Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
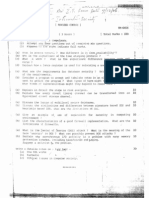
IS Paper 2
Caricato da
Nikhil BagayatkarDescrizione originale:
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
IS Paper 2
Caricato da
Nikhil BagayatkarCopyright:
Formati disponibili
-I ..
,
". - .,. t c.. on /2943-05._,
( 3 Hours ) Total Marks =
.~. (1) Q. No. 1 is compulsory~
(b)
(d)
3) ( 2)
((6)
4)
5) Attempt any four out of remaining six questions.
(c)
(a) Assume any suitable data wherever required but justify the same.
Figures to the right indicate full marks.
Answers to questions should be grouped and written together.
Use legible handwriting.' Use'a blue/black ink pen to write answers.
Distinguish among vulnerability, threat and control.
Can a database contain two identical records without a negative effect
on the integrity of the database!? WhY' or why not?
Explain how a fence register is used for reLocating a user's program.
Compare Copyriqht, Patent and Tr~de Secret Protection.
(a) What is access control? How different is it from availability ?
(b) What are the requirements for database security? Briefly examine each
of the requirements.
( c:) Consider a program to accept and tabulate votes
tn an elector.
Who might want to attack the prog::-am?What.. types of harm m.i.ghtthey
want. to cause? What kinds of vulnerabilities miqht they exploit to
cause harm ?
(a) What is the security purpose for the fields, such as sequence number '.of
an IPSec packet ?
(b) UNDO is a recovery operation for databases. It is a command that
obtains information from a transaction log and resets the elements of a
database to their values before a particular transaction is performed.
Describe a situation in wryich an UNDO command would be useful.
(c) Explain why asynchronous I/O activity is a problem with many memory
protection schemes, including base/bounds and paging. Suggest a
solution to the problem.
(a) List two disadvantages of using physical separation in a computing
system. List two disadvantages of using temporal separation in a
computing system.
(b) Explain Encryption in a multilevel se~ure database management system.
(c) Comparison between the several types of firewalls, such as packet
filtering, Stateful inspection, Application proxy, Guard, Personal
firewall.
I Ie) (b)
(c)
(b)
(a)
(a) Comparison between Lj nk and End-to-End encryption in terms of security
within hosts, Role of user and implecentation concerns.
Explain secure E-mail systems with examples.
List the characteristics of a good firewall implementation. What are
the limitations of a firewall?
Ii
What is the IP spoofing attack ? I'v'hy is it
not easy to detect IP
spoofing attacks?
What is the Denial of Service (DOS) attack? What is the meaning of the
term 'service' in DOS? Hhat can possibly>prevent DOS attacks ?
Explain the term 'Risk Analysis'. List the basic steps of risk
analysis.
Write a details notes on (any two) :-
(a) Kerberos.
(b) Intrusion detection systems.
(c) Contents of a security plan.
Potrebbero piacerti anche
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDa EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeValutazione: 4 su 5 stelle4/5 (5794)
- BusinessStudies12 Finance MarketDocumento24 pagineBusinessStudies12 Finance MarketRam VermaNessuna valutazione finora
- Shoe Dog: A Memoir by the Creator of NikeDa EverandShoe Dog: A Memoir by the Creator of NikeValutazione: 4.5 su 5 stelle4.5/5 (537)
- Chapter 1Documento15 pagineChapter 1ravindhra365Nessuna valutazione finora
- Geography (Mains) Previous 33 Years Question Papers (1979-2011) by (WWW - Mrunal.org) For UPSC IAS IPS ExamDocumento51 pagineGeography (Mains) Previous 33 Years Question Papers (1979-2011) by (WWW - Mrunal.org) For UPSC IAS IPS Examajaybisht42% (12)
- The Yellow House: A Memoir (2019 National Book Award Winner)Da EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Valutazione: 4 su 5 stelle4/5 (98)
- IS Paper 3Documento1 paginaIS Paper 3Nikhil BagayatkarNessuna valutazione finora
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDa EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceValutazione: 4 su 5 stelle4/5 (895)
- Is Paper1Documento1 paginaIs Paper1Nikhil BagayatkarNessuna valutazione finora
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDa EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersValutazione: 4.5 su 5 stelle4.5/5 (344)
- Ips and IDS - 090356Documento13 pagineIps and IDS - 090356Muhammad AslamNessuna valutazione finora
- The Little Book of Hygge: Danish Secrets to Happy LivingDa EverandThe Little Book of Hygge: Danish Secrets to Happy LivingValutazione: 3.5 su 5 stelle3.5/5 (399)
- M01 - What Is Cisco ACI PDFDocumento33 pagineM01 - What Is Cisco ACI PDFkingsley0504Nessuna valutazione finora
- Grit: The Power of Passion and PerseveranceDa EverandGrit: The Power of Passion and PerseveranceValutazione: 4 su 5 stelle4/5 (588)
- 1.0 Network Fundamentals: 1.1 Explain The Role and Function of Network ComponentsDocumento12 pagine1.0 Network Fundamentals: 1.1 Explain The Role and Function of Network ComponentsMOU RFIXNessuna valutazione finora
- The Emperor of All Maladies: A Biography of CancerDa EverandThe Emperor of All Maladies: A Biography of CancerValutazione: 4.5 su 5 stelle4.5/5 (271)
- Installation and Administration Guide SEP14.3RU6Documento697 pagineInstallation and Administration Guide SEP14.3RU6Y.FNessuna valutazione finora
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDa EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaValutazione: 4.5 su 5 stelle4.5/5 (266)
- ITS OD 105 Cybersecurity Pearson 0922Documento3 pagineITS OD 105 Cybersecurity Pearson 0922Lorita GrafNessuna valutazione finora
- Never Split the Difference: Negotiating As If Your Life Depended On ItDa EverandNever Split the Difference: Negotiating As If Your Life Depended On ItValutazione: 4.5 su 5 stelle4.5/5 (838)
- RHEL7 RHCSA Exam ObjectivesDocumento11 pagineRHEL7 RHCSA Exam ObjectivesSujitkumarManeNessuna valutazione finora
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDa EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryValutazione: 3.5 su 5 stelle3.5/5 (231)
- Fortinet - Premium.NSE4 FGT-6.0.by .VCEplus.36qDocumento24 pagineFortinet - Premium.NSE4 FGT-6.0.by .VCEplus.36qFortilab FortilabNessuna valutazione finora
- CCNA Security Lab 3 - Cisco Context-Based Access Control - CLIDocumento10 pagineCCNA Security Lab 3 - Cisco Context-Based Access Control - CLIvelramsenNessuna valutazione finora
- On Fire: The (Burning) Case for a Green New DealDa EverandOn Fire: The (Burning) Case for a Green New DealValutazione: 4 su 5 stelle4/5 (73)
- Anil Sharma ResumeDocumento5 pagineAnil Sharma Resumebindu sharmaNessuna valutazione finora
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDa EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureValutazione: 4.5 su 5 stelle4.5/5 (474)
- Network Security Bangla BookDocumento69 pagineNetwork Security Bangla BookMd Nurul Islam75% (8)
- Team of Rivals: The Political Genius of Abraham LincolnDa EverandTeam of Rivals: The Political Genius of Abraham LincolnValutazione: 4.5 su 5 stelle4.5/5 (234)
- PCNSE - Prepaway.premium - Exam.162q yKUtEdPDocumento63 paginePCNSE - Prepaway.premium - Exam.162q yKUtEdPaliseksendeliNessuna valutazione finora
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDa EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyValutazione: 3.5 su 5 stelle3.5/5 (2259)
- Anwesha CyberDocumento29 pagineAnwesha CyberAnwesha TripathyNessuna valutazione finora
- Private Firewall InstructiuniDocumento54 paginePrivate Firewall InstructiunisudastralNessuna valutazione finora
- CIS Controls v8 Mapping To Microsoft Azure Security Benchmarkv3 2 202Documento224 pagineCIS Controls v8 Mapping To Microsoft Azure Security Benchmarkv3 2 202Franck BNessuna valutazione finora
- Course-Overview XG-Firewall AdministratorDocumento4 pagineCourse-Overview XG-Firewall AdministratorIdrisss SoumahoroNessuna valutazione finora
- Study and Analysis of KSU Computer NetworkDocumento112 pagineStudy and Analysis of KSU Computer NetworkmandarinakosNessuna valutazione finora
- The Unwinding: An Inner History of the New AmericaDa EverandThe Unwinding: An Inner History of the New AmericaValutazione: 4 su 5 stelle4/5 (45)
- CS L06 Strategic Defense02 1599891190158 PDFDocumento43 pagineCS L06 Strategic Defense02 1599891190158 PDFamitNessuna valutazione finora
- Srikanth Reddu Baddam - CISCODocumento7 pagineSrikanth Reddu Baddam - CISCOmandeepmailsNessuna valutazione finora
- Scripting With MikrotikDocumento16 pagineScripting With MikrotikNaz LunNessuna valutazione finora
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDa EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreValutazione: 4 su 5 stelle4/5 (1090)
- Mitel Call Paths and PortsDocumento18 pagineMitel Call Paths and PortsChris McAndrewNessuna valutazione finora
- Fuel Virtual Test Lab 8 Quick Start Guide PDFDocumento7 pagineFuel Virtual Test Lab 8 Quick Start Guide PDFilyasNessuna valutazione finora
- اسئله سايبر فاينلDocumento72 pagineاسئله سايبر فاينلOMAR ALKHUDAYDINessuna valutazione finora
- Cisco Meraki TrainingDocumento3 pagineCisco Meraki TrainingPartha Sarathi NandiNessuna valutazione finora
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Da EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Valutazione: 4.5 su 5 stelle4.5/5 (120)
- Mediabox: User'S ManualDocumento42 pagineMediabox: User'S ManualMohd Khairul Md DinNessuna valutazione finora
- Asset Management - Security MonitoringDocumento182 pagineAsset Management - Security MonitoringRahul KumarNessuna valutazione finora
- Principles of Information Security, Fifth Edition: Security Technology: Firewalls and VpnsDocumento65 paginePrinciples of Information Security, Fifth Edition: Security Technology: Firewalls and VpnsCharlito MikolliNessuna valutazione finora
- Best Practices For PC DSS 3 Network Security Compliance White PaperDocumento9 pagineBest Practices For PC DSS 3 Network Security Compliance White Papero0000oNessuna valutazione finora
- Iptables 2Documento34 pagineIptables 2Claudemir De Almeida RosaNessuna valutazione finora
- Original Thomson Twg870 ManualDocumento90 pagineOriginal Thomson Twg870 Manualbabalinsky0% (1)
- Her Body and Other Parties: StoriesDa EverandHer Body and Other Parties: StoriesValutazione: 4 su 5 stelle4/5 (821)