD), Demilitarized Zone (DMZ) creation, Migration of the Remote Access Server (RAS) to Virtual Private Network (VPN) Technology, and migration of SHGS (Access) to a SQL (web based) database. Access Control Lists (ACLs) will be clearly evaluated and revised to meet current authentication and authorization requirements to meet industrial standards for security. A review of the Malware (Anti-Virus) detection system must be reviewed to validate up-to-date protection of all systems that touch the HWC network to include Remote User devices. A5. IT Infrastructure The ISMS plan will evaluate the information flow and provide steps that change the current flow of information to improve the security of the network and the data that is exchanged. Remote users currently access the SHGS database using a RAS configuration as shown in the LAN drawing below. The Headquarters (HQ) and OGG offices use Windows XP workstations for normal user computer processing. Windows NT servers that provide discretionary access control (HBWC-DC-01), SHGS database access (HBWC-DB-01), and RAS (HBWD-RA-01) connectivity. Network devices such as modems, switches, firewall, proxy, and router provide secure connectivity to internal (Files Shares) and external (Internet Cloud) networks. The elimination of the RAS connectivity and providing a VPN connection will vastly improve security and provide Remote Users with a far more robust connection. In addition the migration of the SHGS database from Access 97 to SQL and establishing a Web presence will reduce the need for Remote Users need for remote access the HBWC network other than teleworkers. Part of the overall migration of SHGS would be the creation of a DMZ on the firewall to isolate the Web traffic and access of webSHGS. The ISMS team will evaluate the firewalls capabilities to determine if upgrade or replacement will be required before implementation. The Internetwork Operating System ( IOS) and/or Current Version of network devices will be upgraded to versions that reduce known threats and improve security. The addition of upgrades to workstations to Microsoft Windows 7 Professional, Microsoft Office 2010 Professional, and Microsoft Windows Server 2008 would greatly enhance security and reduce risk. With the migration to Server 2008 the addition of AD to the current infrastructure will allow better management of the users and computers on the HBWC LAN.
File:FYT2_Task2 By Thomas A. Groshong Sr Page 2 of 5
Health Body Wellness Center
Information Security Management System (ISMS)
Internet Cloud via ISP WAN
Healthy Body Wellness Center (HBWC) As-Is Network Drawing
DSL/Cable Modem Router DSL/ISP Cable/Phone Media Copper CAT5e (Ethernet) Telephone Dial Up POTS lines
Modem wks1 wks2 wks3 wks4 wks5 wks6
Proxy Server Firewall
Workstations OGG Offices 5678 Windows XP
Network Switch
wks1 wks2 wks3 wks4
HBWC-DB-01 SHGTS JINX Server Windows NT Server
HBWC-DC-01 Account Server Windows NT Server
wks5 wks6 RAS Modem
Workstations HBWC Headquarters 1234 Windows XP
HBWC-RA-01 RAS Server Windows NT Server Remote Access Modem Bank
Remote Access Dial Up Connections
wks1 wks2 wks3 wks4 wks5
Telephone company provided lines used to access RAS server
* Notes: Equipment Rack Locations Network Devices Room 1234 Servers Room 1234
wks6
Remote Workstations Managed by HBWC
22Jul2012 Healthy Body Wellness Center FYT2Task2
File:FYT2_Task2 By Thomas A. Groshong Sr Page 3 of 5
Health Body Wellness Center
Information Security Management System (ISMS)
Recommended Additional Steps B1. Discussion HBWC has a LAN that is up and running (As-is-state) and the ISMS team will create a plan to migrate and/or update (To-be-state) it to improve security. PDCA provided a step-by-step process that identifies threats and vulnerabilities and provides a framework to implement, audit, and improve. The logical steps of the PDCA process are; Plan Prepare an ISMS plan with forecasts and management approval the will provide establish security norms and follow industrial standards (ISO 27001). Do Implement the ISMS plan and follow the ISMS team recommendations as set forth in the plan. Check Review and verify the policies exist and are being used per the plan. Establishing a process to audit the ISMS must be created. A review of the effectiveness of the program and any residual risk should be identified. Monitoring and review during the check stage determines the effectiveness of the ISMS plan. Recommendations for improvement are made from audits and assessments made during this stage. Act Improvement of the ISMS policies is a direct result of the check stage of PDCA. Once the review has been completed, the implementation of improvement reduces overall risk and provides a more secure environment for HBWC. The PDCA is not a one-time process and you are done. It is designed in a way that continual review (Check) and improvement (Act) is done. This requires assessments either in-house or external to audit, make recommendations, and provide a process feedback on the ISMS. (Arnason, S, & Willett, K.D,
2008)
B2. Justification The PDCA process provides four stages for the planning, implementation, review, and improvement of the ISMS policies and procedures. By adopting a plan that continually audits, reviews, and improves the LAN security posture a more effective and comprehensive ISMS is created. Industrial standards such as ISO 27001, NIST, COBIT, and ITIL all suggest a plan of continual evaluation and improvement. In the case of HBWC it is clear that the As-is-state did not have any improvement process. The lack of a security plan or improvement process has made HBWCs current systems vulnerable to a great number of threats. The establishment of a comprehensive ISMS policy and the adoption of the PDCA process will greatly reduce the risk of threats and vulnerabilities of HBWC, and it users. Due diligence requirements establish very clear legal ramification for lack of proper handling and due care of information. Organizations must be concerned with relevant compliance to requirements like Sarbanes-Oxley (SOX), Health Insurance Portability and Accountability Act (HIPAA), and Personally Identifiable Information (PII). Establishing a process of continued review and improvement will allow HBWC can adapt to changes in risk (threats) and adapt to ever changing legal responsibilities. (Arnason, S, & Willett, K.D, 2008)
File:FYT2_Task2 By Thomas A. Groshong Sr Page 4 of 5
Health Body Wellness Center
Information Security Management System (ISMS)
Reference Page
Arnason, S, & Willett, K.D. (2008). How to achieve 27001 certification an example of applied compliance. New Auerbach Publications. Tipton, H, & Henry, K. (2007). Official (ISC)2 guide to the CISSP CBK. Boca Raton, FL: Auerbach Publications. Tipton, H, & Krause, M. (2007). Information security management handbook, Sixth Edition. Boca Raton, FL: Auerbach Publications.
File:FYT2_Task2 By Thomas A. Groshong Sr Page 5 of 5
Potrebbero piacerti anche
- PART A AnswerDocumento10 paginePART A AnswerSaad Fahim75% (4)
- Vocations The New Midheaven Extension ProcessDocumento266 pagineVocations The New Midheaven Extension ProcessMiss M.100% (24)
- AdminGuide 3.1Documento305 pagineAdminGuide 3.1fbolivarbuitragoNessuna valutazione finora
- 1634566604muschetto Dragos Platform Threat and Visibility Pdf1634566604Documento11 pagine1634566604muschetto Dragos Platform Threat and Visibility Pdf1634566604Ronald N Meza CNessuna valutazione finora
- CIS RAM v2.1 Core Document Online.22.01Documento27 pagineCIS RAM v2.1 Core Document Online.22.01Raman GautaNessuna valutazione finora
- Asan Visa Ae102901499Documento2 pagineAsan Visa Ae102901499hardeep ranaNessuna valutazione finora
- CCNP Security Certification and Training ProgramDocumento2 pagineCCNP Security Certification and Training ProgramTshepo MoreNessuna valutazione finora
- Cybersecurity Overview: Network SecurityDocumento18 pagineCybersecurity Overview: Network SecuritysubishsNessuna valutazione finora
- AAE ControlRoom UserManualDocumento69 pagineAAE ControlRoom UserManualSai Kumarp85% (13)
- Information Rights Management (IRM)Documento12 pagineInformation Rights Management (IRM)niiconsultingNessuna valutazione finora
- Security Operations Center Job Description TemplatesDocumento20 pagineSecurity Operations Center Job Description Templatesep230842Nessuna valutazione finora
- Everything You Wanted To Know About HIPAA Security You Learned As A Child!Documento29 pagineEverything You Wanted To Know About HIPAA Security You Learned As A Child!tstamm100% (1)
- NTT Security On OT SecurityDocumento4 pagineNTT Security On OT SecurityDK56128Nessuna valutazione finora
- Toolkit Reference For The Microsoft Deployment Toolkit PDFDocumento1.191 pagineToolkit Reference For The Microsoft Deployment Toolkit PDFAaron SemoNessuna valutazione finora
- Security Culture A Complete Guide - 2021 EditionDa EverandSecurity Culture A Complete Guide - 2021 EditionNessuna valutazione finora
- Using ANSI ISA 99 Standards WP May 2012 PDFDocumento11 pagineUsing ANSI ISA 99 Standards WP May 2012 PDFodie99Nessuna valutazione finora
- IoT Auditing ISACA Version 1Documento61 pagineIoT Auditing ISACA Version 1Sridharan Govindaraj100% (1)
- Penetration Testing Framework 0.59 PDFDocumento40 paginePenetration Testing Framework 0.59 PDFSamir MirzəoğluNessuna valutazione finora
- Privileged Access Management Tools Standard RequirementsDa EverandPrivileged Access Management Tools Standard RequirementsNessuna valutazione finora
- 2018 Kaspersky ICS WhitepaperDocumento33 pagine2018 Kaspersky ICS Whitepapercena018Nessuna valutazione finora
- NIST Privacy Framework - Highlights From Version 1Documento17 pagineNIST Privacy Framework - Highlights From Version 1joycechualeekengNessuna valutazione finora
- Pro-Watch 4.5 Installation GuideDocumento46 paginePro-Watch 4.5 Installation GuideTiago DutraNessuna valutazione finora
- ISO450012018AuditChecklistEng 13Documento1 paginaISO450012018AuditChecklistEng 13Anabela GibraltarNessuna valutazione finora
- 5 Ways To Maintain Patient ConfidentialityDocumento2 pagine5 Ways To Maintain Patient ConfidentialityPrincess BalloNessuna valutazione finora
- Sox Octave FinalDocumento11 pagineSox Octave FinalErick MorenoNessuna valutazione finora
- AWS HIPAA Compliance Whitepaper PDFDocumento49 pagineAWS HIPAA Compliance Whitepaper PDFSiva KrishnaNessuna valutazione finora
- Csi Cloud Security BasicsDocumento4 pagineCsi Cloud Security BasicsSrilakshmi PonamgiNessuna valutazione finora
- 1.3-Basic Packet Analysis WiresharkDocumento43 pagine1.3-Basic Packet Analysis Wiresharknbadung100% (1)
- CIP Motion - CIP SyncDocumento33 pagineCIP Motion - CIP SyncPipe CastilloNessuna valutazione finora
- Class 1: Security and Risk ManagementDocumento24 pagineClass 1: Security and Risk ManagementCapitan SwankNessuna valutazione finora
- RemoteAccess Service UserGuideDocumento17 pagineRemoteAccess Service UserGuidetestNessuna valutazione finora
- VMware Infrastructure Architecture OverviewDocumento14 pagineVMware Infrastructure Architecture Overviewnytmare_sisterNessuna valutazione finora
- Hipaa: Health Insurance Portability and Accountability ActDocumento24 pagineHipaa: Health Insurance Portability and Accountability Actshanoo shahNessuna valutazione finora
- IDC Worldwide Cloud Security Gateways 2021Documento8 pagineIDC Worldwide Cloud Security Gateways 2021Avishai ZivNessuna valutazione finora
- MEcat2008 09 Pro WatchDocumento47 pagineMEcat2008 09 Pro WatchJosé Daniel Hernández SánchezNessuna valutazione finora
- PROTECT - Implementing Network Segmentation and Segregation (October 2021)Documento6 paginePROTECT - Implementing Network Segmentation and Segregation (October 2021)gemchis dawoNessuna valutazione finora
- Desktop Virtualization Market - The Future of Corporate Infrastructure - Market Penetration and Stakeholder Analysis (2014 - 2020)Documento8 pagineDesktop Virtualization Market - The Future of Corporate Infrastructure - Market Penetration and Stakeholder Analysis (2014 - 2020)Mordor IntelligenceNessuna valutazione finora
- ReaQta-Hive v3.9 Administration Guide v1Documento90 pagineReaQta-Hive v3.9 Administration Guide v1Hồng Quang Phan100% (1)
- CEH NotesDocumento7 pagineCEH NotesKelvin Danso EffahNessuna valutazione finora
- Skybox ReferenceGuide V10!0!300Documento460 pagineSkybox ReferenceGuide V10!0!300pisanij123Nessuna valutazione finora
- Lutze Switch PowerDocumento268 pagineLutze Switch PowerkanbouchNessuna valutazione finora
- Need For Women in CybersecurityDocumento2 pagineNeed For Women in CybersecurityJordan SalazarNessuna valutazione finora
- Incident Response Plan TemplateDocumento34 pagineIncident Response Plan TemplatelaertepalvesNessuna valutazione finora
- CISSP y CBK PDFDocumento4 pagineCISSP y CBK PDFjpereztmpNessuna valutazione finora
- DCN Manual 2019Documento74 pagineDCN Manual 2019Suhani SrivastavaNessuna valutazione finora
- Iso Ts 16949 Semiconductor CommodityDocumento24 pagineIso Ts 16949 Semiconductor Commoditydyogasara2Nessuna valutazione finora
- Class X-BookDocumento16 pagineClass X-BookPratyakshNessuna valutazione finora
- Technical Information: OPC Interface PackageDocumento52 pagineTechnical Information: OPC Interface PackageFabian GuzmanNessuna valutazione finora
- DLP and Data Classification A Clear and Concise ReferenceDa EverandDLP and Data Classification A Clear and Concise ReferenceNessuna valutazione finora
- Cortex XDR For Network Traffic Analysis PDFDocumento2 pagineCortex XDR For Network Traffic Analysis PDFfabioccnpNessuna valutazione finora
- Power BI PRIVACY IMPACT ASSESSMENT V1.0 RedactedDocumento28 paginePower BI PRIVACY IMPACT ASSESSMENT V1.0 RedactedAhmedNessuna valutazione finora
- Security Monitoring A Complete Guide - 2021 EditionDa EverandSecurity Monitoring A Complete Guide - 2021 EditionNessuna valutazione finora
- Fiscam 1 PDFDocumento478 pagineFiscam 1 PDFhanantoNessuna valutazione finora
- CECIIS 2010 - Digital Evidence Chain of Custody - FrameworkDocumento4 pagineCECIIS 2010 - Digital Evidence Chain of Custody - FrameworkjasmincosicNessuna valutazione finora
- Security 701 Exam Objectives Comparison Flyer OnlineDocumento4 pagineSecurity 701 Exam Objectives Comparison Flyer OnlineWayne WayneNessuna valutazione finora
- Ics Nisttt PDFDocumento155 pagineIcs Nisttt PDFRuchirNessuna valutazione finora
- Nist - Ir.8374 DraftDocumento26 pagineNist - Ir.8374 DraftSpit FireNessuna valutazione finora
- Metalcor - 1.4507 - Alloy - F255 - Uranus 52N - S32520Documento1 paginaMetalcor - 1.4507 - Alloy - F255 - Uranus 52N - S32520NitinNessuna valutazione finora
- Cad Data Exchange StandardsDocumento16 pagineCad Data Exchange StandardskannanvikneshNessuna valutazione finora
- Fmicb 10 02876Documento11 pagineFmicb 10 02876Angeles SuarezNessuna valutazione finora
- Timetable - Alton - London Timetable May 2019 PDFDocumento35 pagineTimetable - Alton - London Timetable May 2019 PDFNicholas TuanNessuna valutazione finora
- Paramount Healthcare Management Private Limited: First Reminder Letter Without PrejudiceDocumento1 paginaParamount Healthcare Management Private Limited: First Reminder Letter Without PrejudiceSwapnil TiwariNessuna valutazione finora
- Water Tanker Check ListDocumento8 pagineWater Tanker Check ListHariyanto oknesNessuna valutazione finora
- 10 Essential Books For Active TradersDocumento6 pagine10 Essential Books For Active TradersChrisTheodorou100% (2)
- Report On Marketing Strategy of Nestle MILKPAKDocumento13 pagineReport On Marketing Strategy of Nestle MILKPAKAzeem Ahmad100% (1)
- Electric Vehicles PresentationDocumento10 pagineElectric Vehicles PresentationVIBHU CHANDRANSH BHANOT100% (1)
- PDS (OTO360) Form PDFDocumento2 paginePDS (OTO360) Form PDFcikgutiNessuna valutazione finora
- Hydrogeological Survey and Eia Tor - Karuri BoreholeDocumento3 pagineHydrogeological Survey and Eia Tor - Karuri BoreholeMutonga Kitheko100% (1)
- Mode of Action of Vancomycin: L D D D D DDocumento8 pagineMode of Action of Vancomycin: L D D D D DNolanNessuna valutazione finora
- Docsity Detailed Lesson Plan 5Documento4 pagineDocsity Detailed Lesson Plan 5Sydie MoredoNessuna valutazione finora
- N50-200H-CC Operation and Maintenance Manual 961220 Bytes 01Documento94 pagineN50-200H-CC Operation and Maintenance Manual 961220 Bytes 01ANDRESNessuna valutazione finora
- Standard nfx15-211Documento2 pagineStandard nfx15-211Luis Enrique Cóndor PorrasNessuna valutazione finora
- Geometry and IntuitionDocumento9 pagineGeometry and IntuitionHollyNessuna valutazione finora
- Advent Wreath Lesson PlanDocumento2 pagineAdvent Wreath Lesson Planapi-359764398100% (1)
- Hetal Patel: Team Leader - SalesDocumento2 pagineHetal Patel: Team Leader - SalesPrashant kumarNessuna valutazione finora
- Bajaj CNSDocumento3 pagineBajaj CNSAbhijit PaikarayNessuna valutazione finora
- Particle BoardDocumento1 paginaParticle BoardNamrata RamahNessuna valutazione finora
- Toi Su20 Sat Epep ProposalDocumento7 pagineToi Su20 Sat Epep ProposalTalha SiddiquiNessuna valutazione finora
- Process Strategy: Powerpoint Slides by Jeff HeylDocumento13 pagineProcess Strategy: Powerpoint Slides by Jeff HeylMuizzNessuna valutazione finora
- JP Selecta IncubatorDocumento5 pagineJP Selecta IncubatorAhmed AlkabodyNessuna valutazione finora
- Baxter - Heraeus Megafuge 1,2 - User ManualDocumento13 pagineBaxter - Heraeus Megafuge 1,2 - User ManualMarcos ZanelliNessuna valutazione finora
- The Minimum Means of Reprisal - China's S - Jeffrey G. LewisDocumento283 pagineThe Minimum Means of Reprisal - China's S - Jeffrey G. LewisrondfauxNessuna valutazione finora
- UntitledDocumento13 pagineUntitledTestNessuna valutazione finora
- Freshers Jobs 26 Aug 2022Documento15 pagineFreshers Jobs 26 Aug 2022Manoj DhageNessuna valutazione finora