Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
SSH - Best Practices - HowtoForge - Linux Howtos and Tutorials
Caricato da
al80al80Descrizione originale:
Titolo originale
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
SSH - Best Practices - HowtoForge - Linux Howtos and Tutorials
Caricato da
al80al80Copyright:
Formati disponibili
Thanks for this, very 2 days 6 hours ago 7 Making PHP-FPM Use A TCP Connection 2 days 6 hours ago
running icecast with icegenerator 2 days 9 hours ago My IP 2 days 14 hours ago
Newsletter
Subscribe to HowtoForge Newsletter and stay informed about our latest HOWTOs and projects. enter email address
(To unsubscribe from our newsletter, visit this link.)
English |
You are here:
Home Howtos Security SSH: Best Practices
Deutsch | Site Map/RSS Feeds | Advertise
SSH: Best Practices
Want to support HowtoForge? Become a !
Submitted by secureguardian (Contact Author) (Forums) on Wed, 2008-01-16 16:51. :: Security
SSH: Best Practices
Introduction
Are you using SSH in the best way possible? Have you configured it to be as limited and secure as possible? The goal of this document is to kick in the new year with some best practices for SSH: why you should use them, how to set them up, and how to verify that they are in place. All of the examples below assume that you are using EnGarde Secure Linux but any modern Linux distribution will do just fine since, as far as I know, everybody ships OpenSSH.
SSHv2 vs. SSHv1
There are numerous benefits to using the latest version of the SSH protocol, version 2, over it's older counterpart, version 1 and I'm not going into a lot of details on those benefits here - if you're interested, see the URL in the reference below or Google around. That being said if you don't have an explicit reason to use the older version 1, you should always be using version 2. To use SSHv2 by default but permit SSHv1, locate the "Protocol" line in your sshd_config file and change it to:
Protocol 2,1
When doing 2,1 please note that the protocol selection is left up to the client. Most clients will default to v2 and "fall back" to v1, while legacy clients may continue to use v1. To force everybody to use SSHv2, change it to:
Protocol 2
When you make this change don't forget to generate the appropriate HostKey's as well! SSHv2 requires the following keys:
# HostKeys for protocol version 2 HostKey /etc/ssh/ssh_host_rsa_key HostKey /etc/ssh/ssh_host_dsa_key
While SSHv1 requires:
# HostKey for protocol version 1 HostKey /etc/ssh/ssh_host_key
Once your changes are made, restart the SSH daemon: # /etc/init.d/sshd restart [ SUCCESSFUL ] Secure Shell Daemon [ SUCCESSFUL ] Secure Shell Daemon From another machine, try SSH'ing in. You can use the -v option to see which protocol is being used, and the '-oProtocol=' option to force one or the other - for example, "ssh -v -oProtocol=2 " would force protocol version 2.
Binding to a Specific Address or Non-Standard Port
If you're running SSH on an internal, firewalled, workstation then you can probably skip this section, but if you're running SSH on a firewall or on a machine with two network interfaces, this section is for you. Out of the box OpenSSH will bind to every available network address; while convenient and suitable for most installations, this is far from optimal. If your machine has two or more interfaces then the odds are that one is "trusted" and the other is "untrusted." If this is the case, and you don't need nor want SSH access coming in on the untrusted interface, then you should configure OpenSSH to listen on a specific interface. To have OpenSSH only bind to your internal interface, 192.168.0.1 in the example below, locate the following line in your sshd_config file:
ListenAddress 0.0.0.0
and change the 0.0.0.0 to 192.168.0.1:
ListenAddress 192.168.0.1
To verify that this change took, restart OpenSSH and look at netstat: # /etc/init.d/sshd restart [ SUCCESSFUL ] Secure Shell Daemon [ SUCCESSFUL ] Secure Shell Daemon # netstat -anp | grep sshd tcp 0 0 192.168.0.1:22 0.0.0.0:* LISTEN 7868/sshd As you can see, the sshd daemon is now only listening on 192.168.0.1. SSH requests coming in any other interface will be ignored. Similarly, you may want to change the port that the SSH daemon binds to. Sometimes there is a functional need for this (ie, your employer blocks outbound 22/tcp) but there is also security-throughobscurity value in this as well. While not providing any real security benefit against a determined attacker, moving the SSH daemon off of port 22 protects you against automated attacks which assume that the daemon is running on port 22. To have OpenSSH bind to a port other than port 22, 31337 in the example below, locate the following line in your sshd_config file:
Port 22
and change the 22 to 31337:
Port 31337
To verify that this change took, restart OpenSSH and, again, look at netstat: # netstat -anp | grep sshd tcp 0 0 192.168.0.1:31337 0.0.0.0:* LISTEN 330/sshd Finally, to SSH into a host whose SSH daemon is listening on a non-standard port, use the -p option: ssh -p 31337 user@192.168.0.1
Using TCP Wrappers
TCP Wrappers are used to limit access to TCP services on your machine. If you haven't heard of TCP Wrappers you've probably heard of /etc/hosts.allow and /etc/hosts.deny: these are the two configuration files for TCP Wrappers. In the context of SSH, TCP Wrappers allow you to decide what specific addresses or networks have access to the SSH service. To use TCP Wrappers with SSH you need to make sure that OpenSSH was built with the -withtcp-wrappers. This is the case on any modern distribution. As I indicated earlier, TCP Wrappers are configured by editing the /etc/hosts.deny and /etc/hosts.allow files. Typically you tell hosts.deny to deny everything, then add entries to hosts.allow to permit specific hosts access to specific services. An example:
# # hosts.deny This file describes the names of # *not* allowed to use the local I # by the '/usr/sbin/tcpd' server. # ALL: ALL # # hosts.allow This file describes the names of # allowed to use the local INET se # by the '/usr/sbin/tcpd' server. # sshd: 207.46.236. 198.133.219.25
In the example above, access to SSH is limited to the network 207.46.236.0/24 and the address 198.133.219.25. Requests to any other service from any other address are denied by the "ALL: ALL" in hosts.deny. If you try to SSH into a machine and TCP Wrappers denies your access, you'll see something like this: ssh_exchange_identification: Connection closed by remote host This simple configuration change significantly hardens your installation since, with it in place, packets from hostile clients are dropped very early in the TCP session -- and before they can do any real damage to a potentially vulnerable daemon.
Public Key Authentication
The last item I will cover is public key authentication. One of the best things you can do to tighten the
security of your SSH installation is to disable password authentication and to use public key authentication instead. Password authentication is suboptimal for many reasons, but mostly because people choose bad passwords and attackers routinely try to brute-force passwords. If the systems administrator has chosen a bad password and he's permitting root logins... game over. Public key authentication is no silver bullet - similarly, people generate passphrase-less keys or leave ssh-agents running when they shouldn't - but, in my opinion, it's a much better bet. Just about every distribution ships with public key authentication enabled, but begin by making sure it is:
RSAAuthentication yes PubkeyAuthentication yes
Both of these options default to "yes" and the "RSAAuthentication" option is for SSHv1 and the "PubkeyAuthentication" option is for SSHv2. If you plan on using this authentication method exclusively, while you're there, you may want to disable password authentication:
PasswordAuthentication no
Before you proceed, make sure you have a terminal open on your target machine. Once you restart the SSH daemon you will no longer be able to log in without a key... which we haven't generated yet! Once you're sure, restart the SSH daemon: # /etc/init.d/sshd restart [ SUCCESSFUL ] Secure Shell Daemon [ SUCCESSFUL ] Secure Shell Daemon Now, from your desktop, try to SSH in to your target machine: $ ssh rwm@brainy Permission denied (publickey,keyboard-interactive).
We're locked out! This is a good thing. The next step, on your desktop, is to generate a key: $ ssh-keygen -t dsa -C "Ryan's SSHv2 DSA Key (Jan 2008)" Generating public/private dsa key pair. Enter file in which to save the key (/home/rwm/.ssh/id_dsa): Enter passphrase (empty for no passphrase): ********** Enter same passphrase again: ********** Your identification has been saved in /home/rwm/.ssh/id_dsa. Your public key has been saved in /home/rwm/.ssh/id_dsa.pub. The key fingerprint is: 98:4d:50:ba:ee:8b:79:be:b3:36:75:8a:c2:4a:44:4b Ryan's SSHv2 DSA Key (Jan 2008)
A few notes on this: You can generate a DSA (-t dsa), RSA (-t rsa), or SSHv1 (-t rsa1) key. In the example above I'm using dsa. I like to put the date I generated the key in the comment (-C) field, that way I can change it out every so often. You're entering a passphrase, not a password. Use a long string with spaces and punctuation. The longer and more complicated the better! The command you just ran generated two files - id_dsa, your private key and id_dsa.pub, your public key. It is critical that you keep your private key private, but you can distribute your public key to any machines you would like to access. Now that you have generated your keys we need to get the public key into the ~/.ssh/authorized_keys file on the target machine. The best way to do this is to copy-and-paste it - begin by concatenating the public key file: $ cat .ssh/id_dsa.pub ssh-dss AAAAB3NzaC1kc3MAAACBAL7p6bsg5kK4ES9BWLPCNABl20iQQB3R0ymaPMHK... ... ds= Ryan's SSHv2 DSA Key (Jan 2008) This is a very long string. Make sure you copy all of it and that you do NOT copy the newline character at the end. In other words, copy from the "ssh" to the "2008)", but not past that. The next step is to append this key to the end of the ~/.ssh/authorized_keys file on your target machine. Remember that terminal I told you to keep open a few steps ago? Type the following command into it, pasting the key you've just copied into the area noted KEY: echo "KEY" >> ~/.ssh/authorized_keys For example: echo "ssh-dss AAAA5kS9BWLPCN...s= Ryan's SSHv2 DSA Key (Jan 2008)" >> ~/.ssh /authorized_keys Now, try to SSH in again. If you did this procedure correctly then instead of being denied access, you'll be prompted for your passphrase: $ ssh rwm@brainy Enter passphrase for key '/home/rwm/.ssh/id_dsa': Last login: Thu Jan 10 14:37:14 2008 from papa.engardelinux.org [rwm@brainy ~]$
Viola! You're now logged in using public key authentication instead of password authentication.
In Summary...
SSH is a wonderful tool and is every systems administrators second best friend (Perl, of course, being the first :). It allows you to read your email from anywhere, provided you still use a terminal-based mail reader. It allows you to tunnel an xterm or X11 application from your home server to your desktop at work. It provides you a far superior alternative to FTP in SFTP and SCP. SSH is great but just like any tool, it's only as good as you use it. I hope that you found value in some of my best practices and if you have any of your own, leave them in the comments! Before I go, here are some additional resources on SSH: The OpenSSH Project SSH, The Secure Shell: The Definitive Guide Introduction to SSH Versions 1 and 2 Knock, Knock, Knockin' on EnGarde's Door (with FWKNOP) Copyright 2008 Ryan All Rights Reserved. add comment | view as pdf | print
Please do not use the comment function to ask for help! If you need help, please use our forum. Comments will be published after administrator approval.
Great how-to, but for PCI compliance, you might need more
Submitted by nowen (registered user) on Thu, 2008-01-24 23:35. SSH is a great, secure tool and these suggestions are great. I would add that if you need to be PCI compliant or face some other audit requirements, you might need something more than public-key authentication. With SSH public-key authentication: There is no way to control which users have public key authorization There is no way to enforce passphrase complexity (or even be sure that one is being used) There is no way to expire a public key as I discussed here:http://www.howtoforge.com/secure_ssh_with_wikid_two_factor_authentication nick
reply |
view as pdf
Use the SSH agent.
Submitted by robertdb (registered user) on Mon, 2008-01-21 20:42. Here are some ssh-agent tricks; how to use the agent. I use these tricks daily and they help me great.
reply |
view as pdf
S/Key
Submitted by BasketCase (registered user) on Fri, 2008-01-18 16:16. If you sometimes have to ssh in from computers that are outside of your control and therefore don't have access to your private key you can use S/Key authentication. S/Key is a one time password system that uses a program on
Potrebbero piacerti anche
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- OSPF Protocol CNDocumento6 pagineOSPF Protocol CNsaraNessuna valutazione finora
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5795)
- PVT 2012 Lab Cisco JabberDocumento88 paginePVT 2012 Lab Cisco JabberGilles de PaimpolNessuna valutazione finora
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (895)
- 3.1.2.7 Packet Tracer - Troubleshooting Serial Interfaces InstructionsDocumento2 pagine3.1.2.7 Packet Tracer - Troubleshooting Serial Interfaces InstructionsjenniferespanolNessuna valutazione finora
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- Commonly Used DSCP ValuesDocumento48 pagineCommonly Used DSCP ValuesrhideNessuna valutazione finora
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (588)
- Computer Networks: Internet, Intranet, Extranet, Lan, Wan, Characteristics and DifferencesDocumento27 pagineComputer Networks: Internet, Intranet, Extranet, Lan, Wan, Characteristics and DifferenceskamijafriNessuna valutazione finora
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (400)
- Tipping Point - Comandos PDFDocumento10 pagineTipping Point - Comandos PDFMario ChelasNessuna valutazione finora
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- Chapter 1 Introduction To Network ManagementDocumento39 pagineChapter 1 Introduction To Network ManagementMe NutzNessuna valutazione finora
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- DrayTek UG Vigor1000B V1.0Documento788 pagineDrayTek UG Vigor1000B V1.0Ziad AhmedNessuna valutazione finora
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2259)
- Configuration Guide - Security (V200R002C00 - 02)Documento296 pagineConfiguration Guide - Security (V200R002C00 - 02)Miguel Angel Delgado GonzálezNessuna valutazione finora
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (74)
- Pass4Cram: Pass4cram-High-Pass-Rate IT Certification Exams CramDocumento4 paginePass4Cram: Pass4cram-High-Pass-Rate IT Certification Exams CramAdilson PedroNessuna valutazione finora
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- OptiX PTN 900 Products BrochureDocumento5 pagineOptiX PTN 900 Products BrochuregomezjcrNessuna valutazione finora
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- Lab 1.5.2: Basic Router Configuration: Topology DiagramDocumento10 pagineLab 1.5.2: Basic Router Configuration: Topology DiagramManaf BinyahiaNessuna valutazione finora
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- UCM6XXX Intro Zero ConfigDocumento37 pagineUCM6XXX Intro Zero Configsuperlucho13Nessuna valutazione finora
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (266)
- E2-E3 Ews Question Bank: A) BangaloreDocumento84 pagineE2-E3 Ews Question Bank: A) Bangalorechandrashekar_ganesanNessuna valutazione finora
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (345)
- How To Configure A Firewall For Domains and TrustsDocumento2 pagineHow To Configure A Firewall For Domains and TrustsBart SimsonNessuna valutazione finora
- 12 Cisco Catalyst 6500 (Sup 2T) QoS Design AAGDocumento2 pagine12 Cisco Catalyst 6500 (Sup 2T) QoS Design AAGpaulo_an7381Nessuna valutazione finora
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- IP Address Details DC1Documento12 pagineIP Address Details DC1Sakthi MuruganNessuna valutazione finora
- The Socket Programming and Software Design For Communication Based On Client ServerDocumento3 pagineThe Socket Programming and Software Design For Communication Based On Client Serverteja61850Nessuna valutazione finora
- NSE4 - FGT 7.0 DemoDocumento6 pagineNSE4 - FGT 7.0 DemoIsabelle CorrêaNessuna valutazione finora
- HF2421&HF2421G User ManualV1.2 (20190116)Documento79 pagineHF2421&HF2421G User ManualV1.2 (20190116)ztodorovicsezampro.rsNessuna valutazione finora
- Ciscoubrmib 3 MDocumento366 pagineCiscoubrmib 3 MAmarilys Figueroa MarreroNessuna valutazione finora
- Proxy List1Documento7 pagineProxy List1sanyam5Nessuna valutazione finora
- Ethernet Overview: Standards and Opera - OnDocumento7 pagineEthernet Overview: Standards and Opera - OnMalinga DabareraNessuna valutazione finora
- Cisco Exploration CCNA 4.0-CCNA 640-802 Blog. Questions & AnswersDocumento11 pagineCisco Exploration CCNA 4.0-CCNA 640-802 Blog. Questions & Answersvaqueva2010Nessuna valutazione finora
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- 9.4.2.6 Packet Tracer - Troubleshooting ACLs InstructionsDocumento3 pagine9.4.2.6 Packet Tracer - Troubleshooting ACLs InstructionsIVANessuna valutazione finora
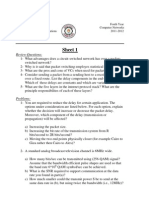
- Sheet 1Documento3 pagineSheet 1Ahmed RawyNessuna valutazione finora
- Guia de Config Basicas Mediante Interfaz Web Home Station Adb PDG A4001n PDFDocumento31 pagineGuia de Config Basicas Mediante Interfaz Web Home Station Adb PDG A4001n PDFCarlos Hernández BrotoNessuna valutazione finora
- INTRON-D Plus: System Overview, Key Components, Networking Capabilities and MoreDocumento28 pagineINTRON-D Plus: System Overview, Key Components, Networking Capabilities and MoreEhsan RohaniNessuna valutazione finora
- Route SummarizationDocumento17 pagineRoute SummarizationGossan AnicetNessuna valutazione finora
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (121)
- B Cmts Cable CMD Ref PDFDocumento3.136 pagineB Cmts Cable CMD Ref PDFp4i9e8r5Nessuna valutazione finora
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)