Documenti di Didattica
Documenti di Professioni
Documenti di Cultura
CEF Configuration Guide 03 02 11
Caricato da
baywatch318Descrizione originale:
Copyright
Formati disponibili
Condividi questo documento
Condividi o incorpora il documento
Hai trovato utile questo documento?
Questo contenuto è inappropriato?
Segnala questo documentoCopyright:
Formati disponibili
CEF Configuration Guide 03 02 11
Caricato da
baywatch318Copyright:
Formati disponibili
Event Interoperability Standard
Common Event Format Configuration Guide
Palo Alto Networks PAN-OS 4.0.0 Date: March 2, 2011
ArcSight Technical Note Contains Confidential and Proprietary Information
Event Interoperability Standard
CEF Connector Configuration Guide Palo Alto Networks PAN-OS 4.0.0 February 25, 2011
Revision History
Date
02/25/2011 03/02/2011
Description
First edition of this Configuration Guide. Certified CEF Compliant PAN-OS4.0.0
ArcSight Technical Note Contains Confidential and Proprietary Information
Event Interoperability Standard
PAN-OS 4.0.0 CEF Configuration Guide
This guide provides information for configuring the Palo Alto Networks next-generation firewalls for CEF-formatted syslog event collection. PAN-OS version 4.0.0 or higher is supported.
Overview
Palo Alto Networks next-generation firewalls provide network security by enabling enterprises to see and control applications, users, and content not just ports, IP addresses, and packets using three unique identification technologies: App-ID, User-ID, and Content-ID. These identification technologies, found in Palo Alto Networks' enterprise firewalls, enable enterprises to create business-relevant security policies safely enabling organizations to adopt new applications, instead of the traditional all-or-nothing approach offered by traditional port-blocking firewalls used in many security infrastructures. Next-generation firewall model families include Palo Alto Networks' PA-5000 Series, PA4000 Series, PA-2000 Series, and the PA-500; and range from 250Mbps to 20Gbps in throughput capacity. Delivered as a purpose-built appliance, every Palo Alto Networks next-generation firewall utilizes dedicated, function specific processing that is tightly integrated with a single-pass software engine. This unique combination of hardware and software maximizes network throughput while minimizing latency. Each of the hardware platforms supports the same rich set of next-generation firewall features ensuring consistent operation across the entire line.
Configuration
Configure the Palo Alto Networks device for ArcSight CEF-formatted syslog events based on information from the PAN-OS administrators guide. 1. 2. 3. Open the UI and select the Device tab. On the left hand side select Syslog under Server Profiles and click Add. In the Syslog Server Profile Dialog enter a server profile Name and Location (location refers to a Virtual System). Select Servers tab, and click Add to provide a name for the Syslog server, IP address, Port (default 514), and Facility (default LOG_USER). Select Custom Log Format tab, and click on any of the listed log types Config/System/Threat/Traffic/HIPMatch to define a custom format based on the ArcSight CEF for that log type.
4.
5.
Below table shows the CEF-style format that was used during the certification process for each log type. These custom formats include all the fields that are displayed in the default format of the syslogs in a similar order. NOTE: Customers can choose to define their own CEF-style formats using the event mapping table provided in addition to this document. The Custom Log Format tab supports escaping any characters defined in the CEF as
ArcSight Technical Note Contains Confidential and Proprietary Information
Event Interoperability Standard
special characters. For instance, to escape the backslash and equal characters by a backslash, specify \= as the Escaped characters and \ as the Escape character. Traffic CEF:0|Palo Alto Networks|PAN-OS|4.0.0|$subtype|$type|1|rt=$cefformatted-receive_time deviceExternalId=$serial src=$src dst=$dst sourceTranslatedAddress=$natsrc destinationTranslatedAddress=$natdst cs1Label=Rule cs1=$rule suser=$srcuser duser=$dstuser app=$app cs3Label=Virtual System cs3=$vsys cs4Label=Source Zone cs4=$from cs5Label=Destination Zone cs5=$to deviceInboundInterface=$inbound_if deviceOutboundInterface=$outbound_if cs6Label=LogProfile cs6=$logset cn1Label=SessionID cn1=$sessionid cnt=$repeatcnt spt=$sport dpt=$dport sourceTranslatedPort=$natsport destinationTranslatedPort=$natdport flexString1Label=Flags flexString1=$flags proto=$proto act=$action flexNumber1Label=Total bytes flexNumber1=$bytes cn2Label=Packets cn2=$packets start=$cefformatted-time_generated cn3Label=Elapsed time in seconds cn3=$elapsed cs2Label=URL Category cs2=$category CEF:0|Palo Alto Networks|PAN-OS|4.0.0|$subtype $threatid|$type|$number-of-severity|rt=$cef-formatted-receive_time deviceExternalId=$serial src=$src dst=$dst sourceTranslatedAddress=$natsrc destinationTranslatedAddress=$natdst cs1Label=Rule cs1=$rule suser=$srcuser duser=$dstuser app=$app cs3Label=Virtual System cs3=$vsys cs4Label=Source Zone cs4=$from cs5Label=Destination Zone cs5=$to deviceInboundInterface=$inbound_if deviceOutboundInterface=$outbound_if cs6Label=LogProfile cs6=$logset cn1Label=SessionID cn1=$sessionid cnt=$repeatcnt spt=$sport dpt=$dport sourceTranslatedPort=$natsport destinationTranslatedPort=$natdport flexString1Label=Flags flexString1=$flags proto=$proto act=$action msg=$misc cs2Label=URL Category cs2=$category deviceDirection=$direction CEF:0|Palo Alto Networks|PAN-OS|4.0.0|$subtype $result|$type|1|rt=$cef-formatted-receive_time deviceExternalId=$serial dvchost=$host cs3Label=Virtual System cs3=$vsys act=$cmd duser=$admin destinationServiceName=$client msg=$path CEF:0|Palo Alto Networks|PAN-OS|4.0.0|$subtype $eventid|$type $eventid|$number-of-severity|rt=$cef-formatted-receive_time deviceExternalId=$serial cs3Label=Virtual System cs3=$vsys fname=$object flexString2Label=Module flexString2=$module msg=$fmt CEF:0|Palo Alto Networks|PAN-OS|4.0.0|$subtype $hip|$type $hiptype|1|rt=$cef-formatted-receive_time deviceExternalId=$serial suser=$srcuser cs3Label=Virtual System cs3=$vsys shost=$machinename src=$src cnt=$repeatcnt
Threat
Config
System
HIP Match
ArcSight Technical Note Contains Confidential and Proprietary Information
Event Interoperability Standard
ArcSight Technical Note Contains Confidential and Proprietary Information
Event Interoperability Standard
Screen Shot
Shown below is a screenshot of the Active Channel page on the ArcSight CEF Server showing the events generated by a Palo Alto Networks Device.
Events
The different log types for which syslogs are generated include TRAFFIC, THREAT, CONFIG, SYSTEM, and HIP MATCH. For the SYSTEM events, the $eventid field captures the specific event associated with that log. Refer to the System Logs document for a listing of all the events grouped by the system area.
Device Event Mapping to ArcSight Data Fields
Information contained within vendor-specific event definitions is sent to the ArcSight SmartConnector, and then mapped to an ArcSight data field. Definitions of Prefix Fields and their values for syslog messages generated by Palo Alto Networks firewalls. The Extension Dictionary that lists Palo Alto Networks-specific event definitions and their mapping to ArcSight CEF data fields.
Prefix fields
CEF Name Data type Meaning Palo Alto Networks Value 0
Version
Integer
Identifies the version of the CEF format. Device Vendor Device Product Device Version Unique identifier per event-type
Device Vendor Device Product Device Version Signature ID
String String String String
Palo Alto Networks PAN-OS Configurable. E.g. 4.0.0 Value is event-type specific:
ArcSight Technical Note Contains Confidential and Proprietary Information
Event Interoperability Standard
Traffic:$subtype Threat:$subtype $threatid Config:$subtype $result System: $subtype $eventid HIP: $subtype $hip Name String Represents a humanreadable and understandable description of the event. Value is event-type specific. Traffic:$type Threat:$type Config:$type System: $type $eventid HIP Match:$type $hiptype Severity Integer Reflects the importance of the event. Only numbers from 0 to 10 are allowed, where 10 indicates the most important event. $number-of-severity Always 1 for traffic, config, and HIP events.
Extension Dictionary
CEF Key Name Full Name Data Type Length Meaning Palo Alto Networks Value Field Value is eventtype specific: Traffic : $action Threat: $action Config: $cmd app ApplicationProto col String 31 Application level protocol, example values are: HTTP, HTTPS, SSHv2, Telnet, POP, IMAP, IMAPS, etc. Represents the category assigned by the originating device. Devices oftentimes use their own categorization schema to classify events. SessionID $sessionid $app
act
deviceAction
String
63
Action mentioned in the event.
cat
deviceEventCat egory
String
1023
cn1
deviceCustomN umber1
Long
ArcSight Technical Note Contains Confidential and Proprietary Information
Event Interoperability Standard
CEF Key Name
Full Name
Data Type
Length
Meaning
Palo Alto Networks Value Field
cn1Label
deviceCustomN umber1 Label deviceCustomN umber2 deviceCustomN umber2Label deviceCustomN umber3 deviceCustomN umber3Label baseEventCount
String
1023
SessionID
cn2
Long
Packets
$packets
cn2Label
String
1023
Packets
cn3
Long
Elapsed time
$elapsed
cn3Label
String
1023
Elapsed time in seconds A count associated with this event. How many times was this same event observed? $repeatcnt
cnt
Integer
cs1
deviceCustomSt ring1
String
1023
Rule
$rule
cs1Label
deviceCustomSt ring1Label
String
1023
Rule
cs2
deviceCustomSt ring2
String
1023
URL Category
$category
cs2Label
deviceCustomSt ring2Label
String
1023
URL Category
cs3
deviceCustomSt ring3
String
1023
Vsys
$vsys
cs3Label
deviceCustomSt ring3Label
String
1023
Virtual System
ArcSight Technical Note Contains Confidential and Proprietary Information
Event Interoperability Standard
CEF Key Name
Full Name
Data Type
Length
Meaning
Palo Alto Networks Value Field $from
cs4
deviceCustomSt ring4
String
1023
Srczone
cs4Label
deviceCustomSt ring4Label deviceCustomSt ring5 deviceCustomSt ring5Label deviceCustomSt ring6 deviceCustomSt ring6Label
String
1023
Source Zone
cs5
String
1023
Dstzone
$to
cs5Label
String
1023
Destination Zone
cs6
String
1023
LogProfile
$logset
cs6Label
String
1023
LogProfile
destinationService Name
String
1023
The service which is targeted by this event.
Value is eventtype specific: Config: $client
destinationTransla ted Address
IPv4 Address
Identifies the translated destination that the event refers to in an IP network. The format is an IPv4 address.Example: 192.168.10.1 Port after it was translated; for example, a firewall. Valid port numbers are 0 to 65535. Any information about what direction the communication that was observed has taken. 255 A name that uniquely identifies the device generating this event. Serial Number of the device.
$natdst
destinationTransla tedPort
Integer
$natdport
deviceDirection
String
$direction
deviceExternalId
String
$serial
deviceInboundInte rface
String
15
Interface on which the packet or data entered the device. Interface on which the packet or data left the device.
$inbound_if
deviceOutboundIn terface
String
15
$outbound_if
ArcSight Technical Note Contains Confidential and Proprietary Information
Event Interoperability Standard
CEF Key Name
Full Name
Data Type
Length
Meaning
Palo Alto Networks Value Field $dport
dpt
destinationPort
Integer
The valid port numbers are between 0 and 65535. Identifies destination that the event refers to in an IP network. The format is an IPv4 address.Example: 192.168.10.1 1023 Identifies the destination user by name. This is the user associated with the event's destination. Email addresses are also mapped into the UserName fields. The recipient is a candidate to put into destinationUserName. The format should be a fully qualified domain name associated with the device node, when a node is available.Examples: host.domain.com or host. Total bytes (rx and tx)
dst
destinationAddr ess
IPv4 Address
$dst
duser
destinationUser Name
String
Value is eventtype specifc: Traffic: $dstuser Threat:$dstuser Config: $admin
dvchost
deviceHostNam e
String
100
Value is eventtype specific: Config: $host
flexNumber1 flexNumber1Label flexString1 flexString1Label flexString2 String String String String
$bytes
Total bytes Flags Flags Module Value is eventtype specific: System:$module $flags
flexString2Label fname filename
String String 1023
Module Name of the file. Value is eventtype specific: System: $object
in
bytesIn
Integer
Number of bytes transferred inbound. Inbound relative to the source to destination relationship, meaning that data was flowing from source to
$bytes_received
ArcSight Technical Note Contains Confidential and Proprietary Information
10
Event Interoperability Standard
CEF Key Name
Full Name
Data Type
Length
Meaning
Palo Alto Networks Value Field
destination.
msg
Message
String
1023
An arbitrary message giving more details about the event. Multiline entries can be produced by using \n as the new-line separator. Number of bytes transferred outbound. Outbound relative to the source to destination relationship, meaning that data was flowing from destination to source.
Value is eventtype specific: Threat: $misc System: $fmt Config: $path $bytes_sent
out
bytesOut
Integer
proto
transportProtoc ol
String
31
Identifies the Layer-4 protocol used. The possible values are protocol names such as TCP or UDP. The time at which the event related to the activity was received. The format isMMM dd yyyy HH:mm:ssor milliseconds since epoch (Jan 1st 1970).
$proto
rt
receiptTime
Time Stamp
$cef-formattedreceive_time
shost
sourceHostNam e
String
1023
Identifies the source that an event refers to in an IP network. The format should be a fully qualified domain name associated with the source node, when a node is available.Examples: host.domain.com or host. Identifies the translated source that the event refers to in an IP network. The format is an Ipv4 address. Example: 192.168.10.1 Port after it was translated by for example a firewall. Valid port numbers are 0 to 65535.
Value is eventtype specific: HIP Match: $machinename
sourceTranslatedA ddress
Ipv4 Address
$natsrc
sourceTranslatedP ort
Integer
$natsport
ArcSight Technical Note Contains Confidential and Proprietary Information
11
Event Interoperability Standard
CEF Key Name
Full Name
Data Type
Length
Meaning
Palo Alto Networks Value Field $sport
spt
sourcePort
Integer
The valid port numbers are 0 to 65535. Identifies the source that an event refers to in an IP network. The format is an Ipv4 address.Example: 192.168.10.1 The time when the activity the event referred to started. The format isMMM dd yyyy HH:mm:ssor milliseconds since epoch (Jan 1st 1970). The time when the activity the event referred to started. The format isMMM dd yyyy HH:mm:ssor milliseconds since epoch (Jan 1st 1970). 1023 Identifies the source user by name. E-mail addresses are also mapped into the UserName fields. The sender is a candidate to put into sourceUserName.
src
sourceAddress
Ipv4 Address
$src
start
startTime
Time Stamp
$cef-formattedtime_generated
start
startTime
Time Stamp
$cef-formattedtime_generated
suser
sourceUserNam e
String
$srcuser
ArcSight Technical Note Contains Confidential and Proprietary Information
12
Potrebbero piacerti anche
- Palo Alto Networks CEF Certified Configuration Guide 03 02 11Documento12 paginePalo Alto Networks CEF Certified Configuration Guide 03 02 11SilvaNessuna valutazione finora
- Palo Alto Networks PANOS 6 0 CEF Configuration Guide 2014Documento18 paginePalo Alto Networks PANOS 6 0 CEF Configuration Guide 2014Ryanb378Nessuna valutazione finora
- Cyber-Ark Privileged Identity Management 7 1 CEF Config Guide 2012Documento8 pagineCyber-Ark Privileged Identity Management 7 1 CEF Config Guide 2012Anitha RajkumarNessuna valutazione finora
- Zscaler - NSS - 4.1 - CEF - Config Guide - 2013Documento7 pagineZscaler - NSS - 4.1 - CEF - Config Guide - 2013amithvaishnav0% (1)
- Q1Labs LEEF FormatDocumento8 pagineQ1Labs LEEF Formatfa_visionNessuna valutazione finora
- ArcSight Flexconnector Training V2Documento75 pagineArcSight Flexconnector Training V2Zoumana DiomandeNessuna valutazione finora
- Nemo File Format 2.15Documento453 pagineNemo File Format 2.15sharliesmileNessuna valutazione finora
- Configuring Host-Based IDS and IPS DevicesDocumento10 pagineConfiguring Host-Based IDS and IPS DevicesSatish GadeNessuna valutazione finora
- SB Imperva SecureSphere CEF GuideDocumento21 pagineSB Imperva SecureSphere CEF GuideElhadji Boly Junior JOHNSONNessuna valutazione finora
- Managing Cisco IPS SensorsDocumento19 pagineManaging Cisco IPS Sensorsscribd_jrNessuna valutazione finora
- Palo Alto GuideDocumento124 paginePalo Alto GuideLuisAgapitoNessuna valutazione finora
- Arcsight Flex ConnectorsDocumento14 pagineArcsight Flex ConnectorsSamirih100% (1)
- Cisco Catalyst SwitchDocumento6 pagineCisco Catalyst SwitchEsteban Kmello RodriguezNessuna valutazione finora
- Apache HTTP ServerDocumento7 pagineApache HTTP ServerYdaelVargasSalazarNessuna valutazione finora
- Simple Event Management Protocol (SEMP)Documento2 pagineSimple Event Management Protocol (SEMP)Jason Meiers100% (3)
- Nemo File Format 2 03Documento373 pagineNemo File Format 2 03Umar PervaizNessuna valutazione finora
- Scor 05Documento11 pagineScor 05Ahmed El kayalNessuna valutazione finora
- Sc14dectipbs Web API v1.3Documento13 pagineSc14dectipbs Web API v1.3Kostas ZafeiropoulosNessuna valutazione finora
- ALE - 1.1UG API GuideDocumento34 pagineALE - 1.1UG API GuideUrahara KisukeNessuna valutazione finora
- NSX 64 Logging and System Events PDFDocumento71 pagineNSX 64 Logging and System Events PDFrubinbrittoNessuna valutazione finora
- ArcSight Audit Quality SIEM SolutionDocumento6 pagineArcSight Audit Quality SIEM SolutionKrishna KumarNessuna valutazione finora
- Pfaff Et Al NETCONF Security 0321 v01Documento13 paginePfaff Et Al NETCONF Security 0321 v01safyh2005Nessuna valutazione finora
- Programmer's Guide For Web Solutions: Wison Technology CorpDocumento10 pagineProgrammer's Guide For Web Solutions: Wison Technology CorpPaolo LozadaNessuna valutazione finora
- Juniper StudiesDocumento7 pagineJuniper StudiesJohnNessuna valutazione finora
- FactoryTalk Alarm and Event (CPR9 and Later) Log Database Schema (Format) PDFDocumento6 pagineFactoryTalk Alarm and Event (CPR9 and Later) Log Database Schema (Format) PDFDavid DuranNessuna valutazione finora
- JULY 2014: Nemo File Format Specification 2.17Documento558 pagineJULY 2014: Nemo File Format Specification 2.17Eric CorpuzNessuna valutazione finora
- Cisco IronPort Cloud Email Security ServiceDocumento18 pagineCisco IronPort Cloud Email Security Servicehadini.jamaleddineNessuna valutazione finora
- Alienvault Data Source Integration - Cisco ASADocumento4 pagineAlienvault Data Source Integration - Cisco ASARaza HaqNessuna valutazione finora
- SBCDocumento21 pagineSBCLazaNessuna valutazione finora
- Symantec Email App For QRadarDocumento24 pagineSymantec Email App For QRadarw0lfmast3rNessuna valutazione finora
- Csharp DeffinationDocumento39 pagineCsharp DeffinationDharmendra SinghNessuna valutazione finora
- Flowmon Ads Userguide enDocumento59 pagineFlowmon Ads Userguide enAnh PhongNessuna valutazione finora
- B Ucs Api BookDocumento44 pagineB Ucs Api Booktanke666Nessuna valutazione finora
- Rsa Netwitness Logs: Tripwire EnterpriseDocumento9 pagineRsa Netwitness Logs: Tripwire EnterpriseTommy Mendez SalcedoNessuna valutazione finora
- Configure Idoc in EccDocumento18 pagineConfigure Idoc in EccUdayNessuna valutazione finora
- Computer Network No2 Layer Approch To Network Design From APCOMS (UandiStar)Documento24 pagineComputer Network No2 Layer Approch To Network Design From APCOMS (UandiStar)UdayKumar JayavaramNessuna valutazione finora
- Rsa Netwitness Platform: Check Point Security Suite, Ips-1Documento19 pagineRsa Netwitness Platform: Check Point Security Suite, Ips-1Tommy Mendez SalcedoNessuna valutazione finora
- Device Sensor: Finding Feature InformationDocumento28 pagineDevice Sensor: Finding Feature Informationkarthong4057Nessuna valutazione finora
- Intro To Sciencelogic EM7 7.3.3Documento98 pagineIntro To Sciencelogic EM7 7.3.3Craquehead67% (3)
- Control Over LAN Using Microsoft Excel: Agilent E5070B/E5071B ENA Series RF Network AnalyzersDocumento12 pagineControl Over LAN Using Microsoft Excel: Agilent E5070B/E5071B ENA Series RF Network AnalyzersRicardo Silva100% (1)
- CCNA Security 210-260 Dump + Explanation (Updating ) - Script KiddieDocumento154 pagineCCNA Security 210-260 Dump + Explanation (Updating ) - Script KiddieJitesh PatelNessuna valutazione finora
- VideoXpert Event Monitor Service User GuideDocumento16 pagineVideoXpert Event Monitor Service User GuideDario Campos AlcantaraNessuna valutazione finora
- Layer 2 Imp Eh33l2Documento32 pagineLayer 2 Imp Eh33l2smarty_rfNessuna valutazione finora
- BCSL 056 Network Programming and Administration Lab 2019 20Documento13 pagineBCSL 056 Network Programming and Administration Lab 2019 20Prashant MishraNessuna valutazione finora
- Hbgary Shell Trojan GensDocumento28 pagineHbgary Shell Trojan GensResearch GuyNessuna valutazione finora
- Controller SMGDocumento696 pagineController SMGJonathan EdvardsNessuna valutazione finora
- Computer Networks CPS 422: Layered Approach To Network DesignDocumento24 pagineComputer Networks CPS 422: Layered Approach To Network DesignLijitha VegiNessuna valutazione finora
- Cisco Unified Border Element Configuration GuideDocumento242 pagineCisco Unified Border Element Configuration GuidenbadungNessuna valutazione finora
- Micro Focus Security Arcsight Connectors: Smartconnector For Arbor Networks Peakflow Syslog Configuration GuideDocumento11 pagineMicro Focus Security Arcsight Connectors: Smartconnector For Arbor Networks Peakflow Syslog Configuration Guideajay kumarNessuna valutazione finora
- Rsa Netwitness Platform: Blue Coat Proxysg SgosDocumento14 pagineRsa Netwitness Platform: Blue Coat Proxysg SgosShirley Diossana GarayNessuna valutazione finora
- Tools To Aid Debugging On AIXDocumento12 pagineTools To Aid Debugging On AIXYoussifAhmedJulaihNessuna valutazione finora
- Log Parsing 101Documento15 pagineLog Parsing 101Seynabou SougouNessuna valutazione finora
- S8 PerfDocumento15 pagineS8 PerfdeponlyNessuna valutazione finora
- 323-1851-194 (6500 R14.0 CLI T-Series) Issue1Documento2.398 pagine323-1851-194 (6500 R14.0 CLI T-Series) Issue1Tariq EhsanNessuna valutazione finora
- PUSH SDK Communication Protocol V2.0.1Documento28 paginePUSH SDK Communication Protocol V2.0.1Héctor Hugo HuergoNessuna valutazione finora
- IBM Qradar DSMConfigurationGuideDocumento18 pagineIBM Qradar DSMConfigurationGuidezefrenchNessuna valutazione finora
- Hacking Connected Cars: Tactics, Techniques, and ProceduresDa EverandHacking Connected Cars: Tactics, Techniques, and ProceduresNessuna valutazione finora
- Mastering Python Network Automation: Automating Container Orchestration, Configuration, and Networking with Terraform, Calico, HAProxy, and IstioDa EverandMastering Python Network Automation: Automating Container Orchestration, Configuration, and Networking with Terraform, Calico, HAProxy, and IstioNessuna valutazione finora
- 12 - AclDocumento14 pagine12 - AclmhdNessuna valutazione finora
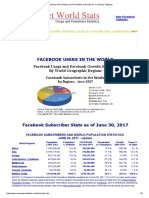
- Facebook World Stats and Penetration in The World - Facebook Statistics 2017Documento5 pagineFacebook World Stats and Penetration in The World - Facebook Statistics 2017Pedro AguiarNessuna valutazione finora
- E-TECH Study Guide: TOPIC 1 - Information and Communication TechnologyDocumento4 pagineE-TECH Study Guide: TOPIC 1 - Information and Communication TechnologyCha-Cha SanchezNessuna valutazione finora
- Post Frame Building Design ManualDocumento89 paginePost Frame Building Design Manualpatrtrem0% (3)
- Pexip Client REST API V32.aDocumento35 paginePexip Client REST API V32.asima pericNessuna valutazione finora
- Types of Internet Protocols - GeeksforGeeksDocumento9 pagineTypes of Internet Protocols - GeeksforGeeksAlok KumarNessuna valutazione finora
- M3-Social Media Text AnalyticsDocumento19 pagineM3-Social Media Text AnalyticsKHAN SANA PARVEENNessuna valutazione finora
- CyberArk Security Fundamentals For Privileged Account SecurityDocumento6 pagineCyberArk Security Fundamentals For Privileged Account SecurityLeandro LomibaoNessuna valutazione finora
- Yahoo Case StudyDocumento19 pagineYahoo Case StudyPankaj Kumar100% (1)
- Don Dalrymple ResumeDocumento2 pagineDon Dalrymple ResumeimhiskidNessuna valutazione finora
- Why Learning Greek Using PDF Lessons Is Practical and E CientDocumento11 pagineWhy Learning Greek Using PDF Lessons Is Practical and E CientThuanNessuna valutazione finora
- About - CA ExamDocumento2 pagineAbout - CA ExamNadeem khanNessuna valutazione finora
- Assignment 1 Question Paper 2023Documento5 pagineAssignment 1 Question Paper 2023katlehoNessuna valutazione finora
- Rex Swain's HTTP Viewer 4 PDFDocumento5 pagineRex Swain's HTTP Viewer 4 PDFVic TorNessuna valutazione finora
- SNA Assignment Group 7Documento6 pagineSNA Assignment Group 7Mafuz KemalNessuna valutazione finora
- Palo Alto CLI Cheat SheetDocumento7 paginePalo Alto CLI Cheat SheetMayur Kakadiya100% (2)
- Chapter Three: E-Commerce Software Building BlocksDocumento20 pagineChapter Three: E-Commerce Software Building BlocksAgmasie TsegaNessuna valutazione finora
- Are You Sure?: (GRR6601) The Expanse RPG PDFDocumento3 pagineAre You Sure?: (GRR6601) The Expanse RPG PDFToto Le GrandNessuna valutazione finora
- Nuance Security Biometrics - June2020Documento25 pagineNuance Security Biometrics - June2020gifta dossNessuna valutazione finora
- LICENSEDocumento22 pagineLICENSEMarkNessuna valutazione finora
- Summer 2020 (Session C) CSE 548: Advanced Computer Network SecurityDocumento15 pagineSummer 2020 (Session C) CSE 548: Advanced Computer Network SecurityIoana Raluca TiriacNessuna valutazione finora
- RT056 DS R1520 V1.0.8Documento2 pagineRT056 DS R1520 V1.0.8yassine saferNessuna valutazione finora
- E-Commerce InfrastructureDocumento15 pagineE-Commerce Infrastructurendc6105058Nessuna valutazione finora
- 3 ADFS Installation and ConfigurationDocumento14 pagine3 ADFS Installation and ConfigurationIngrid CardenasNessuna valutazione finora
- Dingtone Free Calling App Releases New Phone Numbers in 11 Countries, Reaches One Billion Calling Minutes Per YearDocumento2 pagineDingtone Free Calling App Releases New Phone Numbers in 11 Countries, Reaches One Billion Calling Minutes Per YearPR.comNessuna valutazione finora
- Aws S3Documento987 pagineAws S3jstoNessuna valutazione finora
- Enterprise Security Risk Management: Data Is PotentialDocumento15 pagineEnterprise Security Risk Management: Data Is PotentialKampeephorn SantipojchanaNessuna valutazione finora
- and Watch Movies OnlineDocumento3 pagineand Watch Movies OnlineFayazNessuna valutazione finora
- Epinoyload All Product List Globe TMDocumento3 pagineEpinoyload All Product List Globe TMjhecyNessuna valutazione finora
- How To See List of Z T-Codes - SCNDocumento3 pagineHow To See List of Z T-Codes - SCNRaul KarkyNessuna valutazione finora