Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
EE2204 DSA 100 2marks
Caricato da
Vinod DeenathayalanCopyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
EE2204 DSA 100 2marks
Caricato da
Vinod DeenathayalanCopyright:
Formati disponibili
Question Bank EE2204 Data Structures and Algorithms
4202- A.C.T COLLEGE OF ENGINEERING & TECHNOLOGY
NELVOY -603107
DEPARTMENT OF COMPUTER SCIENCE & ENGINEERING
QUESTION BANK
SUBJECT CODE SUBJECT NAME SEM ESTER YEAR REGULATION
: EE2204 : DATA STRUCTURES AND ALGORITHMS : III : II : 2008
Prepared By B.Gopi Krishnan. M.E Asst.Prof/CSE. A.C.T.C.E.T Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy Page 1
Question Bank EE2204 Data Structures and Algorithms
UNIT I LINEAR STRUCTURES PART A (2 MARKS)
1. What is meant by an abstract data type? An ADT is a set of operation. Abstract data types are mathematical abstractions. Eg. Objects such as list, set and graph along their operations can be viewed as ADTs.
2. What are the operations of ADT? Union, Intersection, size, complement and find are the various operations of ADT.
3. What is meant by list ADT? List ADT is a sequential storage structure. General list of the form a1, a2,a3.., an and the size of the list is n. Any element in the list at the position I is defined to be ai, ai+1 the successor of ai and ai-1 is the predecessor of ai. 4. What are the various operations done under list ADT? Print list Insert Make empty Remove Next Previous Find kth 5. What are the different ways to implement list? Simple array implementation of list Linked list implementation of list
6. What are the advantages in the array implementation of list? Print list operation can be carried out at the linear time Find Kth operation takes a constant time
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy Page 2
Question Bank EE2204 Data Structures and Algorithms
7. What is a linked list? Linked list is a kind of series of data structures, which are not necessarily adjacent in memory. Each structure contains the element and a pointer to a record containing its successor.
8. What is a pointer? Pointer is a variable, which stores the address of the next element in the list. Pointer is basically a number.
9. What is a doubly linked list? In a simple linked list, there will be one pointer named as NEXT POINTER to point the next element, where as in a doubly linked list, there will be two pointers one to point the next element and the other to point the previous element location.
10. Define double circularly linked list. In a doubly linked list, if the last node or pointer of the list, point to the first element of the list, then it is a circularly linked list.
11. What is the need for the header? Header of the linked list is the first element in the list and it stores the number of elements in the list. It points to the first data element of the list.
12. List three examples that uses linked list. Polynomial ADT Radix sort Multi lists
13. Give some examples for linear data structures. Stack Queue
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy
Page 3
Question Bank EE2204 Data Structures and Algorithms
14. What is a stack? Stack is a data structure in which both insertion and deletion occur at one end only. Stack is maintained with a single pointer to the top of the list of elements. The other name of stack is Last-in -First-out list. 15. Write postfix from of the expression A+B-C+D? A-B+C-D+
16. How do you test for an empty queue? To test for an empty queue, we have to check whether READ=HEAD
where REAR is a pointer pointing to the last node in a queue and HEAD is a pointer that pointer to the dummy header. In the case of array implementation of queue, the condition to be checked for an empty queue is READ<FRONT.
17. What are the postfix and prefix forms of the expression? A+B*(C-D)/(P-R) Postfixform:ABCD-*PR-/+ Prefixform:+A/*B-CD-PR
18. Explain the usage of stack in recursive algorithm implementation. In recursive algorithms, stack data structures is used to store there turn address when a recursive call is encountered and also to store the values of all the parameters essential to the current state of the procedure.
19. Write down the operations that can be done with queue data structure? Queue is a first in -first out list. The operations that can be done with queue are addition and deletion.
20. What is a circular queue? The queue, which wraps around upon reaching the end of the array is called as circular queue.
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy
Page 4
Question Bank EE2204 Data Structures and Algorithms
UNIT- II TREE STRUCTURES PART A (2 MARKS) 21. Define non-linear data structure Data structure which is capable of expressing more complex relationship than that of physical adjacency is called non-linear data structure.
22. Define tree. A tree is a data structure, which represents hierarchical relationship between individual data items.
23. Define leaf. In a directed tree any node which has out degree o is called a terminal node or a leaf.
24. What is meant by directed tree? Directed tree is an acyclic diagraph which has one node called its root with in degree o while all other nodes have in degree I.
25. What is a ordered tree? In a directed tree if the ordering of the nodes at each level is prescribed then such a tree is called ordered tree.
26. What are the applications of binary tree? Binary tree is used in data processing. File index schemes Hierarchical database management system
27. What is meant by traversing? Traversing a tree means processing it in such a way, that each node is visited only once.
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy
Page 5
Question Bank EE2204 Data Structures and Algorithms
28. What are the different types of traversing? The different types of traversing are, Pre-order traversal-yields prefix form of expression. In-order traversal-yields infix form of expression. Post-order traversal-yields postfix form of expression.
29. What are the two methods of binary tree implementation? Two methods to implement a binary tree are, Linear representation. Linked representation.
30. Define pre-order traversal. Pre-order traversal entails the following steps; Process the root node Process the left subtree Process the right subtree
31. Define post-order traversal. Post order traversal entails the following steps; Process the left subtree Process the right subtree Process the root node
32. Define in-order traversal. In-order traversal entails the following steps; Process the left subtree Process the root node Process the right subtree 34. What is the maximum number of nodes in a binary tree? The Maximum number of nodes in a binary tree is 2i+1.
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy Page 6
Question Bank EE2204 Data Structures and Algorithms
35. Compare General Tree and Binary Tree? General Tree General Tree has any number of children Binary Tree Binary tree has not more than two children
36. What is complete binary tree? A tree is said to be complete binary tree ,if all its level except possibly the last level ,have the maximum number of possible nodes, all the nodes at the last level as far left as possible.
37. What is full binary tree? A binary tree is a full binary tree, if it contains maximum possible number of nodes in all level.
38. What is Expression Tree? It is a binary tree in which the leaf nodes are operands and the interior nodes are operators.
39. what is binary search tree? It is a binary tree in which for every node X in the tree, the values of all the keys in its left subtree are smaller than the key value in X, and the values of right sub tree are larger than the value in X.
40. How do you construct expression tree? Read one Symbol at a time from postfix expression. Check whether the symbol is operand or operator. If the symbol is operand, create one node tree and push pointer to the stack. If it is operator pop two pointers from the stack and form a new tree with root as operator and pointer to new node is pushed on to the stack.
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy
Page 7
Question Bank EE2204 Data Structures and Algorithms
UNIT- III BALANCED SEARCH TREES AND INDEXING PART A (2 MARKS) 41. What is AVL Tree? AVL tree Adel son Velskii and Landis Tree is a binary search tree with a balancing condition. The condition is Right and Left trees have the same height.
42. What is a balance factor in AVL trees? Balance factor of a node is defined to be the difference between the height of the node's left subtree and the height of the node's right subtree.
43. What is meant by pivot node? The node to be inserted travel down the appropriate branch track along the way of the deepest level node on the branch that has a balance factor of +1 or -1 is called pivot node.
44. What is the length of the path in a tree? The length of the path is the number of edges on the path. In a tree there is exactly one path form the root to each node. 45. What is Binary Heap and also list out the basic operations of Binary Heap? The efficient way of implementing priority queue is Binary Heap. Insertion Delete Min
46. What are Heap Properties? Structure Property Heap order Property.
47. What are the other operations of Heap? Decrease Key.
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy Page 8
Question Bank EE2204 Data Structures and Algorithms
Increase Key. Delete. Build Heap.
48. What is B-Tree and also list out the B- Tree Properties? B-Trees are balanced M-way trees, which are well suited for disks. Properties Root is either a leaf or has between 2 and M children. All no leaf nodes have between M/2 and M children. All leaves are at same depth.
49. What is hashing? The implementation of Hash Tables is called as Hashing. It is a technique used for performing insertions, deletions, and finds in constant average time. Hashing is used to perform insertions, deletions and find in constant average time. 50. Define hash function. Hash function takes an identifier and computes the address of that identifier in the hash table using some function.
51. List out the different types of hashing functions? The different types of hashing functions are, The division method The mind square method The folding method Multiplicative hashing Digit analysis 52. What is Hash Table? Hash table data structure is an array of some fixed size, containing the keys. Key is a value associated with each record.
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy
Page 9
Question Bank EE2204 Data Structures and Algorithms
53. What is Hashing function and also list out the methods of Hashing function? It is a key to address transformation, which acts upon a given key to compute the relative position of the key in the array. HASH (KEYVALUE) = KEYVALUE MOD TABLESIZE Module Division Mid Square Method Folding Method. PSEUDO Random Method Digit or Character Extraction Method. Radix Transformation
54. what is separate Chaining? Separate Chaining is an open Hashing Technique. A pointer field is added to each record location. when an overflow occurs this pointer is set to point to overflow blocks making a linked list. Advantages: More number of elements can be inserted as it uses array of linked lists.
55. What are the Disadvantages of Separate Chaining? Separate Chaining requires pointers, which occupies more memory space. Separate Chaining takes more effort to perform a search, since it takes time to evaluate hash function and also to traverse the list.
56. Define Open Addressing. Open Addressing is also called as Closed Hashing, which is an alternative to resolve the collisions with linked lists.
57. What are the Collision resolution strategies? Linear Probing Quadratic Probing. Double Hashing.
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy Page 10
Question Bank EE2204 Data Structures and Algorithms
58. When Collision Occurs? Collision occurs when a hash value of a record being inserted hashes to an address that already contains different record. (i.e.) when 2 key values hash to the same position.
59. List the Collision Resolution Techniques? Separate Chaining. Open Addressing Multiple Hashing.
60. What is Linear Probing? In Linear Probing, the position in which a key can be stored is found by sequentially searching all position starting from the position calculated by the hash function until an empty cell is found.
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy
Page 11
Question Bank EE2204 Data Structures and Algorithms
UNIT IV GRAPHS PART A (2 MARKS) 61. Define Graph. A graph G consist of a nonempty set V which is a set of nodes of the graph, a set E which is the set of edges of the graph, and a mapping from the set for edge E to a set of pairs of elements of V. It can also be represented as G= (V, E).
62. Define adjacent nodes. Any two nodes which are connected by an edge in a graph are called adjacent nodes. For E is associated with a pair of nodesexample, if and edge x (u,v) where u, v, then we say that the edge x connects the nodes u and v.
63. What is a directed graph? A graph in which every edge is directed is called a directed graph.
64. What is a undirected graph? A graph in which every edge is undirected is called a directed graph.
65. What is a loop? An edge of a graph which connects to itself is called a loop or sling.
66. What is a simple graph? A simple graph is a graph, which has not more than one edge between a pair of nodes than such a graph is called a simple graph.
67. What is a weighted graph? A graph in which weights are assigned to every edge is called a weighted graph.
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy Page 12
Question Bank EE2204 Data Structures and Algorithms
68. Define out degree of a graph? In a directed graph, for any node v, the number of edges which have v as their initial node is called the out degree of the node v.
69. Define indegree of a graph. In a directed graph, for any node v, the number of edges which have v as their terminal node is called the indegree of the node v.
70. Define path in a graph. The path in a graph is the route taken to reach terminal node from a starting node.
71. What is a simple path? A path in a diagram in which the edges are distinct is called a simple path. It is also called as edge simple.
72. What is a cycle or a circuit? A path which originates and ends in the same node is called a cycle or circuit.
73. What is an acyclic graph? A simple diagram which does not have any cycles is called an acyclic graph.
74. What is meant by strongly connected in a graph? An undirected graph is connected, if there is a path from every vertex to every other vertex. A directed graph with this property is called strongly connected.
75. When is a graph said to be weakly connected? When a directed graph is not strongly connected but the underlying graph is connected, then the graph is said to be weakly connected.
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy
Page 13
Question Bank EE2204 Data Structures and Algorithms
76. Name the different ways of representing a graph? Adjacency matrix Adjacency list
77. What is an undirected acyclic graph? When every edge in an acyclic graph is undirected, it is called an undirected a cyclic graph. It is also called as undirected forest.
78. What are the two traversal strategies used in traversing a graph? Breadth first search Depth first search
79. What is a minimum spanning tree? A minimum spanning tree of an undirected graph G is a tree formed from graph edges that connects all the vertices of G at the lowest total cost.
80. What is NP? NP is the class of decision problems for which a given proposed solution for a given input can be checked quickly to see if it is really a solution.
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy
Page 14
Question Bank EE2204 Data Structures and Algorithms
UNIT- V ALGORITHM DESIGN AND ANALYSIS PART A (2 MARKS) 81. What is Greedy Algorithm? It works in Phases. In each phase a decision is made considering the local optimum at that time that appears to be good, without considering the future consequences.
82. List some of the techniques that follow Greedy Technique. Dijkstras Shortest path algorithm. Kruskals algorithm Prims algorithm
83. List the applications that use greedy technique. Coin Change Job Scheduling File Compression Bin Packing 84. What is Huffmans algorithm? It works by selecting two characters having the lowest probabilities and replacing them with a single character whose probability is the sum of the probabilities of two characters.
85. What is bin packing and mention its different versions? This algorithm pack the items in the fewest number of bins, where each bin has unit capacity Online algorithm Offline algorithm.
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy
Page 15
Question Bank EE2204 Data Structures and Algorithms
86. What are the classic examples of Divide and Conquer? Merge Sort Quick Sort Binary Search Matrix Multiplication
87. What are the applications that use Divide and Conquer Technique? Computational Geometry. Closest points problem The selection problem
88. What is the running time of Divide and Conquer algorithm for merge sort? T (N) = 2T (N/2) +O (N)
89. What is dynamic programming? It is a technique for solving problems with overlapping sub problems.
90. Give some examples for dynamic programming. All-pairs shortest path Optimal binary search tree 91. What is working backward from the solution? When we have a solution to the problem then we have to work backward to find the starting condition. Even a guess can take us to the starting of the problem. This is very important to systematize the investigation to avoid duplication of our effort.
92. Mention some of the problem solving strategies. The most widely strategies are listed below Divide and conquer Binary doubling strategy Dynamic programming
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy Page 16
Question Bank EE2204 Data Structures and Algorithms
93. What is divide and conquer method? The basic idea is to divide the problem into several sub problems beyond which cannot be further subdivided. Then solve the sub problems efficiently and join then together to get the solution for the main problem.
94. What are the features of an efficient algorithm? Free of ambiguity Efficient in execution time Concise and compact Completeness Definiteness Finiteness 95. List down any four applications of data structures. Compiler design Operating System Database Management system Network analysis
96. What is binary doubling strategy? The reverse of binary doubling strategy, i.e. combining small problems in to one is known as binary doubling strategy. This strategy is used to avoid the generation of intermediate results.
97. Where is dynamic programming used? Dynamic programming is used when the problem is to be solved in a sequence of intermediate steps. It is particularly relevant for many optimization problems, i.e. frequently encountered in Operations research. 98. What is Backtracking algorithm and also give example? It is a search technique to replace the last component of the partially constructed solution with next option.
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy Page 17
Question Bank EE2204 Data Structures and Algorithms
Example The turnpike reconstruction problem To select moves in computer games such as chess and checkers. 99. Give some examples for Branch and Bound algorithm. Assignment Problem Knapsack Problem
100. List some of the examples of NP Complete Problems. Hamilton Circuit Travelling Salesman Problem. Knapsack, graph coloring, Bin Packing and Partition problem.
Dept. of CSE -A.C.T College of Engineering & Technology, Nelvoy
Page 18
Potrebbero piacerti anche
- Cs2201 Ds Question Bank-ActDocumento23 pagineCs2201 Ds Question Bank-ActactvenkatesanNessuna valutazione finora
- Data Structures Question BankDocumento19 pagineData Structures Question BankLn P Subramanian100% (1)
- Data Structures and Algorithms QuestionsDocumento6 pagineData Structures and Algorithms QuestionsJanuNessuna valutazione finora
- Data StructuresDocumento17 pagineData Structuresnaveen rajNessuna valutazione finora
- Ec8393 - Fundamentals of Data Structures in C: Linear DatastructuresDocumento11 pagineEc8393 - Fundamentals of Data Structures in C: Linear DatastructuresRathiNessuna valutazione finora
- Data Structures IntroductionDocumento10 pagineData Structures IntroductionManideep PaduchuriNessuna valutazione finora
- Data Structure Interview QuestionsDocumento15 pagineData Structure Interview QuestionsAmitAsthanaNessuna valutazione finora
- Data Structure Interview Questions Updated On Jul 2018Documento7 pagineData Structure Interview Questions Updated On Jul 2018Ajay MundaniyaNessuna valutazione finora
- CS 2201 - DATA STRUCTURES QUESTION BANKDocumento21 pagineCS 2201 - DATA STRUCTURES QUESTION BANKpitchrks19841Nessuna valutazione finora
- KSRC Engineering Data Structures LabDocumento23 pagineKSRC Engineering Data Structures LabveeraharishNessuna valutazione finora
- Technical Question Bank: Computer ScienceDocumento14 pagineTechnical Question Bank: Computer ScienceUttam SinghNessuna valutazione finora
- Mailam Engineering College Data Structures NotesDocumento56 pagineMailam Engineering College Data Structures NotesVasantha chandrakala RNessuna valutazione finora
- DS2 MarksDocumento25 pagineDS2 MarksPrem KumaranNessuna valutazione finora
- DS Viva QuestionsDocumento6 pagineDS Viva QuestionsDaniel MariadassNessuna valutazione finora
- Data StructuresDocumento6 pagineData StructuresArkadeep RoyNessuna valutazione finora
- DS Unit2 Answers of QBDocumento3 pagineDS Unit2 Answers of QBrbcollege123Nessuna valutazione finora
- Data Structure VIVA QuestionsDocumento11 pagineData Structure VIVA Questionshackers earthNessuna valutazione finora
- CS301MIDTERMSUBJECTIVESOLVEDDocumento9 pagineCS301MIDTERMSUBJECTIVESOLVEDMuhammad ahzamNessuna valutazione finora
- Sample Viva Questions of DSA LABDocumento2 pagineSample Viva Questions of DSA LABshubham dhabarde100% (1)
- Unit-Iv Two Mark QuestionsDocumento5 pagineUnit-Iv Two Mark QuestionsSuresh SaiNessuna valutazione finora
- Real-world applications of common data structuresDocumento26 pagineReal-world applications of common data structuresRaja KushwahNessuna valutazione finora
- DS UNIT-I 2 MarksDocumento5 pagineDS UNIT-I 2 MarksNiran JanaNessuna valutazione finora
- Pachaiyappa's College For Mens., Kanchipuram. Department of Computer Science. Data StructureDocumento17 paginePachaiyappa's College For Mens., Kanchipuram. Department of Computer Science. Data StructureamritamuraliNessuna valutazione finora
- CS301 Data Structures latest solved subjectives from midterm papersDocumento9 pagineCS301 Data Structures latest solved subjectives from midterm papersSammz HillsNessuna valutazione finora
- Data Structures Viva QuestionsDocumento5 pagineData Structures Viva Questionstanvideore91Nessuna valutazione finora
- DS&OOPs Unit IIDocumento42 pagineDS&OOPs Unit IIShanmathyNessuna valutazione finora
- Data Structures AptitudeDocumento80 pagineData Structures Aptituderavi_03dc13Nessuna valutazione finora
- 2MARKS (Data Structures Using Python)Documento22 pagine2MARKS (Data Structures Using Python)Lavanya JNessuna valutazione finora
- It33 - Data Structures and AlgorithmsDocumento20 pagineIt33 - Data Structures and AlgorithmsMathan NaganNessuna valutazione finora
- 200+ TOP DATA STRUCTURES LAB VIVA Questions and Answers CSE VIVA QuestionsDocumento21 pagine200+ TOP DATA STRUCTURES LAB VIVA Questions and Answers CSE VIVA QuestionsHarshal ChaudharyNessuna valutazione finora
- Data Structures VIVA Questions and AnswersDocumento6 pagineData Structures VIVA Questions and AnswersAchyuth Koteswarao100% (1)
- GKM College of Engineering and Technology: Cs1211 - Data Structures and AlgorithmsDocumento14 pagineGKM College of Engineering and Technology: Cs1211 - Data Structures and AlgorithmsCSETUBENessuna valutazione finora
- Data Structure (2marks)Documento9 pagineData Structure (2marks)Akash SanjeevNessuna valutazione finora
- Introduction To Data Structure: What Is Information?Documento6 pagineIntroduction To Data Structure: What Is Information?Sayan Kumar KhanNessuna valutazione finora
- 320 - CS8391 Data Structures - Important QuestionsDocumento22 pagine320 - CS8391 Data Structures - Important Questionscurrent job100% (3)
- Define data structure 2023 question paper with solutionDocumento35 pagineDefine data structure 2023 question paper with solutionBrijesh C.GNessuna valutazione finora
- Viva Questions For Data Structures LabDocumento12 pagineViva Questions For Data Structures LabnonameNessuna valutazione finora
- DSA (Lalit)Documento24 pagineDSA (Lalit)LittaNessuna valutazione finora
- Datastructures LabDocumento18 pagineDatastructures LabgmerlingeorgeNessuna valutazione finora
- Unit-I Linear StructuresDocumento5 pagineUnit-I Linear Structuresrajen789Nessuna valutazione finora
- DSA Interview Questions QuestionDocumento16 pagineDSA Interview Questions QuestionChiragNessuna valutazione finora
- Viva QuestionsDocumento12 pagineViva QuestionsVickyGaming YTNessuna valutazione finora
- Unit 2Documento10 pagineUnit 2see thaNessuna valutazione finora
- Bca C201 QB01Documento21 pagineBca C201 QB01Anjali PawarNessuna valutazione finora
- Data Structure Interview Questions PDFDocumento4 pagineData Structure Interview Questions PDFTrisha SurNessuna valutazione finora
- CRT Technical Data StructuresDocumento7 pagineCRT Technical Data Structureskark437Nessuna valutazione finora
- Cs8391-Data StructureDocumento21 pagineCs8391-Data StructureAmudariaNessuna valutazione finora
- ECE DS Notes 2010 NewDocumento92 pagineECE DS Notes 2010 NewNaveen RajNessuna valutazione finora
- Data Structures Technical Interview QuestionsDocumento11 pagineData Structures Technical Interview QuestionsManoj Kumar GNessuna valutazione finora
- Data Structure Technical Interview Questions and AnswersDocumento8 pagineData Structure Technical Interview Questions and AnswersShivansh tomarNessuna valutazione finora
- EC8393 QB 01 2MARKS - by LearnEngineering - inDocumento9 pagineEC8393 QB 01 2MARKS - by LearnEngineering - inroger basuNessuna valutazione finora
- Dynamic Trees in Data Structure PDFDocumento6 pagineDynamic Trees in Data Structure PDFRASHMI DABRENessuna valutazione finora
- Technical Written Exam Questions: Data StructureDocumento10 pagineTechnical Written Exam Questions: Data StructureRaghunath RampurNessuna valutazione finora
- Viva Question For DSDocumento11 pagineViva Question For DSSaifNessuna valutazione finora
- Mastering Data Structures and Algorithms in C and C++Da EverandMastering Data Structures and Algorithms in C and C++Nessuna valutazione finora
- Data Structures in C / C ++: Exercises and Solved ProblemsDa EverandData Structures in C / C ++: Exercises and Solved ProblemsNessuna valutazione finora
- Advanced C Concepts and Programming: First EditionDa EverandAdvanced C Concepts and Programming: First EditionValutazione: 3 su 5 stelle3/5 (1)
- Opengl - Control FunctionsDocumento3 pagineOpengl - Control FunctionsVinod DeenathayalanNessuna valutazione finora
- Anna University:: Chennai - 600 025: Office of The Controller of ExaminationsDocumento1 paginaAnna University:: Chennai - 600 025: Office of The Controller of ExaminationsVinod DeenathayalanNessuna valutazione finora
- IV Cse - Cns - Ia1 - Set ADocumento1 paginaIV Cse - Cns - Ia1 - Set AVinod DeenathayalanNessuna valutazione finora
- Anna University:: Chennai - 600025. Office of The Controller of Examinations Provisional Results of Nov. / Dec. Examination, 2018. Page 1/7Documento7 pagineAnna University:: Chennai - 600025. Office of The Controller of Examinations Provisional Results of Nov. / Dec. Examination, 2018. Page 1/7Vinod DeenathayalanNessuna valutazione finora
- Chap 8Documento22 pagineChap 8Disha AroraNessuna valutazione finora
- Web Designing BasicsDocumento3 pagineWeb Designing BasicsVinod DeenathayalanNessuna valutazione finora
- Anna University:: Chennai - 600 025: Office of The Controller of ExaminationsDocumento1 paginaAnna University:: Chennai - 600 025: Office of The Controller of ExaminationsVinod DeenathayalanNessuna valutazione finora
- Weekly Test-1 Bio 7aug2017Documento1 paginaWeekly Test-1 Bio 7aug2017Vinod DeenathayalanNessuna valutazione finora
- Co Comp NetworkDocumento2 pagineCo Comp NetworkVinod DeenathayalanNessuna valutazione finora
- Home Tutor Site MARKS: 50 DATE: 06.07.2017 Cbse Class X Science Pa-1 Time: 60 MinutesDocumento2 pagineHome Tutor Site MARKS: 50 DATE: 06.07.2017 Cbse Class X Science Pa-1 Time: 60 MinutesVinod DeenathayalanNessuna valutazione finora
- Ethics FullDocumento32 pagineEthics Fullbalaji badshahNessuna valutazione finora
- cs6711 Security LabDocumento1 paginacs6711 Security LabVinod DeenathayalanNessuna valutazione finora
- Chap 8Documento22 pagineChap 8Disha AroraNessuna valutazione finora
- SCIENCE TEST1 07augDocumento2 pagineSCIENCE TEST1 07augVinod DeenathayalanNessuna valutazione finora
- Section A (2 6 12) Answer All The Questions 2 Mark EachDocumento2 pagineSection A (2 6 12) Answer All The Questions 2 Mark EachVinod DeenathayalanNessuna valutazione finora
- A Conventional Model For Security Challenges in Industrial Internet of ThingsDocumento7 pagineA Conventional Model For Security Challenges in Industrial Internet of ThingsVinod DeenathayalanNessuna valutazione finora
- Ec8561 Communication System LabDocumento1 paginaEc8561 Communication System LabVinod Deenathayalan100% (1)
- IBPS Clerk Pre QUANT Memory Based 2019 QuestionsDocumento8 pagineIBPS Clerk Pre QUANT Memory Based 2019 Questionsk vinayNessuna valutazione finora
- The Banking Current Affairs February 2018Documento4 pagineThe Banking Current Affairs February 2018Devesh KumarNessuna valutazione finora
- IBPS Clerk Pre ENG Memory Based 2019 Questions PDFDocumento8 pagineIBPS Clerk Pre ENG Memory Based 2019 Questions PDFSwarna LathaNessuna valutazione finora
- IBPS Clerk Prelims Memory Based (Reasoning AbilityDocumento8 pagineIBPS Clerk Prelims Memory Based (Reasoning AbilitySunny Dara Rinnah SusanthNessuna valutazione finora
- Eeca Lesson PlanDocumento5 pagineEeca Lesson PlanVinod DeenathayalanNessuna valutazione finora
- Daa May 2015 PDFDocumento19 pagineDaa May 2015 PDFVinod DeenathayalanNessuna valutazione finora
- IBPS Clerk Pre Memory Based 2019 Solutions PDFDocumento14 pagineIBPS Clerk Pre Memory Based 2019 Solutions PDFSunny Dara Rinnah SusanthNessuna valutazione finora
- A Conventional Model For Security Challenges in Industrial Internet of ThingsDocumento5 pagineA Conventional Model For Security Challenges in Industrial Internet of ThingsVinod DeenathayalanNessuna valutazione finora
- Academic Qualification:: Bio DataDocumento1 paginaAcademic Qualification:: Bio DataVinod DeenathayalanNessuna valutazione finora
- Ilovepdf JPG To PDFDocumento1 paginaIlovepdf JPG To PDFVinod DeenathayalanNessuna valutazione finora
- HSN LP-SEM 2015 With RemarksDocumento5 pagineHSN LP-SEM 2015 With RemarksVinod DeenathayalanNessuna valutazione finora
- All Possible 2 Mark 16 Mark III CSEDocumento18 pagineAll Possible 2 Mark 16 Mark III CSEVinod DeenathayalanNessuna valutazione finora
- IBPS Clerk Prelims Memory Based (Reasoning AbilityDocumento8 pagineIBPS Clerk Prelims Memory Based (Reasoning AbilitySunny Dara Rinnah SusanthNessuna valutazione finora
- At HomeDocumento16 pagineAt HomesamoorewritesNessuna valutazione finora
- The General RetiresDocumento17 pagineThe General Retiresfo100% (1)
- v072n10p257 PDFDocumento8 paginev072n10p257 PDFLmf DanielNessuna valutazione finora
- English (Step Ahead)Documento33 pagineEnglish (Step Ahead)ry4nek4100% (1)
- Chara LesDocumento5 pagineChara Lesx456456456xNessuna valutazione finora
- Overweight and Obesity in AmericaDocumento10 pagineOverweight and Obesity in Americamzvette234Nessuna valutazione finora
- The Ultimate 30 Day Guide To Going Full Carnivore PDFDocumento76 pagineThe Ultimate 30 Day Guide To Going Full Carnivore PDFJanZen100% (1)
- Irish Blessings and PrayersDocumento17 pagineIrish Blessings and PrayersvivesurNessuna valutazione finora
- Conquest of The Americas (Eakin-2002)Documento81 pagineConquest of The Americas (Eakin-2002)GregNessuna valutazione finora
- Present Tense Review for Motorcycle RepairDocumento2 paginePresent Tense Review for Motorcycle RepairFaheemuddin Veterans50% (2)
- Allosteric EnzymeDocumento22 pagineAllosteric EnzymeAhmed ImranNessuna valutazione finora
- Number System ConversionDocumento26 pagineNumber System ConversionMahesh Chandra UpadhyayNessuna valutazione finora
- Shaft Deflection in Centrifugal PumpsDocumento2 pagineShaft Deflection in Centrifugal PumpsPieter van der WaltNessuna valutazione finora
- GDPR in ChartsDocumento13 pagineGDPR in ChartsImageking0% (2)
- GEY 102-Introduction To Geology 1-Lecture Slides - Prof. M.E. NtonDocumento44 pagineGEY 102-Introduction To Geology 1-Lecture Slides - Prof. M.E. Ntonabuabdmuqseet2001Nessuna valutazione finora
- Initial Evaluation in The 11th Form B1 LevelDocumento2 pagineInitial Evaluation in The 11th Form B1 LevelDumitru GruscaNessuna valutazione finora
- Paradine V Jane - (1646) 82 ER 897Documento2 pagineParadine V Jane - (1646) 82 ER 897TimishaNessuna valutazione finora
- Paper 3 Vol XXXX No. 2 Dec 2010Documento11 paginePaper 3 Vol XXXX No. 2 Dec 2010Mubi BaloliyaNessuna valutazione finora
- Capillary Puncture Equipment and Procedures: Topic 7Documento39 pagineCapillary Puncture Equipment and Procedures: Topic 7Angelica Camille B. AbaoNessuna valutazione finora
- My Reading Experience of 'Hello Bastar' Highlighting Development, Decentralization and DefenseDocumento3 pagineMy Reading Experience of 'Hello Bastar' Highlighting Development, Decentralization and DefenseSri Tejaswini Mantena0% (1)
- AbstractsbDocumento95 pagineAbstractsbaptureinc100% (1)
- Female by CourseDocumento40 pagineFemale by CourseMohamed AymanNessuna valutazione finora
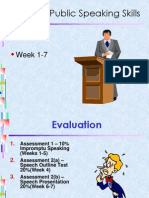
- TOPIC 1 - Public Speaking SkillsDocumento72 pagineTOPIC 1 - Public Speaking SkillsAyan AkupNessuna valutazione finora
- Homework Week 13Documento2 pagineHomework Week 13Nigar QurbanovaNessuna valutazione finora
- Endocrine System Multiple Choice QuestionsDocumento42 pagineEndocrine System Multiple Choice QuestionswanderagroNessuna valutazione finora
- 7 Cancer Immunotherapy Etc-2020Documento32 pagine7 Cancer Immunotherapy Etc-2020Syifa KhairunnisaNessuna valutazione finora
- E-Portfolio Rubric For HHS4C: Criteria Level 1 Level 2 Level 3 Level 4 Overall Expectation ADocumento4 pagineE-Portfolio Rubric For HHS4C: Criteria Level 1 Level 2 Level 3 Level 4 Overall Expectation Aapi-312895913Nessuna valutazione finora
- DualSPHysics v4.0 GUIDE PDFDocumento140 pagineDualSPHysics v4.0 GUIDE PDFFelipe A Maldonado GNessuna valutazione finora
- Project MethodDocumento6 pagineProject MethodMtr Jonathan Uribe CarvajalNessuna valutazione finora
- A Course in KettlebellsDocumento40 pagineA Course in KettlebellsMagoots100% (1)